- 1. What Does a Firewall Do?
- 2. Types of Firewalls
- 3. Firewall Features
- 4. Benefits of Firewalls
- 5. Firewall Challenges
- 6. Firewall Threats and Vulnerabilities
- 7. Firewall Configuration
- 8. Firewall Architecture
- 9. Firewall Rules
- 10. Firewall Best Practices
- 11. What Is Firewall as a Service (FWaaS)?
- 12. Comparing Firewalls with Other Security Technologies
- 13. History of Firewalls
- 14. Firewall FAQs
- What Does a Firewall Do?
- Types of Firewalls
- Firewall Features
- Benefits of Firewalls
- Firewall Challenges
- Firewall Threats and Vulnerabilities
- Firewall Configuration
- Firewall Architecture
- Firewall Rules
- Firewall Best Practices
- What Is Firewall as a Service (FWaaS)?
- Comparing Firewalls with Other Security Technologies
- History of Firewalls
- Firewall FAQs
What is a Firewall? | Firewall Definition
A firewall is a network security solution that monitors and regulates traffic based on defined security rules and accepts, rejects or drops traffic accordingly.
- What Does a Firewall Do?
- Types of Firewalls
- Firewall Features
- Benefits of Firewalls
- Firewall Challenges
- Firewall Threats and Vulnerabilities
- Firewall Configuration
- Firewall Architecture
- Firewall Rules
- Firewall Best Practices
- What Is Firewall as a Service (FWaaS)?
- Comparing Firewalls with Other Security Technologies
- History of Firewalls
- Firewall FAQs
Firewalls act as barriers between private and external networks, checking and filtering data based on set security rules. Using these rules, firewalls decide if they should allow, block, or drop the data to protect the network. Form factors include hardware, software, or a mix of both. This process ensures only safe, legitimate traffic gains entry.
What Does a Firewall Do?

The function of a firewall is to secure network hosts by monitoring and managing traffic flow. Network hosts are devices (e.g., computers) that communicate within a network. Their exchanges can be within an internal network or between internal and external networks.
The role of a firewall in cyber security is paramount. It serves as the first line of defense, scrutinizing and controlling network traffic to thwart potential cyber threats. By maintaining a vigilant barrier between trusted and untrusted networks, firewall systems are pivotal in ensuring the digital safety of an organization's assets and data.
Firewalls filter and scrutinize packets against their rule sets. If a packet doesn't meet the established criteria, entry is denied. A packet is a formatted piece of data equipped for online transmission. Packets transport all data transferred over the internet. They contain core data, information about the data's origin, destination port, and other relevant details.
Stateful packet inspection is a pivotal concept. Every packet is scrutinized within the context of its originating session. This ensures that each packet's journey—origin, destination, and the path it took—is known, allowing for a comprehensive evaluation against potential threats.
Firewalls rely on multiple technologies and methodologies to distinguish legitimate network traffic from potentially malicious activity. Fundamentally, least privilege access stipulates that entities should only access what they need. By setting policies in alignment with this principle, users don't inadvertently introduce threats.
They also conduct rigorous traffic inspection. They compare incoming data against databases of known threat signatures. If traffic aligns with a known threat pattern, it is blocked. It is important to note that relying solely on known signatures isn't sufficient due to the dynamic nature of cyber threats. Solutions must constantly update databases with emerging threat patterns and employ advanced methods to detect previously unseen threats.
The manner in which a firewall treats inbound and outbound network traffic is distinct. Inbound, or north-south traffic, comes from external sources like the internet. As this traffic might carry malicious URLs or malware, firewalls inspect it thoroughly, checking for threats and ensuring no harmful elements breach the perimeter. East-west, or internal traffic, moves between different sections of an internal network. Although it might appear safer, it's crucial to inspect this traffic because threats can bypass the perimeter or enter through other means.
Dive deeper into how firewalls examine and filter network traffic to ensure only authorized and safe traffic passes through by reading, What Does a Firewall Do? | How Firewalls Work.
Types of Firewalls

Firewalls are typically categorized based on systems they protect, form factors, placement within a network infrastructure, or how they filter data.
Firewall Types by Systems Protected
Network Firewall
Protects an entire network by monitoring and controlling incoming and outgoing traffic based on predetermined security policies.
Host-Based Firewall
Installed on individual devices or hosts, these monitor incoming and outgoing traffic from that specific device.
Firewall Types by Form Factors
Hardware Firewall
A hardware firewall is a physical, individual device installed between network elements and connected devices.
Software Firewall
A software firewall is a software form factor rather than a physical appliance, which can be deployed on servers or virtual machines to secure cloud environments.
Types include container firewalls, virtual firewalls (also known as cloud firewalls), and managed service firewalls.
Discover how software firewalls can be deployed on servers or virtual machines to secure cloud environments by reading our article, What is a Software Firewall?
Firewall Types by Placement within Network Infrastructure
Internal Firewall
These are positioned within a network, rather than at the edge, to protect against internal threats.
Distributed Firewall
This is a scalable approach, where the solution is distributed across multiple devices or servers.
Perimeter Firewall
Placed at the edge or boundary of a network, this firewall controls traffic entering or leaving the network.
Firewall Types by Data Filtering Method
Next Generation Firewall (NGFW)
A more sophisticated technology, NGFW combines traditional capabilities with advanced functionalities like intrusion prevention systems (IPS) and encrypted traffic inspection.
Packet Filtering Firewall
This technology examines each data packet sent to the network. If the packet matches an established security rule set, it is allowed; otherwise, it's denied.
Circuit Level Gateway
Functioning at the session layer, these ensure the validity of packets in an attempted connection. Once validated, a persistent connection between networks is permitted.
Web Application Firewall
Specifically designed to protect web applications, this solution filters, monitors, and blocks HTTP traffic to and from web applications, defending against threats such as cross-site scripting and SQL injection.
Proxy Firewall
Operating at the application layer, this solution acts as an intermediary for requests from clients. It evaluates requests against a security rule set and blocks or allows accordingly.
Stateful Inspection Firewall
Unlike stateless firewalls, these remember past active connections. Decisions are based on set rules and context, tracking the state of active connections.
Discover more details about each type of firewall by reading our article, Types of Firewalls Defined and Explained.
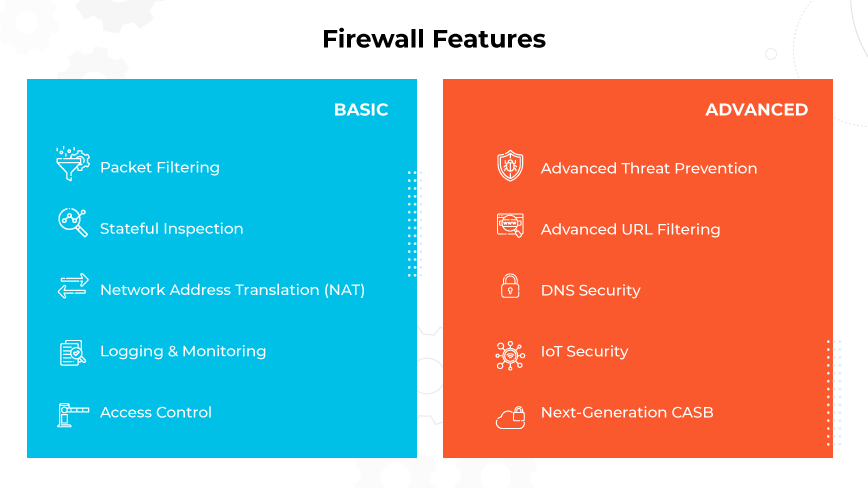
Firewall Features
With evolving times, business protection methods must adapt. It’s important to note that traditional firewalls provide basic defense, but Next-Generation Firewalls (NGFWs), including ML-powered versions, reflect today's advanced digital threats. These firewalls blend old and new technologies for enhanced network security.
Basic Firewall Features
Packet Filtering
Packet filtering evaluates data packets as they pass through a firewall. Based on predetermined criteria, such as source and destination IP addresses or port numbers, the firewall decides whether to allow or block each packet.
Stateful Inspection
Stateful inspection monitors the active connections of a network. By tracking the state and attributes of each data packet, it ensures that only legitimate traffic passes through, enhancing security.
Network Address Translation (NAT)
NAT modifies the source or destination IP address of data packets. This not only conserves IP addresses but also conceals internal network structures, making it harder for potential attackers to gain insight into the network.
Logging and Monitoring
Logging keeps records of network activities. This provides insights into traffic patterns, aiding in vulnerability assessment and facilitating timely responses to potential security breaches.
Access Control
Access control regulates which entities can communicate with the system. By defining a set of rules, firewalls determine which users, systems, or IP addresses are granted or denied access to network resources.
Advanced Firewall Features
Advanced Threat Prevention
Modern firewalls incorporate Advanced Threat Prevention to counteract zero-day attacks instantly. Using inline deep learning engines, this feature offers superior defense against novel exploit attempts and command and control mechanisms. It also supports automated workflows for widely-accepted signature formats.
Advanced URL Filtering
Advanced URL Filtering in cutting-edge firewall products employs inline deep learning to analyze web traffic in real time. This technology effectively stops both known and novel web-based threats, such as phishing and malware, ensuring a more secure browsing experience.
DNS Security
DNS Security, found in contemporary firewall technology, utilizes predictive analytics and machine learning to thwart sophisticated attacks leveraging DNS. Its tight integration with the firewall automates protections, providing deeper insights into threats and eliminating the need for separate tools.
IoT Security
IoT Security offers a robust Zero Trust security approach for IoT devices, combining visibility, prevention, and enforcement. With the integration of machine learning, modern firewalls can segment networks based on context, reducing risk and safeguarding both IoT and IT devices from various threats.
Next-Generation CASBs
Current firewall technology introduces the Next-Generation CASB to secure SaaS applications in real-time across enterprises. Unlike traditional CASB solutions, the next-gen version offers comprehensive data protection, accommodating the evolving needs of distributed workforces.
Benefits of Firewalls
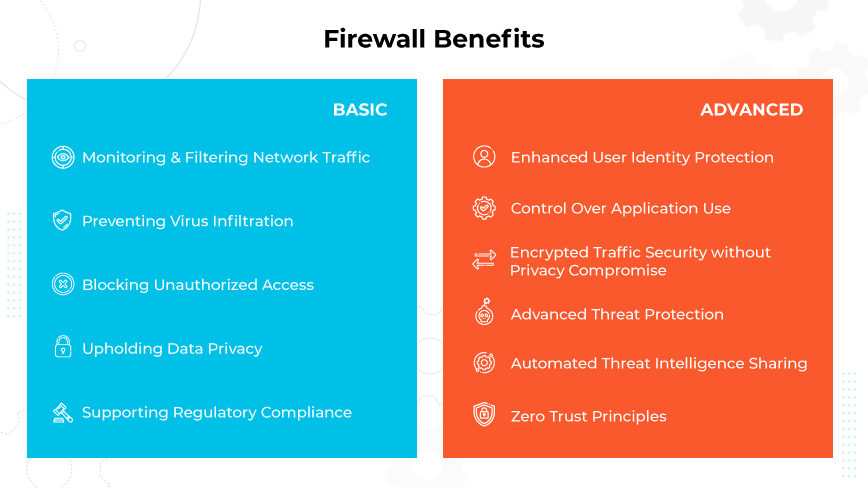
Basic Firewall Benefits
Monitoring and Filtering Network Traffic
A firewall oversees all data packets on a network, primarily using stateful inspection to monitor active connections. Acting as an initial barrier, it filters incoming information, ensuring harmful data or patterns are blocked, thereby safeguarding the internal network.
Preventing Virus Infiltration
Firewalls, alongside antivirus software, provide an effective barrier against evolving viruses. By analyzing data packet headers, they identify and neutralize malicious patterns. Next-generation firewalls (NGFW) further elevate this defense, catching even the most advanced viruses.
Blocking Unauthorized Access
Given the rise in unauthorized access attempts, firewalls serve as gatekeepers to all digital entry points. Network firewalls, in particular, leverage access controls to ensure only trusted sources interact with the system.
Upholding Data Privacy
Firewalls scrutinize data that enters or exits a network, ensuring unauthorized access is prevented and private data stays confidential. They are essential in shielding sensitive business information from external threats in the digital landscape.
Supporting Regulatory Compliance
Firewalls enforce stringent data protection, controlling and logging access to sensitive information. These logs serve as vital evidence for regulatory audits. By maintaining data integrity and offering verifiable logs, firewalls help organizations stay compliant and foster trust.
Advanced Firewall Benefits
Enhanced User Identity Protection
Modern firewalls precisely identify users, ensuring security policies cater to specific business needs. This fine-tuned control allows only certain user groups to perform specific tasks.
Control Over Application Use
Sophisticated firewalls can identify and control application access, ensuring only approved apps are used. This balance ensures security while allowing application flexibility based on business needs.
Encrypted Traffic Security without Privacy Compromise
Advanced firewalls can decrypt malicious traffic without compromising user privacy, allowing for thorough scrutiny of potential threats without violating user rights.
Advanced Threat Protection
With escalating cyber threats, many contemporary firewalls provide integrated solutions for protection across various attack vectors, ensuring defense against both known and emerging threats.
Automated Threat Intelligence Sharing
Some advanced firewalls automate threat detection, analysis, and response, gathering insights globally for prompt security updates.
Zero Trust Principles
Advanced firewalls emphasize the Zero Trust approach, demanding consistent validation and authentication for all network actions, ensuring every potential threat is detected and addressed.
Explore how modern advancements have led to even more sophisticated firewall features and benefits by reading, What Are the Benefits of a Firewall?
Firewall Challenges
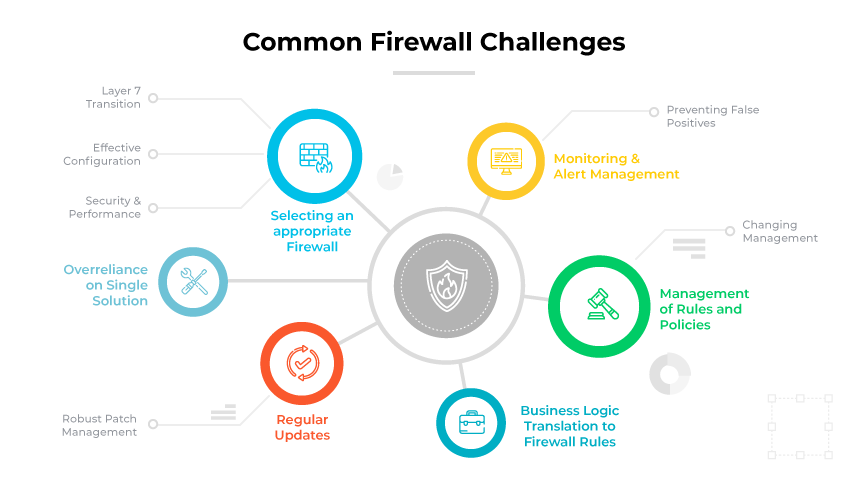
Selecting an Appropriate Firewall
The market offers various types, ranging from basic packet-filtering to advanced next-generation with enhanced features. The selection process demands a clear understanding of organizational needs. Often, organizations deploy multiple solutions to ensure optimal security, cost-efficiency, and performance balance.
Effective Configuration
Proper configuration is imperative. Since there isn’t a universal setting fit for all, it’s essential to tailor features like network segmentation, bandwidth prioritization, and application controls. Detailed policies specifying allowed services, applications, and networks are beneficial.
Regular Updates
Threat landscapes constantly evolve. Therefore, firewalls require periodic updates to address vulnerabilities and refresh hostile traffic definitions. A consistent review and update schedule is advisable to ensure maximum protection. Before updating, it's essential to assess the impacts, like potential disruptions or performance issues.
Management of Rules and Policies
With time and changing circumstances, rules and policies need revisiting. Continually adding rules can lead to a cluttered system with possible performance issues and potential vulnerabilities. Effective management tools offer insights into which rules are redundant or need optimization.
Preventing False Positives
Overly strict policies might wrongly identify legitimate traffic as threats. While stringent rules are preferable to lax ones, they can hinder end user activities. Custom rules and configurations become essential to differentiate specific traffic types. Over time, understanding daily traffic profiles can reduce these challenges, offering better protection.
Monitoring and Alert Management
Continuous performance and availability monitoring is vital. Metrics related to device operation help in early detection of potential issues. For instance, tracking device high-availability failover can identify possible software bugs or hardware issues before they escalate.
Change Management in Dynamic Environments
IT systems undergo constant change. With every addition to the network, rules need updating. Sometimes, vendor documentation might lack clarity on application protocols or ports, necessitating troubleshooting to ensure proper access.
Robust Patch Management
Vulnerabilities exist in all IT systems. A comprehensive patch management process for security devices is critical to ensure vulnerabilities don't become a breach point. Monitoring security notices and regularly updating software versions ensures a fortified network environment.
Business Logic Translation to Firewall Rules
The inherent architecture of firewalls can pose translation challenges. CISOs and other executives may set business logic-based security intentions. Yet not all vendors allow an easy translation of this business logic into rules. If the design can't readily accommodate this translation, the result may be a complex, inefficient set of rules.
Layer 7 Transition Difficulty
Traditional Layer 3, Layer 4 firewalls often accumulate complex rule sets over time. Transitioning from these entrenched systems to an application-level Layer 7 solution can be daunting. This shift requires abandoning old policies and adopting a clearer, more logical approach.
Balancing Security and Performance
Firewalls manage and inspect vast amounts of traffic, potentially becoming network bottlenecks. Administrators must often decide between enhanced security features and optimal network speed. Overloading firewalls can lead to slowed or halted network operations, affecting business activities.
Overreliance on a single solution can lead to performance issues or total system failure. Modern solutions offer predictive tools, such as AIOps, enabling administrators to foresee capacity issues and adjust accordingly.
Firewall Threats and Vulnerabilities
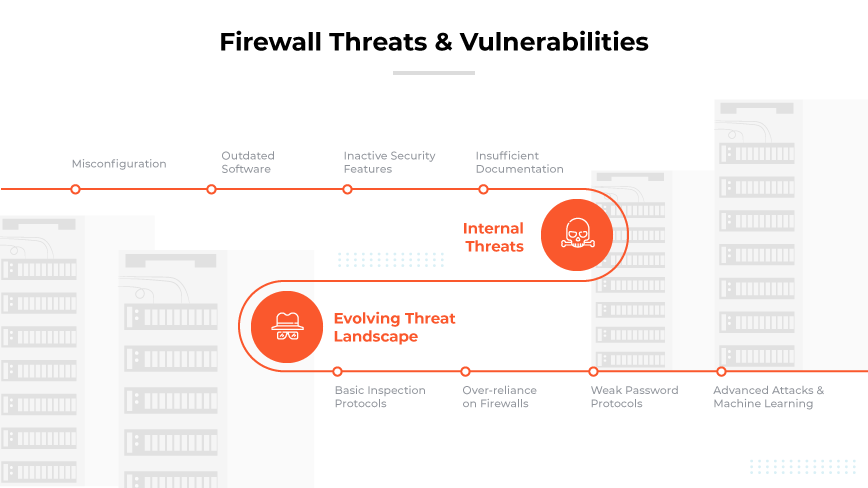
Misconfiguration
The effectiveness of firewalls largely hinges on correct configuration. Any deviation or oversight during this process can result in unintended openings for malicious entities. For instance, when default settings remain unchanged, the device becomes an easier target. Attackers, being familiar with popular products, can exploit these defaults, paving the way for cyber intrusions. Regularly reviewing and adjusting configurations can help in preventing such vulnerabilities.
Outdated Software
Continual software updates are imperative for maintaining efficiency. Manufacturers release patches to combat newly identified threats and vulnerabilities. A firewall operating on outdated software not only becomes susceptible to these threats but can also encounter incompatibility issues with newer systems, leading to unforeseen security gaps. Timely software updates play a pivotal role in preserving protective integrity.
Inactive Security Features
Firewalls often come equipped with an array of security features. However, if not activated, these features remain dormant, providing no real protection. Anti-spoofing measures, for example, need to be activated to detect and block disguised, malicious traffic. Routine system audits can ensure that all these tools are active and operating optimally.
Insufficient Documentation
A comprehensive documentation of firewall configurations, rules, and protocols is crucial. Documentation can aid troubleshooting, ensure consistent firewall management, and streamline the onboarding of new IT personnel. In its absence, organizations risk inconsistencies, especially during personnel transitions, making systems more susceptible to breaches.
Internal Threats
Malicious or disgruntled employees with system access can sometimes bypass firewalls, exploiting their intimate knowledge of internal systems. Monitoring internal traffic and routinely reviewing user privileges becomes essential to counteract such threats.
Weak Password Protocols
Weak password practices can significantly undermine firewall efficacy. Simple, easily guessable, or default passwords are attractive entry points for cyber attackers. By instituting strong password protocols and mandating regular password changes, organizations can substantially reduce this vulnerability.
Basic Inspection Protocols
Traditional appliances often rely on rudimentary inspection methods, checking data packets for source and destination. Malicious actors can easily circumvent such methods using techniques like spoofing. In contrast, newer generations employ advanced strategies like deep packet inspection, which scrutinizes the content within data packets, ensuring a more thorough screening of incoming traffic.
Over-reliance on Firewalls
While firewalls are indispensable to an organization's cybersecurity framework, sole reliance can be perilous. Effective security is multi-layered, encompassing intrusion detection systems, anti-malware solutions, and regular security audits. By integrating multiple security layers, organizations can ensure that even if one layer is compromised, others remain intact to neutralize potential threats.
Evolving Threat Landscape
Relying solely on known threat signatures for defense is becoming insufficient. Advancements in technology have equipped hackers with sophisticated methods, enabling them to generate new threats with unique or evolving signatures. This reality requires solutions to adapt swiftly, recognizing and countering threats that don't fit traditional profiles.
Advanced Attacks and Machine Learning
Hackers now harness machine learning and AI to enhance their attack methods. These advanced threats can bypass traditional signature-based defenses, demanding firewalls to incorporate more proactive and intelligent detection mechanisms.
Firewall Configuration
Firewall configuration involves determining and setting rules, policies, and other criteria to protect a network. The procedure entails making decisions about which data packets should be granted or denied access based on specific criteria, such as source and destination IP addresses or domain names.

How to Configure a Firewall
Secure the Firewall
Begin by updating the latest firmware to receive recent security patches. Default user accounts and passwords should be changed or disabled. Administrative access should be restricted, limiting exposure to threats.
Design Firewall Zones and IP Address Structure
Identify and categorize network assets based on their functions and risks. For instance, servers interfacing with the internet should be in a DMZ, protecting the internal network. Assign zones to designated interfaces to ensure proper routing.
Implement Access Control Lists (ACLs)
ACLs define the permitted or blocked traffic between zones. Rules should be specific to source and destination IPs and port numbers. End each ACL with a "deny all" rule, ensuring only explicit traffic is allowed.
Activate Additional Services and Logging
Modern solutions offer additional services like DHCP and IPS; activate as needed but disable unused services. Logging is essential: set firewalls to send detailed logs to a central service. This data aids administrators in overseeing network activity.
Test the Configuration
Post-configuration, test the firewall using vulnerability scanners and penetration testers. This confirms that undesired traffic is blocked, and legitimate traffic passes. Ensure a secure backup of the configuration for quick recovery.
Ongoing Monitoring and Management
Continuously monitor logs and alerts for optimal security. Adjust rules as threats evolve or network operations change. Document all changes and updates for clarity and accountability.
Health, such as CPU and memory usage, is paramount. Tools like AIOps not only monitor the firewall's alignment with security best practices but also assess its health over time. Predictive analyses can flag potential issues, aiding in proactive remediation.
Firewall Architecture

Firewall architecture refers to the design and deployment of firewalls in various environments to protect networks, applications, and data. Firewall diagrams have evolved over the years in response to changing technological landscapes and emerging threats.
Firewalls were once primarily understood in terms of types, such as packet filtering or intrusion prevention systems. However, the focus has shifted from simply classifying firewalls by their specific technologies to understanding their role in diverse environments. The main aim of modern architectures remains safeguarding networks and data.
Data Center Architecture
The data center represents a distinct architecture. Within many data centers, firewalls, often referred to as 'top of the rack' appliances, protect servers and workloads. These solutions are optimized for high-speed data center operations but can handle advanced threat protection tasks like halting malware. Furthermore, with varied workloads in a data center, segmentation becomes crucial. Whether it's outward-facing web servers or internal servers, different servers have different threat landscapes. Appropriate configurations ensure diverse workloads are adequately protected.
Public Cloud Architecture
With the migration of workloads to public cloud environments, architecture needs to adapt. These environments require firewalls capable of securing specific cloud constructs. Additionally, with the rise of containerized applications, there's a need for solutions that can address such use cases in cloud environments. Leading providers have begun to offer solutions integrated directly into cloud platforms. This allows for direct rule management from cloud interfaces, streamlining operations and ensuring compliance.
Branch Architecture
When discussing deployment in a branch or office setting, it's essential to recognize that the term "architecture" is refers more so to the use case than a traditional structural design. In this context, branch architecture refers to how firewalls are strategically positioned in an office to protect both internal and external traffic. This involves considering zone-based solutions, security enforcement using identity, and application ID, among other factors. A modern solution in a branch setting is critical to monitor and protect against threats, especially as workloads and user activities continue to evolve.
Firewall Rules
Firewall rules are specifications set by network administrators that instruct a firewall on how to process incoming and outgoing network traffic. By dictating how firewalls should handle traffic based on parameters such as source or destination IP addresses, ports, and protocols, they play a pivotal role in maintaining network security.
Types of Firewall Rules
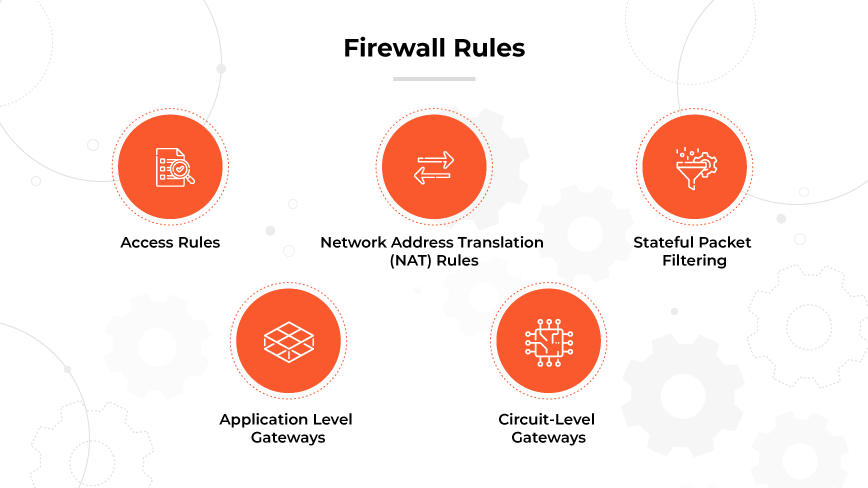
Access Rules
Access rules manage traffic by evaluating parameters like source and destination addresses, protocol, and port number. Traffic is either permitted, blocked, or rejected based on these evaluations.
Network Address Translation (NAT) Rules
Essential for altering IP addresses as traffic moves between networks, NAT rules facilitate routing and can protect private networks from external threats.
Stateful Packet Filtering
Stateful packet filtering inspects individual data packets in relation to existing network connectivity states, making decisions to either allow or block traffic after comparison.
Application Level Gateways
Operating at layer 7 of the OSI model, application level gateways mediate traffic between the internet and an internal network, often used to control access.
Circuit-Level Gateways
Working at layer 5 of the OSI model, circuit-level gateways verify the legitimacy of a session by monitoring TCP handshakes, focusing on verifying the legitimacy of the remote system rather than inspecting individual packets.
Firewall Best Practices
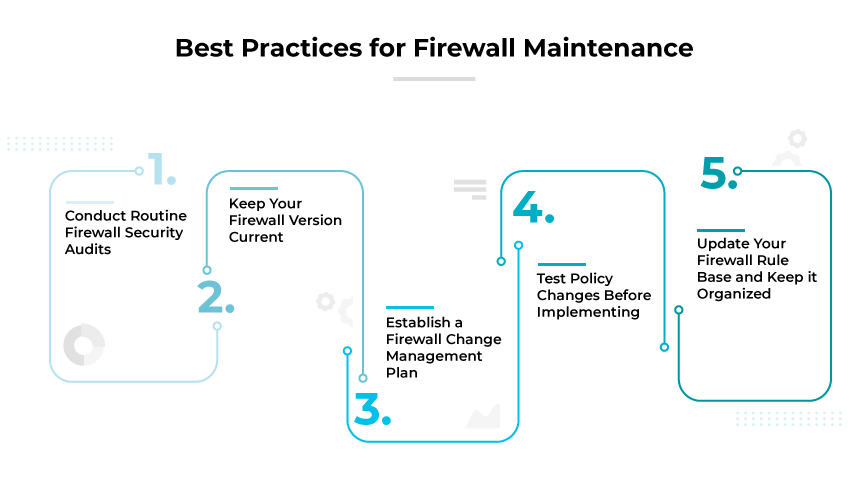
Harden and Configure Properly
Prior to deployment, it's imperative to patch and harden the operating system. By following configuration guidelines from both vendors and reputable third-party sources, like the Center for Internet Security, organizations can solidify their first line of defense.
Deployment Strategy
Firewalls serve as pillars in executing zero-trust security doctrines. Their role in regulating access over network boundaries with diverse settings cannot be understated—whether it's macro-segmented connections between networks or micro-segmented isolation within a network.
Enhance Firewall Security
Elevating firewall security involves multiple measures. It’s advisable to deactivate insecure protocols like telnet and SNMP, and if necessary, shift to secure configurations. Additionally, it's vital to maintain backups, monitor system changes, and keep abreast of known vulnerabilities.
Manage User Accounts
Security starts with user management. Default accounts and passwords should be altered promptly. By mandating multifactor authentication and stringent password regulations, coupled with role-based access controls, the risk of unauthorized access can be significantly mitigated.
Control Traffic and Access
By classifying and controlling traffic based on distinct categories, such as external, internal, or specific business units, a systematic and organized flow is maintained.
Maintain Compliance
Aligning policies with pertinent regulatory mandates is paramount. Often, this alignment necessitates the integration of auxiliary security mechanisms like VPNs, antivirus programs, and intrusion detection systems to ensure comprehensive protection.
Regular Testing
A proactive approach involves using tools for path analysis and verifying policy integrity. By routinely optimizing performance, not just based on functionalities but also on usage patterns, organizations can ensure efficient operations. Additionally, penetration testing is a valuable exercise to pinpoint vulnerabilities.
Routine Audits
To uphold integrity, confirming the currency of software and firmware, as well as the functionality of logs, is essential. Instituting a structured approach for policy modifications ensures that security is never compromised, even when adjustments are made.
Dig deep to ensure your knowledge is up to date about firewall best practices by reading our article, Key Firewall Best Practices.
What Is Firewall as a Service (FWaaS)?

Firewall as a Service (FWaaS) shifts typical functionalities from on-premises equipment to the cloud. FWaaS delivers the advanced network security features found in NGFWs. This includes traditional traffic inspection as well as intrusion prevention, application-specific policy enforcement, URL filtering, and advanced malware detection.
The transition to the cloud allows FWaaS to provide scalable security measures tailored to an organization's specific needs. By operating in the cloud, FWaaS eliminates the need for physical infrastructure, thereby reducing management and maintenance demands. This is especially valuable for organizations with a growing remote workforce or multiple office locations, as it ensures consistent security protocols regardless of where an employee is accessing the network.
By positioning itself between a network and connectivity to the internet, FWaaS examines incoming traffic to discern and counteract threats. This involves inspecting data packets' headers to ascertain their origins and potential malicious indicators. Some FWaaS solutions even offer deep packet inspection, which delves into the content of data packets, granting a more comprehensive understanding of potential threats.
Learn why organizations need Firewall as a Service (FaaS) by reading, What Is Firewall as a Service?
Comparing Firewalls with Other Security Technologies
Firewall vs. Antivirus

Firewalls are primarily tasked with monitoring and regulating data traffic in and out of a network, aiming to block unauthorized access. They can be both hardware and software-based and work at the network protocol level, making them crucial in thwarting unwanted intrusions.
On the other hand, antivirus software operates within computer systems, scanning files and programs for malicious elements such as viruses, worms, and trojans. By detecting, preventing, and eliminating these threats, antivirus tools play a pivotal role in safeguarding a computer system's integrity. However, one limitation is their inability to inspect read-only files.
While firewalls offer protection predominantly at the network level, antivirus solutions emphasize endpoint security. When deployed together, both tools provide a comprehensive defense against a wide range of cyber threats. Combining them ensures that both external and internal threats are addressed.
Discover the key differences between the functions of Firewalls and Antiviruses by reading, Firewall | Antivirus: What is the Difference?
Firewall vs. IDS

A firewall actively inspects and filters network traffic based on set rules. By analyzing the metadata of network packets, it determines which traffic should be permitted or denied, creating a barrier against undesired communication.
In contrast, an IDS is more of a watchful observer. It scrutinizes network traffic and looks for patterns or activities that align with known threats. Upon identifying such patterns, it raises an alert for cybersecurity personnel to act upon. An IDS does not intervene or block traffic; its primary role is detection and alerting.
In many modern cybersecurity solutions, these capabilities merge, offering both traffic filtering and threat detection in a single system.
History of Firewalls

Firewalls emerged in the late 1980s as a solution to safeguard internal company resources. The first ones, packet filtering systems, examined data packets' destination address, protocol, and port number. Traffic that did not adhere to a set of rules was either dropped or rejected.
The progression of technology led to the development of stateful firewalls. This new generation kept a record of computer connections, holding onto data packets to assess their state before deciding on their legitimacy. This ability to determine whether a packet was part of an existing or new connection simplified the filtering process.
The early 2000s saw a shift to Unified Threat Management (UTM) devices. Combining various security technologies, UTMs offered a single platform to provide multiple layers of protection. They integrated firewall, antivirus, intrusion prevention, and more. Although they consolidated multiple network security system technologies, the lack of native integration sometimes resulted in gaps in security, slower performance, and complex management.
In 2008, Next-Generation Firewalls (NGFWs) made their entrance, and Palo Alto Networks was instrumental in defining and pioneering this segment. Unlike UTMs, NGFWs provided by PANW and other vendors offered natively integrated capabilities. They emphasized the identification of traffic based on application, user, and content, and brought in features like intrusion prevention, web security, and encrypted traffic inspection. Importantly, Palo Alto Networks' NGFWs stressed the importance of user identity protection, highlighting that many security breaches involved compromised credentials.
The most recent advancement is the introduction of Machine Learning-Powered Next-Generation Firewalls (ML-Powered NGFWs) in 2020. These utilize machine learning to predict and counter threats in real-time. While the industry started adapting to ML-powered NGFWs, Palo Alto Networks was among the front-runners, leveraging machine learning to not only identify known threats and their variants but also detect anomalies in network behavior, providing tailored security recommendations.
In the context of the shift to cloud computing, cloud-based firewalls or Cloud-delivered security solutions have grown in prominence. Palo Alto Networks played a significant role here with their Prisma Access offering, providing cloud-native security solutions for organizations.
Firewall technology continues to advance, with the integration of machine learning and artificial intelligence marking notable milestones.
The Evolution of Firewalls: From Packet Filtering to Machine Learning-Powered NGFWs