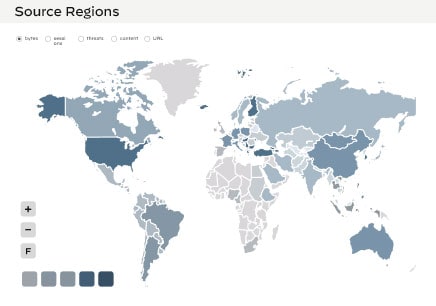
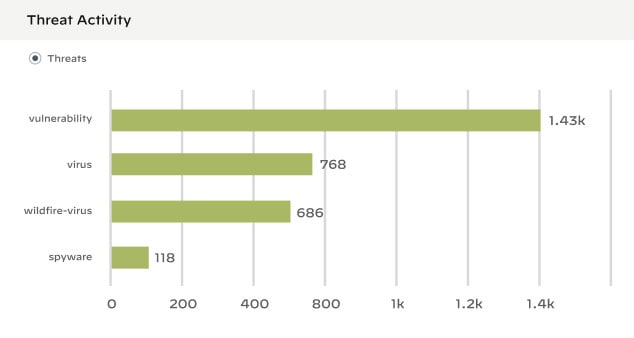
Stay ahead of the most complex threats with ML-powered, cloud-based network security
Leverage inline deep learning to stop unknown zero-day attacks. Our latest innovations go beyond signature-based detection to find the most evasive threats and stop them.
11-time industry leader
Our continued innovations consistently outperform the competition, establishing our products as best-in-class for the 11th consecutive time.
Don’t just react. Think ahead.
- 10
OF THE FORTUNE 100
- #1
IN NETWORK SECURITY
- 85K+
CUSTOMERS
Securing your network requires the right protection in the right place
Our NGFW platform protects your entire business, no matter the size or complexity. With a unified network security architecture and the ability to leverage deep learning in real time, our firewalls can help you see and secure everything.

Branch
Enable Zero Trust Network Security with simplified security for thousands of branch offices.
Enable Zero Trust Network Security with simplified security for thousands of branch offices.

Campus
Integrated capabilities protect your internal assets and the outside world, so your users can connect to data and applications anywhere.
Integrated capabilities protect your internal assets and the outside world, so your users can connect to data and applications anywhere.

Data Center
Get deep visibility and consistent, best-in-class security controls across physical, virtualized, containerized and cloud environments.
Get deep visibility and consistent, best-in-class security controls across physical, virtualized, containerized and cloud environments.

Public Cloud
Secure multiple public cloud environments with the same level of protection as on-premises data centers.
Secure multiple public cloud environments with the same level of protection as on-premises data centers.

5G Security
Leverage a simplified solution to protect all facets of your unique mobile network.
Leverage a simplified solution to protect all facets of your unique mobile network.
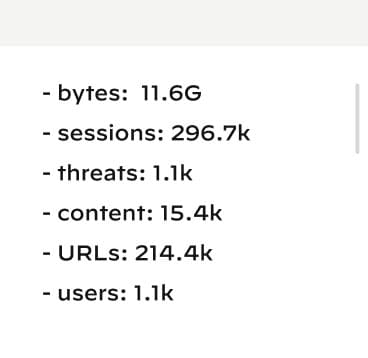
A single platform to see and secure everything

Best-in-class network security for AWS
Managed by Palo Alto Networks and easily procured in the AWS Marketplace, our latest Next-Generation Firewall is designed to easily deliver our best-in-class security protections with AWS simplicity and scale.
Cloud-Delivered Security Services
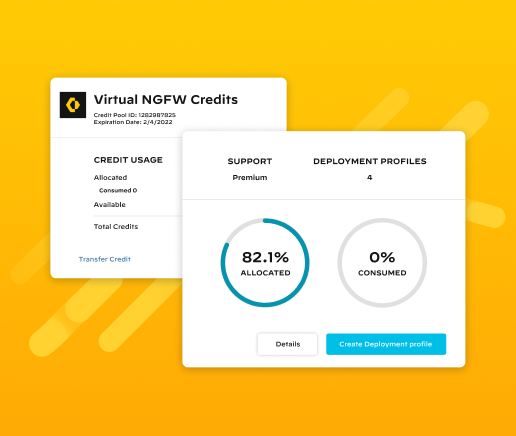
The virtual firewall built for cloud agility
Bring the world's most effective network security to any cloud or virtualized environment for the perfect balance of security, speed and versatility.
Cloud-Delivered Security Services
Protect Kubernetes® Containers
Protect inbound, outbound and east-west traffic between container trust zones and other workload types in Kubernetes environments – without slowing down the speed of development.
Cloud-Delivered Security Services
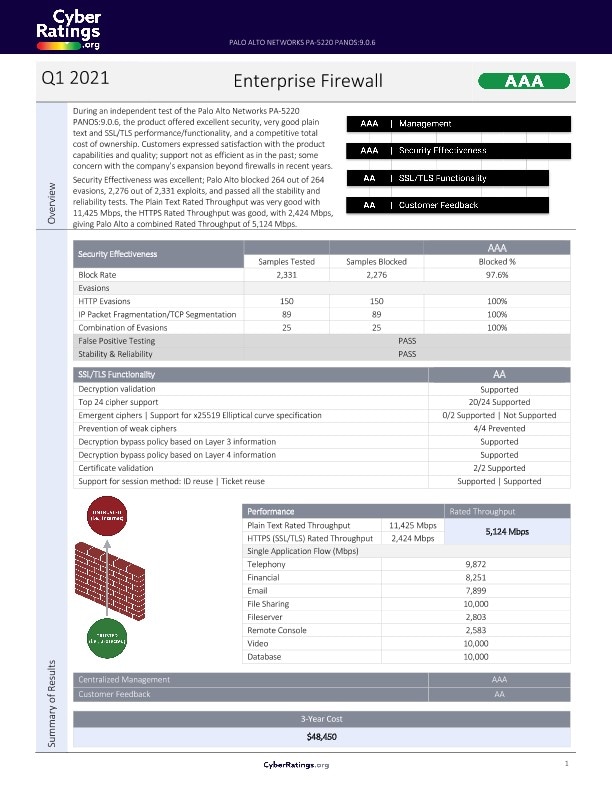
The most trusted Next-Generation Firewalls in the industry
Our flagship hardware firewalls are a foundational part of our network security platform. Automated and driven by machine learning, the world’s first ML-Powered NGFW powers businesses of all sizes to achieve predictable performance and coverage of the most evasive threats.
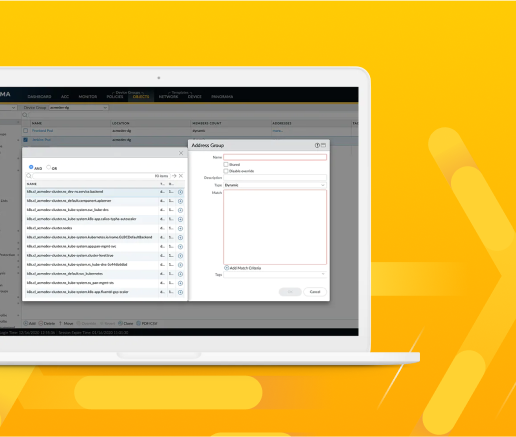
Get an inside look at what Panorama has to offer
With Panorama™, you can monitor, configure and automate security management all within an intuitive user interface.
14 years of industry firsts
From day one, we focused on creating dynamic firewalls to meet the needs of users and their applications. Since then, our commitment to innovation has grown with each product release.
First Next-Generation Firewall
Inline architecture with App-ID™- and User-ID™-integrated security for all types of apps and users
Cloud-Delivered Security Services
Seamless implementation of innovations, eliminating point products
Cloud-Delivered Sandbox
Integrated with a Next-Generation Firewall, leveraging customer community to enhance visibility and protection for everyone
Virtual Next-Generation Firewall
Scalable security for cloud or hybrid environments
Cloud-Delivered Next-Generation Firewall
Platform for easy-to-deploy protection across all users and apps
Containerized Next-Generation Firewall.
Native deployment leverages container context for seamless integration with no security gaps
ML-Powered Next-Generation Firewall
Fully integrated security with recommended Zero Trust policies and simplified deployment
Cloud-Delivered Enterprise Data Loss Protection
Integrates with Next-Generation Firewall to be easily accessible everywhere
IoT Solution Fully Integrated with Next-Generation Firewall
Fully integrated security with recommended Zero Trust policies and simplified deployment
In-Line ML-Based Web Protection
Advanced URL prevents unknown, evasive and targeted web-based threats in real time
SaaS Security Solution to Automatically Discover and Control Applications
Sees and secures new apps, protects data and prevents zero-day threats