VM-SERIES
The virtual firewall built for cloud agility
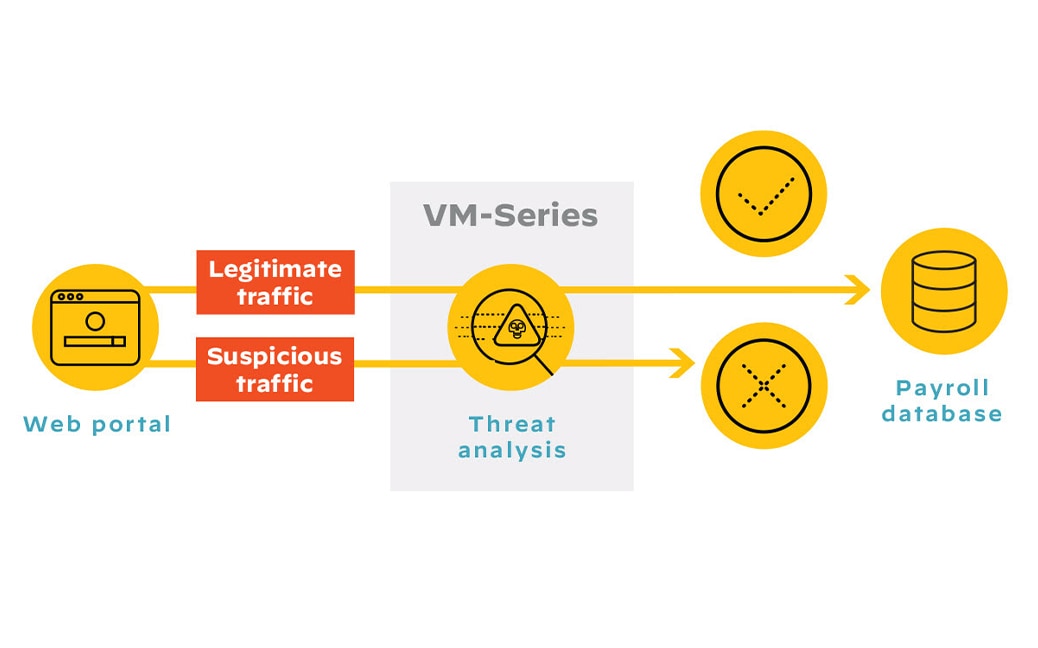
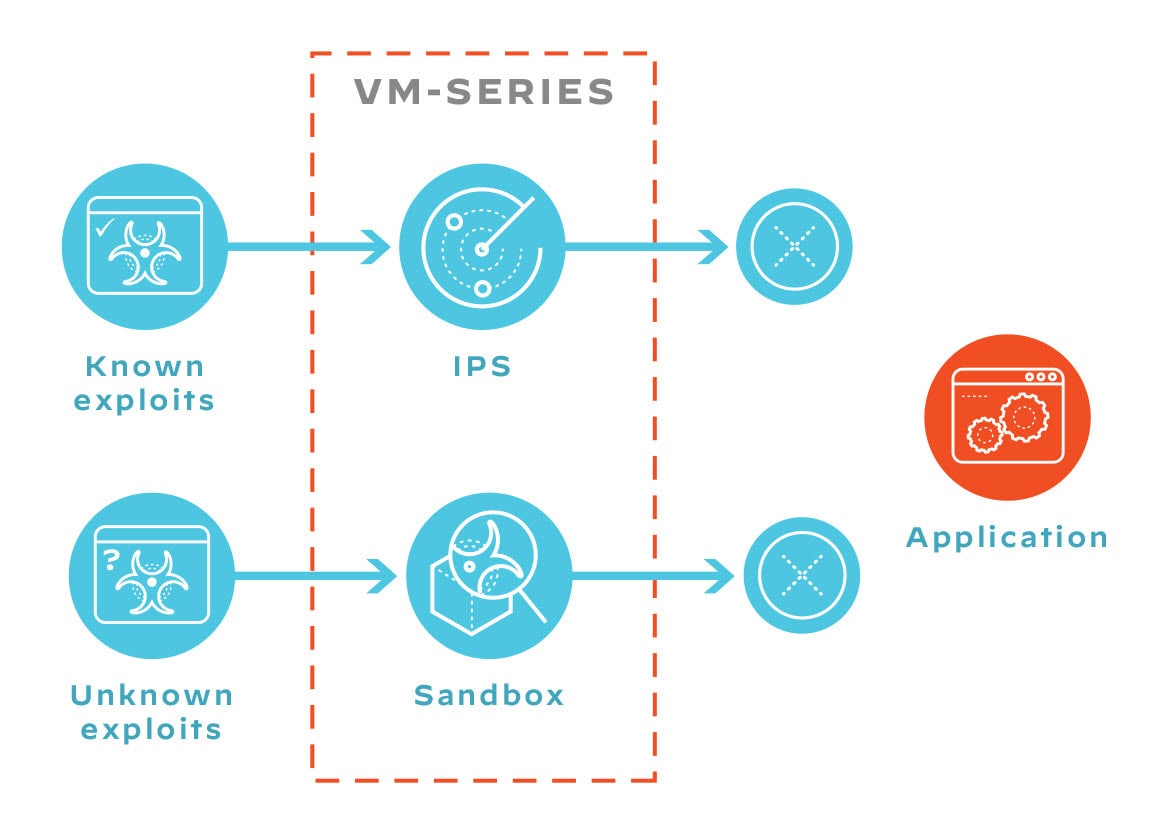
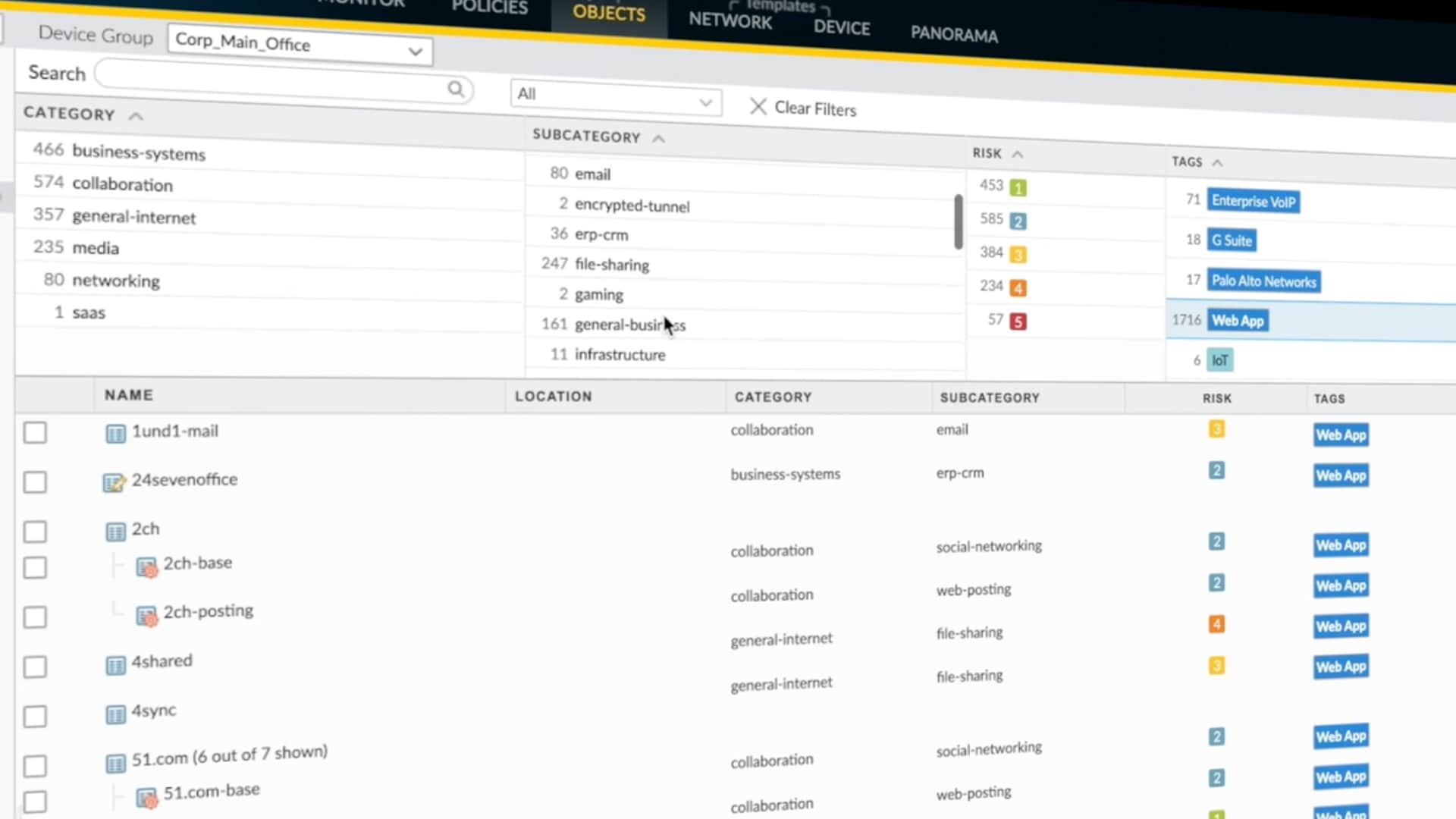
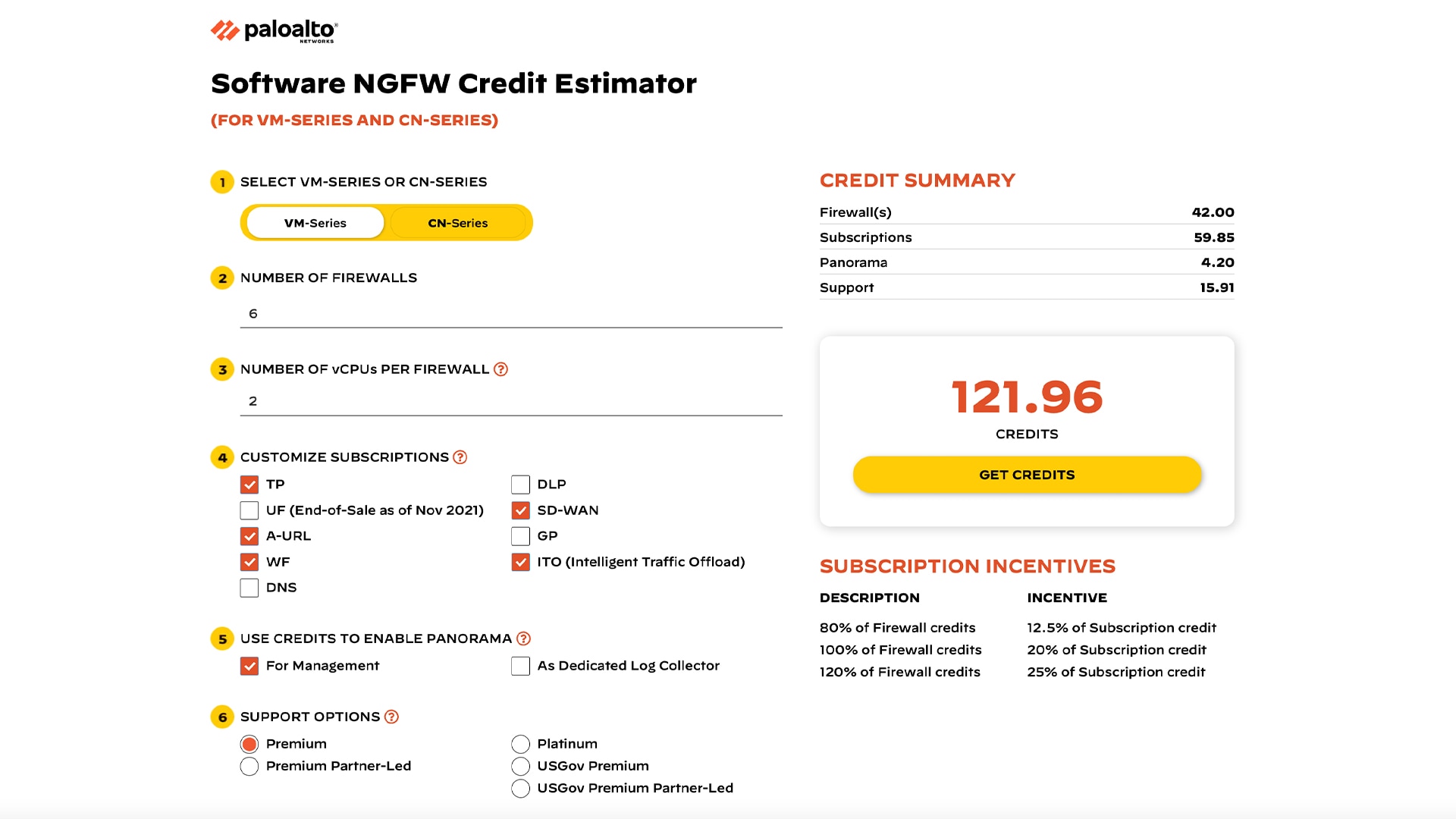
The industry’s leading virtual firewall brings the world's most effective network security to any cloud or virtualized environment. Find the perfect balance of security, speed, and value. The VM-Series stops evasive threats, reduces deployment time by 90%, and cuts downtime by nearly 70%.