As part of our ongoing botnet tracking and research, we have recently discovered a novel approach for detecting the presence of SpyEye in a network. Just in case you aren’t familiar, SpyEye is a rapidly growing banking botnet and a direct rival to Zbot a.k.a. ZeuS. In fact, the SANS reading room has a detailed analysis of how both bots work, and specifically the mechanisms that SpyEye uses to detect and remove ZeuS from an infected machine. http://www.sans.org/reading_room/whitepapers/malicious/clash-titans-zeus-spyeye_33393
The technique we established revolves around the ability to detect the SpyEye configuration file. SpyEye downloads the configuration file from the Internet, providing an opportunity to detect the bot as it traverses the firewall/IPS.
However, detecting the SpyEye configuration file is not a simple task. There are multiple versions of the configuration file and the files themselves are encrypted, making them extremely difficult for an IPS to detect.
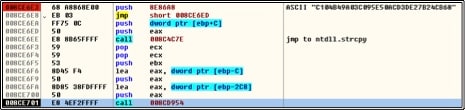
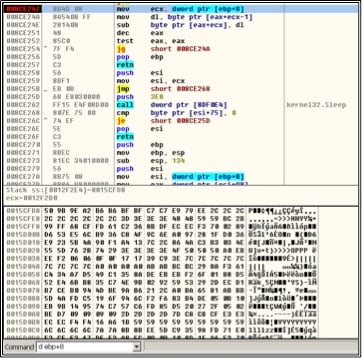
In order to solve this problem, we analyzed 3 different SpyEye configuration files. In each case, the team was able to reverse engineer spyeye samples to find both the encryption key and the location of the encrypted configuration file.
Determine the Key:
Location of the Configuration File:
Once this was established, the configuration file could be decrypted and analyzed. The configuration file was found to be a zip file, which was then opened for detailed inspection. By analyzing all three versions of the configuration file, the team was able to determine that the first 10 bytes of the configuration file are fixed (50 4B 03 04 14 00 09 00 08 00). Using this information, the team was able to craft a decoder and IPS signature capable of detecting the configuration file. This capability has been added as part of Palo Alto Networks regular content update released on 4/12/2011 and available to all Palo Alto Networks customers.