This is the third of a three-part blog series exploring the issues and challenges with consumerization and BYOD. In part 1 of this series, we examined the challenge of dealing with the scope and diversity of consumerization. In part 2 of this series, we took a closer look at why the network plays such an important role in making an effective strategy. In this segment, let’s take a closer look at how the next-generation firewall provides the means to assert control.
It’s clear that the network is the right place for IT to enforce control between applications and users, and that’s true regardless of what device is being used. What the traditional network lacks, however, is the control structure to address applications, users or devices as policy criteria. For example, the legacy firewall can’t make the determination of what applications, users and devices are on the network, even though it is in the right location for enforcement. A VPN might know who wants access to a network after asserting authentication credentials, but it has no idea how to tie identity to the firewall’s enforcement of what traffic may pass. Device identification and blocking methods range from the ineffective (such as MAC address filtering) to the impractical (such as network access control). And some controls for handling consumerization, such as identifying whether an application is being accessed from an IT managed asset (and thus permitted to locally store application data), are not addressed by any traditional network security product.
The next-generation firewall takes a fundamentally different approach towards traffic classification and policy enforcement. Using App-ID, User-ID and Content-ID as its core technologies, the next-generation firewall provides visibility and control in a manner not found in any combination of existing traditional network security products. To understand how this enforcement is possible, let’s revisit the scenario from the previous article, namely a company wants to protect a financial application in the data center, restricting access to accounting employees using an IT-managed endpoint. In addition, in order to reduce the risk of data breaches, the organization wants to make sure that this class of applications is only accessed from a managed, corporate-imaged endpoint with disk encryption, operating system patches, and up-to-date endpoint security signatures.
All of this can be done in a single policy in the next-generation firewall. That’s because that the next-generation firewall is using App-ID for application traffic identification rather than blindly trusting port assignments. It identifies the application traffic itself, rather than the port it uses, and as such, it can zero in on letting the specific financial application through while stopping the traffic that does not belong. With User-ID, the firewall policy incorporates users or group information from a corporate directory to determine who is a part of the accounting organization. Content-ID can check for the flow of inappropriate data (using a regular expression or predefined pattern matches for personally identifiable information) and stop dangerous or inappropriate traffic, such as malware.
GlobalProtect adds two important capabilities to address the dramatic impact that consumerization has on mobile computing. First, GlobalProtect provides the capabilities for endpoints and mobile devices to connect to the next generation firewall from anywhere. This combination provides both remote access and network security, ensuring that the firewall provides consistent enforcement of policy whether the user is on the local LAN or on the road. More specifically, location now becomes a policy enforceable element as well, allowing an organization to specify whether there are additional restrictions in place for external users. GlobalProtect has an extensive set of remote access capabilities that I’ll cover more in depth in a future blog post.
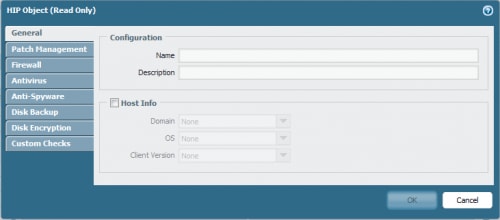
The second component added by GlobalProtect is the ability to use the state of the endpoint when evaluating firewall policy, whether connecting from an internal or external location. The client checks for the presence and state of various security features, and generates a Host Information Profile (HIP). The next-generation firewall uses this information as part of the policy evaluation. Going back to our example, this allows an organization to check for the presence of valid user on a properly managed endpoint before allowing network access to the application in the data center.
GlobalProtect pairs nicely with mobile device management (MDM) solutions from our partners, which include MobileIron and Zenprise. MDM can bring an unmanaged device to a managed state, and in the process, establish connectivity to GlobalProtect through the installation of an authentication certificate. If you want to learn more, MobileIron has a video that’s available to illustrate how the next-generation firewall works together with its mobile device management platform.
That concludes the three part series on the role of the next-generation firewall as it pertains to the issues of consumerization and BYOD, but consider this more of the starting point rather than the end. There’s still a lot more to talk about, on both policy, process, and tech, and I’ll be writing more about these topics in upcoming blog entries. In the meantime, if you’re interested in learning more about the impacts of consumerization, check out the webcast “Coming to Grips with Consumerization” with Nir Zuk and Rich Mogull.