One of the advantages of having an automated malware detection system with distributed nodes around the world is that you get to see a lot of malware.
But sometimes, something interesting stands out. That was the case when our research team discovered 42 samples of what we are now calling the “Jericho” botnet, which Bill Brenner from CSO blogged about the botnet this morning on his Salted Hash blog. Jericho is a variant of well-known banking Trojans such as the stealthy Jorik Trojan.
Jericho was detected by WildFire, our cloud-based analysis engine that was released late last year. WildFire detected more than 42 unique, but related banking botnet samples that were part of an ongoing criminal enterprise, aimed at stealing passwords and login credentials for financial institutions and other valuable sites. Disassembly of the samples revealed well over 100 domains that are targeted with the vast majority belonging to banking and financial sites. As a result, we believe that the core goal of this botnet is related to financial theft.
For those of you who don’t know, the WildFire feature of Palo Alto Networks next-generation firewalls allows the firewall to capture unknown files for analysis in a virtualized malware sandbox, where new malware can be identified based on over 80 different behaviors.
Jericho’s background is somewhat interesting: all infections were delivered from Israeli IP space, however the engineering of the file appears to be of Romanian origin. And there was actually a connection between the two: the vast majority of the URLs used to deliver the malware ended in ierihon(dot)com and Ierihon is the word for “Jericho” in Romania. Hence the name.
But what’s really interesting about Jericho is that like many other contemporary pieces of modern malware, Jericho demonstrates a number of behaviors that are designed for stealth, persistence and avoidance of traditional signature-based approaches to malware detection.
The malware is able to inject itself into the Windows logon to maintain persistence on the infected host after a reboot. What was a bit more interesting was just how efficient the malware was at injecting itself into valid applications such as Firefox, Chrome, Java, Outlook and Skype, and then repurpose their capabilities. This not only enables the malware to hide within approved applications during run time, but it also means that standard methods for observing Windows API calls are subverted. This allows for a more stealth presence in the system-- and can significantly slow down the study of the sample itself.
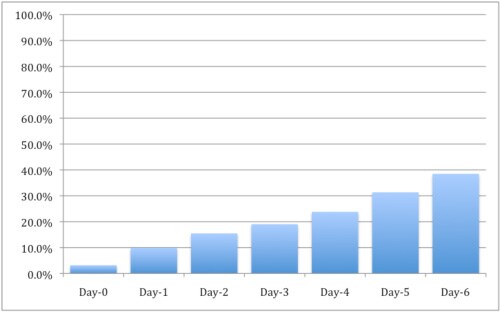
It appears that this combination of a stealthy program and piggybacking on common applications, and what was likely a rapid-iteration process of the malware writers, enabled this botnet to avoid the scrutiny of most antivirus vendors. In fact, Jericho demonstrated the ability to avoid industry AV signatures for multiple days. Of the 42 samples analyzed by Palo Alto Networks, the top AV solutions only achieved a 3.2 percent detection rate on the day the sample was first detected by WildFire. AV coverage seemed to slowly but steadily improve over time, with coverage improving to 39 percent over seven days. However this data is skewed by the fact that 12 of the 42 signatures were not detected at all over a seven-day span.
Poor Coverage of Jericho by Traditional AV Solutions
This trend seems to indicate that this particular criminal operation is cognizant of the AV coverage for their malware and has established a delivery strategy that minimizes collection by AV vendors, and refreshes the malware on a steady schedule to avoid newly released signatures.
Note that all Palo Alto Networks customers with a valid Threat Prevention license are already protected if they have applied the latest AV updates. WildFire is a free feature, and users benefit from protections from threats seen by all Palo Alto Networks customers worldwide.
I’ll be going in-depth on the “nuts and bolts” of the Jericho botnet in my next column for SecurityWeek.