This post is also available in: 日本語 (Japanese)
Today, as we publish our 2022 Unit 42 Ransomware Threat Report, we’re once again reporting that payments hit new records as cybercriminals increasingly turned to dark web “leak sites” where they pressured victims to pay up by threatening to release sensitive data.
A year ago, Unit 42 released its 2021 Unit 42 Ransomware Threat Report, which documented how cybercriminals had used the windfall profits generated from cyber extortion to transform themselves into massive criminal enterprises, some with near-nation state cyber capabilities. We warned that cyber extortion had reached crisis levels due to the wild success of a criminal business model known as ransomware as a service (RaaS).
Ransomware Groups and Trends in Demands and Payments
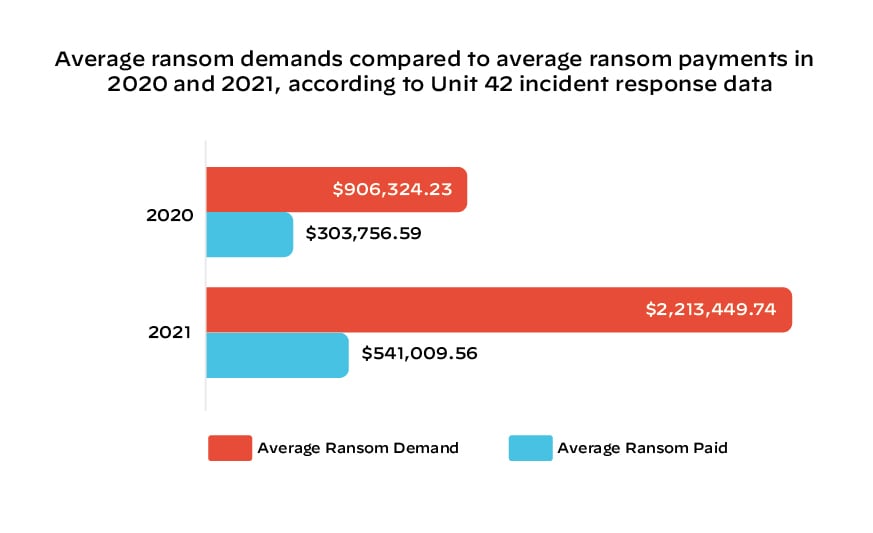
The average ransom demand in cases worked by Palo Alto Networks Unit 42 security consultants rose 144% in 2021 to $2.2 million, while the average payment climbed 78% to $541,010.
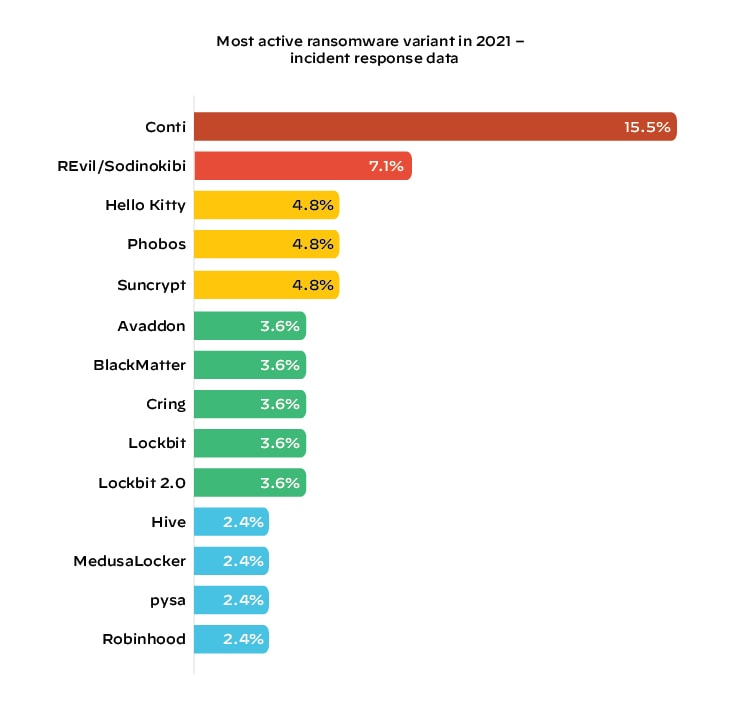
The Conti ransomware group was responsible for the most activity, accounting for more than 1 in 5 cases worked by Unit 42 consultants in 2021. REvil, also known as Sodinokibi, was No. 2 at 7.1%, followed by Hello Kitty and Phobos (4.8% each).
Dark Web Leak Sites and DDoS – Double and Multi-Extortion
For years, the main threat from ransomware has been that it would encrypt data on computers, making it impossible for organizations to use them to manage operations and retrieve critical information. That approach continued last year in some high-profile attacks that interfered with everyday activities that people all over the world take for granted – everything from buying groceries and purchasing gasoline for our cars to calling for emergency services and obtaining medical care.
But threat actors have evolved their techniques in recent years to include additional ways to coerce their victims into paying ransoms.
For example, in addition to holding data and access hostage, some ransomware groups engage in double extortion by using dark web leak sites to threaten to release sensitive information to the public. Some groups engage in further pressure tactics – they harass customers, bring down external websites or cause other harm.
That trend, known as multi-extortion, surged in 2021. The number of victims whose data was posted on those leak sites rose 85% in 2021 to 2,566 organizations, according to Unit 42’s analysis. 60% of leak site victims were in the Americas, followed by 31% for Europe, the Middle East and Africa, and then 9% in the Asia Pacific region. The most affected industries were Professional and Legal Services, Construction, Wholesale and Retail, Healthcare, and Manufacturing.
The 2022 Unit 42 Ransomware Threat Report
Our report also documents other key trends. It explains how RaaS groups are increasingly leveraging zero-day vulnerabilities to launch attacks, plus making their encryption malware faster and more difficult to defeat. It also describes how they’re using slick marketing campaigns to recruit affiliates and increasingly offering technical support to help victims get back online after they pay their ransoms.
Finally, the report outlines a series of best practices that organizations can use to address the threat of ransomware – whether preparing for a possible ransomware attack or facing the impact of an attack that’s already underway.
Download the full 2022 Unit 42 Ransomware Threat Report to learn more, and register to attend the 2022 Unit 42 Ransomware Threat Report Webinar live to hear our security experts discuss the key findings in the report.
Get in Touch
Want to be prepared for a ransomware attack? Call in the experts.
If you think you may have been impacted by a ransomware attack, please contact Unit 42 to connect with a team member. If you have cyber insurance, you can request Unit 42 by name. The Unit 42 Incident Response team is available 24/7/365. You can also take preventative steps by requesting a Ransomware Readiness Assessment.