APIs (application programming interfaces) have been around for decades. They are the default medium for exchanging information between systems and applications. With the more recent emergence of cloud-native applications (architected and built with interconnected services that rely on APIs) APIs have become ubiquitous – the roads and highways of our online world and integral to many services we now rely on.
Why Attackers Are Targeting APIs
Developers are taking an API-first approach to building applications, tools and processes. But, as developers build, manage, publish and leverage APIs for applications, security teams are often ten steps behind in terms of understanding how to secure the APIs from risks inherent to their unique configurations and use.
Hackers are aware of this lag. The lack of security controls, coupled with the increase in API usage and traffic, have made APIs a prime target for bad actors hunting for vulnerabilities and API misconfigurations to access the valuable data and resources within applications.
The recent Optus breach that exposed 10 million customer accounts, for example, involved an internet-facing API that didn’t require authorization or authentication to access customer data. It’s that simple.
Or is it that simple?
Knowing which APIs are in your cloud workloads is complicated, particularly in view of the pace of cloud-based application development. Dev teams commonly find keeping track of new and changed APIs near impossible. What’s more, application complexity leads to misconfigurations, as well as unmanaged and unsecured APIs that create vulnerabilities. In fact, Gartner predicts that by 2025, less than 50% of enterprise APIs will be managed.
Many API gateways and monitoring solutions are unable to identify risk or protect against OWASP Top 10 attacks on APIs. Adding another tool to address API security only increases cost and complexity for security and development teams.
The Prisma Cloud Approach to API Security
Prisma Cloud provides complete API discovery, risk profiling and real-time protection for all APIs as a part of its comprehensive cloud native application protection platform (CNAPP).
API Security capabilities:
- API Discovery: Auto-discover all APIs in your environment and eliminate blind spots caused by shadow or rogue APIs.
- API Risk Profiling: Identify API risks, risk factors (based on risk factors, such as misconfiguration, exposure to sensitive data and access control), and prioritize remediation.
- Real-Time Protection: Enforce real-time protections for attacks across OWASP Top 10 for APIs, rate limiting and bad bots.
The saying that the whole is greater than the sum of its parts applies to platform products. Point solutions, as disconnected parts, often create more work and result in problems relating to limited visibility.
With API security baked into Prisma Cloud’s Code-to-Cloud CNAPP, we are providing better security with fewer tools. Organizations get holistic security for APIs, applications, workloads and infrastructure in a single solution.
API Discovery
You can’t protect what you can’t find. Lacking API documentation creates obstacles for security teams that don’t understand why APIs are being used. Information on the APIs you have running is critical to protecting them from abuse. As you map this landscape, it’s important to find all API communications and gather as much information as possible about shadow APIs and rogue APIs.
API discovery is the first step to securing your APIs. Prisma Cloud provides an automated API discovery capability for all APIs, including both north/south APIs (internet to microservices) and east/west APIs (microservice to microservice). Users are able to export data as an OpenAPI specification, which can be used as a baseline for API protection.
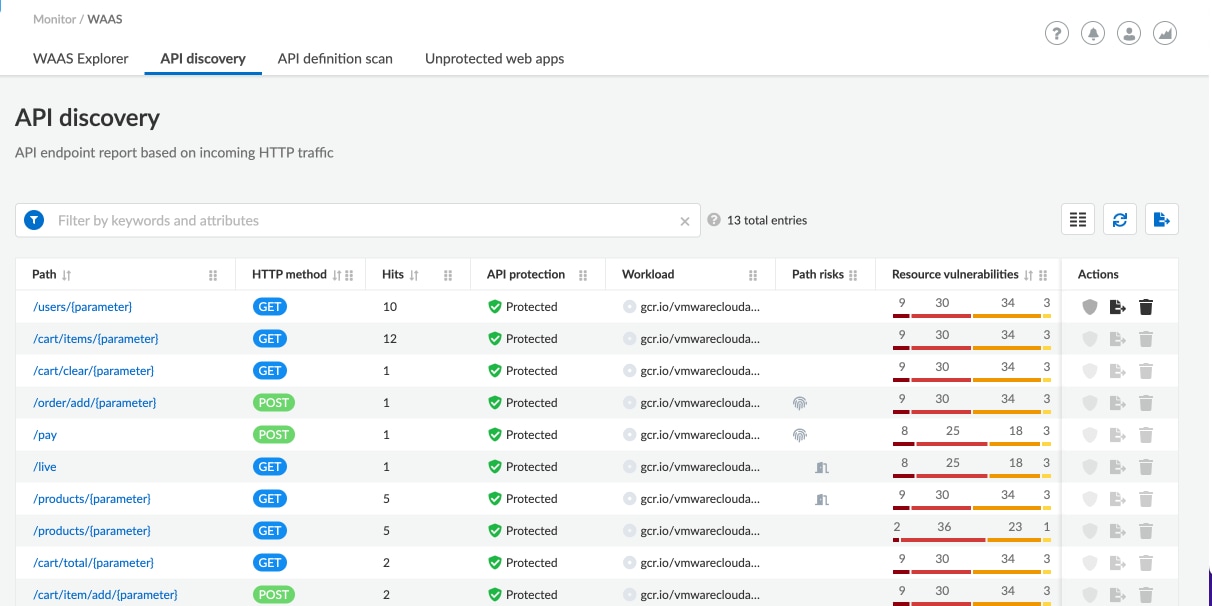
API Observations and Security Teams
Each API endpoint poses a different risk to the application and its data. Various factors contribute to the total risk, and each factor has its own weight, such as exposure to sensitive data, missing authorization and access control. Security teams need visibility into all risk factors associated with APIs and the underlying workload to prioritize risk and take proactive measures.
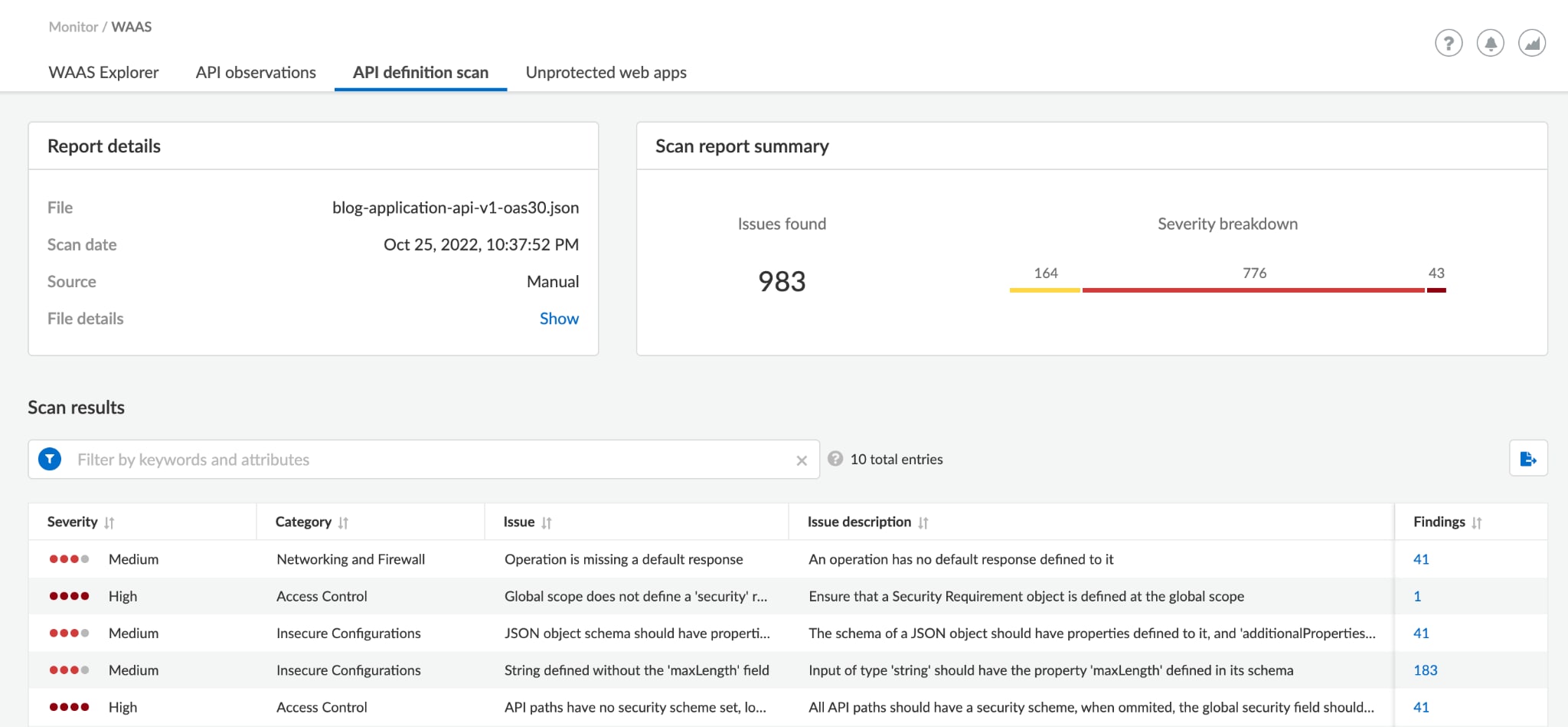
Prisma Cloud helps teams identify API risks, risk factors and prioritize remediation. With API definition file scanning during development and build time, developers can prevent API misconfigurations, improper structure and schemas before they reach production.
Real-Time Protection
The OWASP Security Project states that “API Security focuses on strategies and solutions to understand and mitigate the unique vulnerabilities and security risks of Application Programming Interfaces (APIs).” But, many API security solutions claiming to offer real-time or run-time protection for APIs only provide visibility. And, visibility without protection isn't security.
In an ideal world, API security starts when the API is being built and continues through runtime. Prisma Cloud is proud to offer real-time protection for your APIs against attacks across OWASP Top 10 for APIs, as well as rate limiting, bad bots and more.
Additionally, we offer customizable rules, so teams can tailor rules to their specific scenarios and environment. Users can also enable virtual patches that our threat research team creates for known vulnerabilities, allowing you to patch the application and giving your team time to fix the vulnerability.
Winter Release Updates
Prisma Cloud continues to raise the bar for API security as it leads the charge for Web Application and API Security (WAAS) as a part of the industry’s most complete cloud native application protection platform (CNAPP). This winter, Palo Alto Networks released more features to help organizations secure their APIs with confidence. These innovations are now available in Prisma Cloud and include much more:
API Risk Profiling
Due to the speed of application development, it's challenging without automation to track risks associated with APIs. API Security, though, starts with full insight into the risk APIs pose across cloud environments.
Prisma Cloud’s winter release enhances API security capabilities with API risk profiling. This new feature helps teams understand and prioritize risk based on 200+ factors for all APIs in your environment. Now you can minimize your API attack surface and manage protection based on risk factors, such as misconfigurations, exposure to sensitive data and lack of authentication.
Auto-Apply Virtual Patch
Today, teams have visibility into vulnerabilities found in packages used by the application. A mitigation for such vulnerabilities requires time since the vulnerable packages must either be replaced or patched and then tested before being deployed. Until the vulnerable code is patched, the environment is exposed to exploitation.
In the past, we offered virtual patches for known vulnerabilities to help secure the application while the application owner patched the vulnerability. This gave the security team peace of mind while the development team made the fix in the code.
With our winter release, you can now automatically protect web applications and APIs against vulnerabilities. Using the vulnerability mapping of each workload, WAAS will automatically adjust its traffic inspection policies to detect and block remote HTTP-based exploits.
Learn More About API Security With Prisma Cloud
Prisma Cloud’s API Security capabilities help you secure your APIs with confidence to safely harness the power of APIs. Discover the Prisma Cloud advantage today by signing up for a free trial.