Unifying Data Security: Why DLP, DSPM, and DDR Must Converge
Here is a question I ask every CISO I meet: Do you know the real-time location of your sensitive data? I'm not asking theoretically or based on last quarter's audit, I mean right now, across every cloud, SaaS app, endpoint, email and AI pipeline your teams use. The honest answer, almost universally, is no. The root cause isn't a failure of staffing or budget; it's an architectural flaw, and one that the security industry helped create.
For the past decade, we built data security in layers. Each layer solved a real, discrete problem: for example data security posture management (DSPM) to discover and classify where data is stored at rest, data loss prevention (DLP) to detect sensitive data and protect it across egress points and communication channels, solutions like behavioral analytics to flag anomalous user activity around data, and so on. We treated them as separate investments, with separate vendors, disparate data models, and disconnected policy engines. The result is a fragmented approach to data security, where each solution sees only part of the picture. Without full context across how data is accessed, stored, used, and moved, information security teams manually monitor isolated alerts, making it difficult for them to fully protect data across its entire lifecycle.
This gap isn’t a minor operational inconvenience but precisely where the most consequential breaches occur.
The Cost of Silos We Built Ourselves
I want to be precise about the operational toll of this fragmented approach. Most organizations running enterprise data security have invested substantially. Starting with a DLP platform to detect and protect sensitive data across disparate channels and use cases. Over time, however, DLP policies have become increasingly complex, inconsistently applied, and prone to high volumes of false positives. In parallel, teams have added DSPM tools for data discovery in cloud storages—often covering only a subset of their cloud estate. They have also deployed behavioral monitoring solutions that generate risk alerts security teams cannot fully triage. The result is mounting operational overhead, with fragmented tools producing more noise than actionable insight.
The issue is not the quality of these individual components, but their failure to communicate and cooperate. Consider a single risk scenario: First, your DSPM identifies a critical misconfigured storage bucket containing sensitive customer PII. That finding is locked in one dashboard. Your DLP engine, which enforces your egress policies, has no real-time context on this newly discovered risk location. Separately, your behavioral tool flags an analyst accessing an unusual volume of files. Without the data context from DSPM and DLP, this is a generic alert; the analyst cannot tell if the activity involves benign test data or the newly exposed PII.
Three tools mean three alert queues and a fragmented, incoherent picture of a potential incident. The analyst is left to manually stitch together the pieces, correlating siloed alerts and separate data models, resulting in a time-consuming process that occurs after the risk has materialized.
This architectural debt is now an existential vulnerability, because the environment these tools were designed to protect no longer exists.
The Vanishing Perimeter and The Rise of Machine Speed
The enterprise data security premise used to be that data had a shape. It lived in databases and file servers, it moved through email and web browsers, and it was created and consumed by employees working from a set of managed devices. You could draw a perimeter around most of it.
The perimeter-based premise is gone. Data today is created faster than any inventory process can track, distributed across dozens of SaaS applications and cloud environments, and increasingly accessed not by humans but by AI systems, automated pipelines and agentic workflows operating at machine speed and scale.
Consider what this means in practice. A sensitive document can originate in a cloud data store, be retrieved by an AI agent as part of a workflow, flow through a third-party SaaS integration, and end up in an output that leaves the organization within minutes. All this across channels that no single tool was designed to monitor end-to-end. Furthermore, the average enterprise now has machine identities outnumbering human ones by more than 80 to one. I raise this not to alarm, but because the arithmetic of disconnected data security simply does not work in this environment. The sheer volume, the diversity of channels, and the speed of movement have outpaced what three separate systems, each operating on its own logic, can possibly address.
A Platform Built Around the Data, Not the Perimeter
The right response to this is not another point product. It is a platform that treats DSPM, DLP, and data detection and response (DDR) as three expressions of the same underlying capability. It understands where sensitive data lives and prevents unauthorized movement. By using behavioral analysis across all relevant context, it can accurately detect and respond to issues before any damage occurs.
These capabilities are only meaningful when they share a foundation. Data posture and classification that lives in your DSPM but does not flow into your DLP policies and enforcement means you are writing policies against a data inventory that does not match reality. Behavioral alerts that fire without data context mean your analysts are investigating anomalies without knowing whether anything of consequence was actually touched. Compliance reporting that requires manually assembling evidence across three systems describes your posture months ago, not today.
The picture changes substantially when these capabilities share a common data model that provides a single live inventory of what exists, where it is, who can reach it, and how it is actually being used. Classification happens consistently and propagates to enforcement automatically. A behavioral signal that would have been a low-priority alert in an isolated system becomes a high-confidence incident when correlated with real-time data access context. And compliance becomes a continuous operational output rather than a quarterly exercise.
This convergence matters specifically for the AI era. If your data security architecture cannot see what AI systems are accessing, classifying, or generating or if it has no visibility into the data flowing through agentic workflows or AI-connected applications, then a significant and growing portion of your sensitive data has effectively no protection at all. That is not a theoretical future risk. It describes most enterprises today.
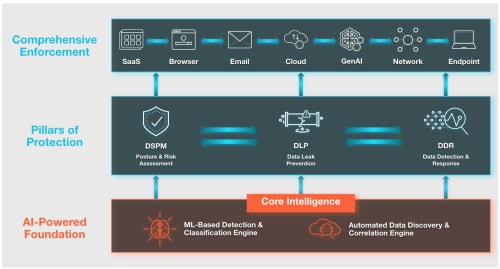
Figure 1: Palo Alto Networks’ Unified Data Security Vision
Our Vision for a Unified Data Security Solution
At Palo Alto Networks, we are deliberately building toward a unified architecture. We recognize that the most persistent failure modes in enterprise data security stem from coverage gaps, where enforcement is handled by disparate systems with different rule sets and classification logic.
Our strategy focuses on bringing these essential capabilities together. Enterprise DLP runs natively within our network security and Prisma SASE platform. It provides comprehensive protection of sensitive data wherever it lives and travels, across SaaS, AI tools, cloud, web, email, endpoints, browser, and private access channels. Crucially, our approach eliminates the coverage gap using a single policy engine for consistent enforcement across all channels.
Our DSPM capabilities drive enforcement with continuous data discovery and classification across cloud environments as part of the same platform and not as a separate product requiring separate administration. When DSPM finds something new, enforcement knows about it. The inventory is live.
Finally, by leveraging user and entity behavior analytics (UEBA), we are developing the DDR component necessary to connect posture and enforcement to real-time response. This allows the platform to better distinguish between unusual developer activity and an actual exfiltration attempt by correlating behavioral signals with data access context.
Our vision is a converged platform where classification, enforcement, and behavioral detection operate from a shared data layer.
For years, the industry has pushed a "best-of-breed" model—buying separate DSPM and DLP tools and attempting to manually integrate them. While individual tools can be excellent at specific tasks, they often produce alert fatigue and manual correlation work that creates windows for adversaries to exploit.
We believe the future of data security requires an architecture that matches the reality of how data actually moves. Our focus is on delivering a platform where DSPM, DLP, and DDR are not separate silos, but a single, coherent investment in protecting your most critical assets. We have built the foundation, and we are continuing to unify these defenses to meet the speed of the AI era.
Ready to see how we are securing the future? Explore how we are securing the agentic enterprise with a unified SASE platform.
Forward-Looking Statements
This blog contains forward-looking statements that involve risks, uncertainties and assumptions, including, without limitation, statements regarding the benefits, impact, or performance or potential benefits, impact or performance of our products and technologies or future products and technologies. These forward-looking statements are not guarantees of future performance, and there are a significant number of factors that could cause actual results to differ materially from statements made in this blog, including, without limitation: developments and changes in general market, political, economic, and business conditions; risks associated with managing our growth; risks associated with new products and subscription and support offerings; shifts in priorities or delays in the development or release of new offerings, or the failure to timely develop, release and achieve market acceptance of new products and subscriptions as well as existing products and subscription and support offerings; failure of our business strategies; rapidly evolving technological developments in the market for security products and subscription and support offerings; our customers’ purchasing decisions and the length of sales cycles; our competition; our ability to attract and retain new customers; and our ability to acquire and integrate other companies, products, or technologies. We identify certain important risks and uncertainties that could affect our results and performance in our most recent Annual Report on Form 10-K, our most recent Quarterly Report on Form 10-Q, and our other filings with the U.S. Securities and Exchange Commission from time-to-time, each of which are available on our website at investors.paloaltonetworks.com and on the SEC's website at www.sec.gov. All forward-looking statements in this blog are based on information available to us as of the date hereof, and we do not assume any obligation to update the forward-looking statements provided to reflect events that occur or circumstances that exist after the date on which they were made.