This post is also available in: 日本語 (Japanese)
Executive Summary
In the past week, multiple vulnerabilities affecting the Spring Framework have been disclosed to the public. Among four vulnerabilities released since the beginning of March, CVE-2022-22965, which was uncovered on March 31, 2022, had the most critical impact and was dubbed SpringShell.
The SpringShell vulnerability allows attackers unauthenticated remote code execution (RCE) to affected systems. A full analysis of the SpringShell vulnerability can be found in the Unit 42 Threat Brief.
Prisma Cloud can detect all recent SpringShell vulnerabilities across all cloud assets. In addition to detecting affected instances, Prisma Cloud can prevent and stop the execution of vulnerable container images. Prisma Cloud is also able to prevent exploitation of the vulnerabilities with different capabilities as well as post-exploitation techniques.
Background
The Spring Framework is an open-source and comprehensive application framework for the Java Platform. It is widely used in the industry due to its powerful features and ease of use. The Spring Core component is the core of the framework that provides powerful features such as Inversion of Control and dependency injection. It contains core, beans, context, and the Spring Expression Language (SpEL) modules.
The Spring Cloud Function is a project that is designed to promote the development lifecycle of business logic and support uniform programming models across serverless providers. Where the Spring Expression Language (SpEL) supports the querying and manipulation of an object at runtime, using a Unified EL which includes method invocation and basic string templating functionality.
Since the beginning of March, there have been a total of four CVEs published pertaining to the Spring Framework:
- CVE-2022-22947 - Spring Cloud Gateway - Remote Code Execution
- CVE-2022-22950 - Spring Expression Language (SpEL) - Denial of Service
- CVE-2022-22963 - Spring Cloud Function - Remote Code Execution
- CVE-2022-22965 - Spring Core - Remote Code Execution
Prisma Cloud Detection Capabilities
Prisma Cloud users can detect software components affected by either of these two vulnerabilities, CVE-2022-22963 or CVE-2022-22965. The Prisma Cloud Intelligence Stream (IS) automatically updates to include the vulnerability information from official vendor feeds. This allows Prisma Cloud to directly reflect any updates or analysis by Linux distribution and application maintainers, allowing Prisma Cloud to detect any affected functions, images, and hosts.
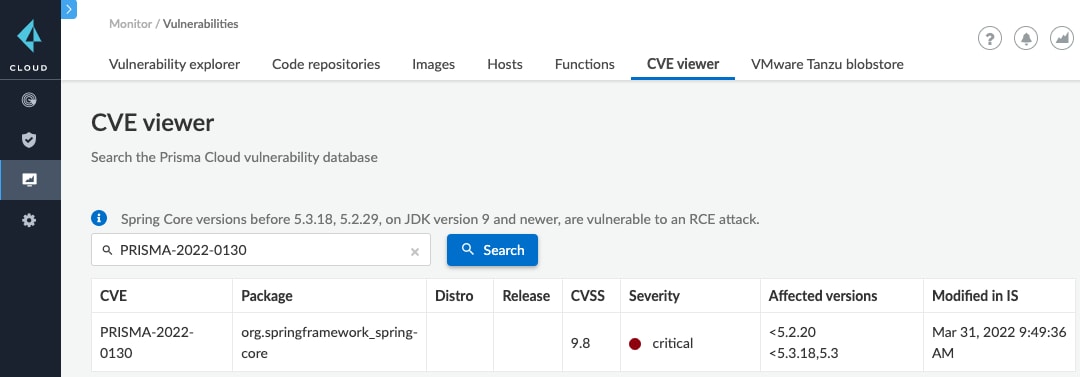
Prisma Cloud also employs the use of PRISMA IDs which contain a curated set of industry-known vulnerabilities affecting systems and applications, but which have not been, or not yet been, assigned CVE tracking numbers. Vulnerabilities that are industry known but have yet to be assigned a CVE tracking number are analyzed by Prisma Cloud’s Cloud Security Research Team (CSRT) and then added to Prisma Cloud’s IS. With PRISMA-IDs to track industry-known vulnerabilities, Prisma Cloud can push vulnerability detection rules to client environments in short order, often times faster than CVE publications are released to the public.
Case in point, the SpringShell vulnerability (CVE-2022-22965) is one such example of Prisma IDs rules providing vulnerability detections at a faster rate than public CVE publications. The SpringShell CVE (CVE-2022-22965) was published on March 31, 2022, however, Prisma Cloud’s CSRT published the Prisma ID rule ‘PRISMA-2022-0130’ on March 30, 2022. This equates to clients of Prisma Cloud’s Cloud Workload Protection (CWP) module being capable of detecting CVE-2022-22965 hours prior to the official vulnerability release.
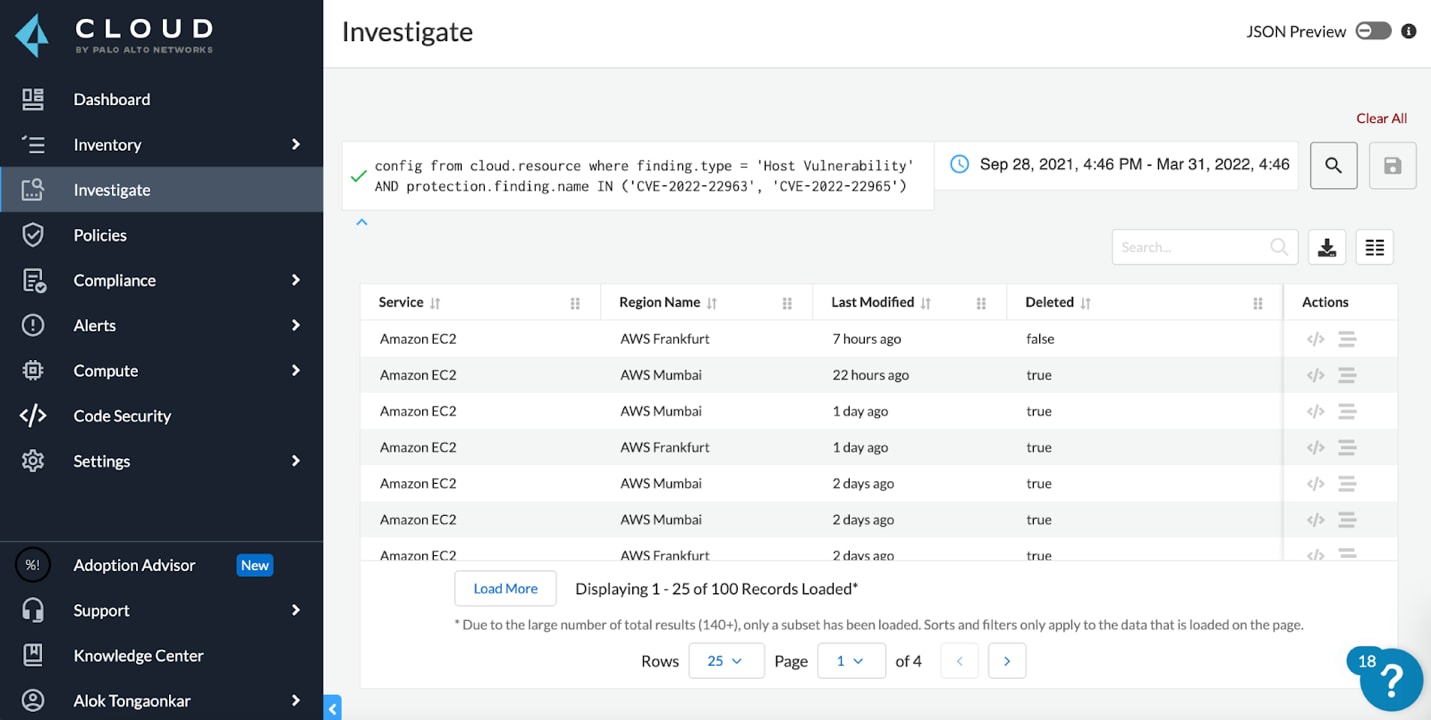
Query Your Environments for Hosts with This Risk
Prisma Cloud’s RQL (Resource Query Language) provides a quick and easy way to query for resources impacted. In this case, users can utilize the Prisma platform's capabilities to isolate assets with vulnerabilities and prioritize them further by looking for internet-exposed assets receiving traffic.
Know the hosts in your cloud that have the specific vulnerability CVE-2022-22963 or CVE-2022-22965:
config from cloud.resource where finding.type = 'Host Vulnerability' AND finding.name IN ('CVE-2022-22963', 'CVE-2022-22965')
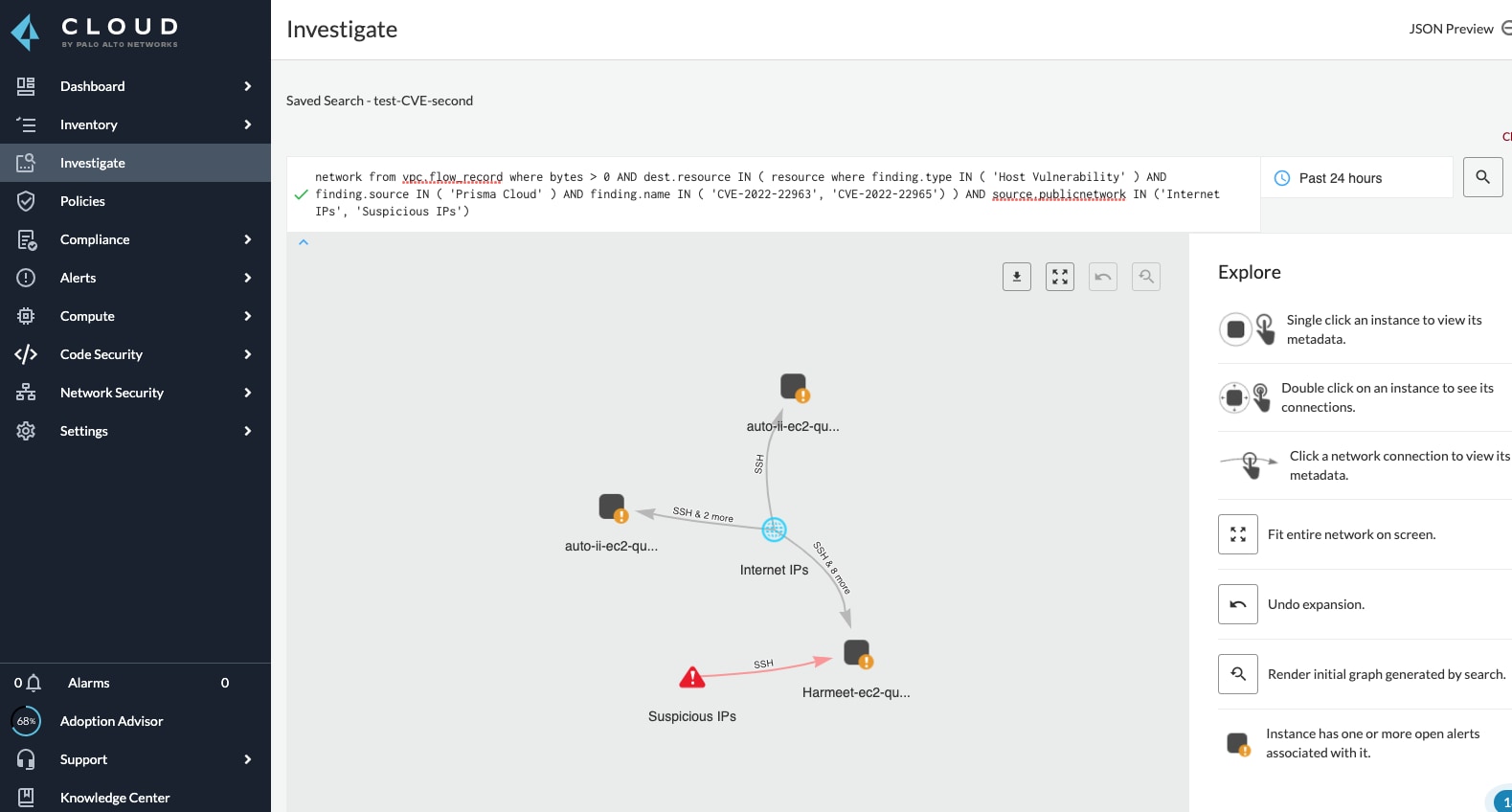
Know the Internet exposed hosts that are receiving traffic in your cloud and have the specific vulnerability CVE-2022-22963 or CVE-2022-22965:
network from vpc.flow_record where bytes > 0 AND destination.resource IN ( resource where finding.type IN ( 'Host Vulnerability' ) AND finding.source IN ( 'Prisma Cloud' ) AND finding.name IN ('CVE-2022-22963', 'CVE-2022-22965') ) AND source.publicnetwork IN ('Internet IPs', 'Suspicious IPs')
Prisma Cloud users with WAAS enabled are protected from the majority of exploits we analyzed for SpringShell (CVE-2022-22965) by the App Firewall Code Injection detection feature.
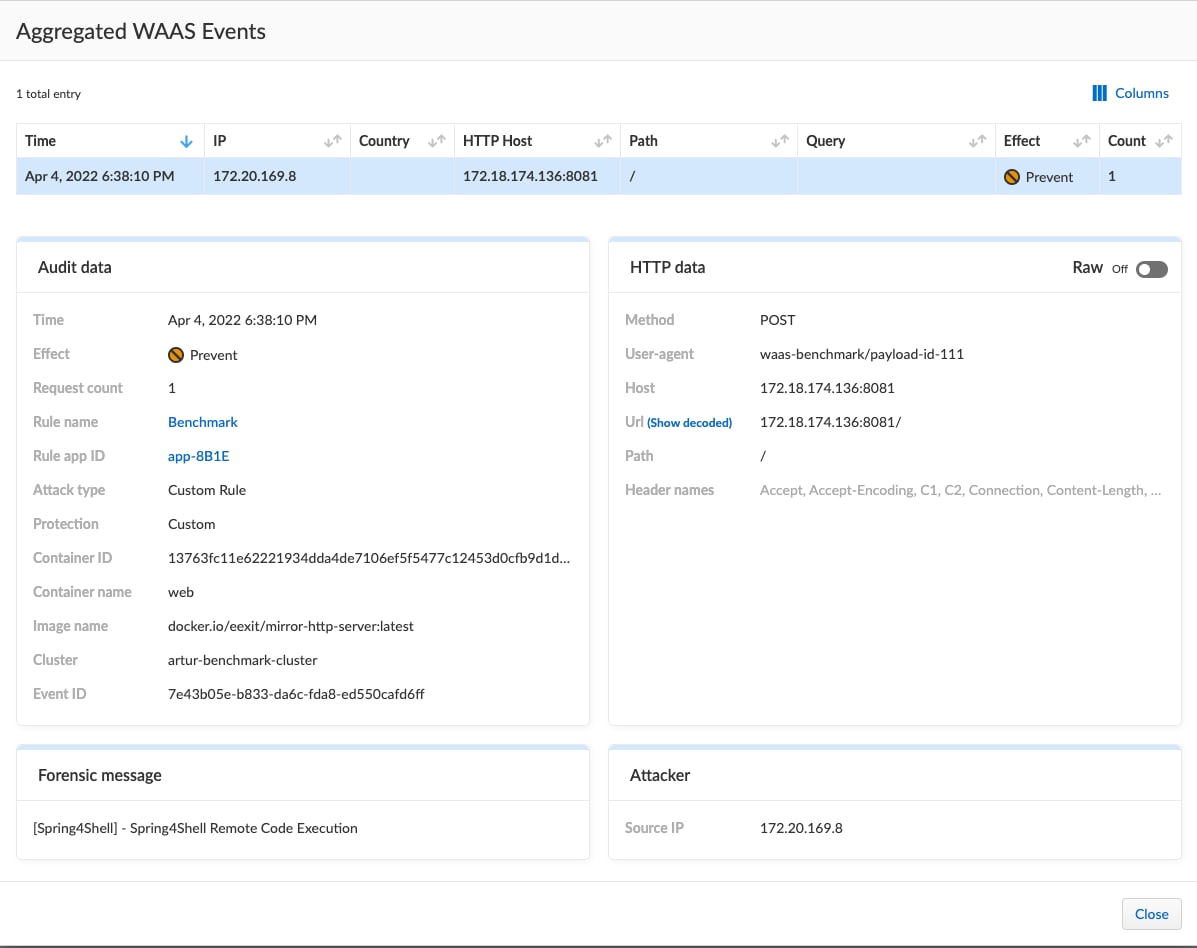
Custom rule was created to more accurately cover CVE-2022-22965 (Spring4Shell) and CVE-2022-22963 (Spring Cloud Function) including their bypasses, users with WAAS enabled may import the following new custom rules for protection:
Rule compatible for WAAS version 22.01.839 and above:
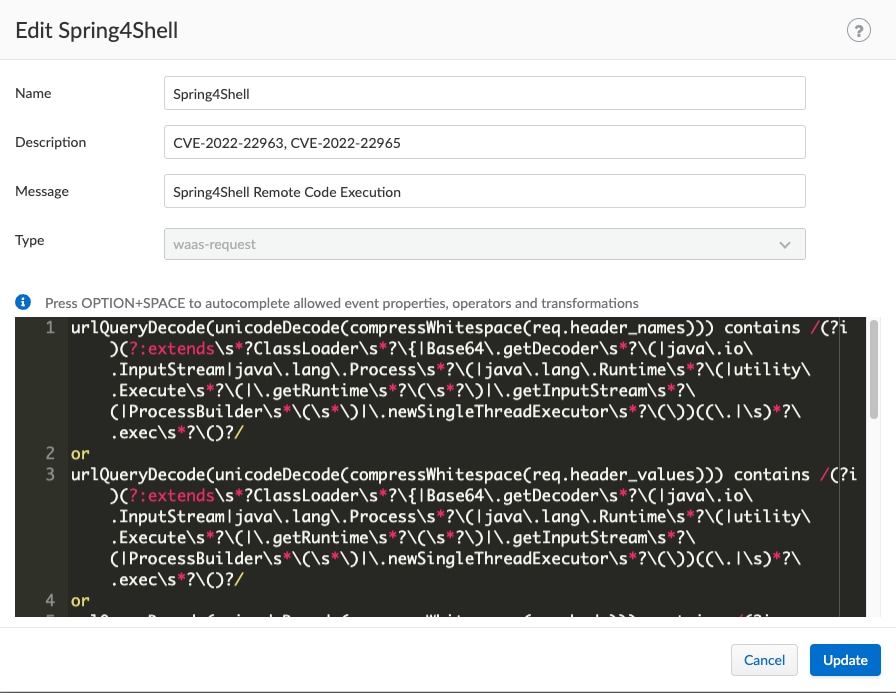
urlQueryDecode(unicodeDecode(compressWhitespace(req.header_names))) contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
urlQueryDecode(unicodeDecode(compressWhitespace(req.header_values))) contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
urlQueryDecode(unicodeDecode(compressWhitespace(req.body))) contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
urlQueryDecode(unicodeDecode(compressWhitespace(req.body_param_values))) contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
urlQueryDecode(unicodeDecode(compressWhitespace(req.query_param_names))) contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
urlQueryDecode(unicodeDecode(compressWhitespace(req.query_param_values))) contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
Rule compatible for WAAS version 21.08.525 and above:
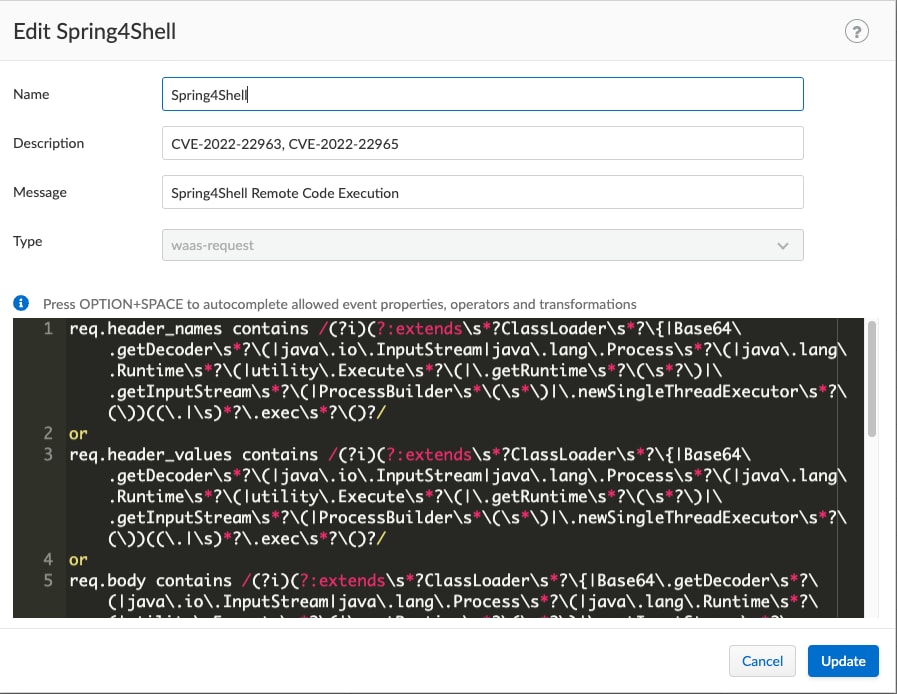
req.header_names contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
req.header_values contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
req.body contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
req.body_param_values contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
req.query_param_names contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
or
req.query_param_values contains /(?i)(?:extends\s*?ClassLoader\s*?\{|Base64\.getDecoder\s*?\(|java\.io\.InputStream|java\.lang\.Process\s*?\(|java\.lang\.Runtime\s*?\(|utility\.Execute\s*?\(|\.getRuntime\s*?\(\s*?\)|\.getInputStream\s*?\(|ProcessBuilder\s*\(\s*\)|\.newSingleThreadExecutor\s*?\(\))((.|\s)*?\.exec\s*?\()?/
Summary
SpringShell was a severe vulnerability affecting the widely used Spring Framework. SpringShell is officially assigned CVE-2022-22965 and the patch was released on March 31, 2022. In addition, three other vulnerabilities affecting the Spring Cloud Gateway, Spring Expression Language (SpEL), and Spring Cloud Function components have been disclosed since the beginning of March 2022.
Prisma Cloud can help in detecting all vulnerable instances in your deployments. Prisma Cloud may also be configured to fully prevent running any images or hosts vulnerable to this issue.
For an in-depth technical analysis of the SpringShell vulnerability, please refer to Palo Alto Networks Unit 42’s Threat Brief.