On being appointed Chief Information Security Officer of Aramis Group, one of the first calls Philippe Faure made was to Palo Alto Networks. Philippe Faure had recently joined Aramis from a major French grocery retailer with highly effective cloud security, and believed a similar deployment could achieve great results at Aramis – and he was proved right. Prisma Cloud is now delivering full stack, full lifecycle cloud security at this leading European online automotive retailer.
A French subsidiary of the global automotive group Stellantis, Aramis Group is revolutionising the way vehicles are bought and sold. Operating online, with approximately 480,000 customers and operations across Europe, Aramis makes a wide choice of reliable cars accessible to all.
Trends like electric vehicle (EV) adoption, connected car services, and supply chain hold-ups are upending the automotive industry. Buying and selling habits are changing too, with customers increasingly switching to fast, frictionless, online purchase and sale methods.
Aramis has responded to this upheaval by moving to the cloud. A digital transformation strategy, predominantly based on Amazon Web Services (AWS), enables the organisation to pivot at pace and respond faster to whatever automotive change is around the corner.
However, it’s a challenge to ensure this fast-scaling cloud environment remains secure.
Aramis needed to safeguard the AWS environment from threats that might disrupt their customers’ online buying/selling experiences and compromise data protection. One major step in their security strategy was to improve developer efficiency, reduce the required responses of their security operations, and deliver better security by identifying and addressing development vulnerabilities as early in their application development lifecycles as possible.
Newly appointed as Aramis’s Chief Information Security Officer (CISO), Philippe Faure believed that when it came to delivering on that cloud security promise, one potential partner stood head and shoulders above the others: Palo Alto Networks.
"One of the first decisions when I joined Aramis was to call Palo Alto Networks. We had enjoyed a highly successful deployment of their cybersecurity portfolio in my previous company, and we wanted to repeat that experience at Aramis."
– Philippe Faure
Chief Information Security Officer, Aramis Group
Prevent misconfigurations and threats
Philippe Faure and his team established several requirements:
- Support the AWS cloud transformation strategy with a complete, comprehensive, cloud security platform.
- Unify visibility into staging and production environments.
- Prevent misconfigurations in the development pipeline from reaching production.
- Use intelligent automation and reporting to demonstrate compliance.
According to Jeremy Mousset, IT Security Expert, Aramis Group, Palo Alto Networks Prisma Cloud offers them agile, trusted cloud security. He explains: “Prisma Cloud gives us unified cloud security posture management and cloud workload protection in a single console. Pre-built policies deliver faster, smarter compliance support, such as GDPR compliance, and role-based access controls allow our team to segregate security across the different business units.”
Full stack, full lifecycle security
Prisma Cloud secures Aramis’s cloud-native applications across the application lifecycle. Integrated vulnerability scanning currently checks more than 100 containers, integrating seamlessly with the CircleCI continuous integration (CI) solution. Simultaneously, the Cloud Security Posture Management (CSPM) provided by Prisma Cloud is used for detecting and preventing the misconfigurations and threats that lead to data breaches and compliance violations – ensuring the 40-strong development team can work at peak productivity.
Here’s how it works
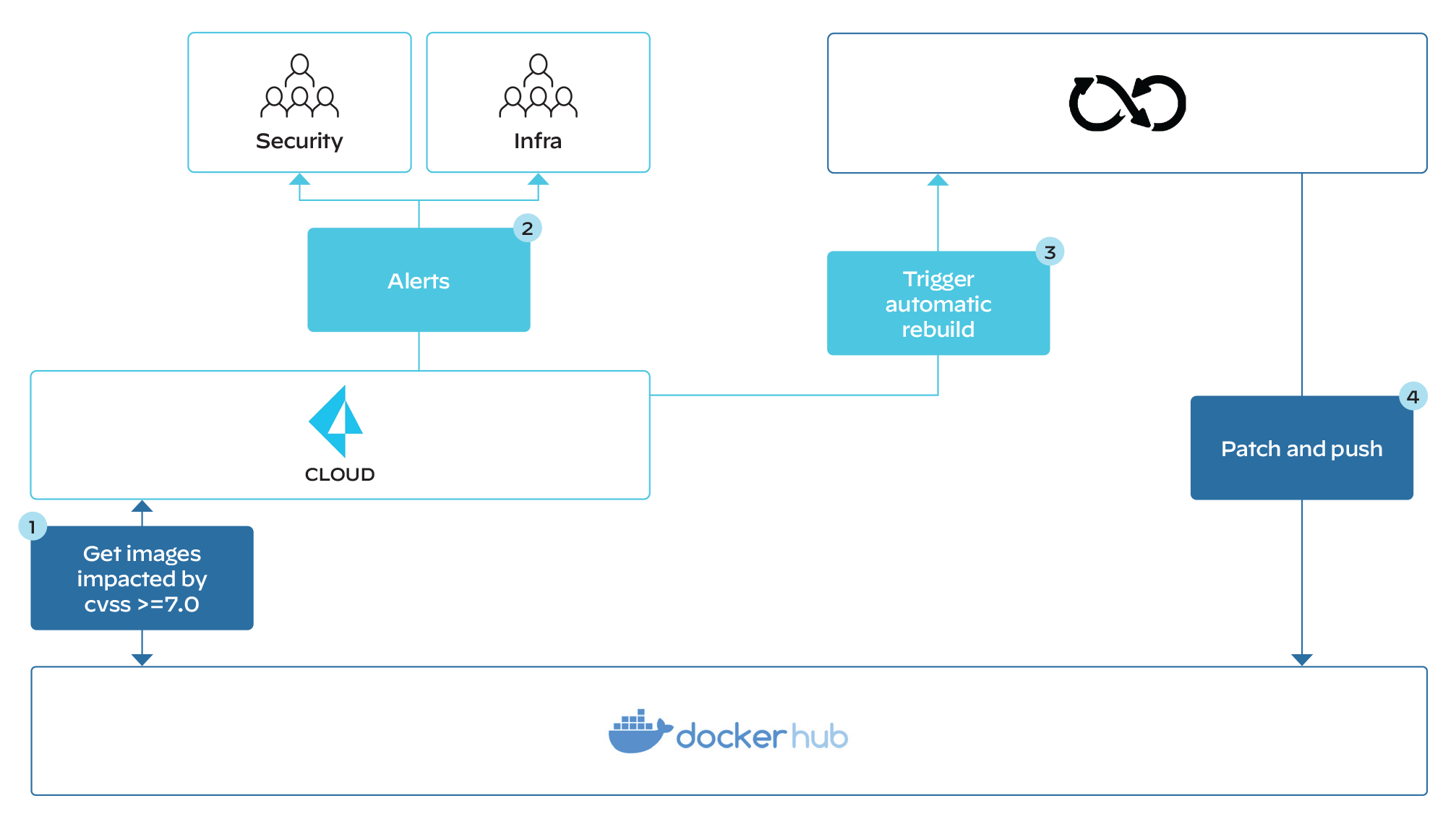
Figure 1: Continuous monitoring of base images
Prisma Cloud scans all base images in Docker (1). If an image scores higher than seven on the Common Vulnerability Scoring System (CVSS), the security and infrastructure team members are alerted (2). At the same time, Prisma Cloud is configured to trigger an automated rebuild (3) in the CircleCI CI/CD solution, which subsequently updates (patches) the base images and pushes them into the Docker registry (4). Prisma Cloud currently detects 1-2 image vulnerabilities each week.
"By controlling what moves through the pipeline, we can be confident the images are secure. It’s all automated, managed through a central console, and the team is immediately alerted to any vulnerabilities."
– Jeremy Mousset
IT Security Expert, Aramis Group
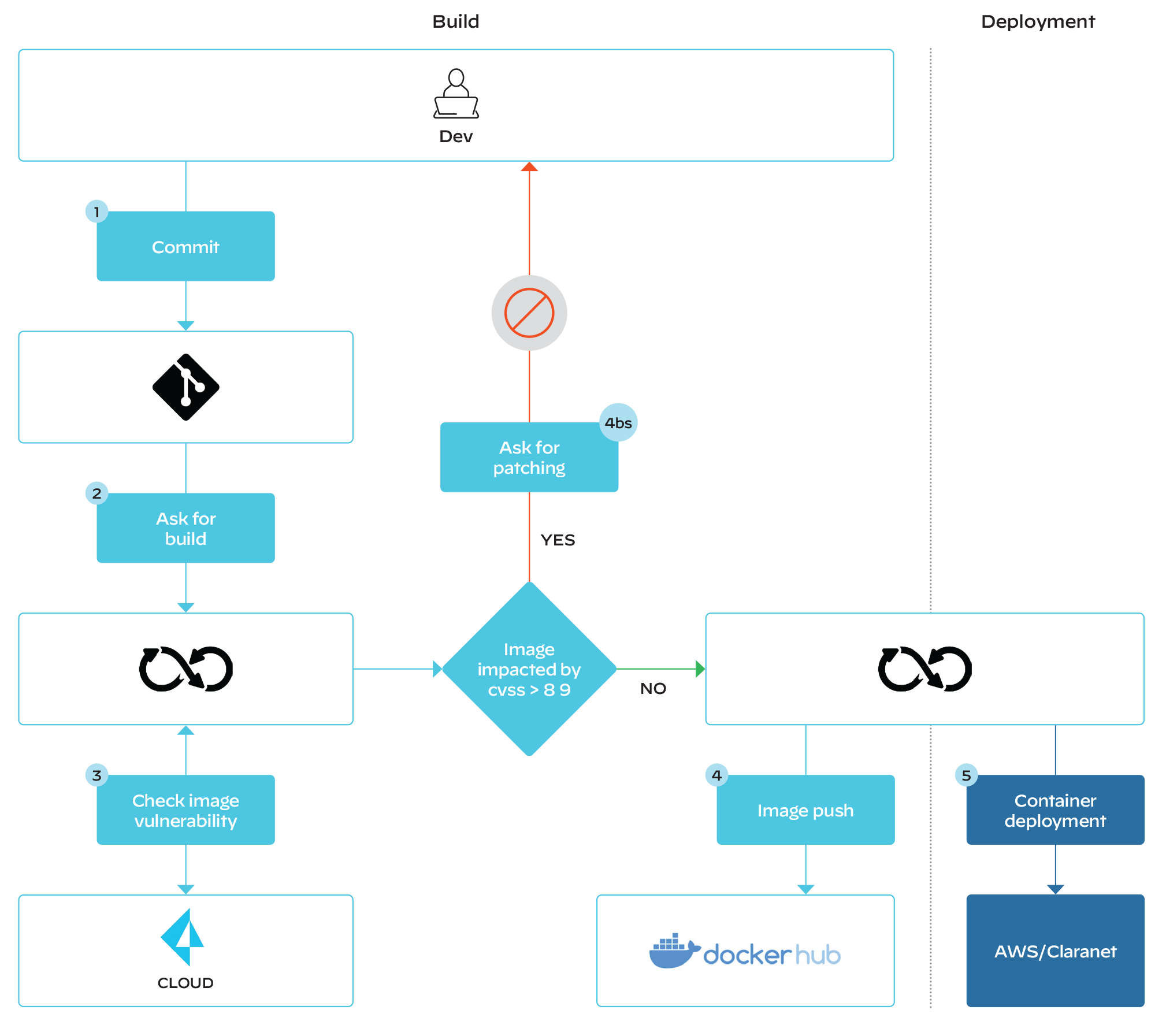
Figure 2: Prevents builds from moving forward in pipelines
Developer commits code to GitHub (1), which automatically triggers the CI/CD build process in CircleCI (2). During the CI/CD process, CircleCI connects with Prisma Cloud to check the image for system/package vulnerabilities (3). An image impacted by the CVSS (scoring >8.9) will not be deployed and the developer is alerted, asking him/her to patch/rebuild the image (4bs). If there is no vulnerability, the image is sent to CircleCI, which pushes it to the Docker hub for deployment (4). All containers running are scanned twice per day (5).
Unified CSPM
Prisma Cloud is also used to support Aramis’s CSPM strategy, continuously monitoring the AWS cloud resources for misconfigurations, vulnerabilities, and other security threats. “CSPM was incredibly easy to implement. We didn’t need to deploy an appliance; simple configurations quickly secured our cloud infrastructure,” says Jeremy. Using reporting as an example, he continues: “The single dashboard maintains a history of configuration changes, so we can understand exactly when a new security issue was introduced and by whom, to simplify cloud forensics and auditing.”
Driving forward to success
This cloud-native security strategy has many benefits. For example, it:
- Accelerates business transformation and innovation: offers complete development visibility, threat detection, and automated response to ensure the growing AWS environment is secure, enabling Aramis to confidently accelerate its digital transformation.
- Unifies trusted security: aggregated containers and cloud workload security ensure development processes are trusted and secure. “With Prisma Cloud we can be confident that vulnerabilities are identified and eliminated very early in the development lifecycle,” says Philippe Faure. “We sleep better now.”
- Supports governance and compliance: provides full visibility into all cloud assets and simplifies compliance reporting. Prisma Cloud maintains support for more than 20 compliance frameworks (GDPR, for example), with support for custom frameworks, and enables fast, simple reporting.
- Enables a shift-left strategy: delivers a single platform that ensures cloud security from build time to runtime, seamlessly connecting Aramis’ security and development teams.
"I would advocate for all organisations to explore Prisma Cloud. We always work with clean base images – and that is a vital step in speeding up the development lifecycle. This full stack, full lifecycle security platform is proven to deliver."
– Philippe Faure
Chief Information Security Officer, Aramis Group
For more information about Prisma Cloud please visit the website.