Trusted by the best








































of 10 of the Fortune 10
of 10 largest U.S. banks
of 10 largest utilities
of 10 Top U.S. hospitals
of 10 largest manufacturing companies in the world
of 10 largest oil & gas in the world
See how leading organizations are fueling innovation from a secure foundation
Driving AI Transformation
How to secure your AI builders, users, and operators.

Glean Defends the Enterprise with Prisma AIRS

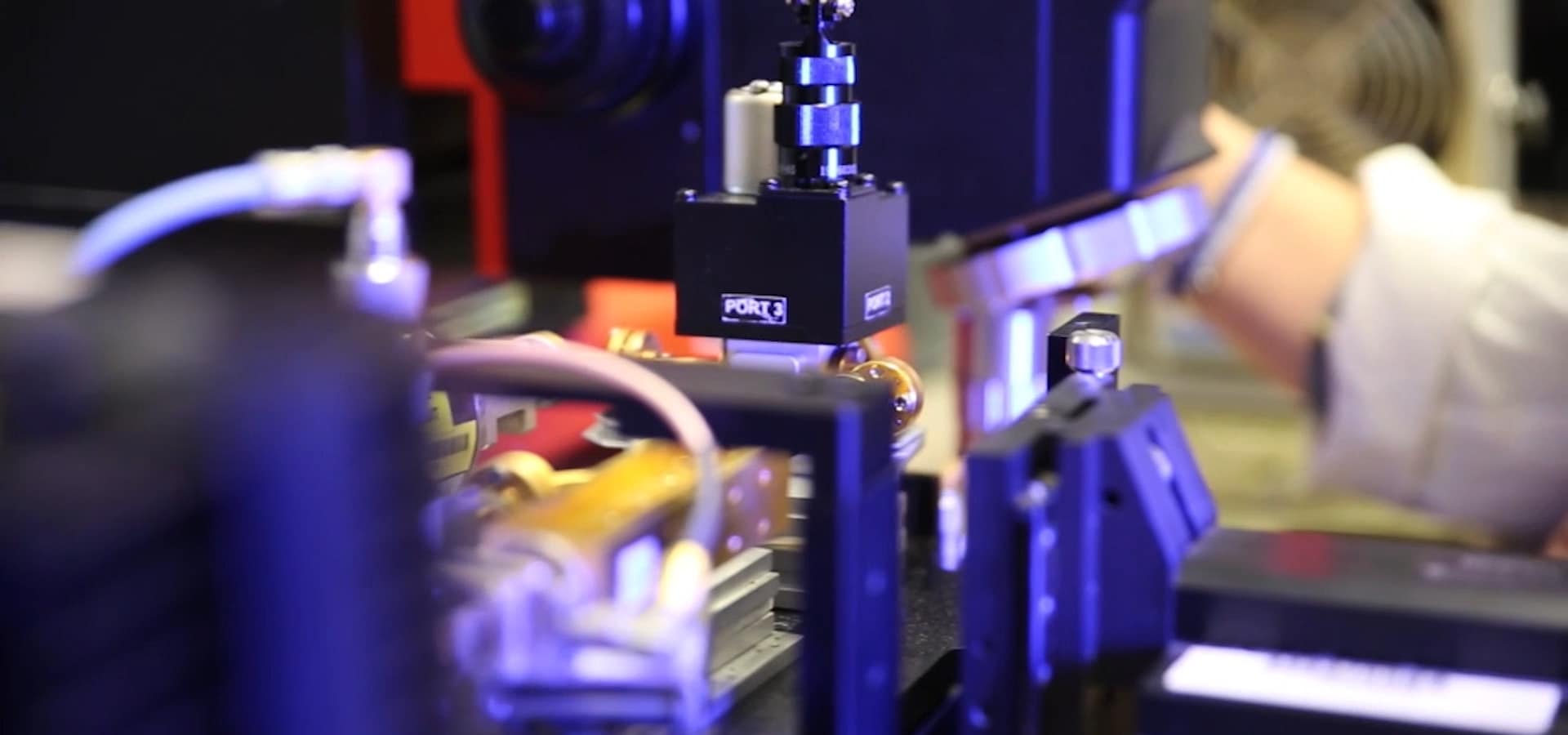
Colgate-Palmolive advances vision for secure manufacturing with a unified platform approach
6 to 1
consolidated 6 tools to 1 console for incident investigation
900
enhanced performance for 900 unique applications across business and factory sites

Banco Inter resolves cases 98% faster with Cortex XSIAM
95%
faster MTTD
98%
faster MTTR