Continual monitoring across AWS environments
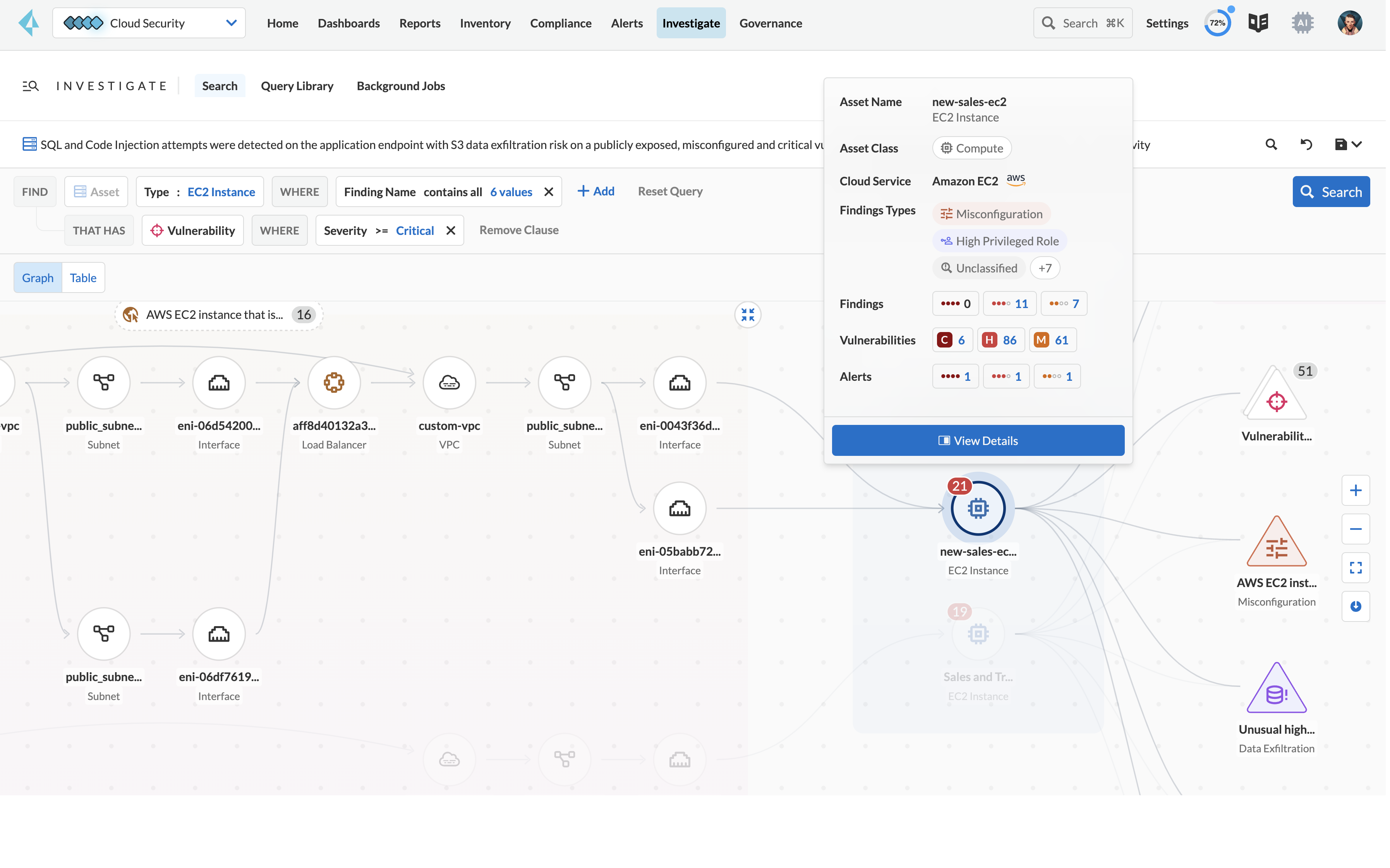
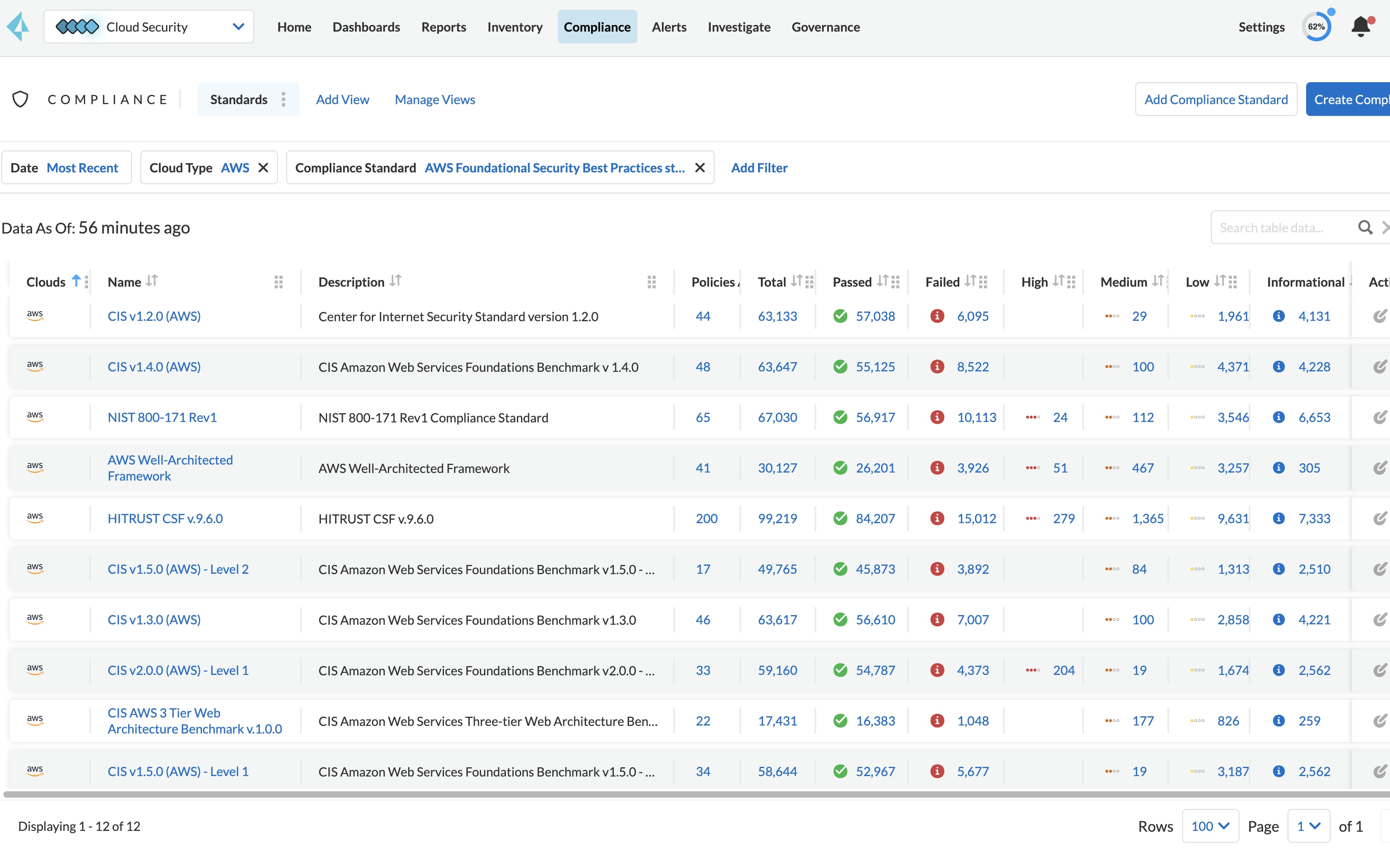
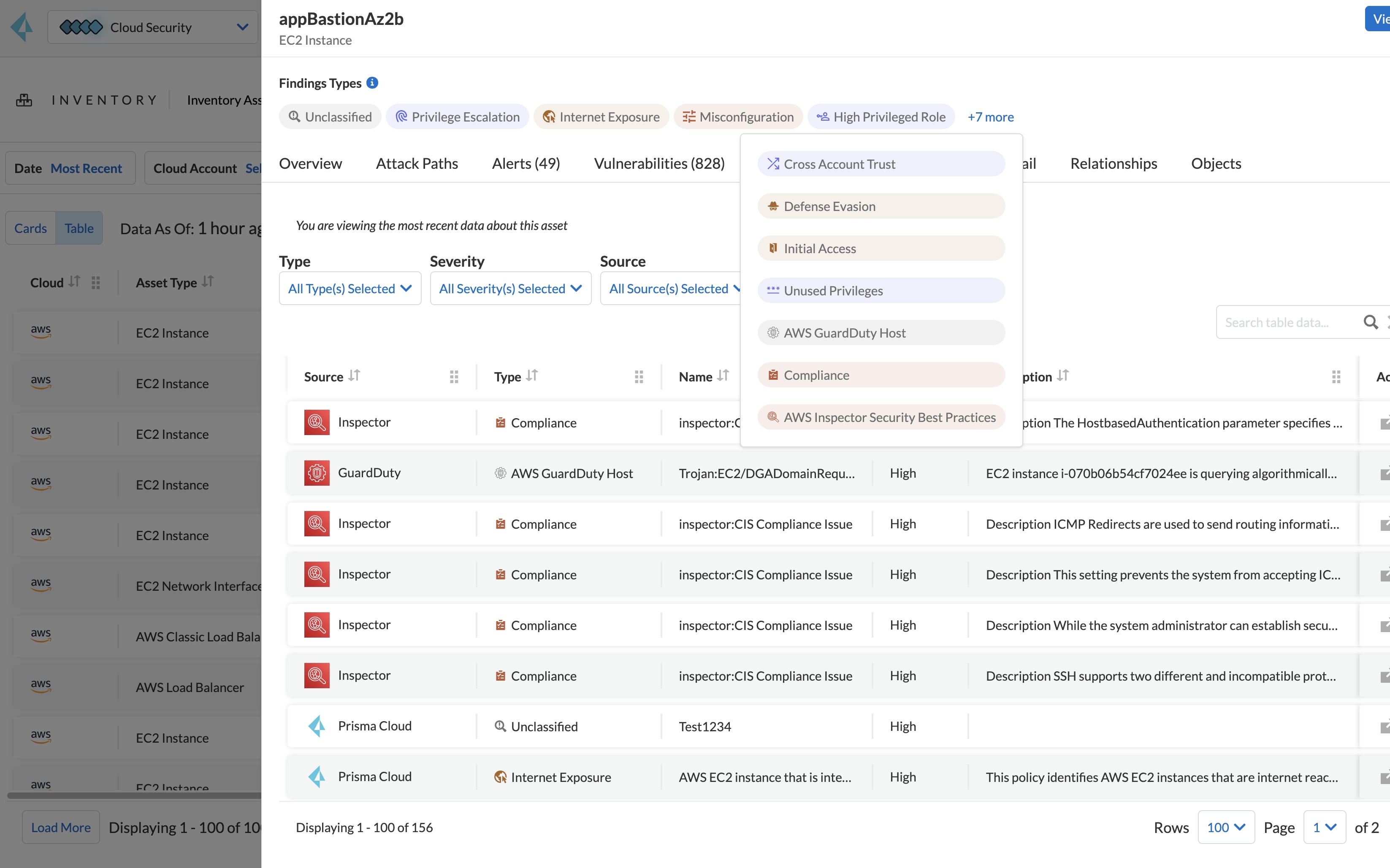
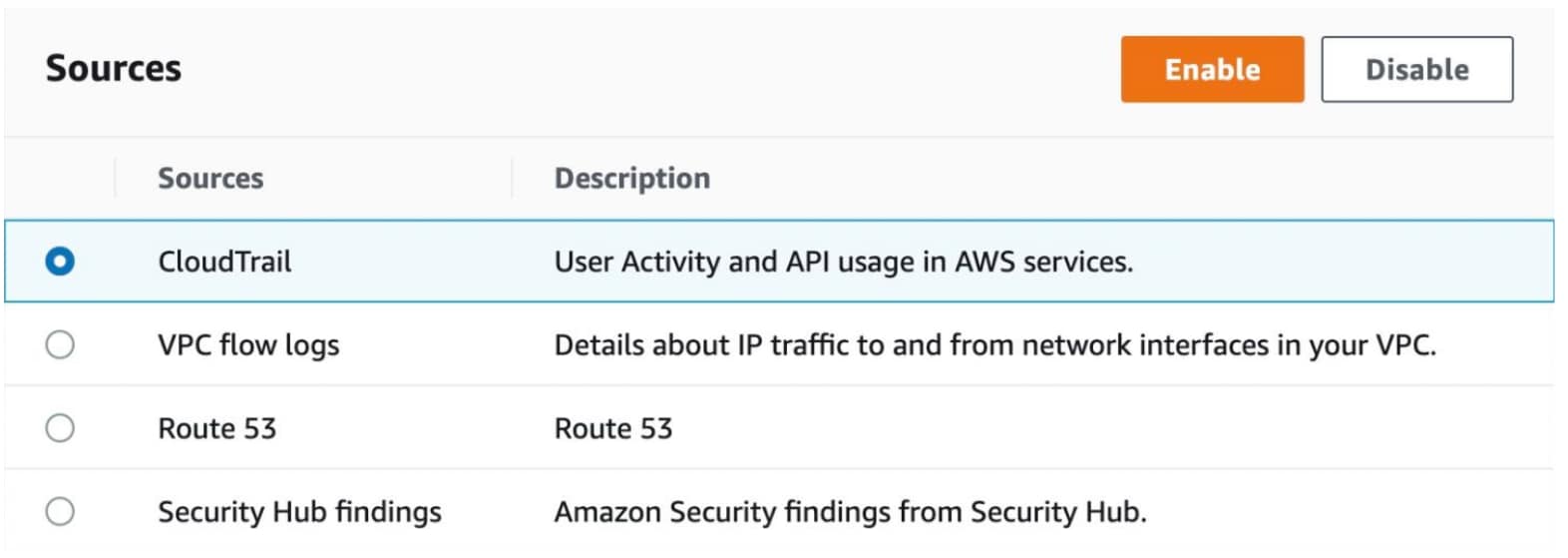
By integrating findings and security workflows with native AWS services like Amazon Inspector, Amazon GuardDuty, and AWS Security Hub, Prisma Cloud helps ensure continuous security and compliance monitoring across AWS cloud environments.