Search
WHY IT MATTERSHybrid is the new reality. Span your security from the data center to the cloud.
Hybrid is the new reality. Span your security from the data center to the cloud.
Embracing new forms of infrastructure is a key part of digitization as enterprises look to scale outside of their existing footprints to build hybrid environments. Here are three use cases for securing a hybrid data center.
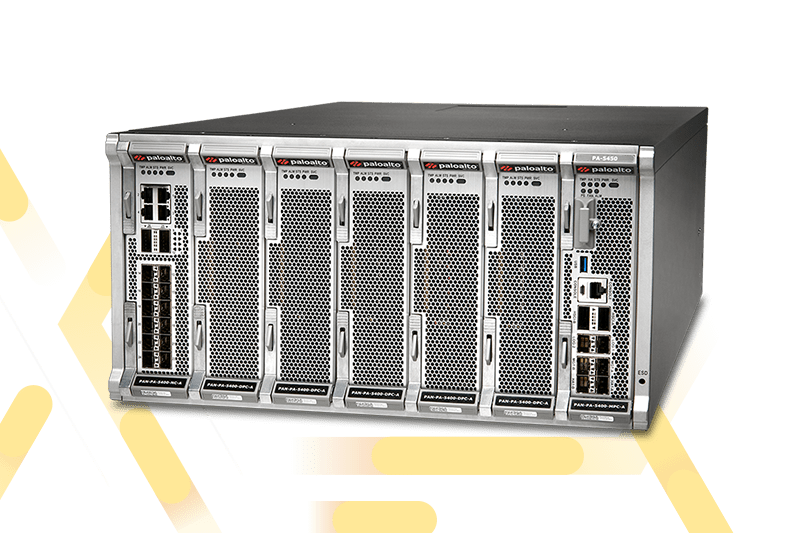
FEATURED PRODUCTS
Why choose Palo Alto Networks?

Centralized firewall management simplifies firewall configuration, auditing and reporting. Leverage policy management with a single solution to manage all firewall form factors and Cloud-Delivered Security Services. Manage and enforce a consistent policy model across on-premises deployments and multiple clouds.

Get best-in-class threat prevention and response from our wide range of security subscriptions. Block known threats and vulnerability attacks. Automatically identify and protect against zero-day exploits, malware, spyware and more.

Our virtual firewalls simplify security deployment. Deep integrations with the leading virtualization, software-defined networking, container and public cloud infrastructure providers make use of automation to simplify firewall deployment and scalability.
Meet with us
Contact our team of NGFW experts today. We want to meet with you to help keep your network secure.



