Ransomware
In recent years, the cybersecurity world has observed various changing trends in the malware landscape. From plain viruses and worms through DDoS botnets and banking Trojans, criminal organizations and malware authors are always trying to ramp up their attack abilities to adapt to the advancing security market and stay ahead of detection and prevention technology.
One of the most recent evolutions of this cat and mouse game is encrypting ransomware, which has lately become very popular with cyber criminals. The figure below shows the number of encrypting ransomware variants that have been spotted in attacks around the world, according to the date they were spotted on:
An encrypting ransomware is a malicious piece of software that infects a computer and encrypts all of its valuable files. The ransomware reaches the computer by way of exploiting a vulnerability (typically in a browser or a document reader), or via a downloaded executable run by an unsuspecting user. The malicious payload then encrypts valuable files on the machine (e.g. documents, images, certificates, etc.), requesting payment for their decryption within a certain time-frame.
The key needed for decryption is uploaded to a remote C&C server and is not stored on the local machine, making remediation very difficult. Removing the malware is not enough, since the bulk of the user’s files are encrypted and cannot be recovered without the key. Thus, if the victim chooses not to oblige within the given time-frame, the files remain encrypted with very little hope of recovery.
The effectiveness of this threat has contributed to its popularity among cyber criminals, which use it to infect individuals and organizations alike.
Looking at Things Differently
Most of the publications on encrypting ransomware focus on the infection methods, the encryption algorithm, or the C&C server communication. In this post, we look at ransomware from another angle, by analyzing the file operations they perform on the files they encrypt. A high-level overview using simple methods can provide significant insight into malware behaviors -- insight that might otherwise go unnoticed when delving into the little details.
We can divide encrypting ransomware into three categories, based on the way they access and modify files:
- Write-in-place
- Rename-and-encrypt
- Create-encrypt-and-delete
As part of our ongoing research into battling these pieces of ransomware, we analyzed many samples and variants, coming from different origins. We present a summarized study of some of the samples we analyzed, one for each of the aforementioned techniques.
Write-in-place
The ransomware in this category operate in the following manner:
- Create a temporary file
- Read the original file
- Encrypt the data and write it to the temporary file
- Read the encrypted data from the temporary file
- Write the data back to the original file
- Delete the temporary file
Ransomware of this type includes CryptoLocker, CryptoWall, CryptoDefence and DirCrypt.
Note that process memory can be used as the temporary storage area instead of a temporary file, and the malware still belongs to this category.
As an example, let us analyze a sample of the DirCrypt ransomware (md5: 0e5e8f6edd2c1496614bb6a71ba3f256), which uses the process’s memory as its temporary workspace, as depicted below:
- Open the file using CreateFile
- Get the file size and data length using GetFileInformationByHandle
- Read the file’s data (piece by piece), encrypt the data in memory, and write it back to the same file
- Finally, close the file, as shown below
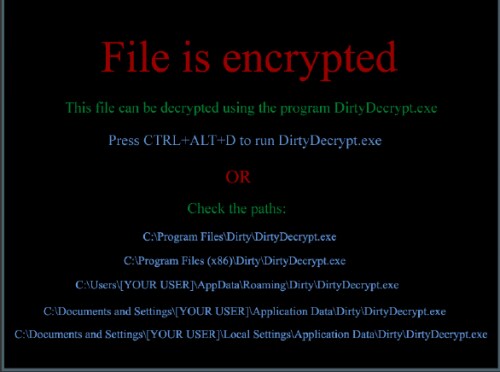
Upon opening the encrypted file, the user is faced with this message:
Rename-and-encrypt
Ransomware belonging to this category operate as follows:
- Rename the original file.
- Read the renamed file.
- Encrypt the data and write it back to the renamed file.
- Rename the file again to the original name (+ some extension).
Ransomware such as Onion/CBT/Critroni exhibit this method of operation.
This type of sequence is more complex than the first technique presented, since the file is renamed before the encryption. The defender might therefore need to keep track of all the different names a file may have.
An analysis of an Onion ransomware sample (md5: 10a472ec4a6687f1c432c639effbae00) shows the following actions being performed on the files to be encrypted:
- Open the file using CreateFile
- Rename the file using SetFileInformationByHandle to a file in a Temp directory, named 0.tmp
- Get the file size, and data length using GetFileInformationByHandle
- Read the renamed temp file, encrypt the read data, and write it back to the same file
- Set a new file size with SetFileInformationByHandle
- Rename the file again, this time to the original name, in the original path, with ".ctb2" extension with SetFileInformationByHandle
Note that the malware uses GetFileInformationByHandle and SetFileInformationByHandle to preserve the original timing attributes of the file.
After all files of interest had been encrypted, the following message appears:
Create-encrypt-and-delete
The operations performed by malware in this category are:
- Create a new file
- Write the encrypted data to the new file
- Delete the original file
Ransomware such as ZeroLocker and TorrentLocker use this method when encrypting files.
This technique is the hardest to identify as a malicious activity, since the API calls by themselves can’t associate the events of creation, writing and deletion together and show that they correspond to the same files. Furthermore, legitimate operations, such as moving files between different hard drives, might produce similar logs.
Analysis of a sample of the ZeroLocker ransomware variant (md5: 3772a3deeb781803a907ed36ee10681d) shows that for each of the files in a set of predetermined directories, the following actions are performed:
- Open the file using CreateFile
- Create a new file in the same location, with the same name and an additional ".encrypt" extension
- Get the file size and data length using GetFileInformationByHandle
- Read the original file, encrypt it, and write it to the newly created file
- Delete the original file using SetFileInformationByHandle
At the end of this procedure, the ransomware creates a directory named "ZeroLocker" with two files. One of the files contains the following message:
Conclusions
In this post we examined the methods of operation for several common ransomware samples. The first method, write-in-place, is the most simplistic method in terms of file operations. The second method, rename-and-encrypt, is very similar to the first method, but adds the complexity of tracking all the different names a file may possess.
The last method, create-encrypt-and-delete, is the file operation method, used by ransomware, that is the most challenging to identify. This stems from the fact that the file operations involved can be seen in everyday use-cases, and it is hard to relate them to malicious activity that aims to encrypt files on the machine.
Palo Alto Networks has been researching a solution in Advanced Endpoint Protection that, based on our lab tests, would have blocked the ransomware families mentioned above and prevented malicious activity. We hope to share more details of this solution in the coming months.