
Are you challenged by the need to enforce security policy in an agile application development process? Do you need a rapid and automated way to secure public cloud applications without adding delay? You can combine the flexibility of dynamic address groups and the VM monitoring capabilities on the firewall and Panorama to dynamically apply security policy as VM workloads spin up or down, and IP addresses change frequently.
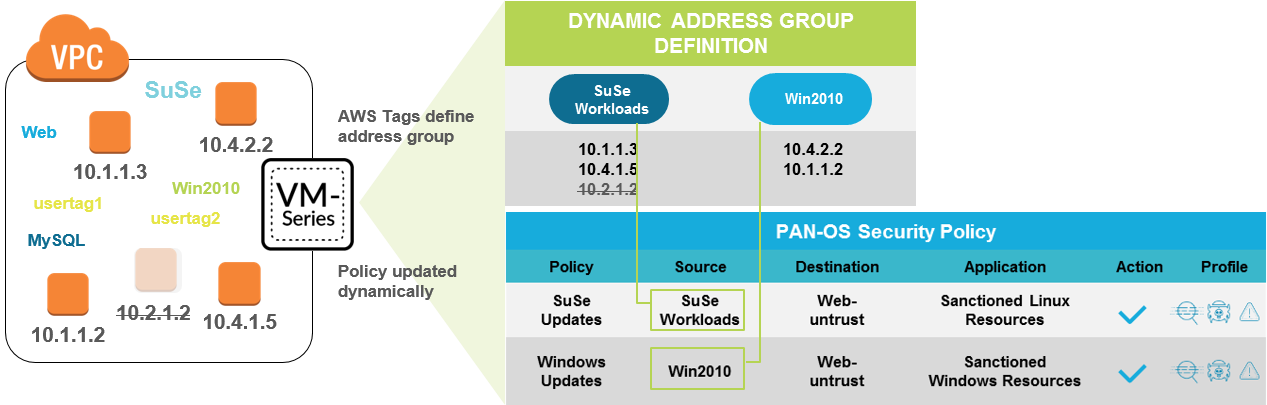
The VM Monitoring capability allows the firewall to be automatically updated with IP addresses of a source or destination address object referenced in a security policy rule. Dynamic address groups use the metadata about the cloud infrastructure, mainly IP address-to-tag mappings for your VMs. Using this metadata, i.e. tags, instead of static IP addresses, in Security policy makes them dynamic. So, as you add, change, or delete tags on your VMs, security policy is always enforced consistently.
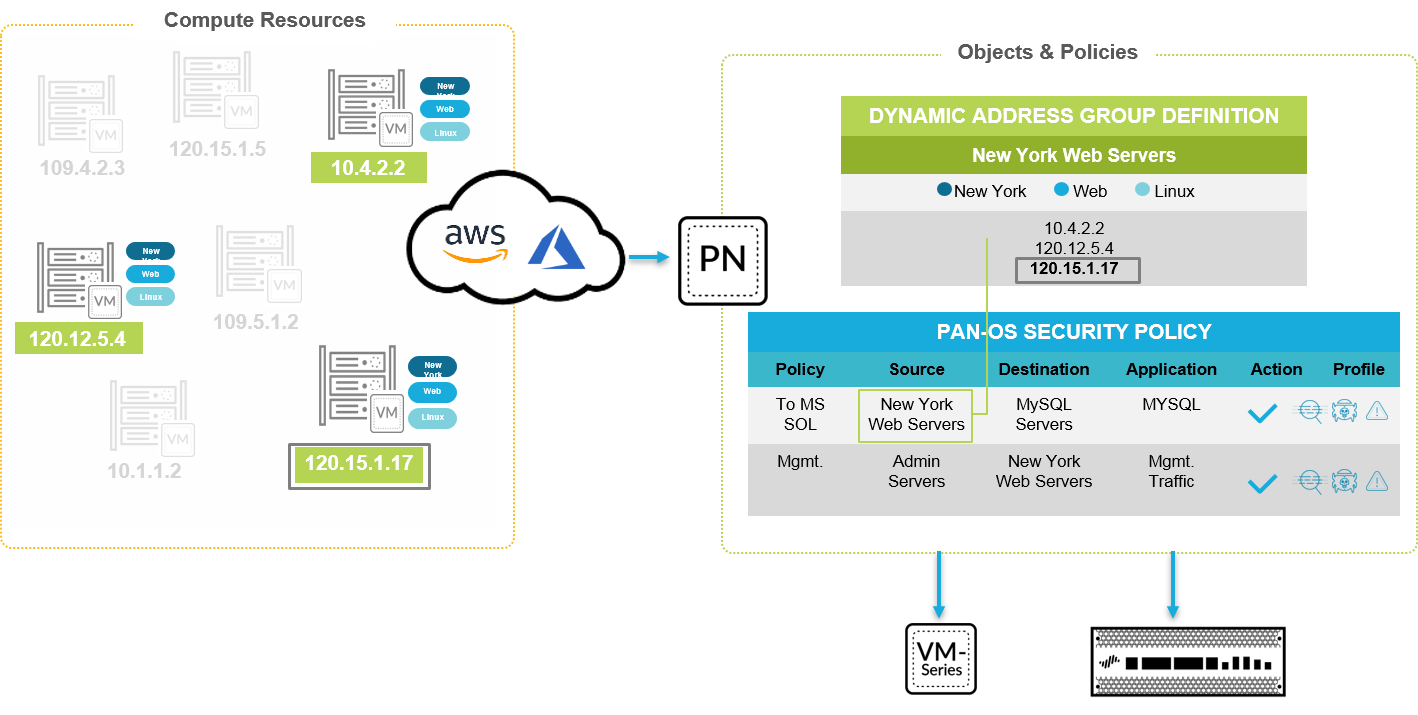
Depending on your scale and the cloud environments you want to monitor, you can choose to enable VM Monitoring for either the firewall or Panorama to poll the evolving VM landscape. The all new Panorama plugin now allows you to monitor up to 100 VM sources on AWS and Azure, allowing your development team to more freely add and remove workloads to AWS VPCs or Azure Subscriptions. This new plugin complements the existing PAN-OS functionality that enables you to monitor up to 10 VM sources.
- VM information source on the Palo Alto Networks firewalls enable you to poll up to 10 sources, such as AWS VPCs, ESXi or vCenter servers, or Google Projects. This option is well suited for smaller deployments where the firewall can retrieve the metadata (IP address to tag mapping) for your workloads and directly enforce policy.
- Panorama plugins support larger scale deployments in the Azure and AWS public cloud. You can use Panorama 8.1.3 or later, as an anchor to poll up to 100 Azure subscriptions and 100 AWS VPCs for tags, and then distribute the metadata (IP address to tag mapping) to many firewalls in a device group.
Plug in and be agile with one or both options!
As always, you can find our content on our Technical Documentation site.
Happy reading!
Your friendly Technical Documentation team
Have questions? Contact us at documentation@paloaltonetworks.com.