Ransomware attacks have evolved over the years from a threat primarily targeting individuals with modest ransom demands, to a sophisticated form of cybercrime that now jeopardizes large companies, government agencies and critical infrastructure. It's increasingly common to hear of a major corporation, educational institution or local government falling victim to a ransomware attack, in addition to the incidents that make national headlines. These attacks have far-reaching implications, affecting everything from critical public services, like hospitals, disruptions in supply chains, and even taking critical gas pipelines offline. I recently had the opportunity to testify before two subcommittees of the U.S. House of Representatives Committee on Oversight and Accountability on combating ransomware attacks.
My full written testimony goes into depth on the nature of the threat and how it’s changing, as well as how defenders can meet the moment through innovation, public-private partnership and a well-prepared workforce. Here, I’m sharing a few prominent insights from the ransomware cases we see as incident responders, as well as our key recommendations for how organizations can reduce risk.
Ransomware Actors Are Becoming More Sophisticated
Adversaries continue to enhance their techniques and increase their sophistication. In our 2023 Ransomware and Extortion Report, we specifically illuminate three alarming trends:
- An increase in multi-extortion techniques
- An increase in harassment activity
- Continued evolution in the attack vectors used for initial compromise
Multi-Extortion
Threat actors have come to realize they’re more likely to get paid if they put additional layers of pressure on their victims. We call this multi-extortion. Aside from using ransomware to lock up an organization, the attackers also steal data and threaten to leak it. Multi-extortion tactics continue to rise. For example, threat actors are currently engaged in data theft in addition to ransomware in more than 70% of cases on average, compared to only about 40% of cases as of mid-2021. Criminal groups post about this data on leak sites, where Unit 42 researchers observe about seven new victims a day, on average – that’s about one every 4 hours.
Ransomware and Harassment
Harassment is one particularly notable multi-extortion tactic. Ransomware actors now frequently target specific individuals in an organization (often in the C-suite) with threats and unwanted communications. This harassment is now involved in 27% of ransomware cases Unit 42 investigates, compared to just 1% a few years ago.
Ransomware Actors Evolve Attack Vectors
The group Unit 42 tracks as Muddled Libra (related to Scattered Spider) looks for strategic points of leverage to scale the impact of their malicious activity. By targeting business process outsourcing (BPO) providers, they’ve proven adept at compromising these widely used third-party services to gain access to BPO customers across multiple sectors. Among other tactics, threat actors frequently use social engineering or text messages to lure employees into providing credentials that allow access to organizations.
Attack Surfaces Remain Vulnerable to Ransomware
We have found that even sophisticated enterprises actually have twice the number of systems exposed on the internet than what they were internally monitoring – a visibility gap that gives adversaries the upper hand.
Our Attack Surface Threat Report provides a detailed analysis of the digital infrastructure that adversaries may try to exploit. A particularly concerning finding is the ubiquity of poor configurations around a remote access method called Remote Desktop Protocol (RDP), a prime target for ransomware attacks. RDP misconfigurations make up 20% of all exposures we observe on the public-facing internet. Additionally, over 85% of organizations we observed with these exposures left them unaddressed for at least 25% of a typical month. This leaves the organizations open to ransomware attacks or unauthorized login attempts for sustained periods of time.
Five Key Recommendations to Reduce Risk
We recommend organizations focus on the following actions to increase their cyber resilience:
- Maintain an Incident Response Plan – Prepare for and respond to cyber incidents, including emerging ransomware tactics like extortion, multi-extortion and harassment. Organizations that continuously review, update and test their incident response plans (ideally with input from cybersecurity experts) are much more likely to effectively respond to and contain an active attack.
- Ensure Complete Visibility of Your Attack Surface – 75% of ransomware attacks and breaches fielded by Unit 42’s Incident Response Team result from a common culprit – internet-facing attack surface exposures. Deploying solutions that provide centralized, near real-time visibility can help organizations identify and mitigate vulnerabilities before they can be exploited.
- Leverage the Power of AI and Automation – Modernize security operations and reduce the burden on overworked analysts. The latest technology can help organizations drive down key cybersecurity metrics, like mean time to detect and mean time to respond, denying attackers the time they need to compromise an organization’s systems or exfiltrate its data. Additionally, technique-based protections mapped to the MITRE ATT&CK Framework can help defenses nimbly evolve in response to adversarial tactics.
- Implement Enterprise-Wide Zero Trust Network Architecture – This is a fundamental security principle that assumes the network is already compromised and implements processes that continuously validate the user, device, application and data in a controlled manner. Zero Trust network architecture creates layers of security that prevent or limit an attacker from successfully moving laterally around the network. This provides victims with more time to detect, properly contain and remediate the threat.
- Protect Cloud Infrastructure and Applications – With cloud migration accelerating, threat actors will continue to develop tactics, techniques and procedures designed to target and compromise cloud workloads. Organizations leveraging cloud infrastructure should implement a cloud security program and platform that offers comprehensive cloud-native security.
While there is no silver bullet in cybersecurity, prioritizing these recommendations will materially reduce the risk of falling victim to an attack, more effectively contain an attack if one does occur, and help increase resilience for the entire cybersecurity ecosystem.
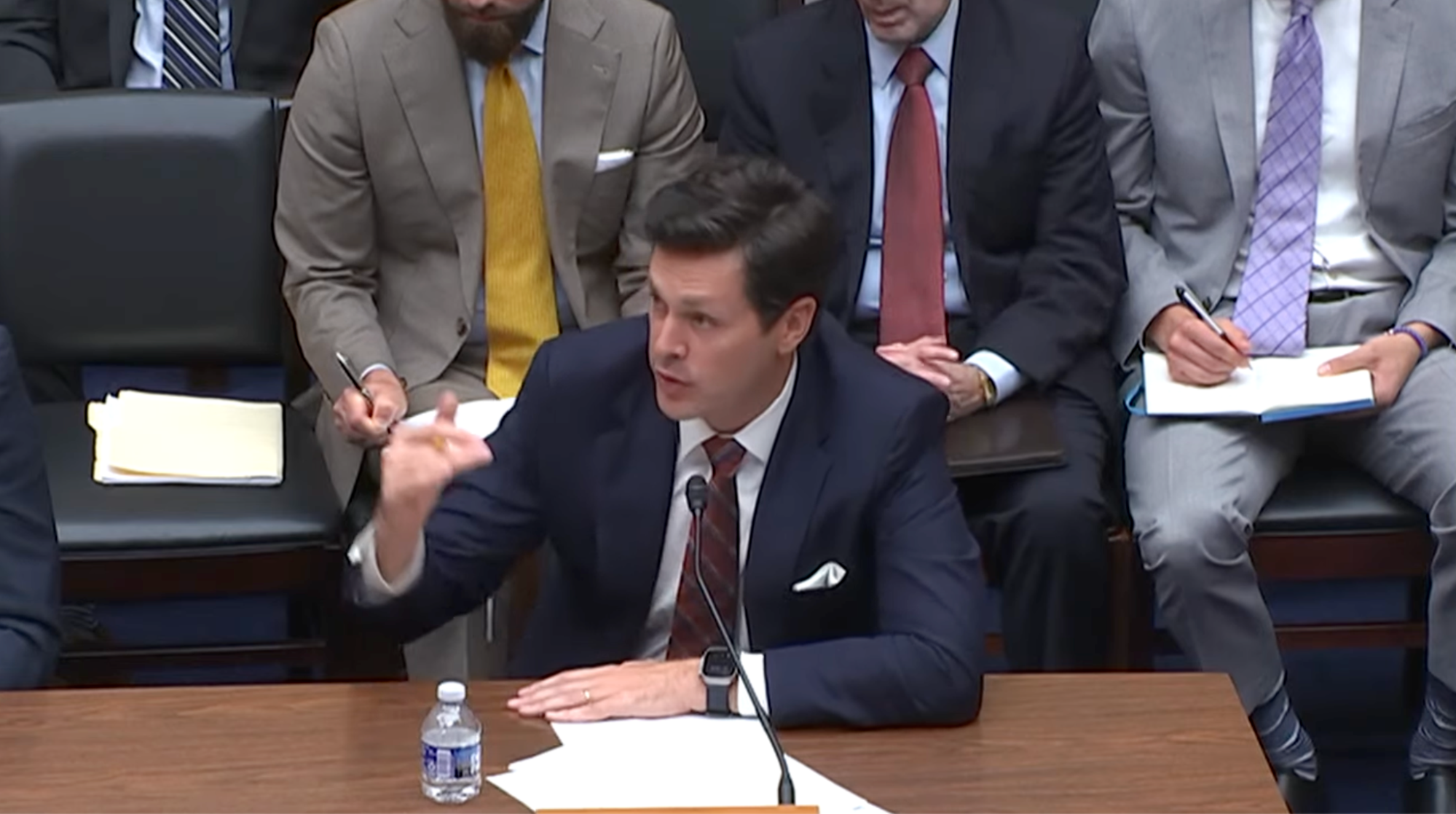
![Sam Rubin at the hearing table on ransomware defense.]() Partnership Remains Critical to Fortify Defenses
Partnership Remains Critical to Fortify Defenses

Information sharing venues, where commercial competitors become threat intelligence partners, remain a critical part of our collective defense. Whether through participation in the Ransomware Task Force, CISA’s Joint Cyber Defense Collaborative or the Cyber Threat Alliance, we’ve seen firsthand the value of sharing technical threat intelligence about ransomware threat actors and collaborating to build stronger defenses. Palo Alto Networks is committed to working in partnership with other organizations to be good cyber citizens and trusted security partners.
Sam Rubin is vice president and global head of operations for Unit 42, the threat intelligence and incident response division of Palo Alto Networks.
Watch Sam’s full testimony in this replay of the hearing.