The Challenges of Today’s SOC
Security teams have an important and difficult job – protecting their organizations from a threat landscape that is constantly changing. Based on investigations conducted by our Unit 42 team, we know that threat actors are carrying out end-to-end attacks faster, from initial compromise, all the way to data exfiltration in just a matter of hours. Considering that companies take an average of 5.5 days to initially contain an incident once discovered, this increases the pressure on security teams to get things right as quickly as possible.
It’s important to recognize that security teams have done an admirable job over the years trying to react to the evolving threat landscape. They’ve invested heavily in security by building complex security operations centers (SOCs) that use an abundance of security tools to generate and collect vast amounts of data from across the organization. If there is one thing that most SOCs can agree on, it’s likely that there is no shortage of security tools and data to use.
However, even with the best of intentions, there are fundamental challenges with how SOCs of today have been built. Even with a variety of security tools, and access to all the data you need, it still takes SOCs too long to detect security threats. And when those incidents are detected, it's taking even longer to remediate. We believe that these problems can be boiled down into three fundamental areas:
- Siloed Tools and Data – Today’s SOCs are built on a variety of disparate tools that address specific security functions (endpoint security, automation, incident and event management, etc.). All of these tools have different consoles and store data separately. Security teams attempt to resolve this with SIEMs or through integration, but this just means more fragile integrations between different products. This results in operational complexity in the SOC.
- Weak Threat Defense – There is much data being generated across the organization – endpoint events, network traffic, cloud infrastructure events, identity and access management logs and application data – just to name a few. Within all of this data exists information about suspicious or malicious activity. Unfortunately, relying solely on static correlation rules or extensive detection engineering work is only going to catch a fraction of that activity and likely will result in significant false positives. This results in the inability to stop threats at scale.
- Heavy Reliance on Manual Work – When you combine too many tools with weak threat defense, SOCs are ultimately overwhelmed with a high number of inaccurate and disconnected alerts to process. They struggle to prioritize which alerts to handle first, and many important alerts are ignored or overlooked. Manually investigating and resolving alerts simply takes too long. This results in slow incident remediation.
Many SOCs today are feeling this pain, but Cortex XSIAM was built from the ground up to solve these specific challenges and more. This earned the platform a leader and outperformer position in the GigaOm Radar Report on Autonomous Security Operations Center (SOC).
"As a solution built from the ground-up with lessons learned from a suite of leading security products, Cortex XSIAM delivers a comprehensive autonomous SOC solution that scores high on a wide range of key criteria," states GigaOm analyst Andrew Green.
Introducing Cortex XSIAM 2.0
Cortex XSIAM is an award-winning and groundbreaking AI-driven platform that converges SOC capabilities, leverages AI for accurate threat protection and applies an automation-first approach to security operations. With XSIAM, we aim to simplify security operations, stop threats at scale and accelerate incident remediation.
With our latest XSIAM 2.0 release, we’re building on those outcomes with exciting new capabilities:
- XSIAM Command Center
- MITRE ATT&CK Coverage Dashboard
- Bring Your Own ML (BYOML)
- And many other new features and innovations
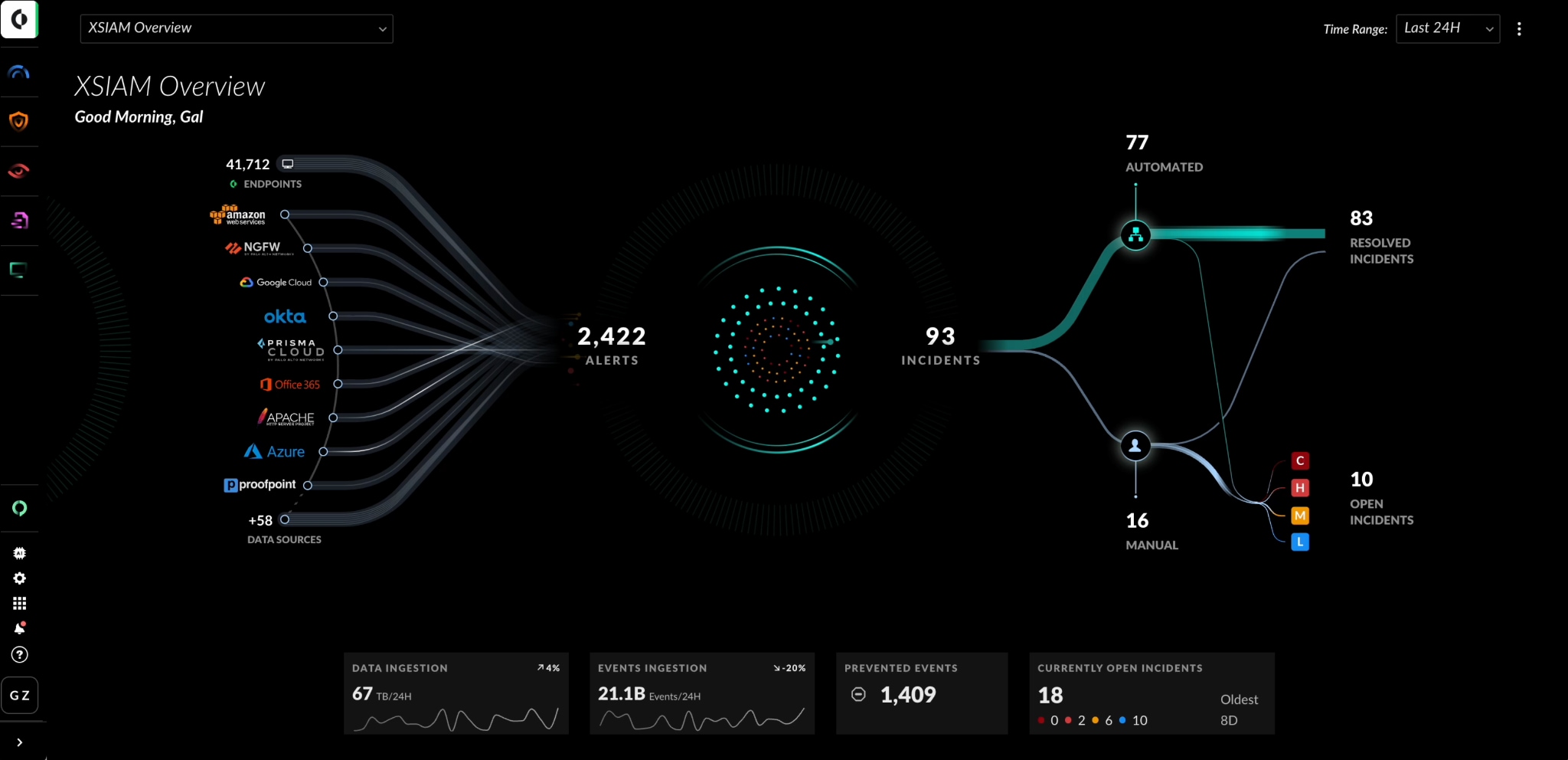
XSIAM Command Center
SOC teams are overloaded with an abundance of information and metrics to process on a daily basis:
- What data is being analyzed?
- How many threats were prevented?
- How many incidents are open?
- What incidents should be prioritized?
All of this can be overwhelming and can slow down security operations.
The XSIAM Command Center completely overhauls how security teams monitor their security operations through a new, simplified and elegant visualization of the entire SOC workflow. Security teams are provided with a comprehensive overview of SOC operations, including visibility into all data sources being consumed by XSIAM, which can help with identifying data health or integration issues that need to be resolved. Security alert and incident information, such as the number of resolved or open security incidents, helps with incident prioritization and resource allocation. As a result, this new UI streamlines security operations and reduces operational complexity with a more user-friendly design.
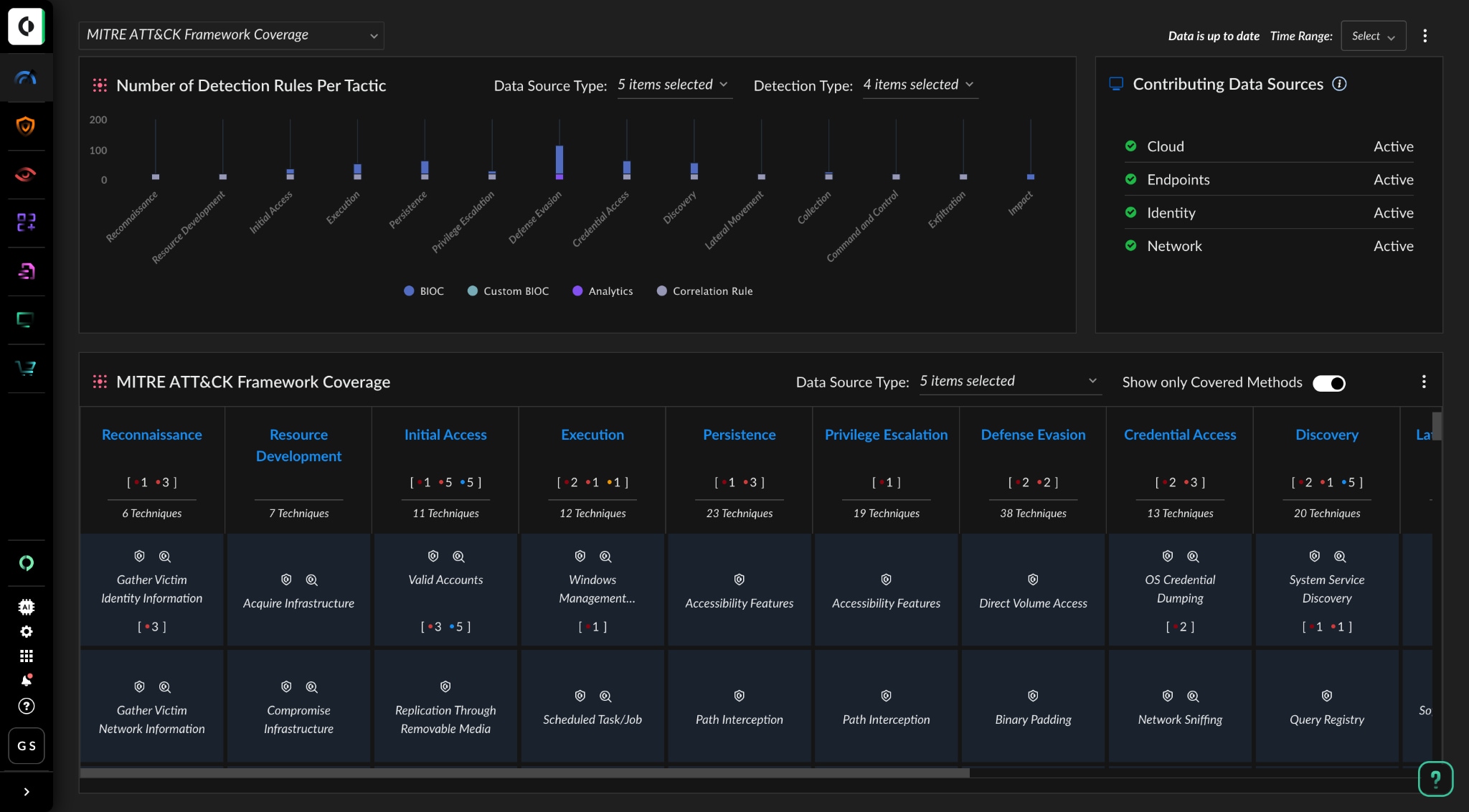
MITRE ATT&CK Coverage Dashboard
Security leaders and practitioners need an easy way to report on their security posture and determine if they have protection coverage against the latest techniques being used by threat actors. This information can be used for reporting metrics to the leader or the board, and it can be used for continuously improving detection and prevention capabilities.
With the XSIAM MITRE ATT&CK Coverage Dashboard, security teams can stop guessing about where they are or how to protect against the latest threat vectors in the organization. Instead, they can take control by mapping coverage directly to MITRE ATT&CK. This dashboard provides detailed visibility of detection and prevention coverage across tactics and techniques in the MITRE ATT&CK framework. Armed with this information, SOCs gain confidence that they’re covered against the latest attacker tactics, techniques and procedures (TTPs). They can quickly assess their overall security posture and focus efforts to increase threat vector detection and prevention coverage over time, contributing to the ability to stop threats at scale.
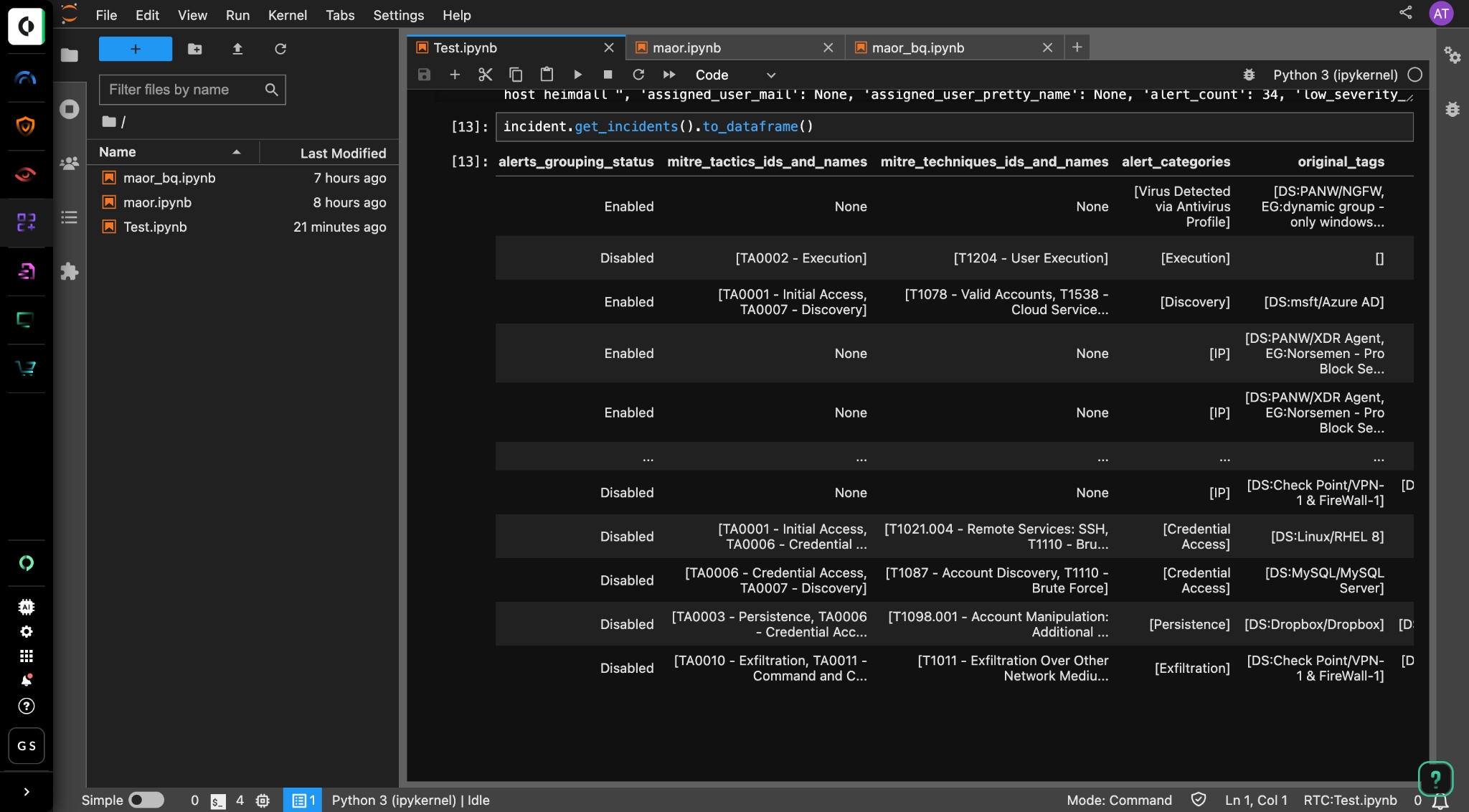
Bring Your Own ML
Many security organizations have a desire to build their own custom machine learning (ML) models and perform analytics on unique security use cases. However, they are often forced to replicate the data into a separate data lake, which adds additional infrastructure complexity and costs.
XSIAM ingests vast amounts of complete security data across hundreds of supported sources to enable better out-of-the-box AI/ML analytics. For the first time, mature SOCs can take advantage of this data lake to create and customize ML models, using a bring your own ML (BYOML) capability. This provides a new framework that enables security teams to integrate their own custom ML models on top of XSIAM and execute security ML use cases unique to their environment. Using the familiar open-source Jupyter Notebook tool, security teams can code their own ML to satisfy unique security use cases in their organizations, including fraud detection, threat hunting, research, incident management and data visualization. All of this provides security teams with greater flexibility in how they use their data for threat analysis, incident response and security research.
Other New Features and Security Innovations
We’re committed to providing the most comprehensive security platform to protect organizations against the threats of today and into the future. With this goal in mind, XSIAM continues to receive the latest innovations and security enhancements built into each of our leading Cortex platform products, including Cortex XDR, Cortex XSOAR and Cortex Xpanse. These innovations are aimed at improving analyst experience and driving better security outcomes. Here is a list of just some of the latest enhancements you can expect in XSIAM 2.0:
- Contextual In-Product Help Assistant – Streamline access to documentation and better understand product capabilities by accessing product help and documentation, without the need to navigate out of the product.
- New Security Protection – Improve detection and protection coverage capabilities with new modules for early detection of threats targeting macOS ransomware, Kubernetes (K8s) and master boot records (MBRs).
- Network Detection (NDR) Coverage – Expand the network coverage of the endpoints with over 50 new detectors covering generic and specific protocol-based threat detection.
- Advanced Local Analysis for macOS and Linux – Provides enhanced coverage for local analysis of macOS and Linux file systems, leveraging ML models to provide accurate and adaptive response to evolving threats.
- Free Text Search – A simplified search experience that enables analysts to simply query the entire security dataset, without the need to craft specific XQL queries.
- New Attack Surface Management (ASM) Policies – Brand new ASM policies add to the library of over 700 existing policies to help with proactively discovering and eliminating attack surface risks.
The Only Security Operations Platform You Need
Effective security operations require a new approach with simplification, AI and automation at the core. XSIAM is the only security solution built from the ground up with these principles in mind. With a combination of a converged platform, AI-driven outcomes and an automation-first approach, XSIAM strives to be the only security operations platform you need.
To learn more, join us for a virtual launch event in your region where we will explore XSIAM 2.0 and delve into the power of AI in the realm of cybersecurity.