Traditional security operations centers (SOCs) are drowning in security alerts, and a lack of context across data sources creates even more headaches for your security teams. Investigations of these alerts are time-consuming; remediation is often slow; and, security analysts are facing burn-out as they try to keep their heads above water. Deloitte’s AI-Native Security Operations Platform™, powered by Palo Alto Networks Cortex XSIAM®, is designed to modernize your SOC.
Hiring more staff is costly and difficult due to a high demand for skilled talent. But, adding more people doesn't address the modernization problem at its root: Traditional SOC technologies inundate analysts with data that lacks context, cause, prioritization or assistance with remediation.
A constant backlog of security alerts and subpar key performance indicators (KPIs) should serve as a wake-up call that it is time to modernize your organizations’ SOCs. However, many still suffer from these issues. A modern SOC reduces costs, helps your organization achieve compliance, and simplifies and scales security operations through automation.
It’s time to flip the script. Technology should be empowering your security analysts, not burdening them. SOC technology should reduce the load for security teams. Swap the alert fatigue and backlog frustration with the ability to address critical alerts and do work that improves your organization’s security posture and helps make lives better.
Create the Modern SOC with AI and Automation
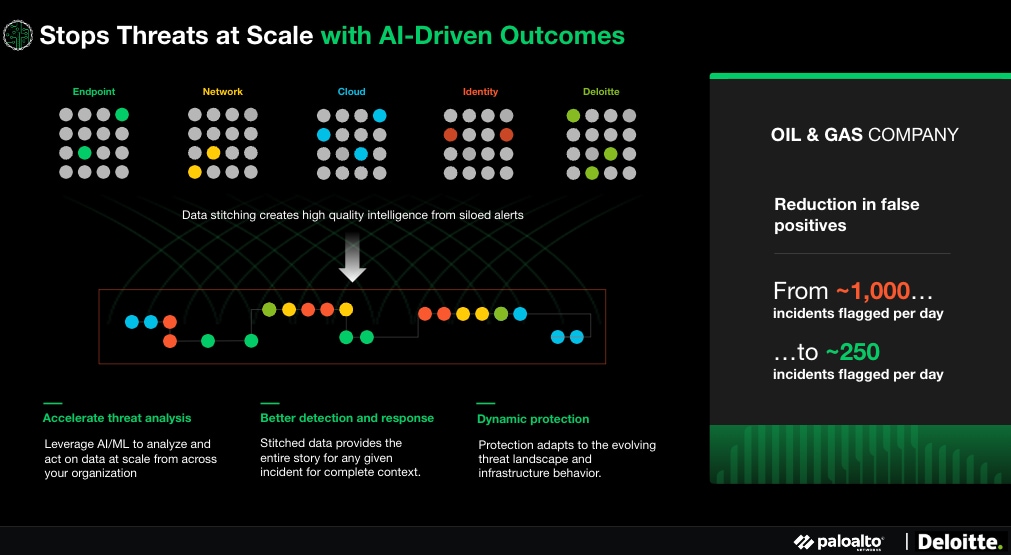
Deloitte’s AI-Native Security Operations Platform has the ability to pull security data together from disparate sources to build a coherent and complete picture of incidents and run use-case-focused automations. This ensures that creating a modern SOC will not only relieve alert fatigue but also help you improve efficiency, effectiveness and overall security outcomes without ignoring a company’s security needs.
Establishing a modern SOC begins by centralizing multiple products into a single, coherent platform. This platform is purpose-built for security operations in order to reduce risk and operational complexity.
Cortex XSIAM unifies best-in-class security operation functions:
- Endpoint Detection and Response (EDR)
- Extended Detection and Response (XDR)
- Security, Orchestration, Automation and Response (SOAR)
- Attack Surface Management (ASM)
- User and Entity Behavior Analytics (UEBA)
- Threat Intelligence Platforms (TIP)
- Security Information and Event Management (SIEM)
XSIAM allows you to automate data integration and analysis by centralizing all of your security data, enabling the use of machine-learning data models designed specifically for security. With this capability, you will simplify security operations, stop threats at scale, and accelerate incident remediation. This level of automation frees up your analysts to focus on the incidents that matter and the work that requires human intuition, like threat hunting.
Working from the new baseline of converged data and AI-driven response, the next step is to ensure the solution is personalized to your organization with Deloitte’s AI-Native Security Operations Platform. This means having a supportive partner with specific capabilities:
- Meeting your business security posture (wherever it is) with advisory, design, implementation and managed services.
- Migrating your current SIEM capabilities and data pipelines to Cortex XSIAM.
- Working closely with your team to deploy an endpoint product that integrates effectively with Cortex XSIAM.
- Offering a proprietary accelerator to add on top of Cortex XSIAM, designed to automate ticketing and remediation.
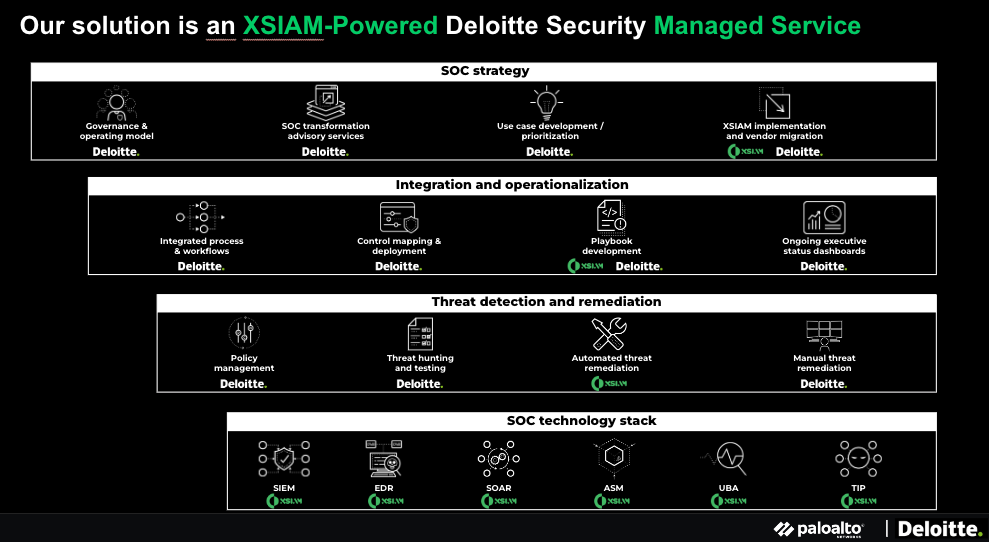
To further reduce the stress on analysts, you can create playbooks in XSIAM to help automate repetitive actions, including remediation (fully recorded with a logging trail to aid in regulatory compliance). Beyond this, Deloitte’s playbooks are built based on common, real-world incidents that Deloitte specialists repeatedly see. These playbooks help you identify and respond to incidents quicker and gain organization-wide value faster.
How It Works in Action
Let’s look at a common scenario: an endpoint firing off an alert.
In a traditional SOC, an analyst swivels to a console, looking at their network behavior anomaly detection to see if the alert also fired there. If it did, the analyst checks the firewall console. This cycle continues across point product consoles and systems as the analyst manually stitches together the context required to make sense of the alert. If the problem is tangled in code full of complex interdependencies and third-party components, the process can take days or even weeks. On top of this complexity, the SOC may receive several alerts across systems for the same incident. This lengthy process provides valuable time for a threat actor to execute their mission.
This process is much simpler in a modernized SOC with Cortex XSIAM and Deloitte accelerators. Rather than a tidal wave of disparate alerts, these alerts across your data sources are grouped and stitched together as incidents. Delivering a single, contextualized, end-to-end story to the analyst. Security events are detected, connected and scored via artificial intelligence/machine learning (AI/ML) into alerts. When correlation exists, they are elevated into incidents. For specific alerts and incidents, automated remediation is triggered, with all activity recorded in a defensible audit trail.
The hours saved automating these processes can be funneled into more valuable efforts that impact the business:
- Tuning the system for an even better response.
- Building additional playbooks.
- Focusing on more complex, critical incidents.
- Proactively hunting threats.
- Creating automation for manually resolved incidents.
- Educating users across the organization on secure work practices.
An Alliance of Global Security Leaders
Palo Alto Networks and Deloitte are an alliance of trusted business advisors and cybersecurity specialists who combine industry-leading technology platforms with leading integration and managed services. Using Palo Alto Networks Cortex XSIAM with Deloitte's security services represents the latest advancement in a longstanding collaboration. Deloitte’s AI-Native Security Operations Platform™ utilizes Palo Alto Networks Cortex XSIAM to provide extended security intelligence and automation management, helping clients consolidate multiple products into a single, integrated platform, cutting costs, improving operations, and increasing analyst productivity.
Together, Palo Alto Networks and Deloitte help clients across a wide range of industries to accelerate adoption through a cyber-first mentality while adhering to regulatory compliance. Visit our alliance websites to learn more:
This posting contains general information only, does not constitute professional advice or services, and should not be used as a basis for any decision or action that may affect your business. Palo Alto Networks and Deloitte shall not be responsible for any loss sustained by any person who relies on this posting.
As used in this document, “Deloitte” means Deloitte & Touche LLP, a subsidiary of Deloitte LLP. Please see www.deloitte.com/us/about for a detailed description of our legal structure. Certain services may not be available to attest clients under the rules and regulations of public accounting.