This post is also available in: 日本語 (Japanese)
Executive Summary
The Cortex Threat Research team has been tracking the widely spread LockBit ransomware since it first emerged in September 2019. Since then, the operations have grown rapidly and new updated versions of the ransomware were released: LockBit 2.0 in mid-2021 and LockBit 3.0 that was released in June of 2022.
The LockBit ransomware operation follows the ransomware-as-a-service (RaaS) model and uses affiliates to distribute the ransomware. The affiliates deploy the ransomware using many varying tactics, techniques, and procedures (TTPs) and attack a wide range of businesses and critical infrastructure organizations worldwide. The operation of LockBit runs as any other “normal” business operation, which contributes to it becoming the most profitable and active ransomware group in the world with tens of victims every month.
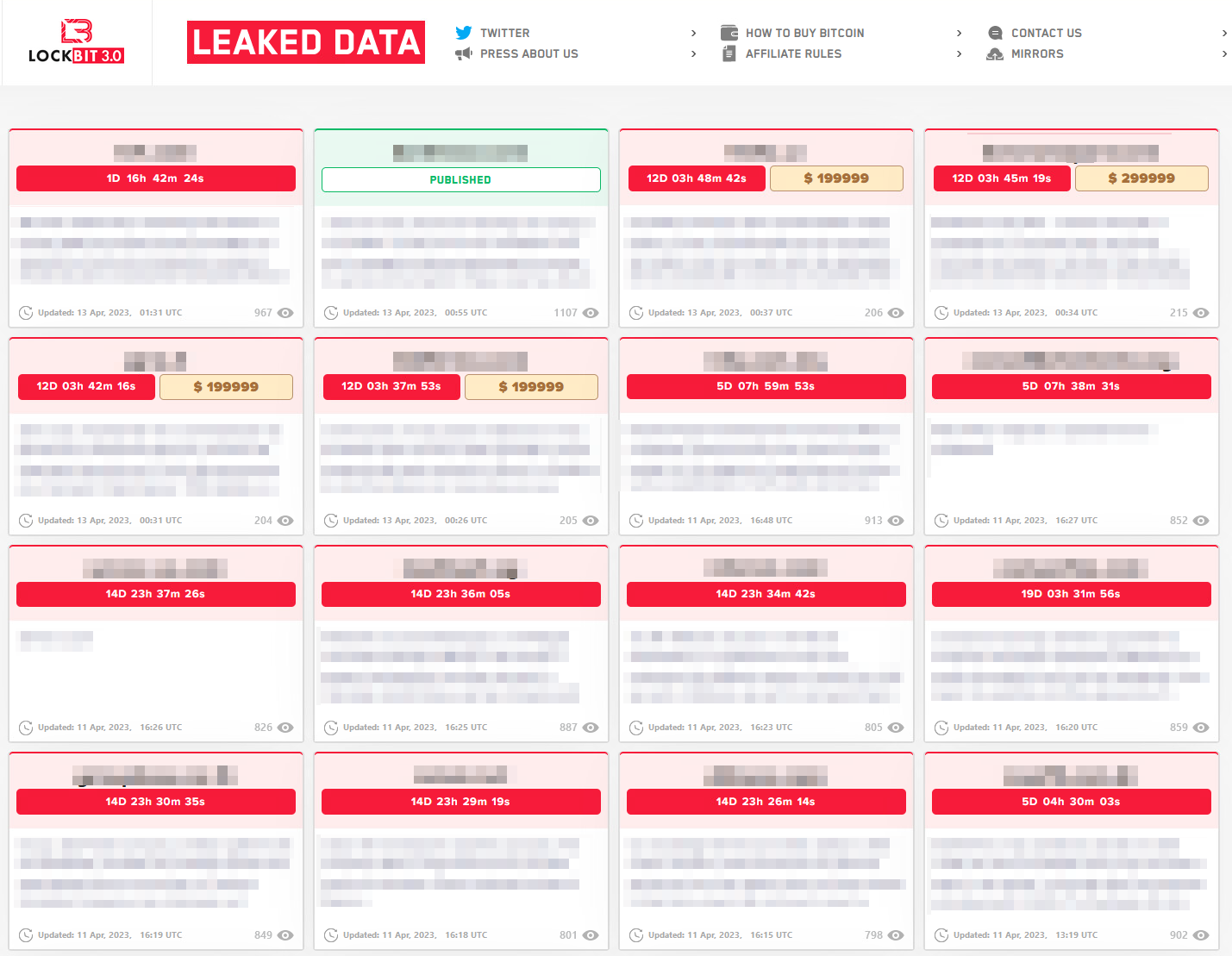
In 2022, LockBit posted information about 801 breached organizations on their leak site, which was an increase of 95% in victim count compared to last year’s entries, according to the 2023 Unit 42 Ransomware and Extortion Report. As of May 25, 2022, LockBit 2.0 accounted for 46% of all ransomware-related breach events shared on leak sites in 2022. The LockBit 2.0 RaaS leak site has published names and information about more than 850 compromised organizations. It's believed that LockBit 3.0 will continue to lead in the ransomware threat landscape in 2023 as well.
LockBit 3.0, also known as “LockBit Black,” was created after some critical bugs were found in LockBit 2.0 in March of 2022. Besides those bug fixes, and even a public “bug bounty” program, LockBit 3.0 was added with additional features that makes it more evasive than ever.
Historically, the LockBit operation uses payloads designed for attacks on Windows, Linux, and VMware ESXi servers. However, in April 2023, an archive was uploaded to VirusTotal containing some test builds that suggests LockBit 3.0 also has payloads for encrypting macOS, ARM, FreeBSD, MIPS, and SPARC CPUs. This marks a significant shift in the ransomware threat landscape as it shows that attackers are now targeting Apple products, which were believed to be almost immune to such attacks.
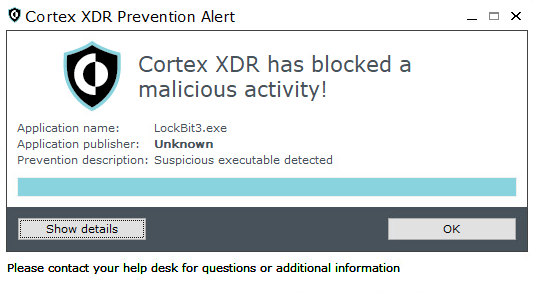
Cortex XDR uses multi layers of protection, including behavioral threat protection and exploit protection, to protect customers against the LockBit ransomware.
Initial Access
As mentioned earlier in the blog, the LockBit ransomware operation follows the ransomware-as-a-service (RaaS) model and uses affiliates to distribute the ransomware. Those affiliates use different attack methods in order to penetrate an organization and eventually deploy the ransomware. Since it can differ from one affiliate to another, it poses a challenge trying to find a clear pattern of attack.
From the information available obtained by researchers and incident responders, the following methods were observed used as an initial infection vector in LockBit attacks:
- Gaining initial access to victim networks via Remote Desktop Protocol (RDP) exploitation.
- Gaining initial access to victim networks via drive-by compromise.
- Gaining initial access to victim networks via phishing campaigns.
- Gaining initial access to victim networks via abuse of valid accounts. Those accounts can be bought in hacking forums or achieved using brute force attacks.
- Gaining initial access to victim networks via exploitation of public-facing applications.
Data Exfiltration
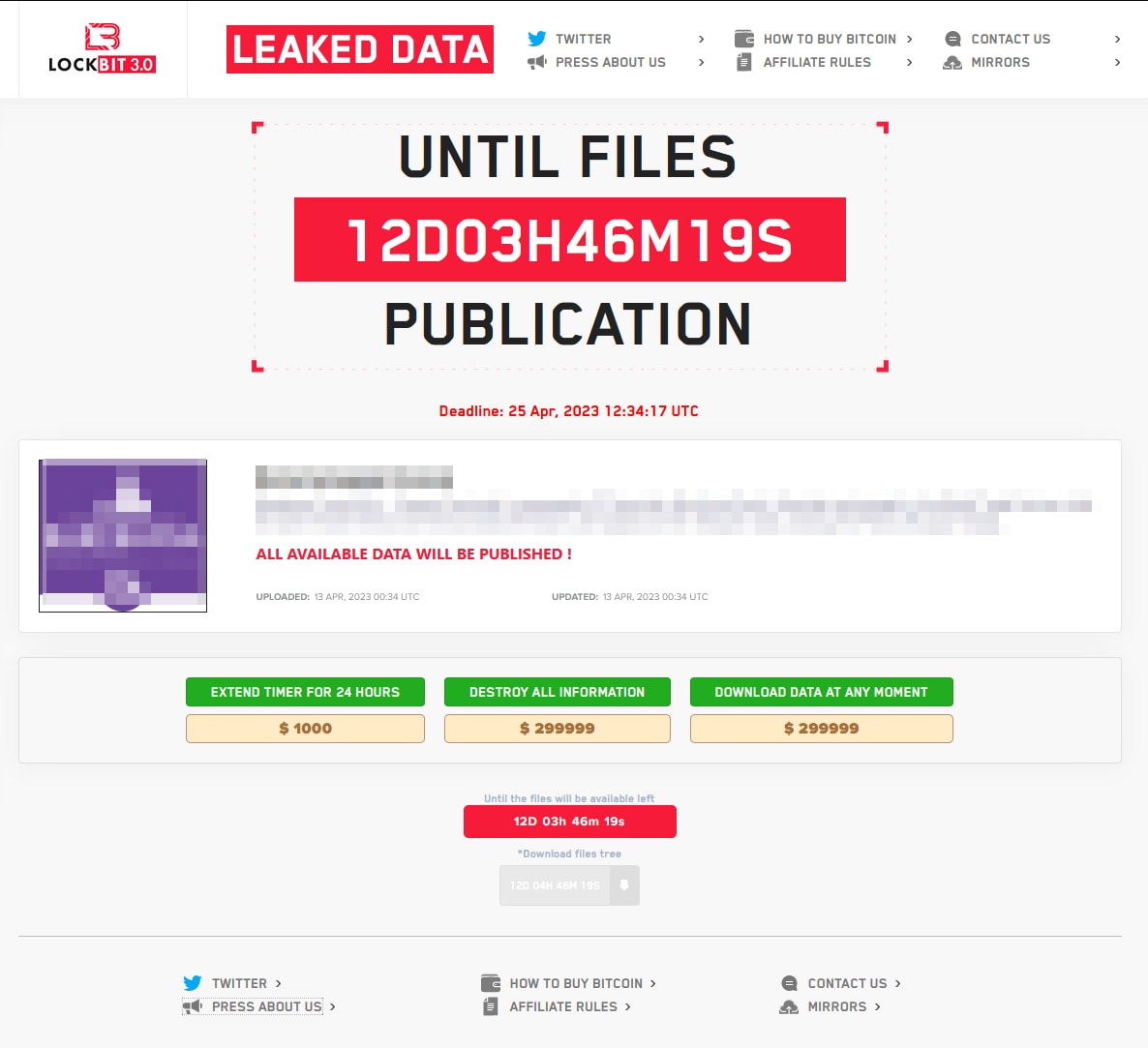
In a similar fashion to other ransomware emerged over the years, the LockBit group follows the growing trend of double extortion. As part of the attack, the operators steal sensitive files and information from their victims and later use it to extort the victims by threatening to publish the data unless the ransom is paid.
From the information available obtained by researchers and incident responders, the following tools were reported abused by LockBit’s affiliates to exfiltrate data:
- WinSCP
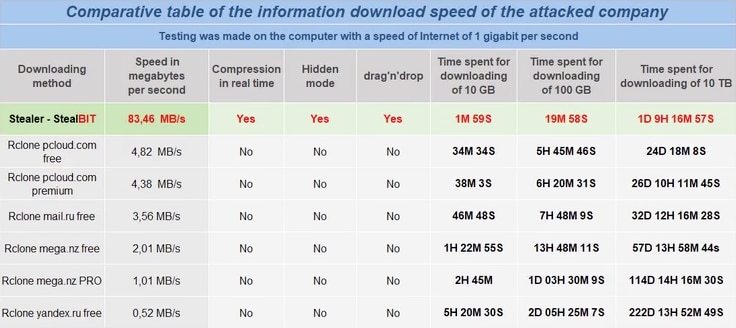
- Rclone
- MEGA Ltd MegaSync
- FileZilla
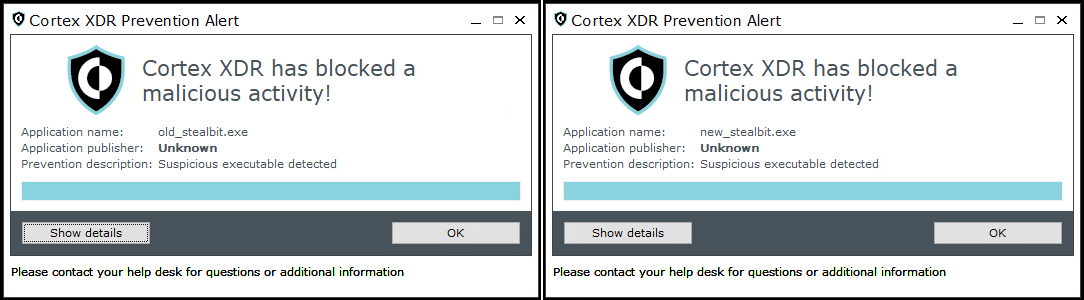
The affiliates operating the ransomware can also choose another tool to perform the data exfiltration - the LockBit team’s tool, StealBit.
StealBit, which was first introduced as part of LockBit 2.0, is given to the affiliates as part of their arsenal that also includes LockBit Windows version and LockBit Linux/ESXi version. According to the group behind it, it’s the fastest and easiest solution to perform data exfiltration.
Interestingly, the older build of StealBit didn’t require a password to operate, but the newer builds, created around July 2022, around the same time of LockBit 3.0, do require a password in order to run.
This is aligned with the overall attempts by the gang to keep their code from being analyzed and investigated by security researchers.
Ransomware Execution
LockBit 3.0 is configured upon compilation with many different options that determine the behavior of the ransomware. Some are built in and some can be turned on by providing a parameter via command line. LockBit 3.0 is equipped with the following capabilities:
- Flexible Windows execution - can be run as an EXE, DLL, reflective DLL, or PowerShell.
- Automatic distribution in the network via admin shares
- Built in port scanner to search for all shares such as SMB, WebDav and DFS
- Printing the ransom note via network printers
- Ability to distribute via Group Policy Objects (GPO)
- Changes extensions, icons, ransom note and wallpaper
- Self Deletion
- Shutting down the machine
- Execute in safe mode to avoid security solutions
- Shutting down processes, services and security solutions
In addition, the group indicates that there is flexibility to add features as for affiliate’s requests, which provides a modular structure to the ransomware.
As mentioned, various parameters can be supplied to further modify the behavior of the ransomware:
| -pass (32 character value) | (Required) Password used to launch LockBit 3.0 |
| -del | Self-delete |
| -gdel | Remove LockBit 3.0 group policy changes |
| -gspd | Spread laterally via group policy |
| -path (File or path) | Only encrypts provided file or folder |
| -psex | Spread laterally via admin shares |
| -safe | Reboot host into Safe Mode |
| -wall | Sets LockBit 3.0 Wallpaper and prints out LockBit 3.0 ransom note |
Table 1. Argument supported by LockBit 3.0
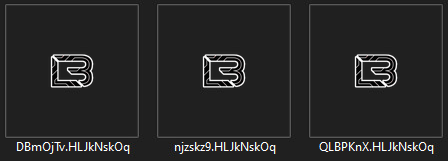
The extension appended to newly encrypted files, as well as the ransom note, differ per victim and contain nine random digits (for example: T0p50Ce4N, Fx44f6z3n, 8GxwvnaA3).
A ransom note is dropped onto the victim’s machine, and contains information about what happened to the machine and how to contact the group and pay the ransom.
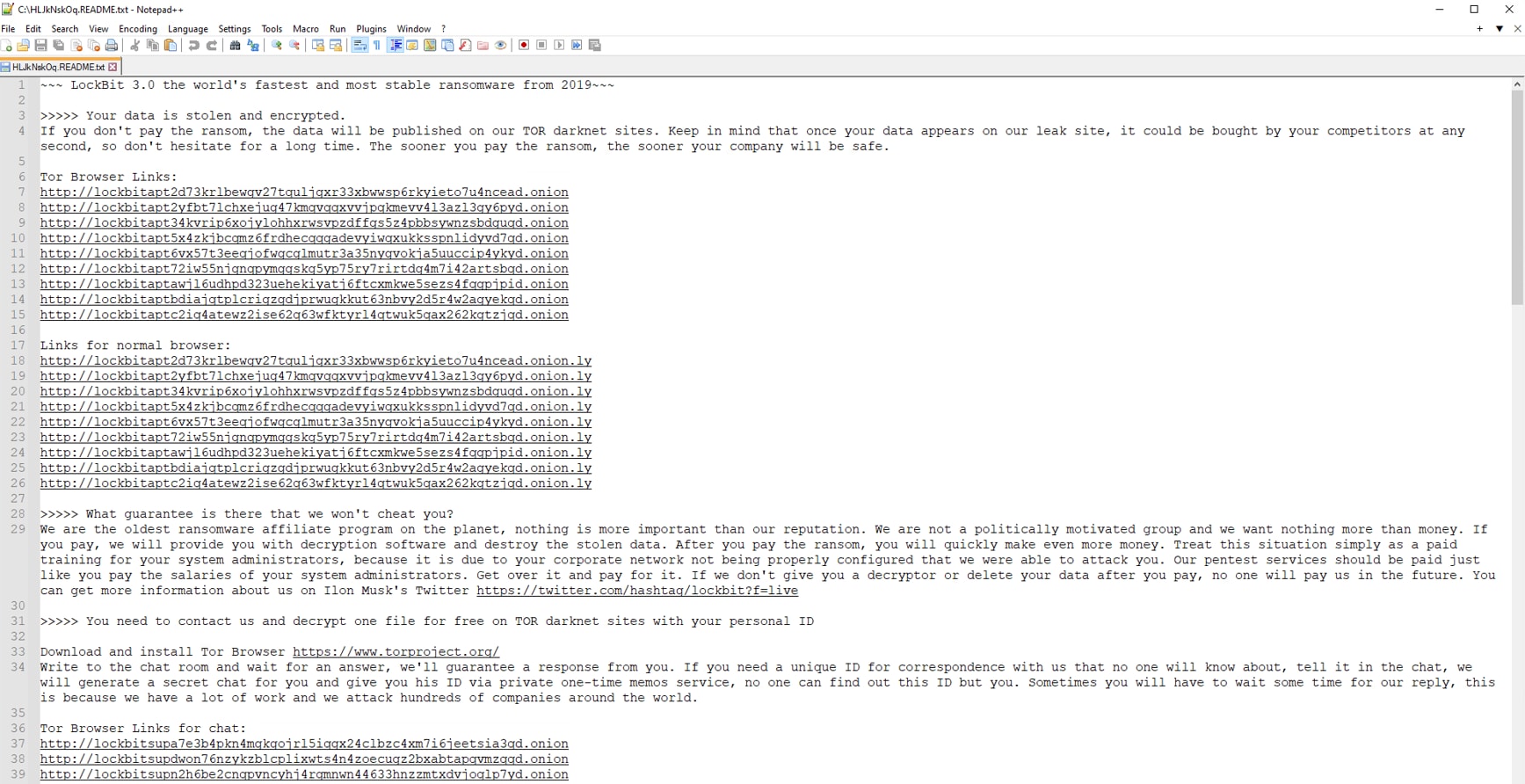
To make sure the ransom note is not missed, LockBit also changes the wallpaper and instructs the user to read the ransom note.
The encrypted files' icons are set to be the LockBit logo.
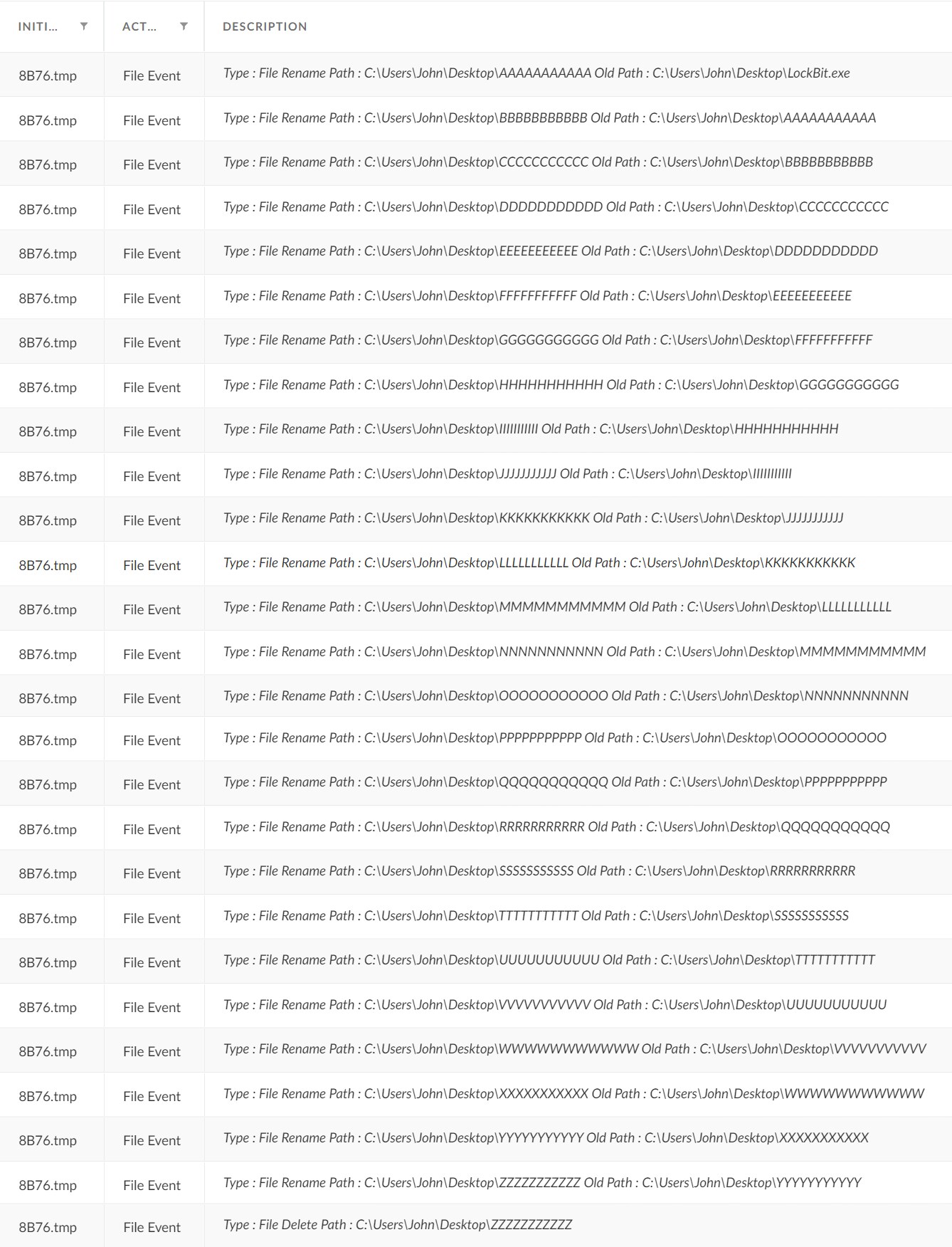
After execution, the ransomware attempts to delete itself. To do so, it drops another executable, in our example 8B76.tmp, that is in charge of removing tracks.
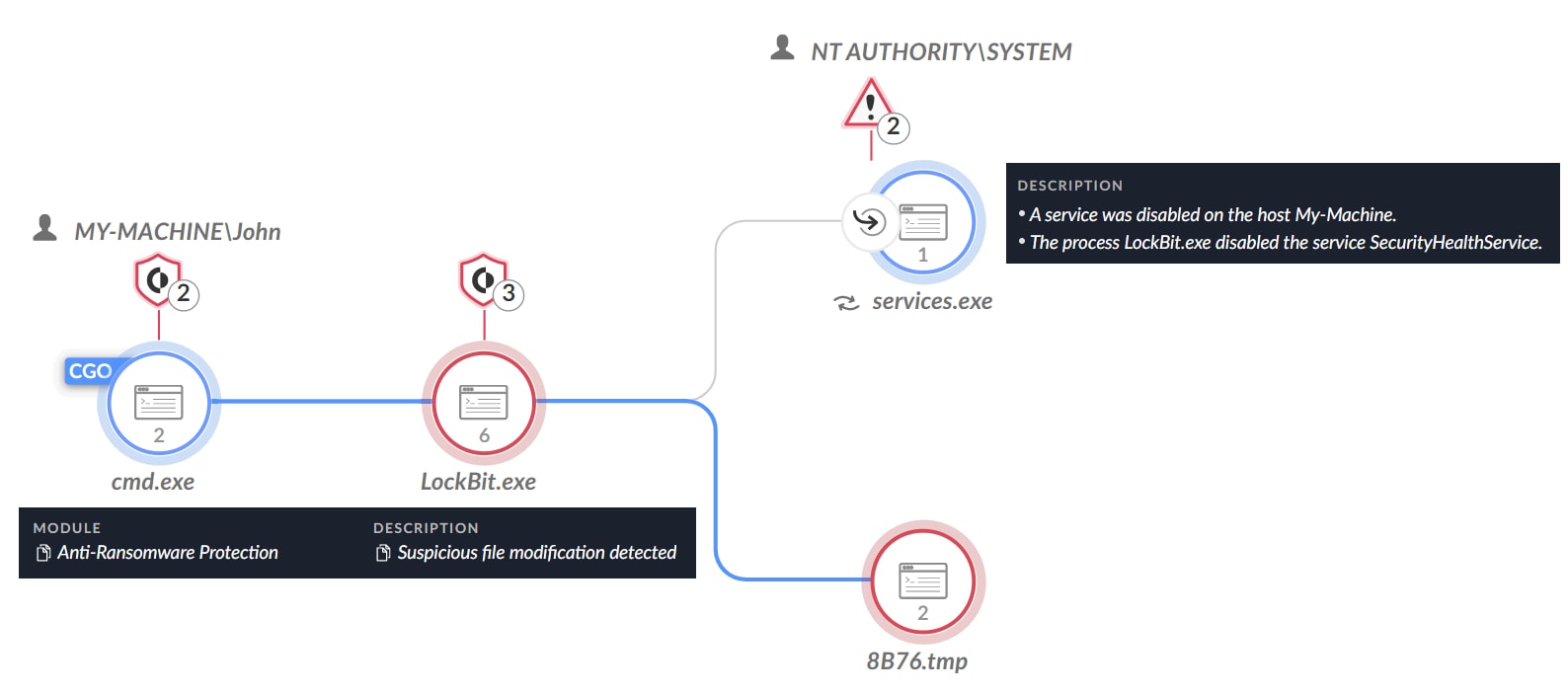
The .tmp file overwrites the contents of the ransomware binary and then renames the file multiple times, with the new file names based on the length of the original file name. In our example, LockBit.exe which has eleven characters (including the file name extension), is renamed as “AAAAAAAAAAA”, and then “BBBBBBBBBBB”, up to “ZZZZZZZZZZZ”, which is eventually deleted by the .tmp file.
This routine can likely be the LockBit ransomware group’s attempt to completely remove tracks and avoid recovery of the ransomware binary by forensic tools. This is aligned with the group’s many attempts to protect their tools from researchers.
Protections and Mitigations
Palo Alto Networks customers are protected against the LockBit ransomware, as well as the StealBit malware.
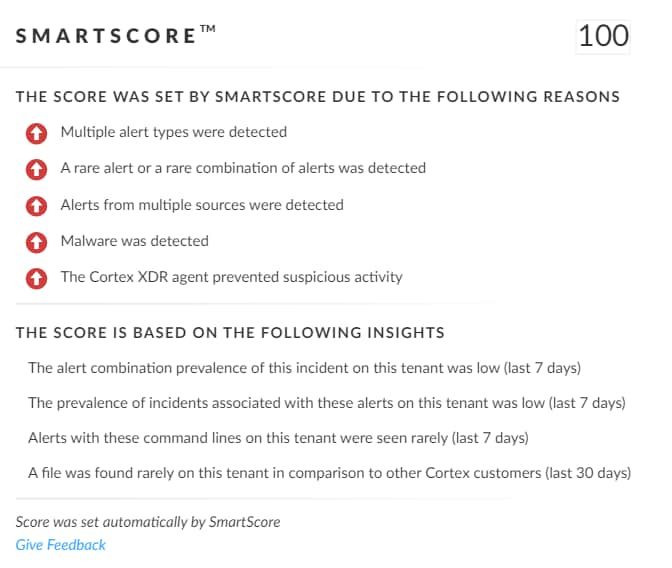
SmartScore, A unique ML-driven scoring engine that translates security investigation methods and their associated data into a hybrid scoring system, scored this incident a 100 score - the highest level of severity.
For Palo Alto Networks customers, our products and services provide the following coverage associated with this group:
- WildFire cloud-based threat analysis service accurately identifies the known samples as malicious.
- Advanced URL Filtering and DNS Security identify domains associated with this group as malicious.
- Cortex XDR detects user and credential-based threats by analyzing user activity from multiple data sources including endpoints, network firewalls, Active Directory, identity and access management solutions, and cloud workloads. It builds behavioral profiles of user activity over time with machine learning. By comparing new activity to past activity, peer activity, and the expected behavior of the entity, Cortex XDR detects anomalous activity indicative of credential-based attacks.
It also offers the following protections related to the attacks discussed in this post:- Prevents the execution of known malicious malware, and prevents the execution of unknown malware using Behavioral Threat Protection and machine learning based on the Local Analysis module.
- Protects against credential gathering tools and techniques using the new Credential Gathering Protection available from Cortex XDR 3.4.
- Protects from threat actors dropping and executing commands from webshells using Anti Webshell Protection as of Cortex XDR 3.4.
- Protects against exploitation of different vulnerabilities including ProxyShell, ProxyLogon and OWASSRF using the Anti-Exploitation modules as well as Behavioral Threat Protection.
- Cortex XDR Pro detects post-exploit activity, including credential-based attacks, with Cortex Analytics.
If you think you may have been impacted or have an urgent matter, get in touch with the Unit 42 Incident Response team or call:
North America Toll-Free: 866.486.4842 (866.4.UNIT42)
EMEA: +31.20.299.3130
APAC: +65.6983.8730
Japan: +81.50.1790.0200
Palo Alto Networks has shared these findings, including file samples and indicators of compromise, with our fellow Cyber Threat Alliance (CTA) members. CTA members use this intelligence to rapidly deploy protections to their customers and to systematically disrupt malicious cyber actors. Learn more about the Cyber Threat Alliance.
Indicators of Compromise
LockBit 3.0
80e8defa5377018b 093b5b90de0f2957f7062144c83a09a56bba1fe4eda932ce
d61af007f6c792b8fb6c677143b7d0e2533394e28c50737588e40da475c040ee
a56b41a6023f828cccaaef470874571d169fdb8f683a75edd430fbd31a2c3f6e
0d38f8bf831f1dbbe9a058930127171f24c3df8dae81e6aa66c430a63cbe0509
d6e94871d7a9a9fd0629831915ccef9d87cfd3778da5e8edb95d90754b76e6c6
391a97a2fe6beb675fe350eb3ca0bc3a995fda43d02a7a6046cd48f042052de5
c6cf5fd8f71abaf5645b8423f404183b3dea180b69080f53b9678500bab6f0de
ef3544a7f6356e7b1e9fc115a112305cef7697e0b0fa29a060d5755372b0d263
3c5c10a4bc148784a86f8d994ad15efa14ec6c7a671f1500c795f22a218e3e69
fd98e75b65d992e0ccc64e512e4e3e78cb2e08ed28de755c2b192e0b7652c80a
c597c75c6b6b283e3b5c8caeee095d60902e7396536444b59513677a94667ff8
2c1dad3e59340259cda94ff6c86e598c65fe82de1b66fb4dfa2494169d89adaa
LockBit 3.0 - .tmp file
917e115cc403e29b4388e0d175cbfac3e7e40ca1742299fbdb353847db2de7c2
b9678789f2c5a55de90d91da6ad03f1013fb77a984df35a0dd2cf333d1b3f820
b1ae7316e73ceebb1b429dd707387bfd12fd489c2af0ed1083895195e7baf119
StealBit
Newer version
021da911374076b34516dd64026563ad72557805b746702b2ab7c7ca274b9ebd
d9279e39d84a30d97da85df64c65f62bd83d6ce8e326e272c7456d04d81c07e1
b625782574e7524f7d990d4142cb370d72829243b0193335c8aeccca59f86670
803469cf8bde18f46cab075132371ee0a4578dc078af16423bfb6c71abafb20d
063257e4bc950ca4b4a6006eae4774dbffcfd0fdef6b8bcbb87ad7bccbb1e7ca
f7788fb208df43e7850b8ffc79bc293010d89d008b9df9b51f44abd0d3dbd54d
cc25452c8940c0d42119e3036669f05e9632469aad6c7059c293cc4511615901
5b56bdd1e4363bf19e78cce5d9f31117e7c3a964e6e700492b4d361403b1ad8a
e779bc97cda0781232814844f13dea9d7215f072a840d89827b63be5b5a3596b
e62dbfb759291720d542b8c56c52f9822edd60df72556899324602e86471be17
Older version
d248a1bb6d93705f9fc2c328222fbbe8c3acceb7c0890f93aba2e7e9c651c86f
6c9a92955402c76ab380aa6927ad96515982a47c05d54f21d67603814d29e4a5
797b76433aa3c786d718094d12e866b8b95f92878ee33ee199de384eff58d090
6b795d9faa48ce3ae31f0bde3dcb61a6d738e8cc0e29b5949d93a5c8ee74786a
8b5f88aeaad4d50c90e0c6dabc5145ef73063e098b22ed7820168aa0954505b2
48b813ad7b27cbb35ab8a871d0c232469a74985e264360831bfd4b3e408bff16
6b9aa479a5f9c6bfee52046c1afa579977dfcde868fdad3f18fdcd1779535068
cd6483b93cecb1aa4d1acf8ba1ec8eaba293b2af224f9b70760bf278ee8fbe29
4b2b0c99b88e3fa7542165be931e2fd863f5546bbae71e9e8f21e2f3a1ebdda5
ce6b07c00894fd72d7733f12b42b82bb58691f83458cc0a4f1414328df8c1c79
465a6d931492ca980ec7ef0293c02b373598760f6d2df39cc621cf0fd50b8113
968875370dbc26a6439860f854c91f9ee675e588f8dbf78e6cb7e20b6d957bec
a55255d5ba2607e687c35ce8264a906337ff898139174f5d85400e8a3f92a0e5
460e555466911f833cc90c95f5dd9628a96ff08872a1fd2f5e20b528da5840f2
26f8447d9f9e230d31cf43b991b85f336af604405572d3b817d4e54bd722bd3d
Additional Resources
- https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-075a
- https://news.sophos.com/en-us/2022/11/30/lockbit-3-0-black-attacks-and-leaks-reveal-wormable-capabilities-and-tooling/
- https://www.cybereason.com/blog/research/cybereason-vs.-lockbit2.0-ransomware
- https://thehackernews.com/2023/03/lockbit-30-ransomware-inside.html
- https://blogs.vmware.com/security/2022/10/lockbit-3-0-also-known-as-lockbit-black.html
- https://www.wired.com/story/lockbit-ransomware-attacks/
- https://security.packt.com/lockbit-3-0-a-deeper-look/
- https://techcommunity.microsoft.com/t5/microsoft-security-experts-blog/part-1-lockbit-2-0-ransomware-bugs-and-database-recovery/ba-p/3254354
- https://www.sentinelone.com/labs/lockbit-3-0-update-unpicking-the-ransomwares-latest-anti-analysis-and-evasion-techniques/
- https://www.trendmicro.com/en_us/research/22/g/lockbit-ransomware-group-augments-its-latest-variant--lockbit-3-.html