Improve your ASM Program Efficiency with Self-Service User Management and Remediation Guidance
Today, we are announcing Self-Service User Management (SSUM) and Remediation Guidance to all Cortex Xpanse customers to help reduce their cyber risks, and make user management easier and remediation faster.
The latest ESG report observes that the responsibility for managing an external attack surface is split across the security group (16%), IT and operations group (41%), or a combination of the two groups (43%). The common theme is that multiple teams within an organization find value in an ASM solution. Consequently, access to the platform is shared across multiple teams, and to make it easier for these teams to provide access and manage their users, the Xpanse team has introduced Self-Service User Management. SSUM offers customers greater control in managing their users across the attack surface management lifecycle.
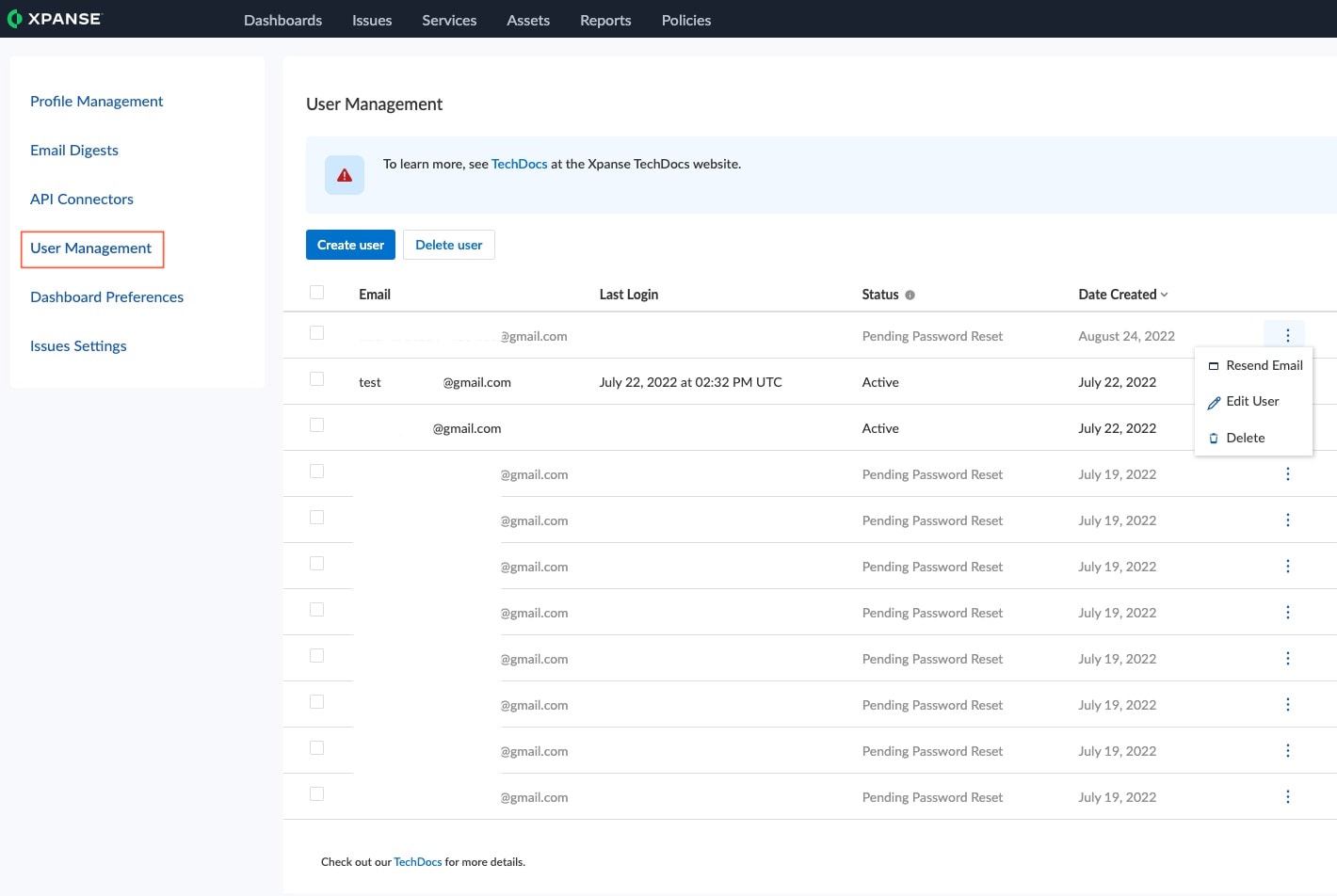
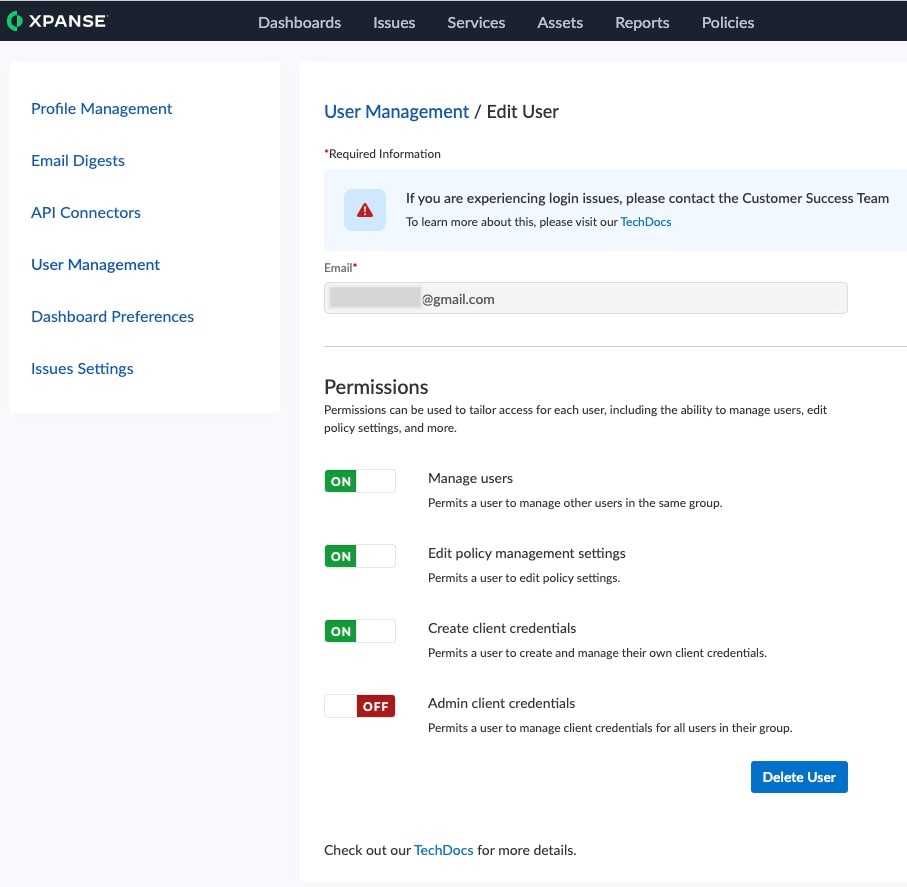
Self-service user management enables you to add new users, remove users, and change the permissions of existing users in Expander. You no longer need to reach out to your customer success manager to perform these tasks. With SSUM, you can effortlessly manage your users in real time and at your convenience.
Apart from allowing you to create new users, SSUM allows you to assign existing users additional permissions, revoke permissions, and delete users if needed.
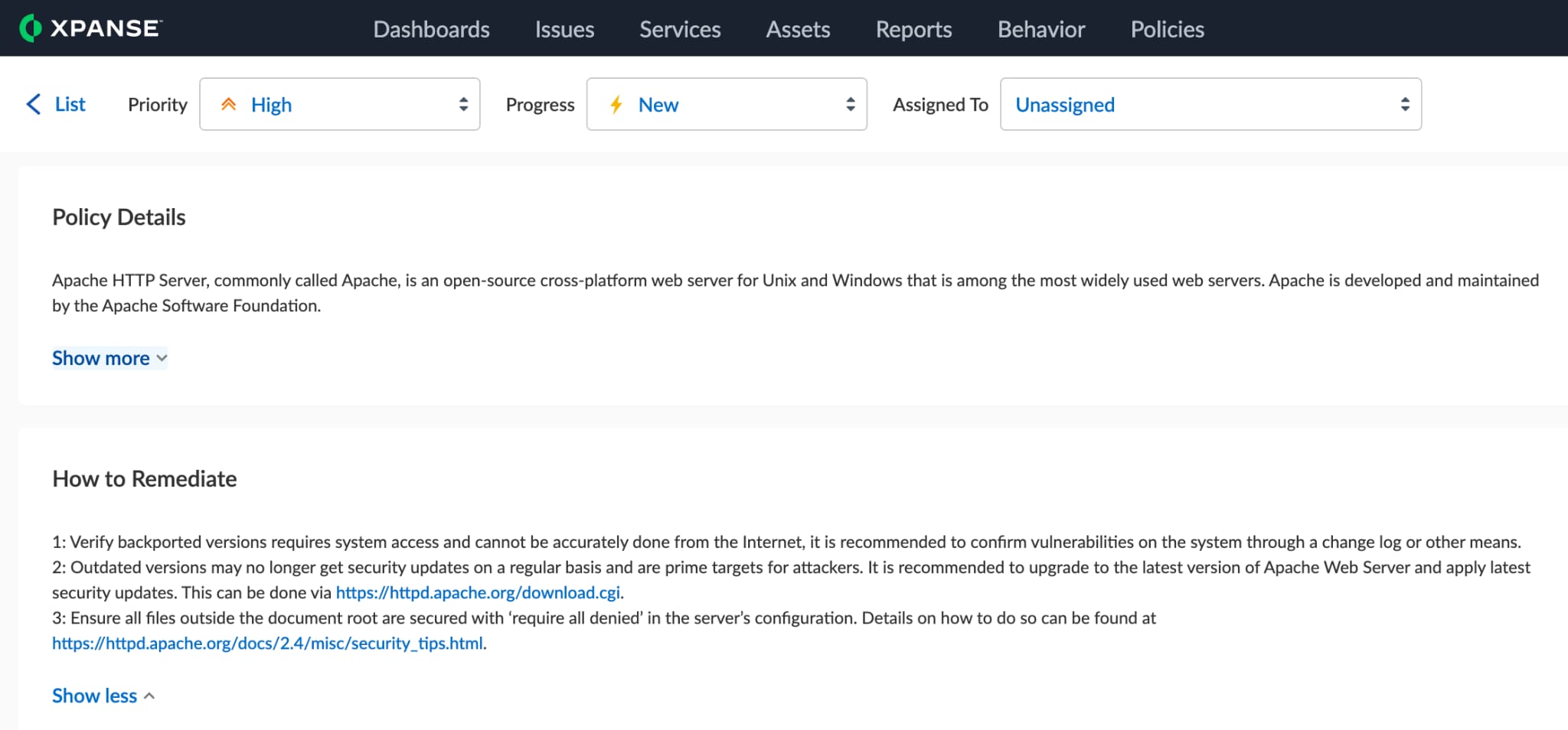
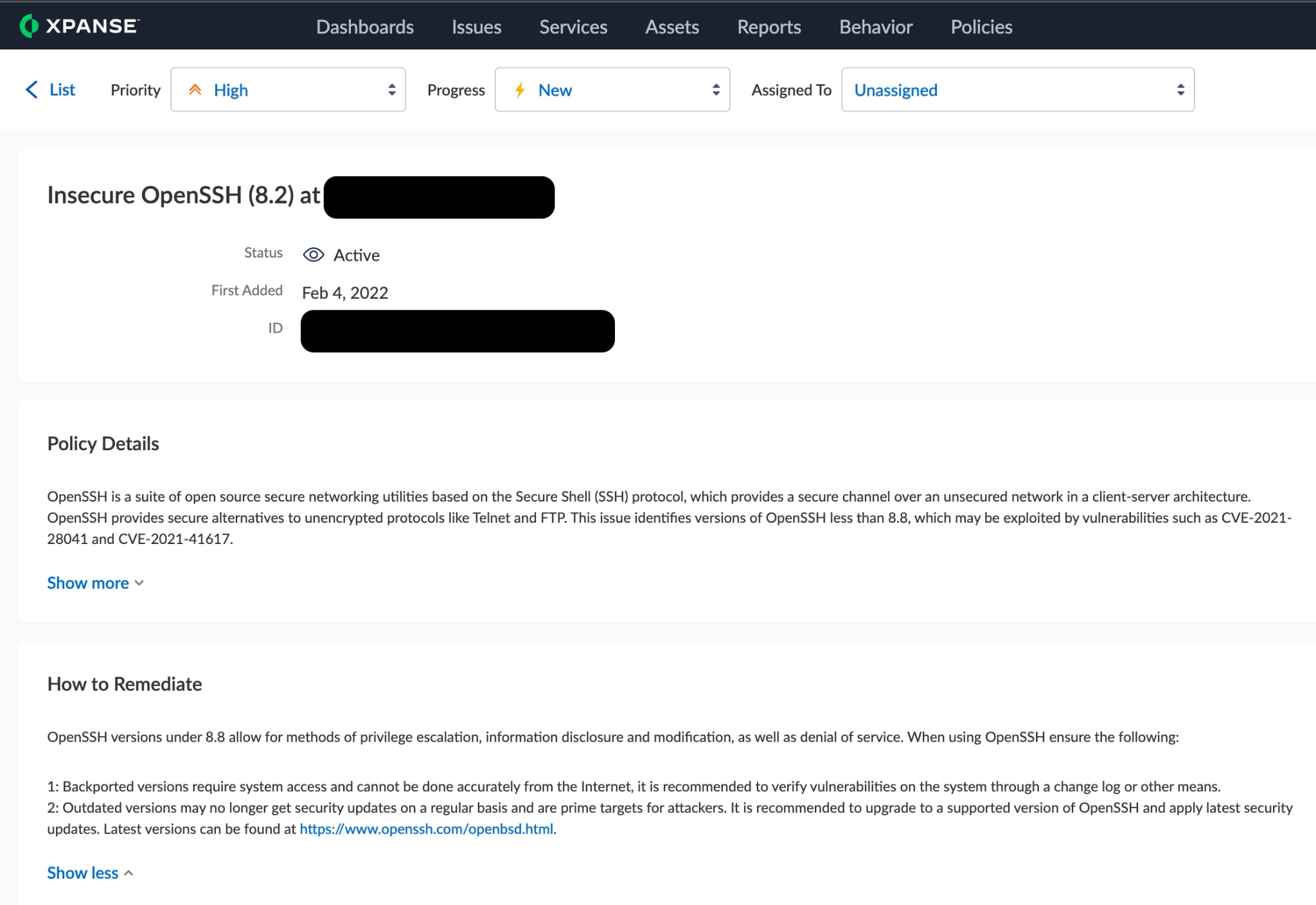
While it is essential to understand an organization’s unknown unknowns, it is far more important to remedy these critical exposures to the public internet. On the path to helping customers manage their entire attack surface management lifecycle, Xpanse is rolling out Remediation Guidance to all users.
Remediation Guidance will provide customers recommendations from the Palo Alto Networks Security research team on resolving specific issues. It provides insight into questions customers might have about the risk of exposing the service/application, whether that risk is acceptable, what steps should be taken to take the service off the internet or what to do when that action is not possible. In the future, the Remediation Guidance team will also point the security analyst toward the latest research from the Unit 42 threat research team concerning more details about the issue seen in their environments.
Learn More About Remediation Guidance Here
Xpanse continues to help organizations in their pursuit to manage their continuously growing attack surface, as the absence of an ASM Program comes at a cost. To learn more about how your organization can benefit from Cortex Xpanse, download the “Value Drivers for an Attack Surface Management Program.”