Continuous asset discovery and monitoring
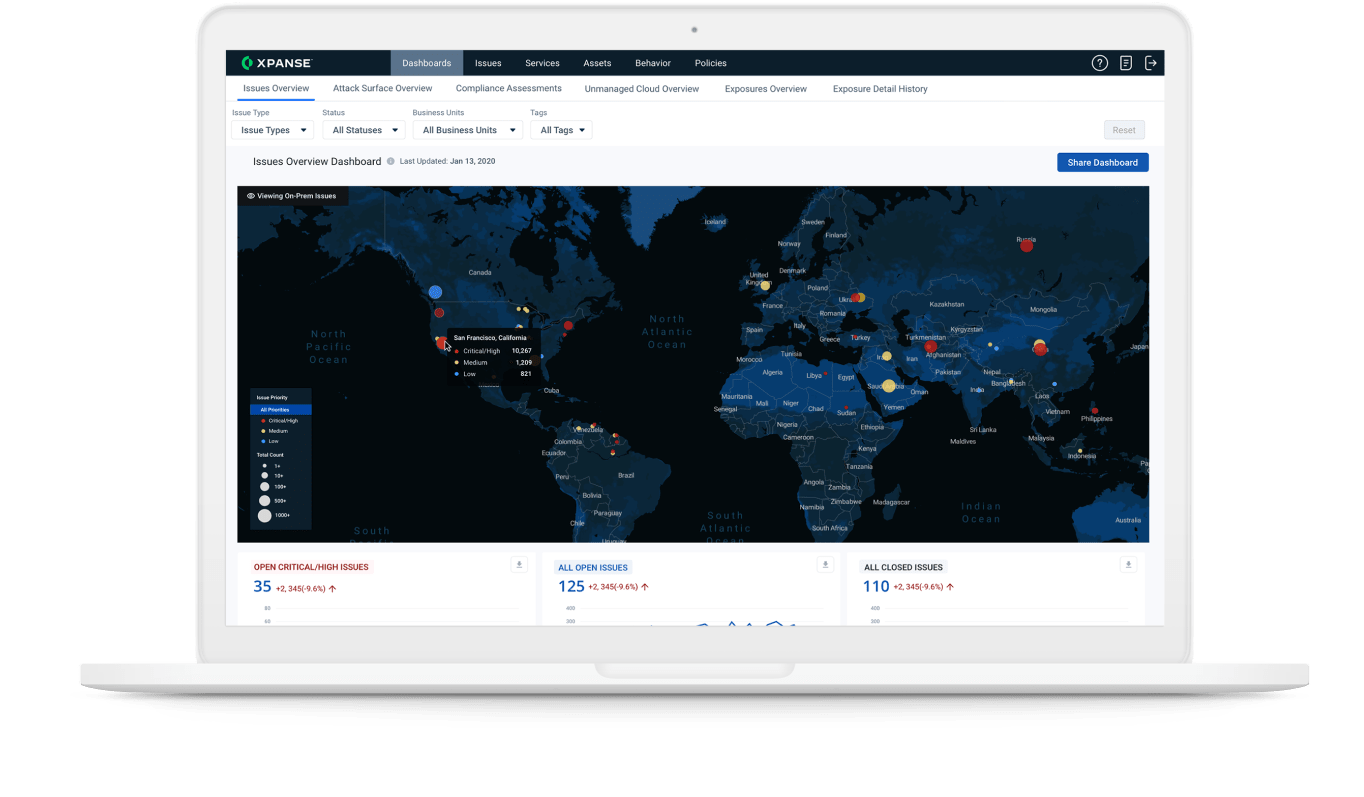
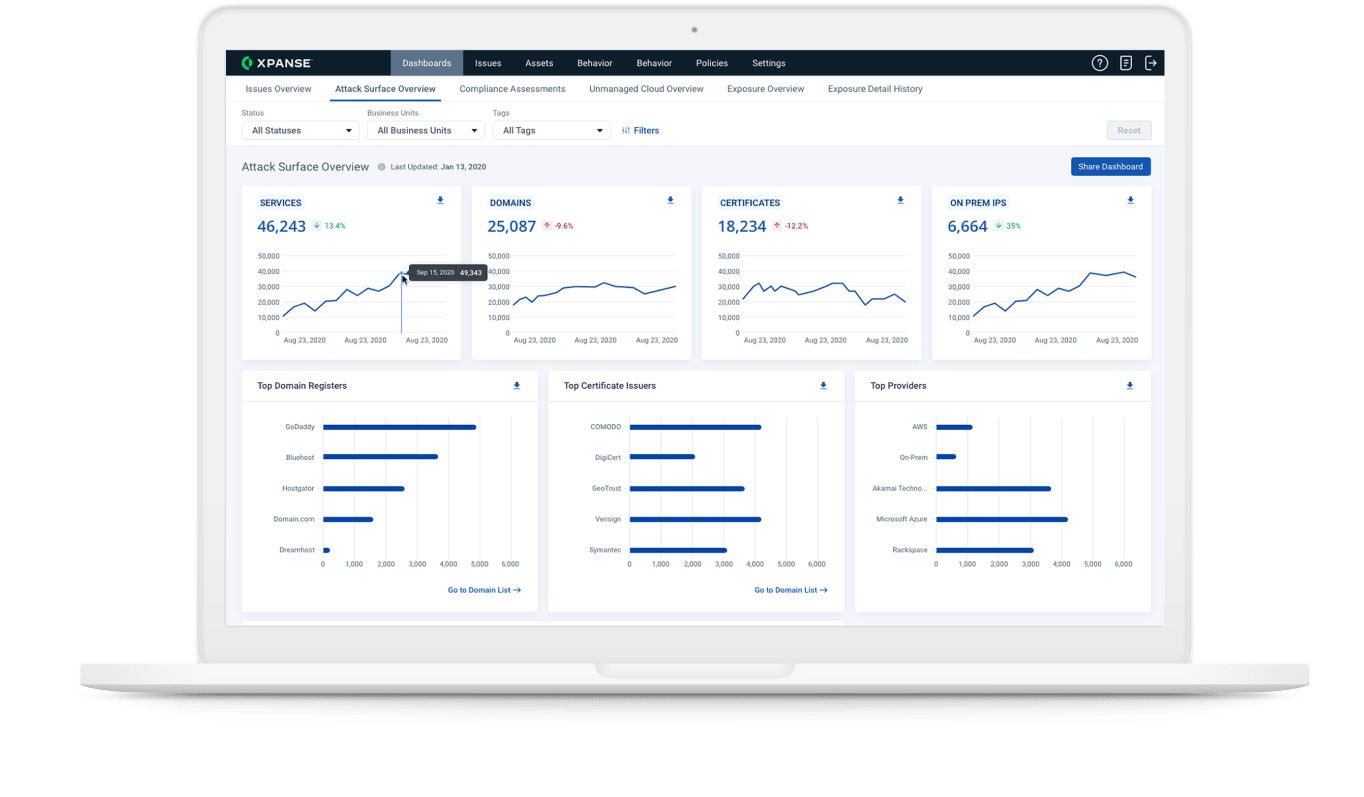
Xpanse scans the entire IPv4 space several times per day to uncover all your internet-connected assets. It monitors changes to cloud assets that may put them at risk, even if those assets were unknown to you.
No more unknown assets
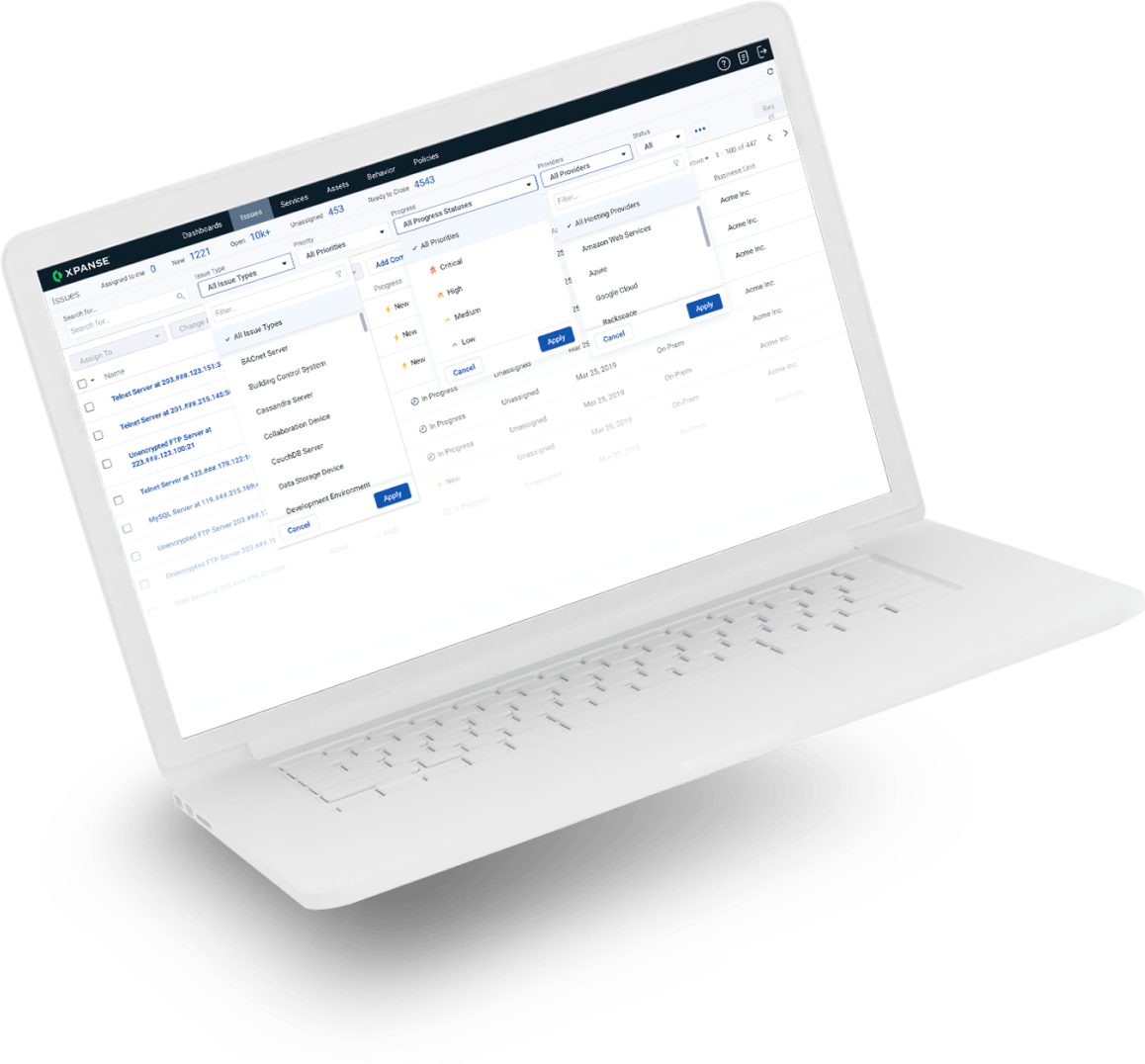
Maintaining compliance relies on having a constantly updated single source of truth. This ensures there is no unaccounted asset.
Continuous monitoring
Cloud assets can appear in minutes. Misconfigurations and accidental exposures are common. This is why you need continuous monitoring of internet assets.