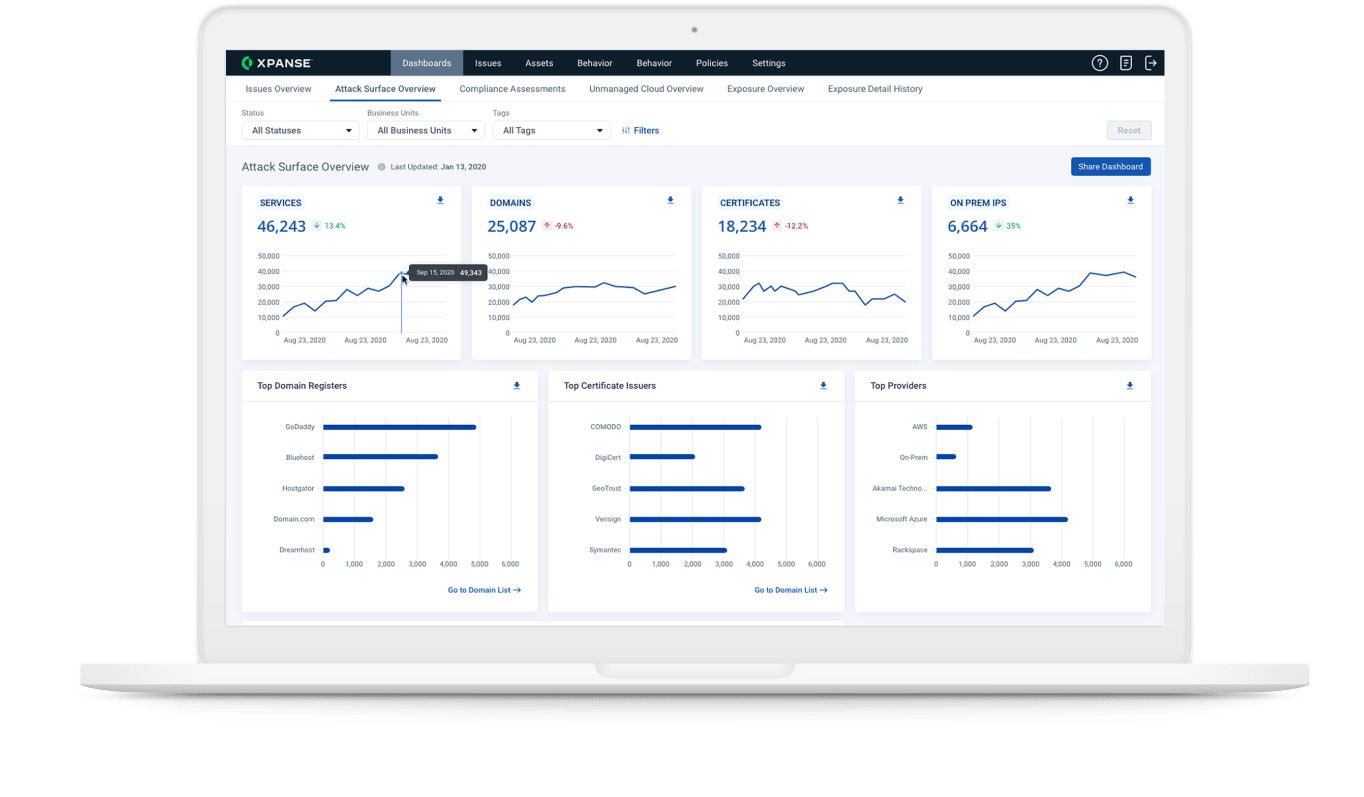
Streamlined IOM
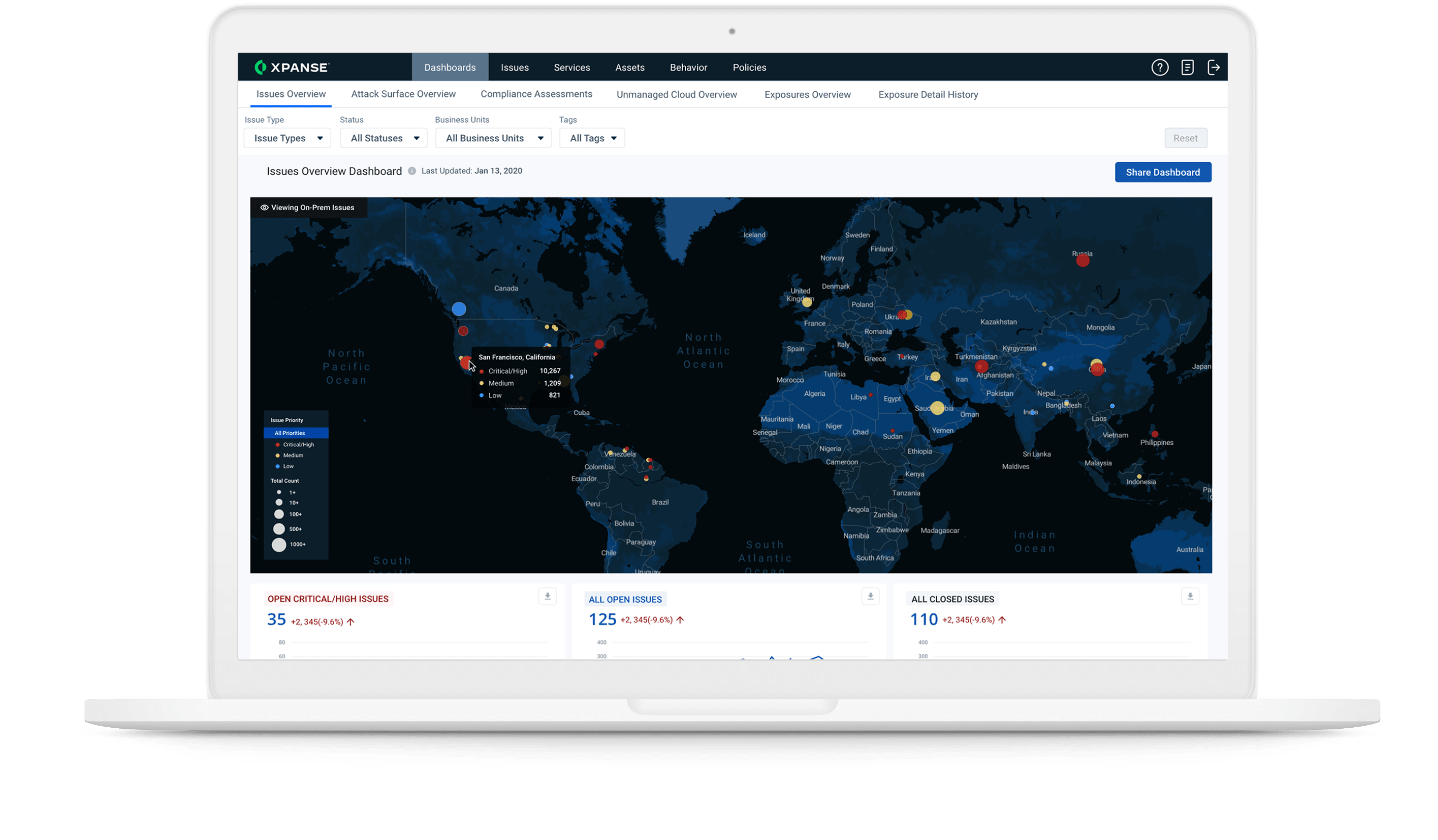
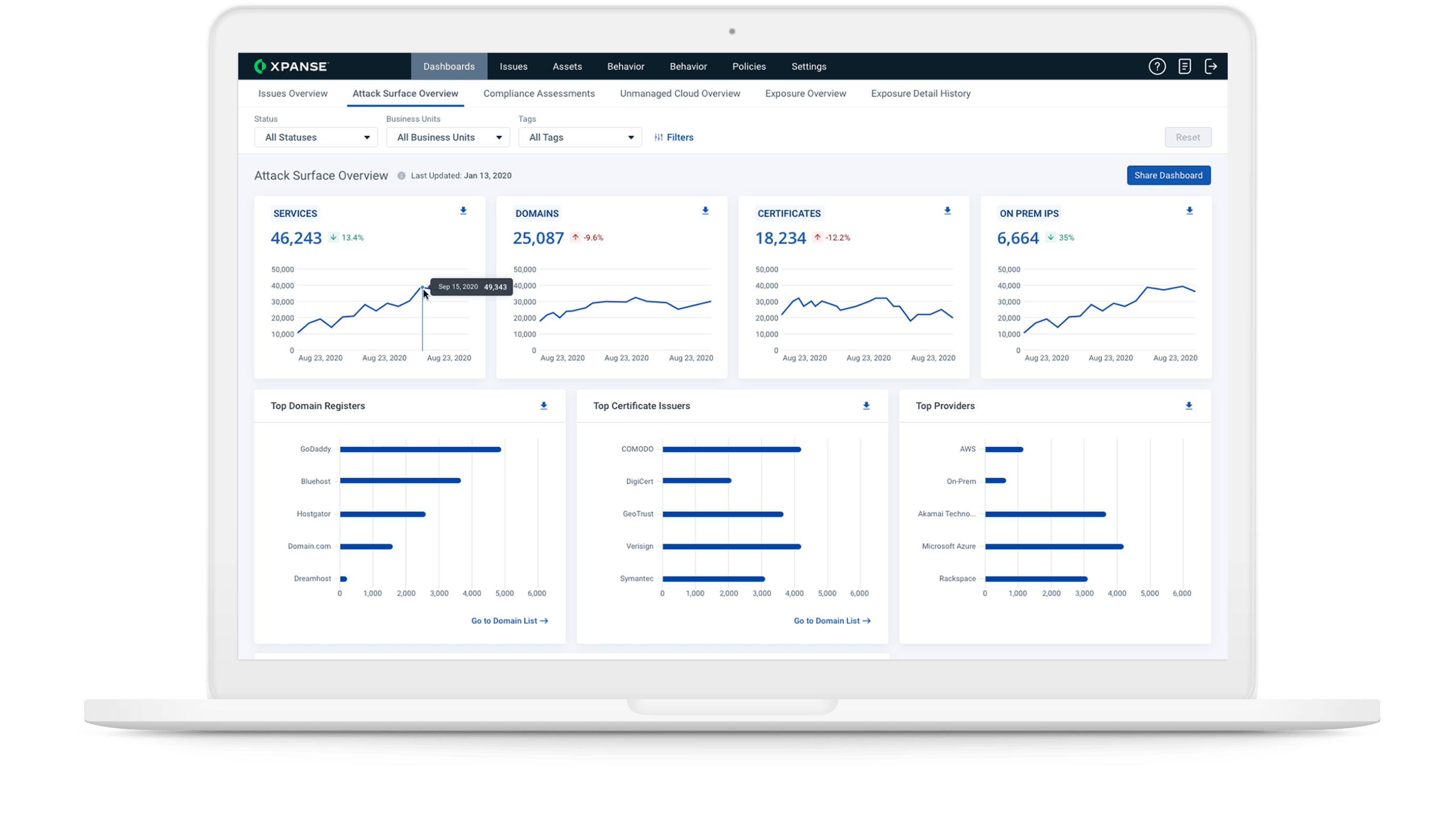
Hostile nation-states and other bad actors relentlessly probe the networks of federal, state, and local governments. Get 24/7 visibility into all internet assets. It empowers government organizations to remediate vulnerable assets before malicious actors get to them.
Understand remote worker security
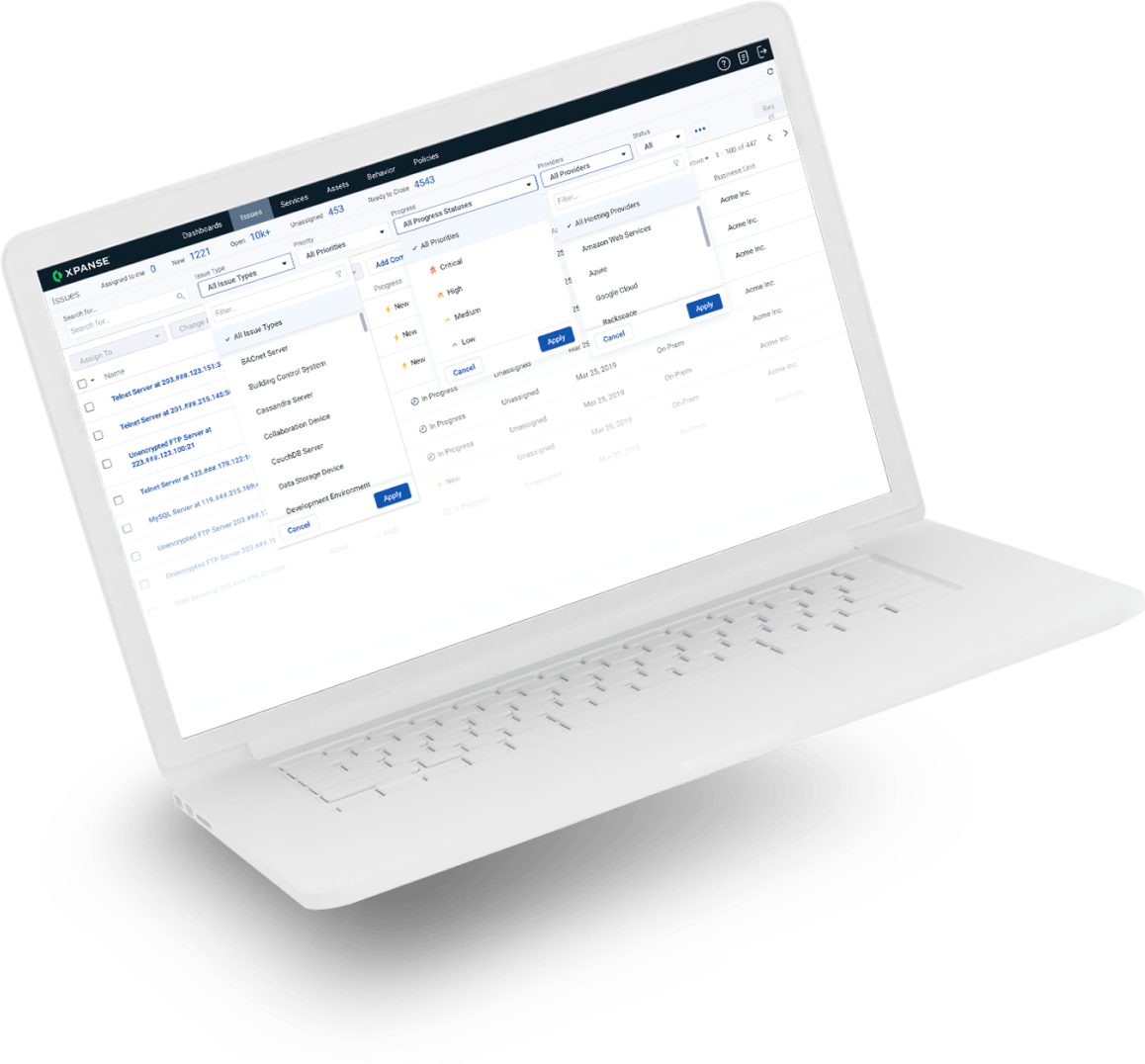
In a highly federated environment with workers constantly on the move, knowing the security posture of remote networks is critical.
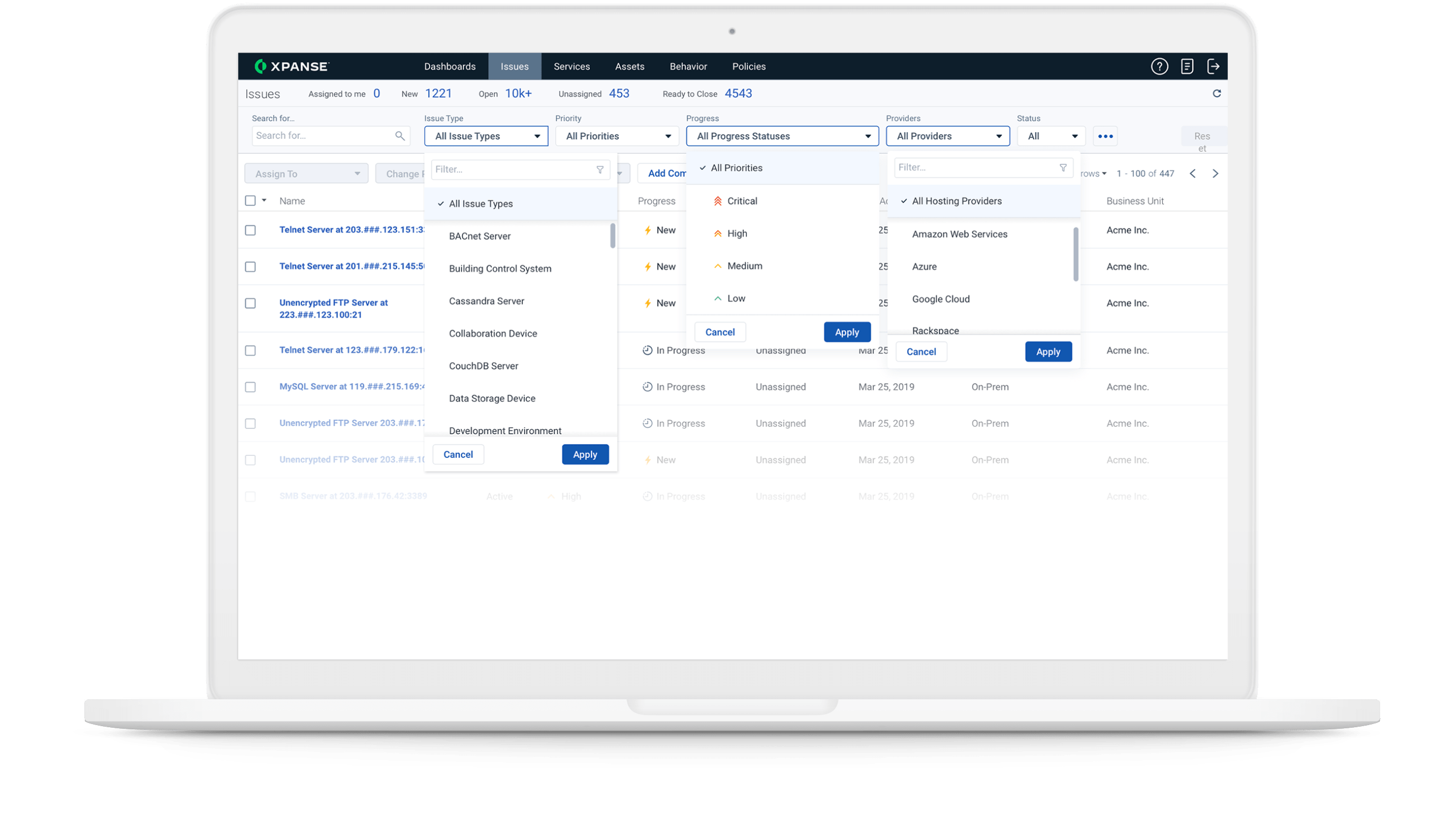
Shared governance across multi-tier networks
Security teams, contractors and subcontractors work jointly to prevent weak links. Meet risk management objectives based on continuous monitoring of tiered multi-level operations.