Attackers have an unfair advantage
Attackers scan the entire internet for vulnerabilities within 45 minutes. Meanwhile, enterprises take an average of 3+ weeks to find and fix them.
They’re actively looking for weaknesses. Are you?
Attackers scan the entire internet for vulnerabilities within 45 minutes. Meanwhile, enterprises take an average of 3+ weeks to find and fix them.
They’re actively looking for weaknesses. Are you?
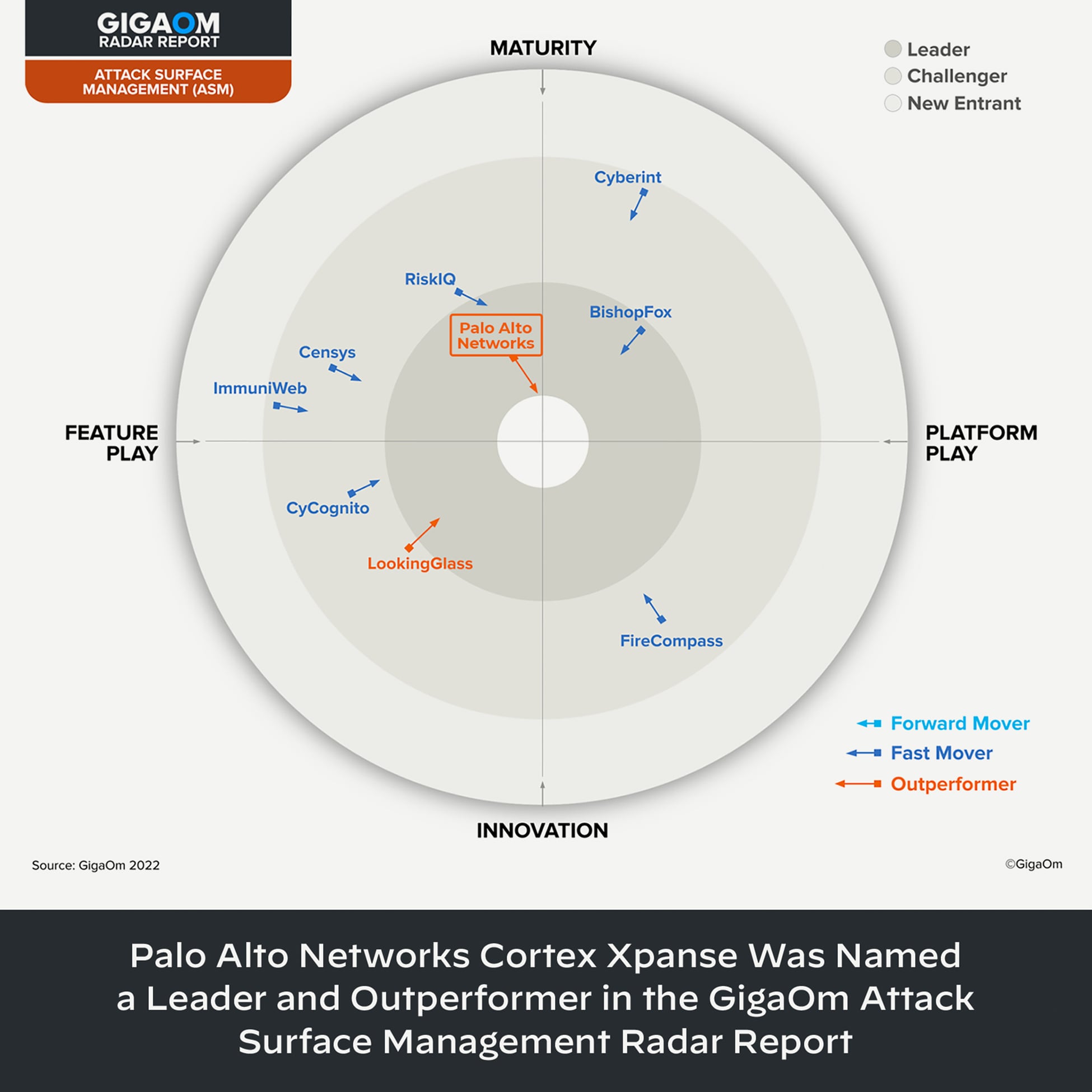
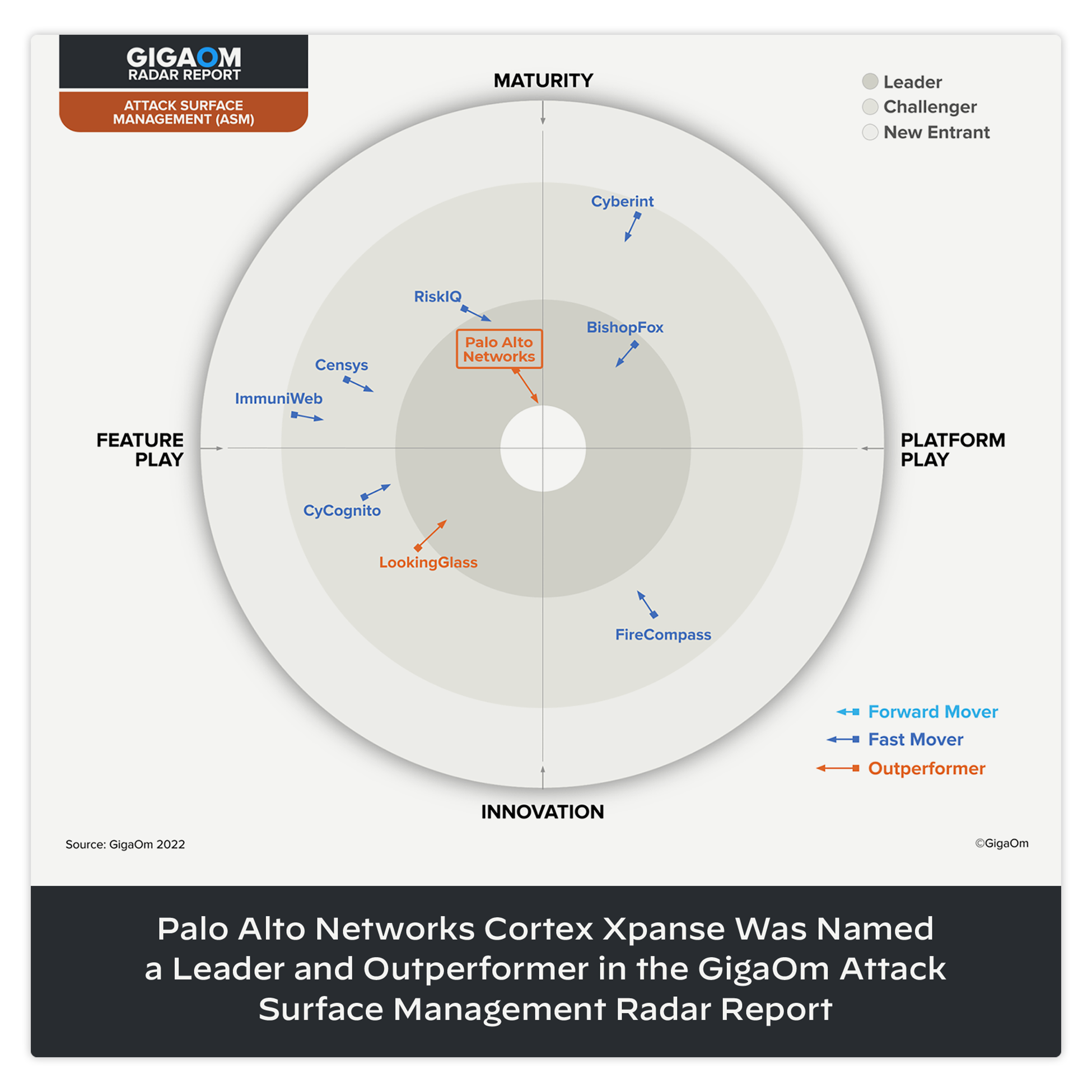
The move to hybrid work and the cloud have scattered your IT infrastructure, creating cracks in your security programs. Attack surface management (ASM) actively discovers, learns and responds to your unknown risks in all connected systems and exposed services.
Fight back with Active Attack Surface Management.
Legacy vulnerability scanners scan infrequently. Security ratings and periodic pentesting are fine for your known assets. But what about the 30% or more assets that you’re not monitoring?
PORTS SCANNED DAILY
IPv4 ADDRESSES SCANNED MULTIPLE TIMES A DAY
BRANCHES OF THE U.S. MILITARY USE XPANSE