It’s always a good idea to look up and down – as well as from side to side – when threats abound. Ask any horror film protagonist or big-city pedestrian. Yet even the threats these folks confront seem insignificant compared to the alarming challenges network security architects face. They’re trying to manage – all at once – software-defined networking (SDN) environments, tools and platforms such as private clouds, VMware NSX-T, VMware NSX for VSphere and Nutanix Flow. How do you stay vigilant in several places simultaneously and stay calm?
While people fighting monsters (or avoiding maniacs behind the wheel) usually have the luxury of taking on their challenges in one surrounding at a time, network security teams responsible for SDN environments defend against threats all over the place: In private clouds and virtual networks, as well as in on-prem data centers and public cloud environments. Understanding how these environments interact can go a long way in helping network pros manage security with confidence.
Because network traffic flows inside and between all of these settings, network security professionals need to think about managing overlapping boundaries and environment-specific trust zones – not just the traditional north-south traffic challenges now found on increasingly blurred perimeters and east-west traffic hazards that can span environments.
This makes a holistic approach to security critical within and beyond SDN environments. Data, workloads and applications will continue to be dispersed, which increases the odds that threats will proliferate and hijack network traffic everywhere – and from every direction.
Complex SDN Environments Require Both Flexibility and Vigilance
SDN environments are a good place to start thinking holistically, because there’s usually a lot going on and things can get complicated fast. To stay vigilant in several virtualized places at once, network security teams leverage SDN platforms and tools such as VMware NSX-T, VMware NSX for VSphere, and Nutanix Flow to implement microsegmentation. This isolates individual workloads within SDN trust zones and helps reduce an organization’s attack surface.
But as important as microsegmentation is for locking down virtual environments, it can also create a false sense of security.
Yes, microsegmentation effectively isolates workloads from each other, which closes the door on some malicious traffic. However, many workloads still need to interact with other workloads or particular network services to function properly, which means that network security teams routinely punch holes between microsegmented boundaries to make sure the business stays in business. It’s risky, though, because attackers can take advantage of these allowed connections to move laterally in the environment.
That necessary risk can be found, for example, in financial applications that need to communicate with DNS servers located in a different trust zone. Other applications can also reside in different trust zones. A web-based ordering system might send and receive sensitive customer information to and from a database in a high-trust segment, as shown below:
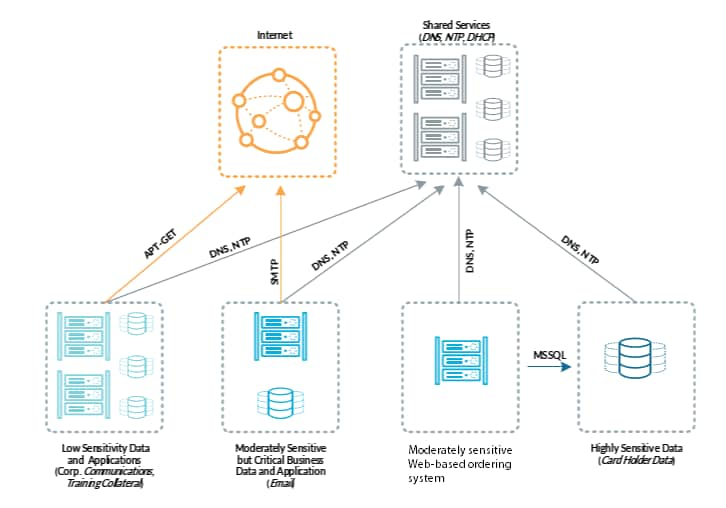
Unfortunately, microsegmentation by itself doesn’t detect or respond to threats. Additional protection is needed to inspect traffic for threats that can move laterally throughout allowed connections in NSX and other SDN environments – and that’s critical when communications between microsegmented workloads are opened up so traffic can flow between between trust zones.
What Does it Take to Hit Moving Targets in an Expanding Universe?
Intrusions are inevitable in SDN environments, but damage can be limited by deploying security tools that limit and detect threat movement. This allows security teams to respond quickly and effectively and prevent data loss. These security tools must also provide protection beyond SDN environments. In addition to virtualized workloads, data center and campus perimeters must be secured and physical networks segmented while trust boundaries need to be established between physical, virtual and public cloud workloads.
Network security teams are best served when they can enforce the same threat prevention policies consistently throughout the enterprise environment. Communication across different workload types residing in different trust zones is increasingly common, as are trust zones themselves being located on physical, virtual, and public cloud networks.
Advanced threat prevention, including intrusion prevention, is a must to secure traffic that moves between trust zones, especially when the levels of trust differ. Intrusion prevention systems (IPS) help security teams monitor the network for malicious traffic to ensure that only known, acceptable services are running.
VM-Series Virtual Firewalls Get in the Zone to Detect, Inspect and Prevent Threats
Deploying next-generation firewalls is a best practice for securing traffic between a trusted zone and a completely untrusted zone – if those firewalls come with capabilities such as DNS Security and URL Filtering—to help guard against data exfiltration.
And that’s where VM-Series virtual firewalls play a large role in securing boundaries and trust zones. These virtualized instances of the Palo Alto Networks Next-Generation Firewall provide a full suite of threat prevention and exfiltration prevention services, including intrusion prevention, DNS security and anti-malware capabilities. By taking a Zero-Trust approach, they identify and block exploits, stop malware, and prevent previously unknown threats from infecting sensitive information and critical systems.
For example, a unique single-pass architecture ensures that VM-Series firewalls inspect every packet to prevent attacks from circumventing the built-in Layer 7 protections NSX provides. And because SDN security must consider other environments as well as its own trust zones, these virtual firewalls can be automatically and repeatedly deployed on a wide range of private and public cloud environments, such as Cisco ACI and ENCS, KVM, OpenStack®, Amazon Web Services (AWS®), Microsoft Azure®, Oracle Cloud® Infrastructure, and Google Cloud Platform (GCP™).
What’s more, a single pane of glass ensures consistent management of policies and activities so network security teams can see all their environments holistically – and protect their NSX investments along with other components of their networking infrastructure.
To find out more about how VM-Series virtual firewalls secure overlapping boundaries and trust zones, see these specific SDN security resources.