A single nebula can span light-years in the distance, occupying trillions of miles in space. Its sheer mass is impractical to fathom, not dissimilar to the amount of data needed to power the machine learning that detects the elusive and unknown threats plaguing security teams.
As today’s unknown threats become more sophisticated, automated, and difficult to prevent, we need a new approach to secure modern enterprises. Our upcoming webinar is the first episode in a series of technical deep dives. It will explore campus, data center and branch security with the goal of defining what type of network security is needed at the internet edge to secure your web gateway and at the segmentation layer of your network to secure against lateral movement. We’ll also get into the groundbreaking technology behind the innovations needed in hardware to deliver prevention inline from verdicts derived in the cloud.
Join us for the first episode of our six-part webinar series! In episode one, we’ll get into the nitty gritty of our new NGFW and security infrastructure that redefines what was thought possible – the prevention of advanced evasive threats as they happen.
The Shift in Network Security
In March, we introduced PAN-OS 10.2 Nebula, our latest series of network security innovations. Nebula brings a fundamentally differentiated approach to network security. The industry’s first inline, deep learning protection helps stop sophisticated attacks as they happen – with 3x faster prevention and 48% more evasive threats detected, surpassing anything previously available.
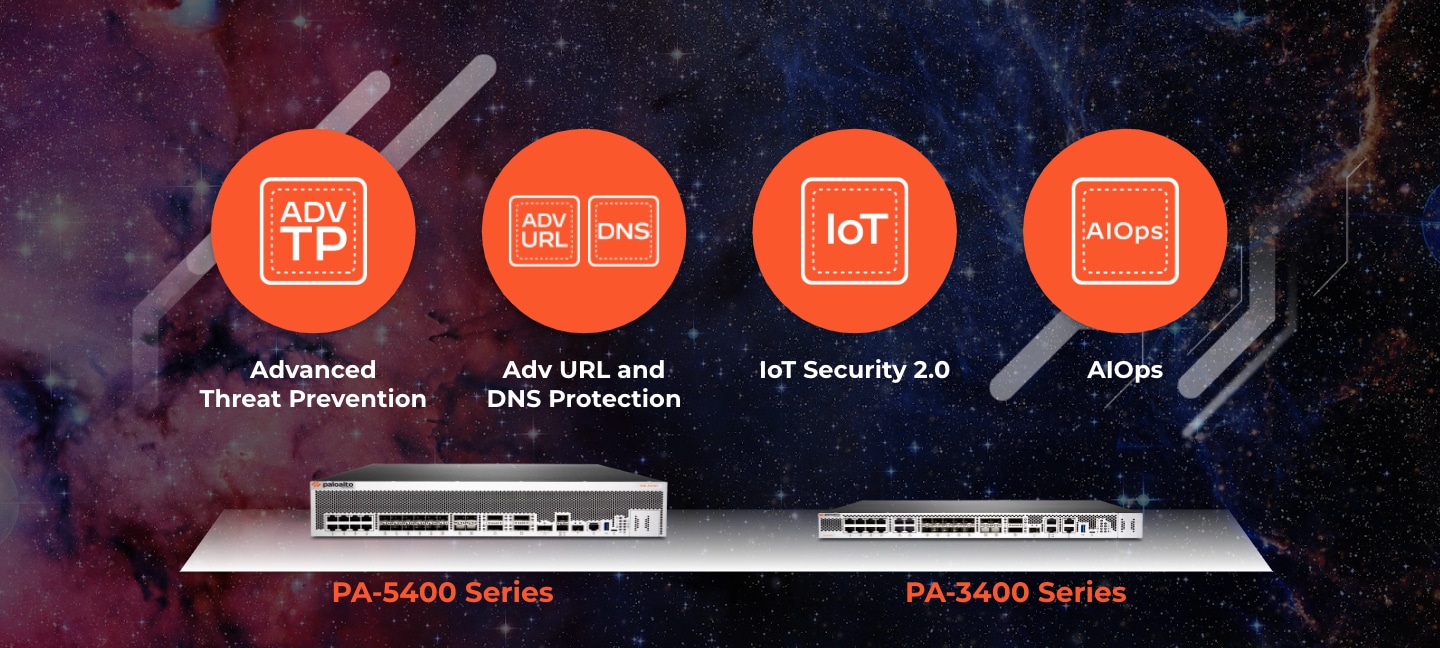
But, how? We introduced AIOps to optimize management and get ahead of configuration issues, released an industry-first update for Intrusion Prevention Systems (IPS/IDS) in Advanced Threat Prevention, and enhanced web security with innovations to Advanced URL Filtering and DNS Security. We also defined IoT Security 2.0, making device discovery and control a part of the standard process for network security.
A lot of the software advancements were made possible thanks to innovations in hardware for cloud and on-prem compute.
Our portfolio of 4th generation ML-Powered Next-Generation Firewalls launched seven new models across two new families – the PA-5400 Series and PA-3400 Series. Join our webinar to understand how we simplified the CPU architecture to drastically increase efficiency, performance, and connectivity to deliver 3x security performance in a smaller package. These new NGFW models secure three primary use-cases across the data center and campus.
Securing Your Internet Edge
As the threat landscape continues to evolve, the web gateway requires greater protection from more sophisticated, automated and highly evasive attacks. Many of these use multiple vectors at different stages, for example, phishing URLs for initial access, SaaS applications for account takeover, and later DNS for command and control or data exfiltration. When you look at the stats, you can see trends emerging, for example, 85% of malware now uses DNS to establish command and control communications, 40% of malware is unknown, and in 2021, organizations were using an average amount of 110 SaaS apps[1]. And the stats don't lie, these tactics were seen in Log4j, Colonial Pipeline, Solar Storm and many other less profiled attacks.
This introduces two key questions for network security architects and practitioners:
- What type of threats are the most harmful to my organization right now, and;
- What threat vectors require protecting to minimize my risk (versus spend)?
As more business is conducted online and data is stored virtually, protecting all traffic to and from the internet (north-south) becomes vital for the entire network. Securing your internet edge involves visibility into web and non-web traffic, stopping indirect attempts like phishing and credential misuse, preventing the delivery of known threats as they proliferate into new threat vectors, stopping unknown threats as they test traditional security, and ensuring connectivity remains constant to minimize business disruption. It’s also critical to ensure the same security protecting on-prem is used for branches, remote workers, your entire enterprise – otherwise you are just increasing the burden on security teams to identify and close gaps between technologies.
Our webinar will ensure you are one of the first to understand which threat vectors Palo Alto Networks believes are critical to securing your web gateway.
Securing Segmentation within Your Data Center and Campus
Many attackers today capitalize on weak implementations of Zero Trust and least privilege concepts. In fact, 70% of attacks rely on lateral movement to achieve their objectives. Without secure network segmentation that incorporates prevention, security teams are reliant on detecting an ongoing attack further down the chain, which is costly, time consuming and risky. Understanding the flow of east-west traffic and segmenting networks is a normal part of architectural design. Now more than ever, it’s critical to deploy the right segmentation technology that can bring extensive context around users, devices, applications, machines and dynamic workloads, while implementing policies of least privilege to control risk and preventing threats specific to the needs of that network location.
Secure Segmentation for Data Center
Least privilege access to resources allows an organization to establish a security posture to achieve Zero Trust. Threats such as exploits, malware and encrypted command-and-control can traverse freely. Prevention capabilities must aid segmentation strategies to stop lateral movement of threats from application to application, machine to machine, and workload to workload.
Secure Segmentation for Campus
One of the easier targets for entry and lateral movement are IoT devices. They make up a sizable portion of the devices on a campus network and are often unidentified and unprotected. However, segmentation between IT and IoT/OT is hard to set up, let alone maintain. Segmentation should incorporate both easy-to-implement policies, enforcement and management to separate devices, but also include the ability to find and stop known and unknown threats. This ensures an attack that goes undetected on entry can be stopped before it proliferates across your campus.
To learn more about Nebula’s innovations in campus and data center security, be sure to register for the first episode of our Nebula Tech Deep Dives: Industry Firsts in Campus and Data Center Security, 3x Faster with ML-Powered NGFW.
In addition, be sure to register for our next episodes, including the Evolution of IPS to Advanced Threat Prevention, Innovations in Web Security to Stop Evasive Threats, and others! See you there!
- https://www.statista.com/statistics/1233538/average-number-saas-apps-yearly/ ↑