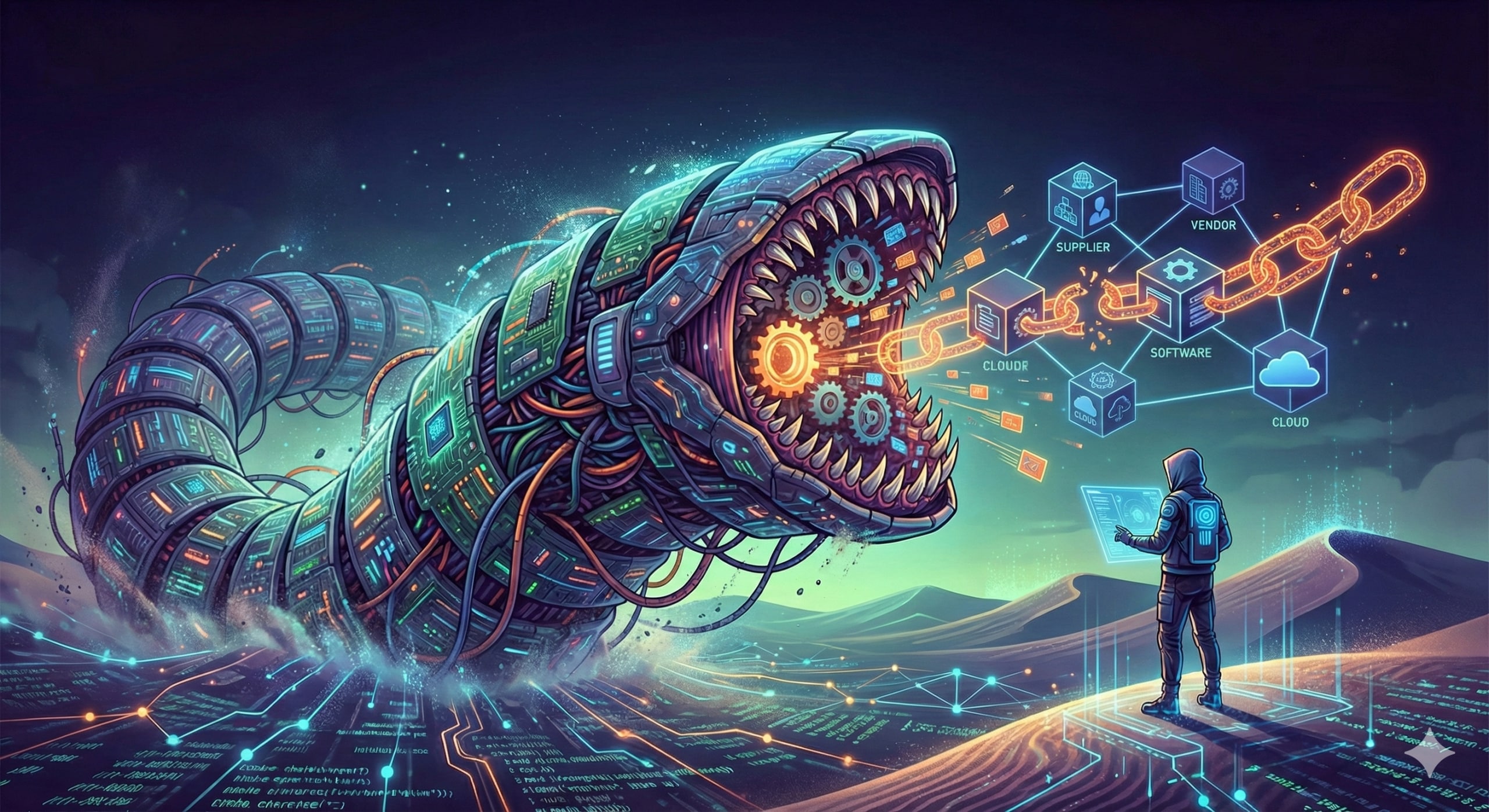
How the Latest Frontier AI Models Are Driving the Need for Real-Time Cloud Security
Frontier AI models are accelerating zero-day attacks at scale. Learn why real-time cloud runtime protection is essential to stop exploits the moment they execute.
Frontier AI models are accelerating zero-day attacks at scale. Learn why real-time cloud runtime protection is essential to stop exploits the moment they execute.
By submitting this form, you agree to our Terms of Use and acknowledge our Privacy Statement. Please look for a confirmation email from us. If you don't receive it in the next 10 minutes, please check your spam folder.