SD-WAN Controllers: High Value Targets for Attackers
The modern Wide Area Network (WAN) securely connects users, devices, and applications scattered across branches, data centers, and multiple clouds. To manage this complexity, Software-Defined WAN (SD-WAN) has become the industry standard to manage any enterprise network. However, as the orchestrator of the entire fabric, the SD-WAN controller has emerged as a critical infrastructure component—and the ultimate target for attackers.
SD-WAN controllers are an especially juicy target: SD-WAN controllers control your network infrastructure; those in control can change software levels, circumvent network security, and erase their footsteps. Additionally, SD-WAN controllers need to be exposed to the broader internet in order to function, so restricting them from broader internet access isn’t an option.
A recent high-profile exploit serves as a critical reminder of the vulnerabilities inherent in legacy controller architectures. By bypassing weak authentication on a privileged account, it was possible for unauthorized actors to downgrade system software to a compromised version and establish long-term persistence. In this scenario, the controller vulnerability grants full visibility and control of the WAN network. This event underscores a fundamental truth in modern networking: a controller isn’t just a management tool; it is the most sensitive part of the security perimeter and must be built on secure-by-design principles.
When evaluating SD-WAN and, more broadly, Secure Access Service Edge (SASE) solutions, the datapath security functions of your WAN are critical, but the security posture of your controller is even more so. CIOs, CTOs, and CISOs need to evaluate if their SD-WAN solution leverages a controller built using modern and cloud-influenced security principles vs an adoption of legacy software architectures. In other words, is your controller cloud-native, or is it merely cloud-adopted? Cloud-native vs cloud-adopted SD-WAN - this distinction is the difference between Prisma SD-WAN and legacy SD-WAN solutions, and it has massive implications for your organization's risk.
SD-WAN Controller Security: A Murky Past
In the past decade, solution providers rushed new products to market, quick to capitalize on the cost savings and operational efficiencies that SD-WAN brought. Along the way, mistakes were made, and organizations inadvertently opened themselves to cyberrisk. Vendors make an active choice in terms of their investments into security hardening of their products; not all solutions are the same. Below are some resources that we recommend decision makers review ahead of their next major solution selection:
- Common Vulnerabilities and Exposures: Known vulnerabilities are catalogued, and assessed based on severity at cve.org. Search for your solution of interest here and you'll uncover some compelling data.
- The SD-WAN New Hope Project broadly documented security deficiencies across five different SD-WAN solutions. The project created tools to harvest and infiltrate access to SD-WAN appliances and controllers alike. While this project has been dormant for 6 years, it is a reminder of the mistakes of the past.
While no software is entirely immune to risk, the disparity in vulnerability density across the industry is not accidental—it is a direct reflection of secure design principles. Solutions built on a cloud-native, microservices SD-WAN architecture have consistently demonstrated higher resilience against attacks. By eliminating implicit trust with strong authentication and segmenting controller components, these modern architectures reduce the blast radius of any single flaw.
Traditional SD-WAN Controllers: Cloud-Adopted, Monolithic, Fragile
The architecture of the traditional SD-WAN controllers have originated from on-premises software designed to run on specific hardware or virtual machines. When ported to the cloud, these designs retain their legacy monolithic structure.
- Single Point of Compromise: In a monolithic controller, the entire application runs as a single component or as a collection of virtual machines. A single vulnerability can compromise the entire platform, granting an attacker complete control over the networking fabric, configuration, and security policies. Cloud-adopted components use a DIY approach to securing the environment, requiring operators to implement 100s of pages from a hardening guide, only to minimize (but not eliminate) the attack surface of the controller.
- Static and Inflexible: Cloud-adopted controllers struggle with elasticity. They cannot dynamically decompose to defend themselves, and their complexity makes them far more difficult and time-consuming to patch—a critical weakness when a zero-day vulnerability is announced.
- The Persistence Problem: Because these are essentially long-running servers rather than dynamic microservices, attackers who gain access can establish long-term persistence, hidden within the complex state of the system for months or years.
When you choose a cloud-adopted controller, you are accepting the structural fragility of a legacy system disguised as modern cloud technology.
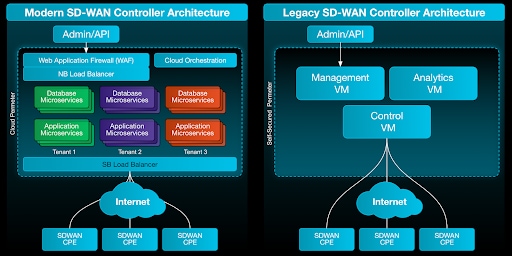
Diagram: Modern vs Legacy SD-WAN controller architectures
Prisma SD-WAN: Cloud-Native, Web-Scale, Resilient
Palo Alto Networks Prisma SD-WAN and Prisma SASE solutions are built on a foundational philosophy: security cannot be bolted on; it must be designed in from the beginning. This starts with the controller architecture using cloud-native secure and scalable building blocks.
Prisma SD-WAN utilizes a cloud-native controller built using secure design principles and constructs.
- Strong Isolation and Strict Access Control: Secure design principles of isolated management, continuous certificate based MFA, and ephemeral tokens are implemented and continuously monitored to ensure integrity of the system. To prevent infiltration, there is no concept of a high privilege system account in the architecture. Tightly restricted administrative access, used sparingly, leverages strongly authenticated short lived OIDC tokens.
- Microservices Security: A cloud-native controller breaks down its functions into small, independent, and isolated microservices (e.g., authentication, policy engine, analytics). If a vulnerability is discovered in one microservice, the blast radius is limited. The rest of the controller remains secure, and the single compromised component can be automatically isolated and restarted.
- Immutable Infrastructure: Components are designed to be immutable. Rather than patching a running system, a cloud-native architecture replaces it with a new, patched version instantly, to stop persistence exploits and maintain configuration conformity.
- Elastic Web-Scale Defense: Built on the same principles as giants like Google or Amazon, the controller automatically scales its security resources to meet demand, providing inherent resilience against Distributed Denial of Service (DDoS) attacks that would cripple a traditional, single-instance controller.
Prisma SD-WAN: G-SIB Proven Security by Design
Because of its secure by design architecture, Prisma SD-WAN stands apart from SD-WAN’s chaotic history of severe and exploited vulnerabilities.
Prisma SD-WAN was built with the explicit intent of securing the most critical networks in the world. Mutually authenticated TLS is leveraged to stop unauthenticated attackers before any communications can take place. Unique per-device manufacturing and customer certificates are generated for all devices within a tenant. Asymmetric encryption keys are rotated hourly by default. As a result, Prisma SD-WAN is deployed at Global Systemically Important Banks (G-SIBs). For a G-SIB, a network compromise is not just an IT issue; it is a threat to the global financial system. The presence of Prisma SD-WAN in these institutions is the ultimate validation of our security-first, web-scale philosophy.
Demand More from Your SD-WAN Solution
Your SD-WAN controller has the keys to your kingdom. If it is compromised, your entire network is lost, and your business operations can cease in an instant. Before you sign your next contract, demand that your SD-WAN solution provider answers the hard questions about their architectural foundations to ensure that it is secure.
Three Questions Every Potential SD-WAN Buyer Must Ask:
- Is your SD-WAN controller a monolithic application that was ported to the cloud (cloud-adopted), or is it a true microservices-based, secure, web-scale architecture built specifically for the cloud?
- Does your controller maintain a static, persistent state that must be manually patched, or is it an immutable infrastructure where vulnerable components are destroyed and replaced automatically to enforce patching?
- In the event of a successful zero-day exploit against your controller, can you guarantee that the entire management and control plane will not be compromised, or does a single exploit grant root access to everything?
In an ever increasing AI-powered threat landscape, the security of your network, and its crown jewels, the SD-WAN controller, is paramount. Demand a cloud-native, security-by-design architecture. See how Prisma SD-WAN delivers the industry’s most secure controller architecture. Request a demo on how Prisma SD-WAN can accelerate your secure WAN transformation.