Govern every identity
Idira® delivers a single system of record for all entitlements, including full change history, so teams always know who has access, if it changed and why.
Idira® delivers a single system of record for all entitlements, including full change history, so teams always know who has access, if it changed and why.
AI identifies the right, least-privileged access by analyzing your environment and routing access requests via native ITSM or ticketing workflows. Continuously validate access accuracy and maintain visibility into the access estate from Idira.
Continuously uncover identity risks and stay compliant by monitoring entitlements across all applications. Receive real-time alerts for high-risk access and misaligned permissions to quickly flag Segregation of Duties (SoD) violations and orphan accounts that often go unnoticed.
Ensure connectivity, visibility and rapid time to value with comprehensive coverage for SaaS, on-prem and custom applications. Connect via API catalogs and use robotic process automation that can continuously sync with apps without publicly available APIs, including on-prem applications.
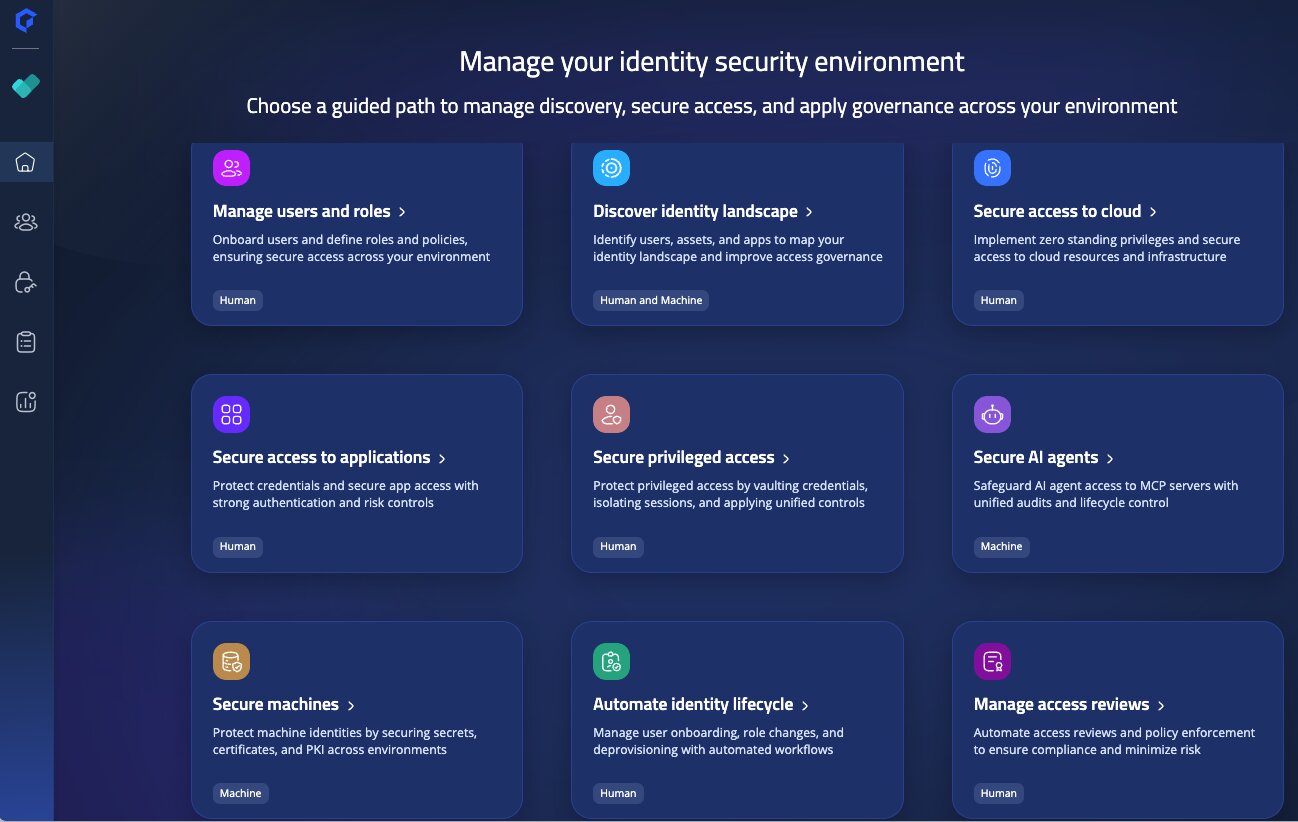
Eliminate siloed tools. Use a modern identity security platform that delivers continuous visibility, intelligent access decisions and automated lifecycle controls across all identities and environments.
Automation onboards applications, uses built-in workflows to populate missing data, generates the campaign, invites reviewers to complete their work, enables administrators to track reviewer progress and generates an audit-ready evidence package at the end of each campaign.
Automate joiner, mover and leaver events with AI-driven access recommendations and efficient provisioning workflows that reduce tickets, prevent access drift and improve productivity. Identities are secure at birth with the right access.
Get a unified view of human and machine identities to discover gaps before they become a breach. Create policies to detect SoD conflicts and orphan accounts, with real-time alerts to monitor and remediate risks in real time.
Governance is the backbone of strong identity security, and identity security must include robust governance processes. But this is hard to achieve across fragmented tools. Idira Human Identity Security treats authentication, privilege and governance as a single continuous motion.