Introduction
Identity analytics is a critical cybersecurity tool in combating the challenges posed by compromised user accounts and malicious insiders. Identity threats are pervasive across organizations of all sizes and industries, potentially exposing sensitive information to security breaches. Compromised credentials, especially on privileged accounts, pose significant risks, particularly in environments where the principles of least privilege are not strictly enforced.
Identity analytics leverages an analytics engine to analyze logs and data from various sensors, to establish what is considered normal behavior across an organization. By establishing a baseline, abnormal activities such as stolen or misused credentials, lateral movement, credential harvesting, or exfiltration can be detected. Cortex XDR utilizes identity analytics to investigate suspicious user activity - aggregating and displaying user profile information, activity, and incidents associated with user-based analytics alerts and BIOC rules. This approach enhances threat detection capabilities, providing organizations with the necessary insights to mitigate risks effectively.
To handle the Cortex XDR Identity Analytics alerts, we created the 'Cortex XDR Identity Analytics' playbook. This playbook enables complete automation of enrichment, investigation, and response processes for handling Cortex XDR Identity Analytics alerts.
In addition to the playbook, we created a layout that presents all the alert details and necessary data to the analysts.
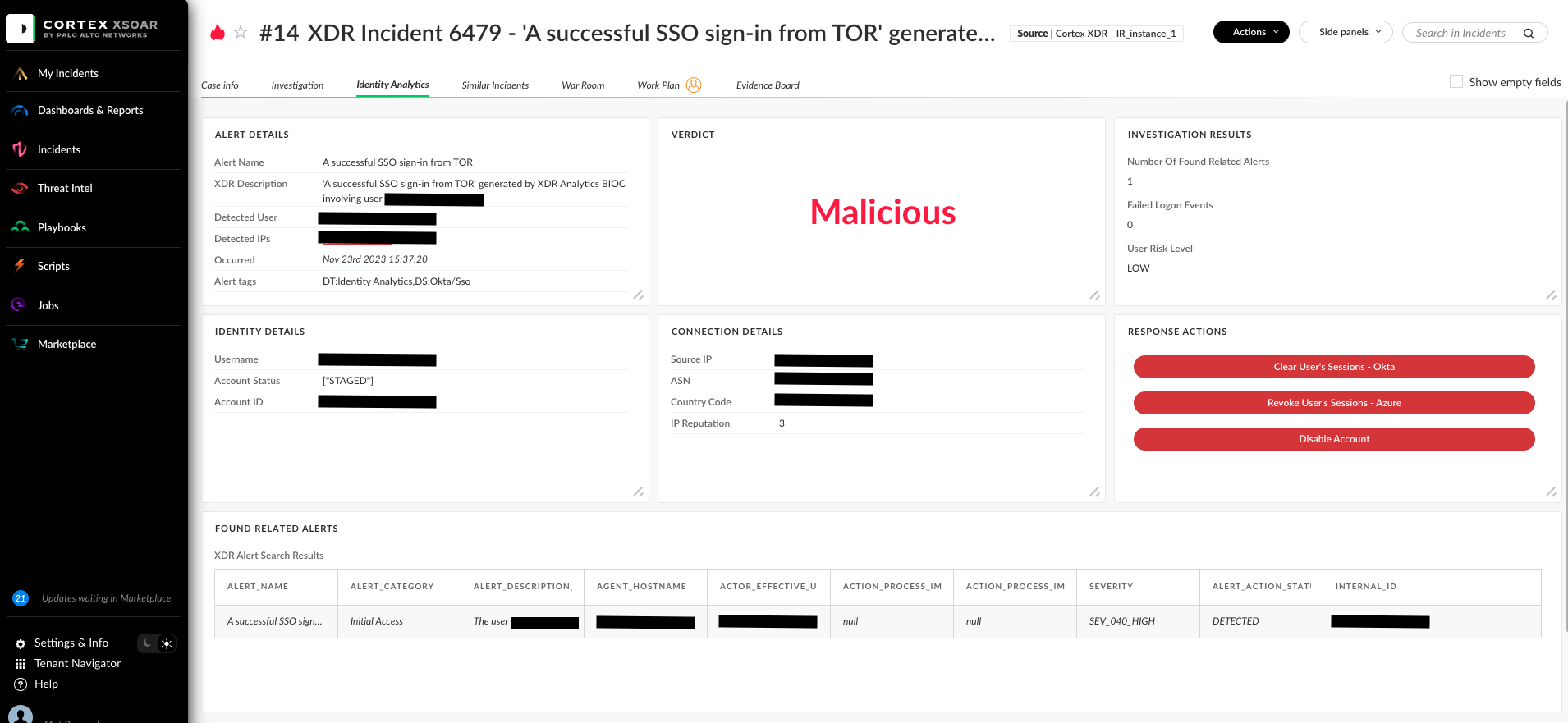
The Layout
Within this playbook, a comprehensive layout presents the analyst with all the relevant details required for investigating and resolving the incident.
Under the 'Identity Analytics' tab, there’s vital information about the alert, including alert specifics, user data, IP address details, and thorough investigation insights. This encompasses the investigation verdict, a concise summary of the findings leading to the severity determination, and any Cortex XDR-related alerts tied to MITRE tactics executed by the user. Furthermore, the layout incorporates buttons to facilitate quick response actions related to the alert, such as user disabling or clearing/revoking the user’s sessions.
What Does the Playbook Do?
Enrichment
The initial phase of the playbook encompasses essential tasks aimed at identifying and mitigating potential threats. To accomplish this, the playbook initiates indicator enrichment to gather pertinent details on the IP address associated with the potential threat. It consolidates data and reputation insights from all accessible and configured IP enrichment sources. Furthermore, the playbook enhances user information by aggregating data from all accessible and configured internal user management systems using the ’Account Enrichment - Generic v2.1’ sub-playbook and ‘Cloud IAM Enrichment - Generic’ sub-playbook.
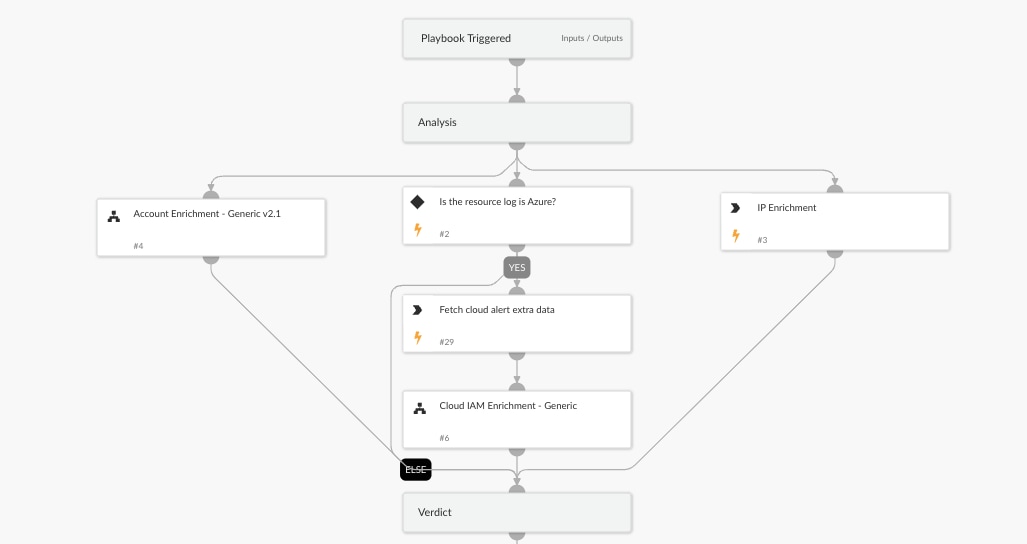
Verdict
The playbook establishes a severity verdict by evaluating indicator enrichment data and user risk level data from the Cortex XDR ITDR module. If the IP reputation is poor or the user risk level is high, the verdict is classified as malicious, and the playbook will perform remediation action to block the attack. Otherwise, the playbook will proceed to the investigation phase to gather additional findings regarding the user activity.
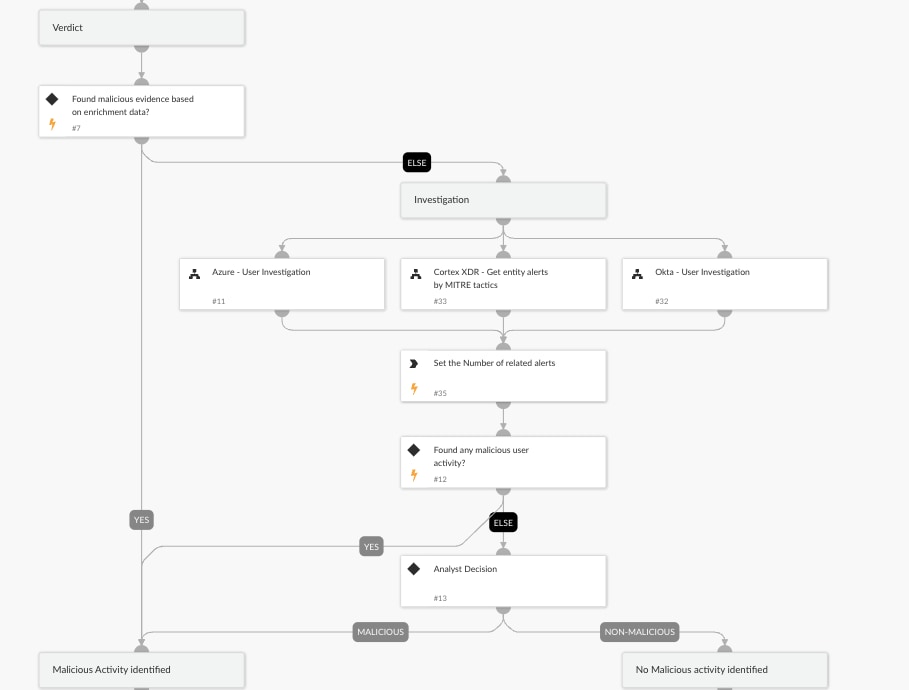
Investigation
The investigation workflow focuses on user activity, to uncover any suspicious behavior that could indicate malicious activity. To achieve this, the playbook utilizes the following sub-playbooks to pull user activity data from various sources:
- Okta - User Investigation: Okta serves as one of the log sources for identity analytics alerts. This sub-playbook extracts additional information about the user from Okta, enabling the identification of malicious user activities such as script-based user agents, the frequency of failed logins, and other suspicious behaviors.
- Azure - User Investigation: Similar to Okta, the Azure Event Hub is a crucial log source for identity analytics alerts. This sub-playbook utilizes Azure data to uncover malicious user activities, including script-based user agents, failed login attempts, and other suspicious patterns.
- Cortex XDR - Get entity alerts by MITRE tactics: The playbook also uses this sub-playbook to search for XDR-related alerts. This sub-playbook focuses on MITRE ATT&CK tactics to identify any malicious activities performed by the user.
Following the investigation, the playbook determines the verdict. If the verdict indicates malicious activity, the playbook initiates remediation actions to block the attack. However, if the verdict is inconclusive based on the enrichment and investigation tasks, further analysis by an analyst is required to determine the incident's malicious nature. This analysis involves reviewing all the details collected by the playbook and presented in the layout.
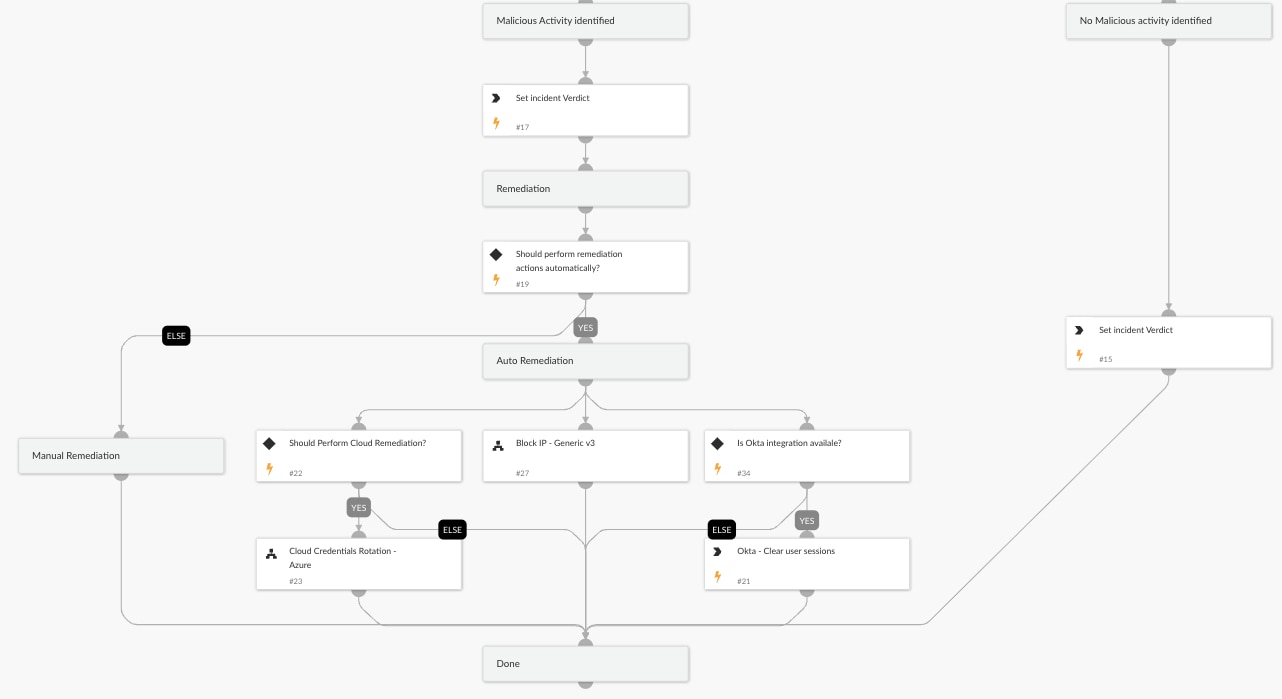
Response Actions
The response actions are initiated only when the verdict is determined to be malicious. The playbook executes remediation steps, including blocking the identified malicious IP address using the sub-playbook 'Block IP - Generic v3'. It also clears the user session in Okta, revokes the user session in Azure, and enforces re-authentication via MFA. By default, the playbook revokes sessions in Azure. However, by adjusting a specific playbook input, it can also reset the user's password on Azure using the sub-playbook 'Cloud Credentials Rotation - Azure'.
Conclusion
Analysts can be more effective in handling identity threats with the help of the Cortex XDR Identity Analytics playbook, which streamlines the response to attacks caused by compromised user accounts and malicious insiders. With identity analytics, analysts gain clarity on security alerts, and this new playbook simplifies the response process with a user-friendly layout and action buttons.
Curious about what our users automate most often and not sure where to start? Listen to our on-demand webinar where XSOAR deployment experts walk you through the process we share with our own customers.