A Sea of IOCs
Enrichment of indicators is one of the first tasks security teams perform during incident response. The challenges here are twofold. Firstly, the process of indicator enrichment is as repetitive as it is important. Analysts risk getting mired in this grunt-work while the attack continues to manifest. Secondly, isolated security tools result in a struggle to reconcile threat intelligence data across platforms to get an overall understanding of indicator malice.
How Orchestration Helps
Security orchestration playbooks can automate enrichment of indicators by querying different threat intelligence tools for context. By running this playbook at the outset of incident response, security teams have the enrichment data available for study within seconds, shaving off wasted time that can be used towards proactive investigation.
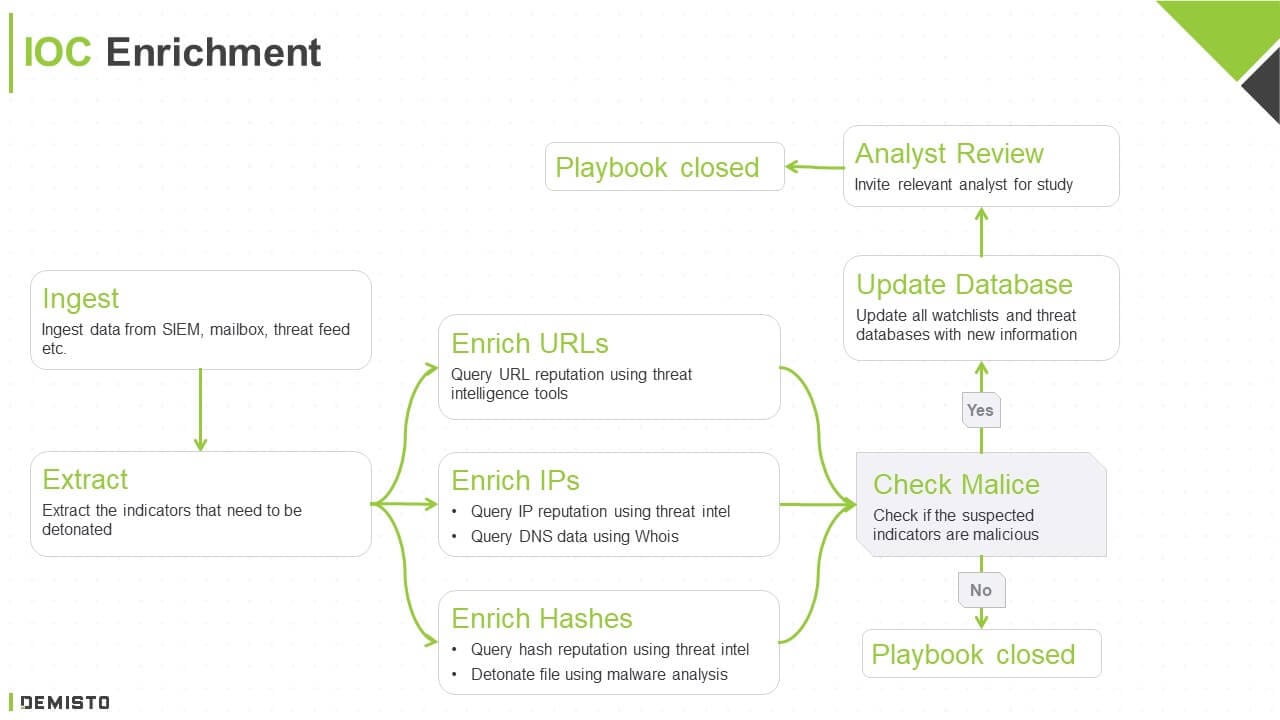
1. Ingestion
The playbook can ingest data from a variety of sources such as SIEMs, mailboxes, and threat intelligence feeds.
2. Extraction
The playbook extracts the IOCs (IPs, URLs, hashes, etc.) that need to be enriched.
3. Enrichment
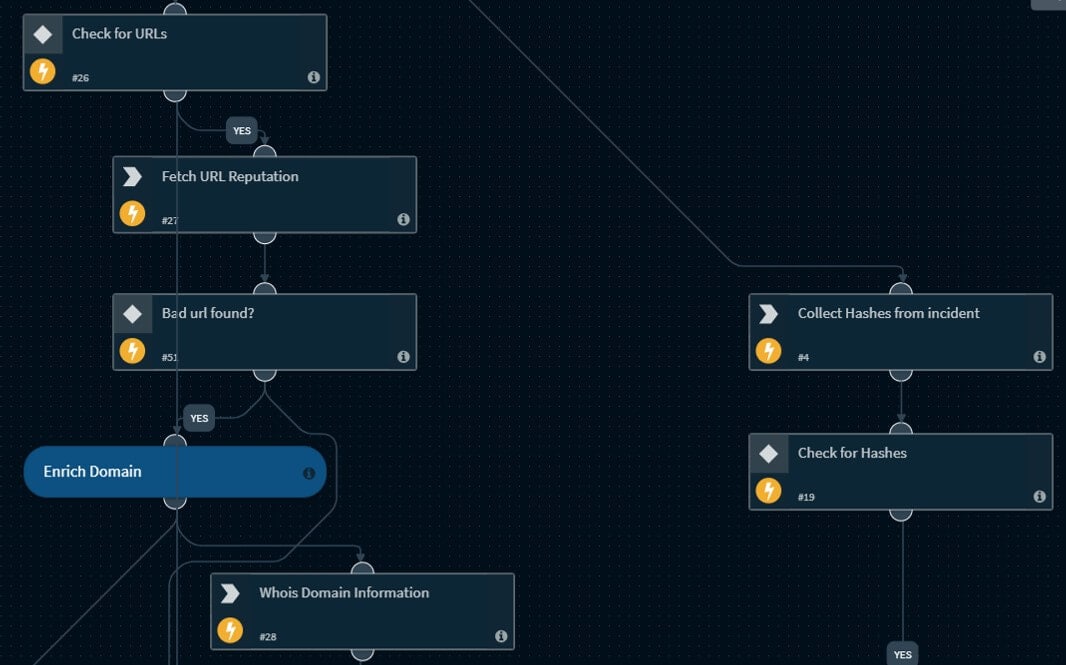
The playbook enriches the IOCs across however many threat intelligence tools the SOC uses -- weaving in threat intelligence tools, DNS services, and malware analysis tools that may enrich URLs, IPs, and hashes, for example.
4. Update Databases
The playbook executes initial response actions based on indicator malice. For instance, malicious indicators are fed back into threat intelligence databases and tool watchlists to avoid future attacks using the same indicators.
5. Analyst Review
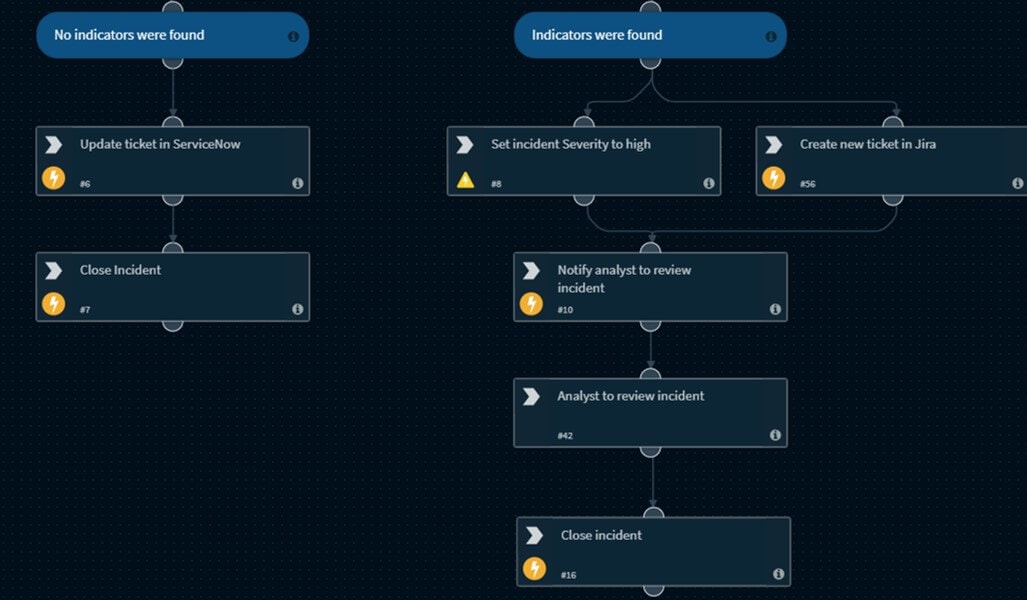
The playbook checks if the indicators are identified as malicious. If they are, the playbook raises the incident severity, opens a ticket, and brings in the relevant analyst for further review and investigation. If the indicators are not identified as malicious, the playbook records the context for future reference and closes the incident, preventing analysts from being bogged down by false positives.
To access Cortex XSOAR's IOC enrichment playbook and other orchestration use cases, visit our GitHub playbook repository and see what's possible
Benefits
Unify security functions: By coordinating among multiple tools, an IOC enrichment playbook can enable security teams to have improved, centralized visibility over security data. In this example, the playbook collects intelligence from multiple threat intelligence tools, DNS tools, and malware analysis products.
Automate repeatable steps: There are multiple security actions that, while important, are time-consuming to execute every time indicators need to be enriched. Automating these steps shave off large chunks of response time while still providing overall control and decision-making power to the security team.
Improve investigation quality: Security orchestration platforms usually correlate intelligence from multiple tools so that security teams can quickly identify whether any IOCs are isolated or persistent within their environments. In this example, security teams can study IOC reputation, see how many other incidents these IOCs have been found in, and identify larger attack campaigns at play.
A Good Playbook Should Be...
Simple and intuitive: The playbook should ideally be represented as a task/process flow through a simple drag-and-drop graphical interface. Coding expertise shouldn't be a 'must-have' to make even the most complex playbooks, although each playbook’s code should also be available for analysts to tweak if required.
Primed for automation: Analysts should be able to automate the entire playbook in response to a phishing attack, greatly reducing response time, effort, and the possibility of human error for large-volume attacks. However, analysts should also be able to include manual steps in playbooks and require human intervention for sophisticated attacks.
Customizable: Analysts should be able to make copies of the standard playbook, modify it, or embed it in other playbooks as needed.
We hope you found this use case walk-through helpful. This is only a skeletal workflow - your own 'playbook' can be as simple or complex as your needs merit.
To learn about more security orchestration use cases, download our free Community Edition.