There have been over 1.5 billion U.S. dollars spent on acquisitions of external attack surface management (EASM) startups over the past few years. What’s more interesting is the breadth of companies moving into this space, ranging from security consultancies, vulnerability management, threat intelligence, and cybersecurity solutions companies. Given the heavy spending across multiple segments there’s clearly a shared vision or understanding of the direction security operations needs to go, but why is this important now?
Your infrastructure is a living, breathing organism
Ok, well maybe not living, but take a moment to take a long, slow deep breath… hold it… now exhale completely. Do this again and pay attention to your body, in particular, how you are expanding and contracting your chest cavity while doing this. When people talk about the ephemerality of cloud assets, it’s this expansion and contraction of your infrastructure that they are talking about. It breathes.
Using Cortex Xpanse customer data observed over the past couple months to demonstrate: On any given day our median customer has about 4560 active services exposed to the public internet. Of these services, on a monthly basis the median expansion of new services is 20%, and the contraction is about 22%. Your infrastructure breathes.
A mandate for continuous management
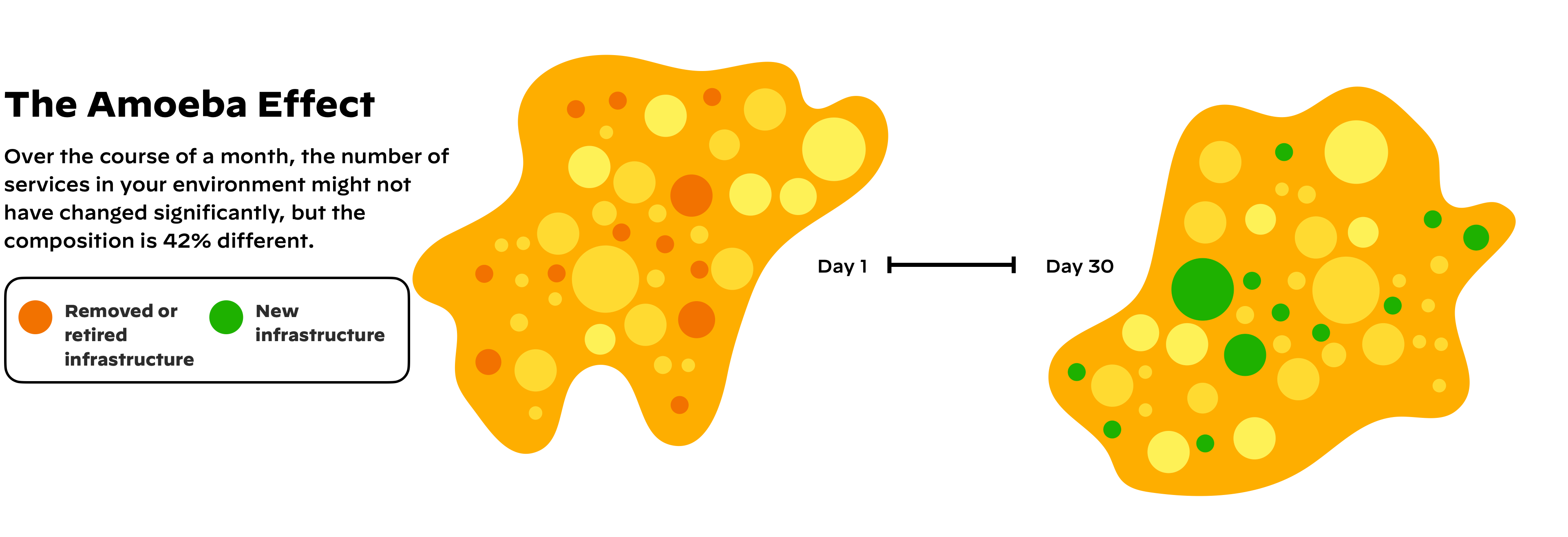
Looking at this data, you may see a net change in your infrastructure of -2%. What’s important is that there’s a gross change of 42% or nearly half your infrastructure is different from what it looked like last month. There are two critical consequences of this information that has lead to well over 1.5 billion dollars of investment into this emerging EASM space:
- Security teams have to shift their paradigm from scanning known infrastructure on a weekly basis to performing EASM as a continuous monitoring capability. Your infrastructure is changing faster than it ever has, and even if you tried using your vulnerability management product to scan more frequently, cloud adoption means you don’t know all the places you need to be scanning.
- Most change control processes assume expansion but never compensate for contraction or taking services offline. Over time, your change control processes may leave your firewalls looking like Swiss cheese as services are stood up, taken down, and others requiring their own exceptions find their way into the same place.
EASM provides operational assurance through awareness and automation
With new clients, we commonly see up to 60% of their cloud infrastructure doesn’t have their cloud security software deployed – and this is essentially a second-tier problem compared to not knowing the asset exists to begin with. Whether dealing with issues of newly identified assets or exposures in known assets, the ability to automate and respond is critical. This is also a major shortcoming of homegrown EASM solutions as we’ll explore with Matt Kraning, Marshall Kuypers, and myself in our upcoming LinkedIn Live event on May 10, “Why You Don’t Want to Go With Homegrown Attack Surface Management.”
Sleep better knowing the infrastructure you’re protecting and that the security investments you’ve made are in place. You know how to secure your environment, it’s time to make sure that knowledge is operationalized across your infrastructure.