- What Is Exposure Management?
- ASM Tools: Top 8 Solutions for 2026 (Compared)
- Best Tenable Competitors & Alternatives for 2026
- ASM Tools: How to Evaluate and Select the Best Option
- Best Exposure Management Platforms (2026): Top 8 Tools + Evaluation Checklist
- What Is Continuous Threat Exposure Management (CTEM)?
-
What Is External Attack Surface Management (EASM)?
- External Attack Surface Management Explained
- Internal vs. External Attack Surface Management
- How External Attack Surface Management Works
- Why EASM Is Important
- Use Cases for External Attack Surface Management
- Benefits of EASM
- Approaches to Attack Surface Management
- EASM Challenges
- How to Choose an Attack Surface Management Platform
- External Attack Surface Management FAQs
- What Are the Types and Roles of Attack Surface Management (ASM)?
-
What Are Common Use Cases for Attack Surface Management?
- What Is the Purpose of Attack Surface Management?
- Decoding the Attack Surface: Ten Examples
- Understanding ASM from the Threat Actor’s Perspective
- Ethical Hackers and Attack Surface Management: A Unique Use Case
- Examples of Attack Surface Management Use Cases
- Common Use Cases for Attack Surface Management FAQ
- How Does a CISO Effectively Manage the Attack Surface?
- What Is the Attack Surface Management (ASM) Lifecycle?
- What is Attack Surface Assessment?
- What is the Difference Between Attack Surface and Threat Surface?
What Is Attack Surface and Attack Surface Management?
Attack Surface refers to the sum of all potential entry points that an attacker can exploit to gain unauthorized access to an organization's systems, data, and infrastructure. As organizations adopt cloud technologies, remote work, and Internet of Things (IoT) devices, their attack surface expands, making monitoring and securing all vulnerabilities increasingly challenging.
The potential entry points that an attack surface comprises include:
- Applications: Software accessible externally
- Websites: All company-hosted websites
- Networks: Any network used to connect devices
- Devices: Any connected device
- Cloud infrastructure: Any cloud services used
Attack Surface Management (ASM) performs several critical functions to give a security operations center (SOC) the visibility needed to ensure security across an organization:
- Provides a complete, up-to-date inventory of all assets (both known and unknown).
- Continuously finds potential vulnerabilities
- Offers risk prioritization.
What is Attack Surface Management?
Learn how Cortex Xpanse, an attack surface management platform, provides protection for all public-facing assets and synchronizes that data across other existing tools, ensuring complete network coverage.
Importance of Knowing Your Attack Surface
In cybersecurity, the principle "you can’t secure what you don’t know exists" is a fundamental truth. If an organization lacks visibility into its internal and external assets, it cannot effectively protect them from cyber threats.
Every unmonitored device, misconfigured cloud instance, or forgotten web application represents a potential entry point for attackers. Without a clear understanding of its attack surface, an organization risks data breaches, operational disruptions, and regulatory non-compliance.
The evolving IT landscape, influenced by cloud adoption, remote work, and third-party integrations, complicates maintaining visibility. Shadow IT, where employees use unauthorized software or cloud services, worsens the problem. These unmanaged assets typically evade traditional security monitoring, leaving security teams unaware of potential threats.
Organizations that actively monitor and manage their attack surface can:
- Identify and mitigate vulnerabilities before they are exploited.
- Reduce the risk of cyberattacks by limiting exposure to attackers.
- Improve compliance with security regulations by securing all assets.
Attack Surface vs. Threat Surface
While the terms attack surface and threat surface are often used interchangeably, they represent different aspects of cybersecurity. The attack surface includes all possible vulnerabilities within an organization, whether actively exploited or not.
In contrast, the threat surface focuses specifically on the vulnerabilities currently targeted by cybercriminals. The attack surface is broad and relatively static, while the threat surface is dynamic, shifting based on emerging cyber threats and new attack techniques.
Learn how to identify the differences in your attack and threat surfaces to strengthen your security strategies: What is the Difference Between Attack Surface and Threat Surface?

Types of Attack Surfaces
Attack surfaces can be categorized into three main types: Digital Attack Surface, Physical Attack Surface, and Social Engineering Attack Surface. Each type presents unique risks and requires specific security measures to mitigate vulnerabilities.
Digital Attack Surface
The digital attack surface includes all internet-connected assets vulnerable to attackers, such as web applications, APIs, cloud environments, and digital credentials. Risks often arise from misconfigurations, outdated software, or unauthorized third-party integrations. As organizations move to the cloud, their digital footprint grows, increasing potential entry points.
Physical Attack Surface
The physical attack surface includes hardware and components that can be compromised to access sensitive data, such as laptops, servers, USB drives, mobile devices, and network connections. Attackers exploit physical security weaknesses, like stolen devices or unauthorized area access, to breach an organization’s systems.
Social Engineering Attack Surface
Unlike digital and physical attack surfaces, the social engineering attack surface involves the human element of cybersecurity. Attackers exploit psychological manipulation techniques to deceive employees into revealing confidential information, clicking on malicious links, or bypassing security protocols.
Common social engineering methods include phishing, pretexting, baiting, and impersonation attacks. Since human error is often the weakest link in security, organizations must invest in employee awareness training to mitigate these risks.
Deep dive into the types, categories and roles of attack surface management: What Are the Types and Roles of Attack Surface Management?
Examples of Human Attack Surfaces
The human attack surface refers to vulnerabilities due to human behavior, errors, and social engineering tactics. Cybercriminals exploit trust, manipulation, and deception to gain unauthorized access to systems, steal data, or execute attacks.
Phishing Attacks
Phishing remains one of the most effective cyberattack methods because it targets human psychology rather than technical vulnerabilities. Attackers use fraudulent emails, messages, or websites to trick users into providing sensitive information like usernames, passwords, financial details, or personal data.
Insider Threats
Insider threats occur when employees, contractors, or partners misuse their access to an organization’s systems intentionally or unintentionally. Unlike external threats, insider threats bypass traditional security defenses because the attacker has legitimate access to critical resources.
Social Media Exploits
Social media platforms serve as goldmines for attackers seeking intelligence on individuals and organizations. Cybercriminals, hacktivists, and nation-state actors can leverage personal and professional details shared on social media to craft targeted attacks.
Explore various ASM use cases and how they apply across industries: What are Common Use Cases for Attack Surface Management?
Attack Vectors Commonly Exploited
Attack vectors are the paths or methods attackers use to exploit vulnerabilities and gain access to an organization's systems and data. It is a way for an attacker to exploit a vulnerability and reach its target. Examples of attack vectors include:
- Phishing
- Malware
- Social Engineering
- Web Application Vulnerabilities
- Network Attacks
- Zero-Day Exploits
- Cloud Misconfigurations
- Supply Chain Attacks
- Insider Threats
- Physical Attacks
Measuring and Assessing Attack Surface
Security teams may overlook vulnerabilities without proper measurement and assessment of the attack surface, increasing the risk of cyberattacks. By accurately measuring and assessing, organizations can:
- Identify security gaps before they are exploited.
- Prioritize risks based on severity and impact.
- Enhance incident response by understanding potential entry points.
- Ensure compliance with regulatory frameworks like NIST, GDPR, and ISO 27001.
Methods to Determine the Attack Surface
- Asset Inventory & Discovery
- Organizations must first identify all digital, physical, and human-related assets that contribute to their attack surface.
- This includes cloud environments, on-premises infrastructure, mobile devices, APIs, and third-party systems.
- Regular asset discovery scans ensure that new, unknown, or unmanaged assets are identified and included in security protocols.
- Network and System Scanning
- Network Scanners: Identify open ports, misconfigured firewalls, and exposed services.
- Vulnerability Scanners: Detect unpatched software, outdated systems, and exploitable security flaws.
- Penetration Testing (Pen Testing): Simulates real-world cyberattacks to uncover weaknesses before malicious actors do.
- Risk-Based Prioritization
- Not all vulnerabilities pose the same level of risk. Organizations must prioritize attack vectors based on:
- Likelihood of exploitation (e.g., unpatched critical vulnerabilities).
- Potential impact (e.g., exposure of customer data).
- Ease of remediation (e.g., quick patching vs. long-term fixes).
- Threat intelligence feeds help security teams track active exploits and emerging threats, ensuring resources focus on the most critical risks.
- Not all vulnerabilities pose the same level of risk. Organizations must prioritize attack vectors based on:
- Human Attack Surface Analysis
- Security assessments must include an evaluation of human vulnerabilities, such as:
- Social engineering susceptibility (e.g., phishing simulations).
- Insider threats (e.g., monitoring user access and behavior).
- Credential hygiene (e.g., enforcing strong passwords and multi-factor authentication).
- Security assessments must include an evaluation of human vulnerabilities, such as:
Explore the dynamic framework of the ASM lifecycle and how it helps security teams proactively detect and mitigate cyber risks: What is the ASM Lifecycle?
Tools and Techniques for Attack Surface Analysis
Attack surface analysis involves identifying, assessing, and reducing the points of entry attackers can exploit in an organization’s digital, physical, and human attack surfaces. Security teams use a combination of automated tools, manual assessments, and proactive security frameworks to monitor and mitigate risks continuously:
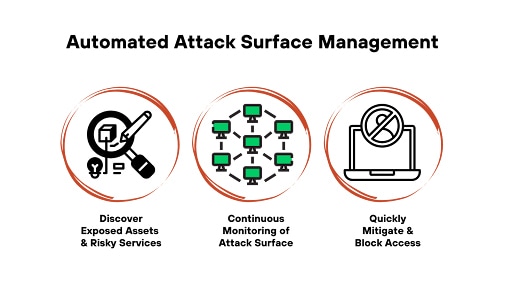
Automated Attack Surface Discovery tools continuously scan and inventory an organization's infrastructure, identifying external-facing assets, shadow IT, vulnerabilities, and misconfigurations.
Vulnerability Scanners assess known software, network, and application weaknesses, providing detailed risk reports for remediation.
Network Scanning & Security Testing helps organizations identify open ports, weak firewall rules, and exposed services that could be exploited.
Penetration Testing (pen testing) & Red Team Exercises involve simulating real-world cyberattacks to uncover security weaknesses that automated tools may miss.
Cloud Security & Configuration Management tools assess misconfigurations, access controls, and compliance risks in cloud environments.
Endpoint Detection & Response (EDR) & Behavioral Analytics tools monitor endpoint activity, detect anomalies, and prevent malware attacks.
Identity & Access Management (IAM) Auditing tools assess user access, enforce least privilege policies, and detect unauthorized login attempts.
Threat Intelligence & Dark Web Monitoring platforms help security teams identify active attack campaigns, leaked credentials, and zero-day vulnerabilities before they are exploited.
Security Orchestration, Automation, and Response (SOAR) platforms automate security workflows, incident response, and attack surface remediation.
Explore how to assess the three types of attack surfaces and gain expert tips on reducing attack surface risks: What is Attack Surface Assessment?
Attack Surface Management (ASM)
Attack Surface Management (ASM) is the process of continuously identifying, monitoring, and mitigating risks across an organization’s digital and physical assets.
Importance of Managing Attack Surfaces
Organizations that lack attack surface management are more susceptible to cyber threats because they may not be aware of all their exposed assets.
Effective ASM ensures:
- Greater visibility across all internet-facing and internal systems.
- Proactive risk mitigation through automated detection and patching.
- Regulatory compliance with security standards such as NIST, GDPR, and ISO 27001.
Attack Surface Management Strategies
- Continuous Asset Discovery – Automatically detect new, unknown, or unmanaged assets.
- Risk-Based Prioritization – Focus security efforts on high-risk vulnerabilities.
- Automated Response – Implement security workflows to mitigate threats efficiently.
Explore the definitive CISO’s guide to ASM, with expert strategies for risk assessment, asset control, and cybersecurity: How Does a CISO Effectively Manage the Attack Surface?
Reducing the Attack Surface
Reducing an organization's attack surface is a proactive approach to cybersecurity that involves minimizing potential entry points, hardening security controls, and continuously monitoring for vulnerabilities. By adopting a security-first approach and leveraging proactive attack surface reduction techniques, organizations can limit exposure, improve cyber resilience, and significantly reduce the likelihood of successful cyberattacks.
Attack Surface Reduction Strategies
To effectively reduce security risks, organizations must actively minimize exposure by implementing security best practices and eliminating unnecessary attack vectors. Key strategies include:
- Eliminating unnecessary software and services that create additional entry points.
- Implementing least privilege access controls to restrict user permissions.
- Using strong authentication measures such as Multi-Factor Authentication (MFA).
- Segmenting networks into isolated zones to restrict lateral movement.
- Disabling default credentials and hardening configurations.
Steps to Reduce Potential Vulnerabilities
- Conduct Regular Security Assessments – Perform penetration testing and vulnerability scans.
- Patch and Update Systems – Apply security updates and software patches immediately.
- Encrypt Sensitive Data – Protect information at rest and in transit.
- Monitor Third-Party Access – Restrict vendor and contractor permissions.
- Control Shadow IT – Identify and manage unauthorized cloud applications.
Limiting Attack Surface Expansion
As organizations adopt cloud computing, remote work, IoT, and edge computing, their attack surface grows. Security teams must enforce strict security policies and leverage automation to prevent expansion from leading to unmanageable risks:
Cloud Security & Access Controls
Secure cloud environments with least privilege IAM policies, continuous cloud security posture monitoring (CSPM), and real-time misconfiguration detection.
Endpoint Protection & Zero Trust Security
With remote work and BYOD (Bring Your Own Device) policies increasing risk, enforcing endpoint detection and response (EDR), managed device security, and Zero Trust Network Access (ZTNA) reduces exposure.
Continuous Security Monitoring & Automated Threat Detection
Deploying SIEM (Security Information and Event Management), threat intelligence feeds, and automated attack surface monitoring helps detect threats before they become breaches.
Real-World Examples of ASM
Preventing a Cloud Misconfiguration Data Breach
Scenario: A multinational retailer had thousands of cloud storage buckets across different regions, many managed by different teams. Without continuous attack surface assessment, security teams overlooked a misconfigured cloud storage bucket that was left publicly accessible.
- Risk: The bucket contained sensitive customer payment information, leaving it exposed to cybercriminals scanning for misconfigured assets.
- Solution: The company implemented an External Attack Surface Management (EASM) tool that continuously scanned cloud assets for misconfigurations. Within hours of detection, the misconfigured bucket was secured, preventing a potential data breach that could have cost millions in fines and reputational damage.
Identifying and Patching Critical Vulnerabilities Before an Exploit
Scenario: A global financial institution discovered that several of its customer-facing applications were running outdated versions of a widely used web server software.
- Risk: A recently disclosed zero-day vulnerability in that software was actively being exploited by threat actors, putting millions of customer accounts at risk.
- Solution: By using automated vulnerability scanning, the security team quickly identified which applications were running the vulnerable software and prioritized patching those systems within 24 hours. Because of this proactive attack surface assessment, the institution avoided potential breaches that could have led to massive financial and reputational loss.
Detecting a Rogue Insider Before a Data Leak
Scenario: A tech startup was expanding rapidly and granted employees broad access to internal systems. An attack surface assessment revealed that multiple employees still had access to sensitive financial data even after switching roles.
- Risk: One former employee, who had access to proprietary software source code, attempted to sell it on the dark web after leaving the company.
- Solution: By conducting regular access control audits as part of attack surface management, the company flagged unnecessary access privileges and revoked them before the ex-employee could exploit them. This prevented intellectual property theft and legal repercussions.
Attack Surface Management (ASM) FAQs
ASM focuses on external attack surfaces and continuously identifies unknown assets, whereas traditional vulnerability management primarily assesses known internal assets and patches vulnerabilities.
