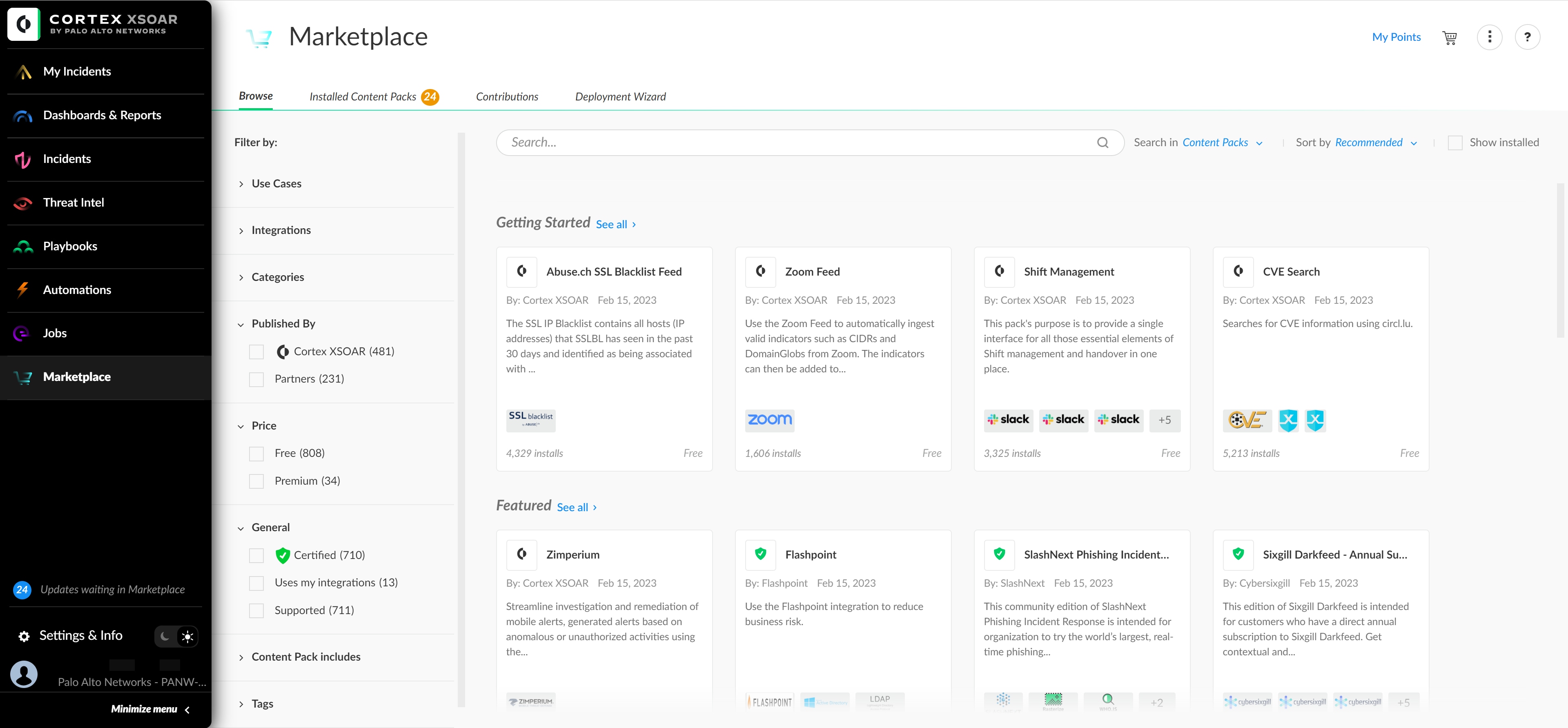
When it comes to incident response, SOC teams must shift their thinking to an automation-first mindset.
Putting humans at the frontlines of incident response is no longer sustainable. Modern SOCs are incorporating automation into their incident response workflows to maximize operational efficiencies.
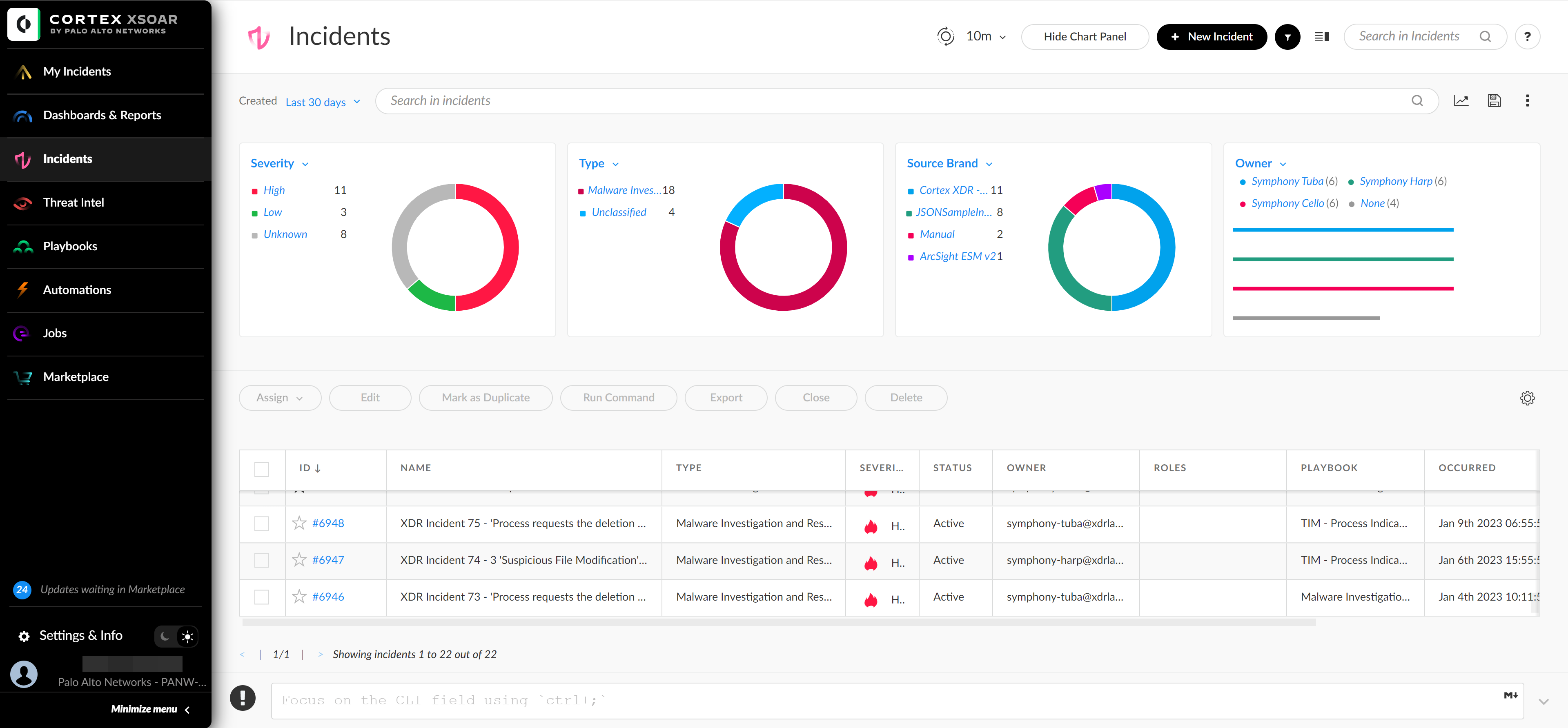
Reduce alert noise and surface critical incidents
Eliminate repetitive, manual tasks
Facilitate analyst investigation and collaboration
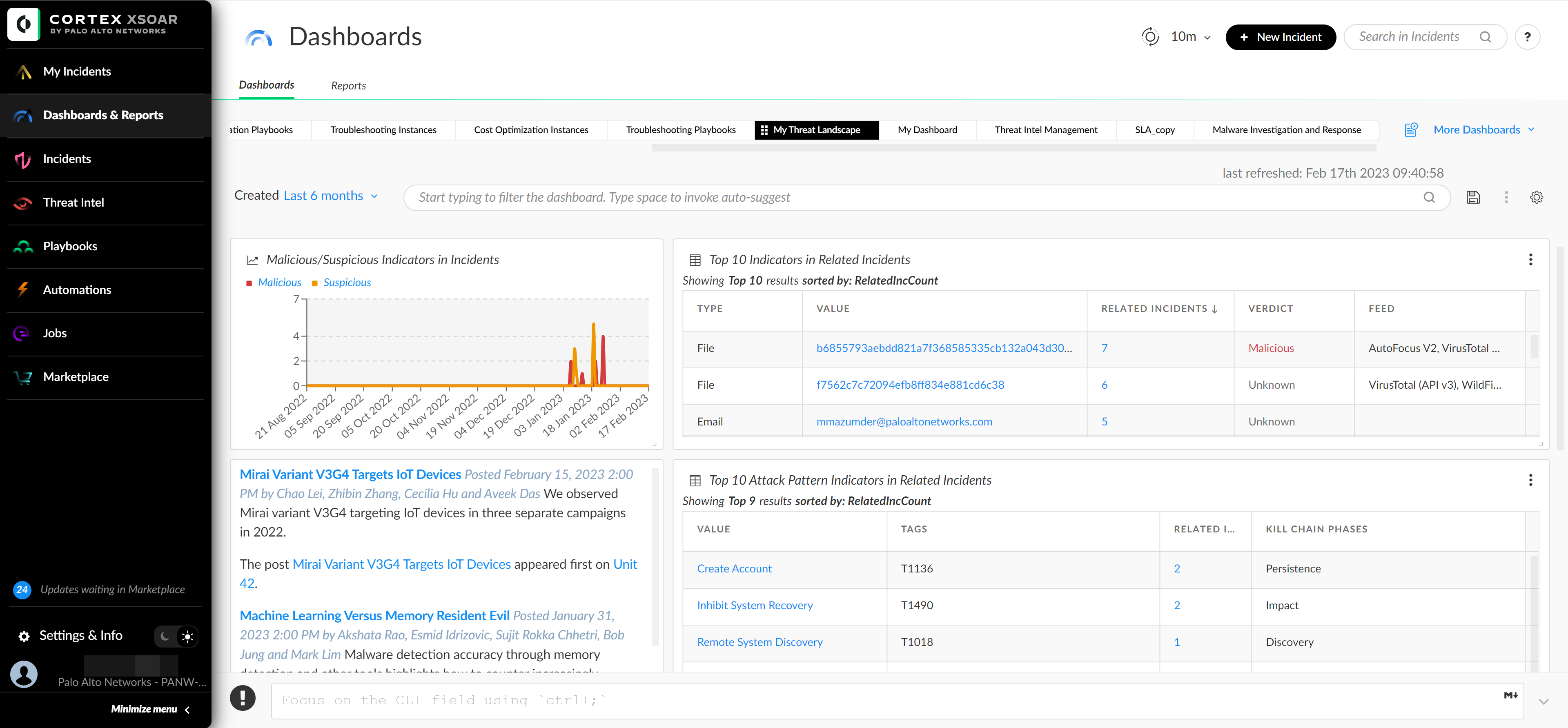
Map external threats to SOC incidents