Visibility
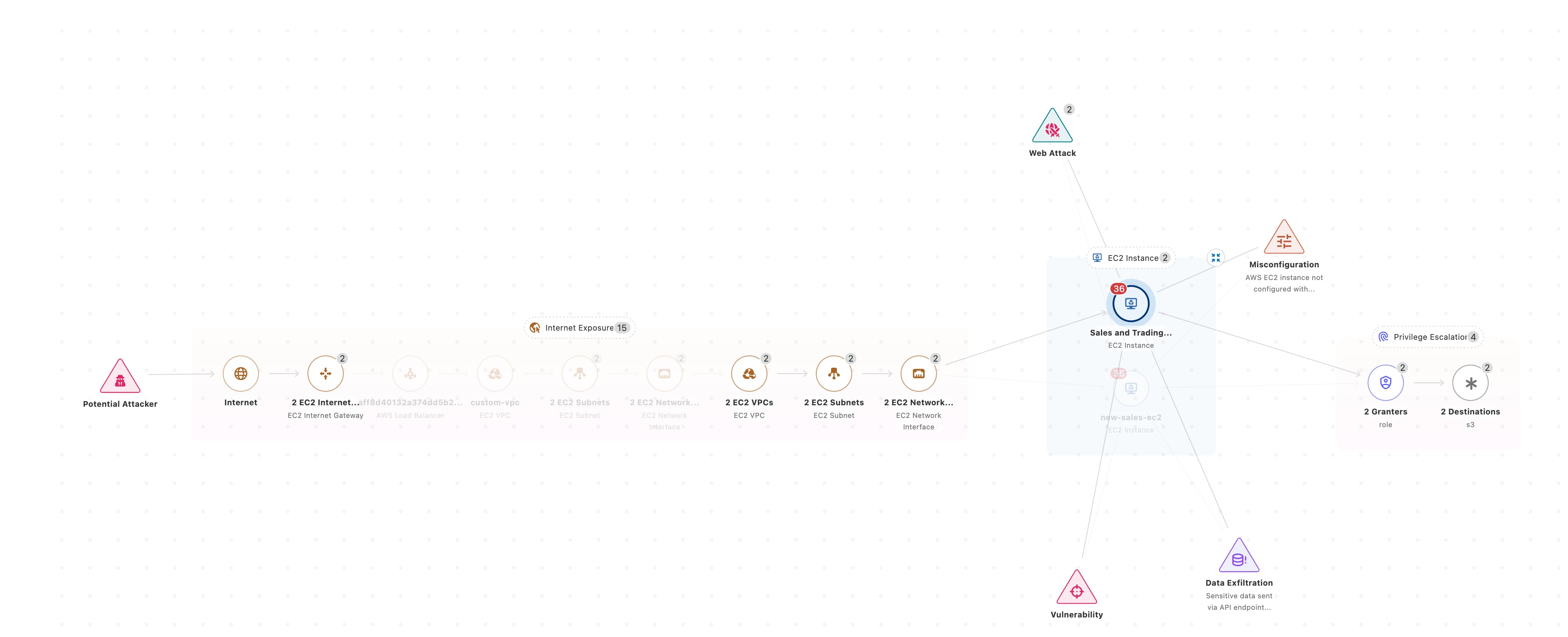
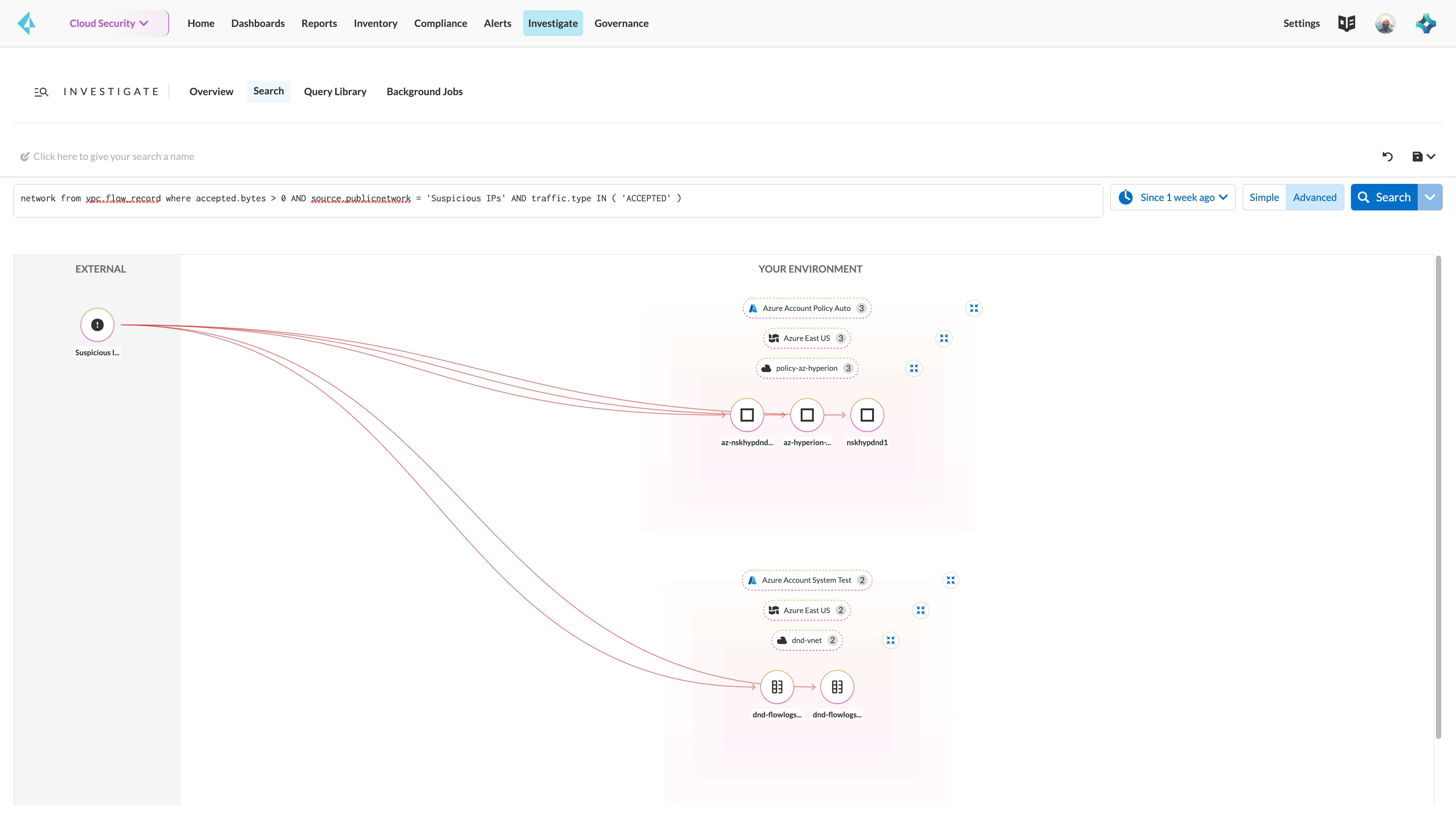
Prisma Cloud delivers comprehensive visibility across your cloud environments. While some solutions capture snapshots of your cloud, Prisma Cloud provides continuous monitoring and near real-time detection.
Agentless visibility
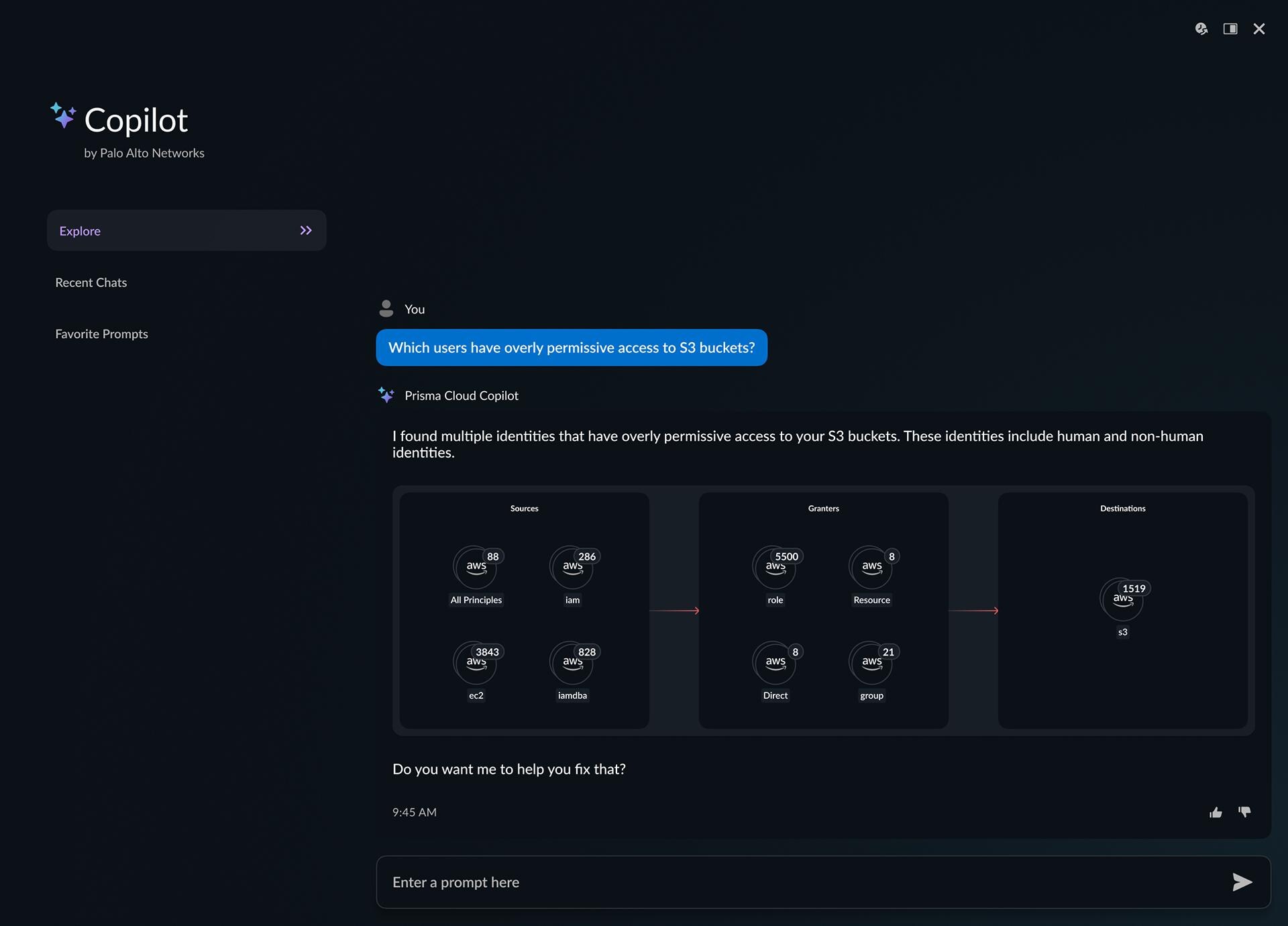
Simply connect Prisma Cloud to your cloud environments in minutes to gain visibility across IaaS, PaaS, Kubernetes, containers, serverless functions, networks and storage services. Prisma Cloud offers valuable insights without disrupting business or inserting agents and proxies.
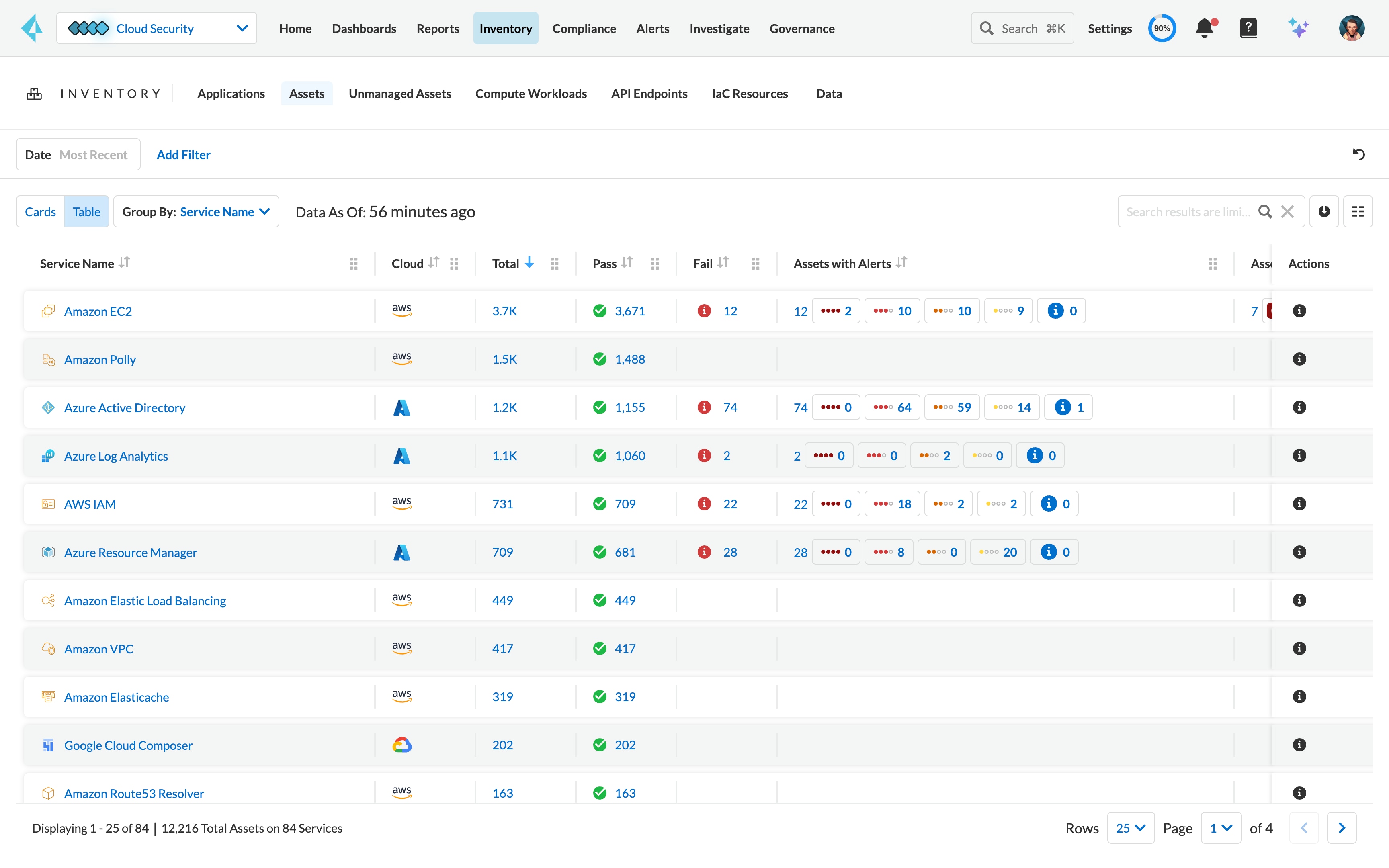
Broad cloud coverage
Get visibility into more than 350 cloud-native services across the six largest cloud providers—Amazon Web Services (AWS), Microsoft Azure, Google Cloud (GCP), Oracle Cloud (OCI), Alibaba Cloud and IBM Cloud.
Near real-time visibility
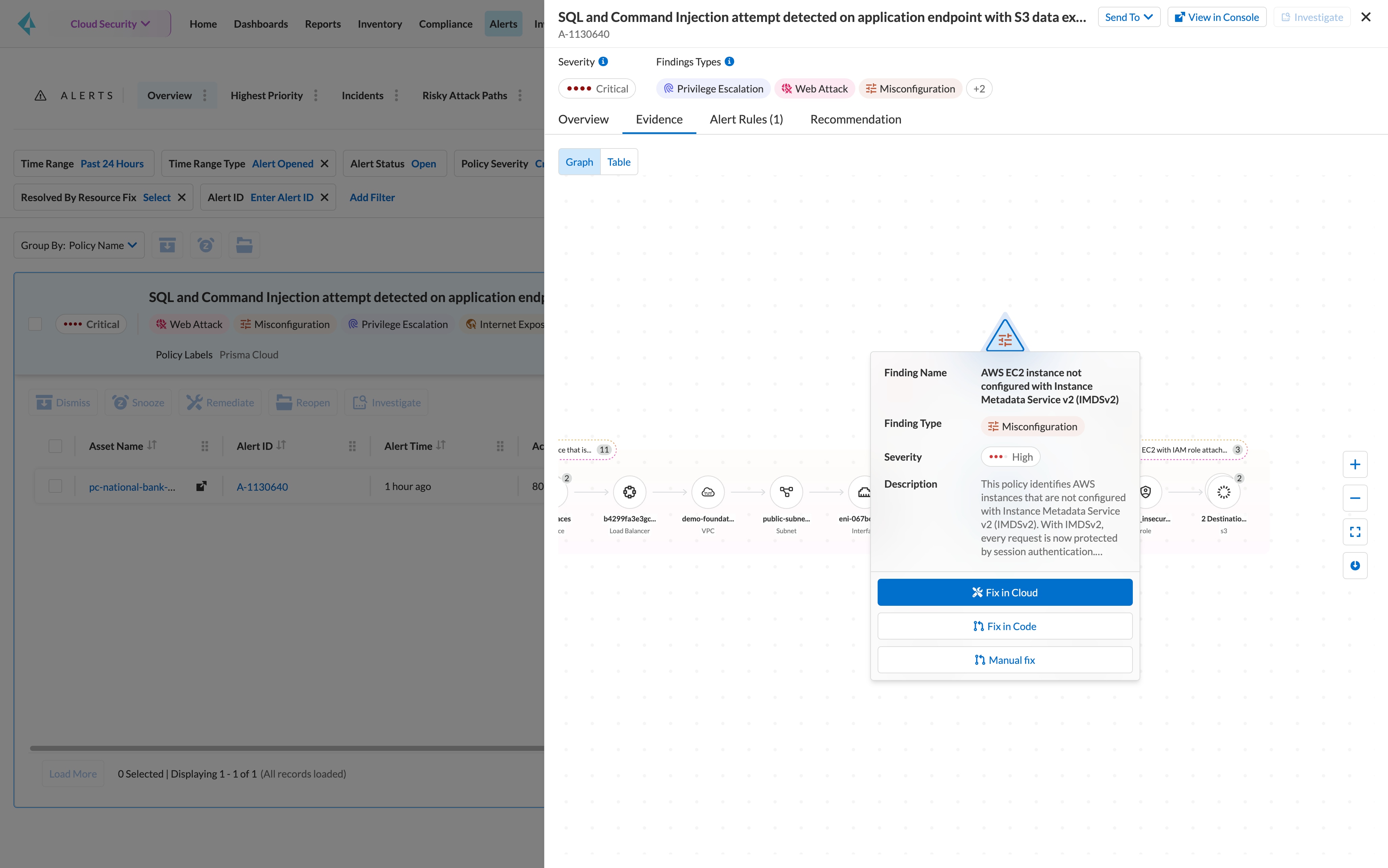
Unlike snapshot-based tools that provide point-in-time visibility, Prisma Cloud continuously monitors cloud environments. You get near real-time misconfiguration detections and historical lookback of configuration changes.