Defeat attacks with machine learning
Antivirus signatures can’t keep up with fast-moving threats. You can eliminate known and unknown malware with AI-powered security that continuously evolves to stop new attacks.
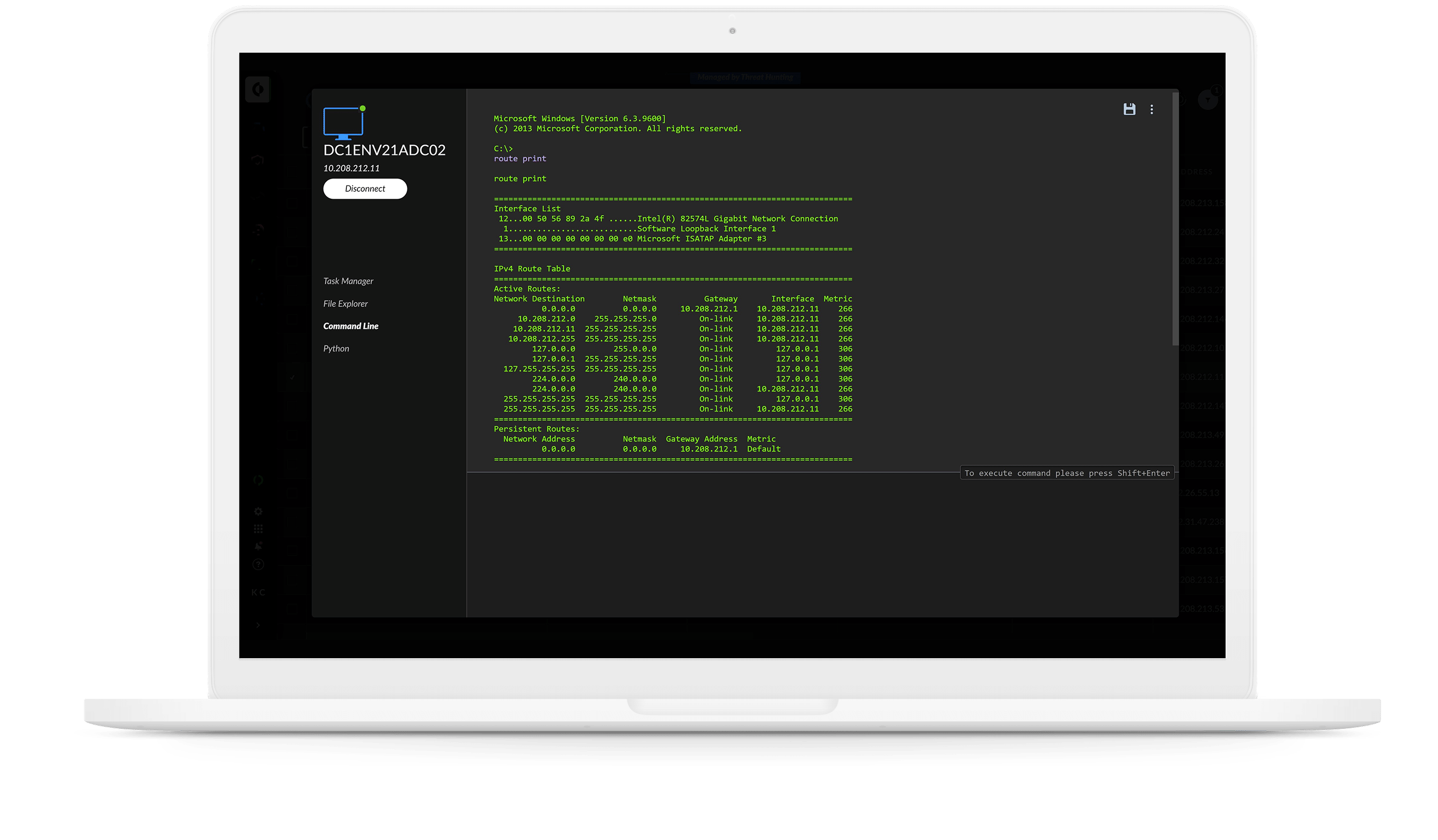
AI-driven local analysis
Analyze thousands of attributes of a file to correctly find and block malware.
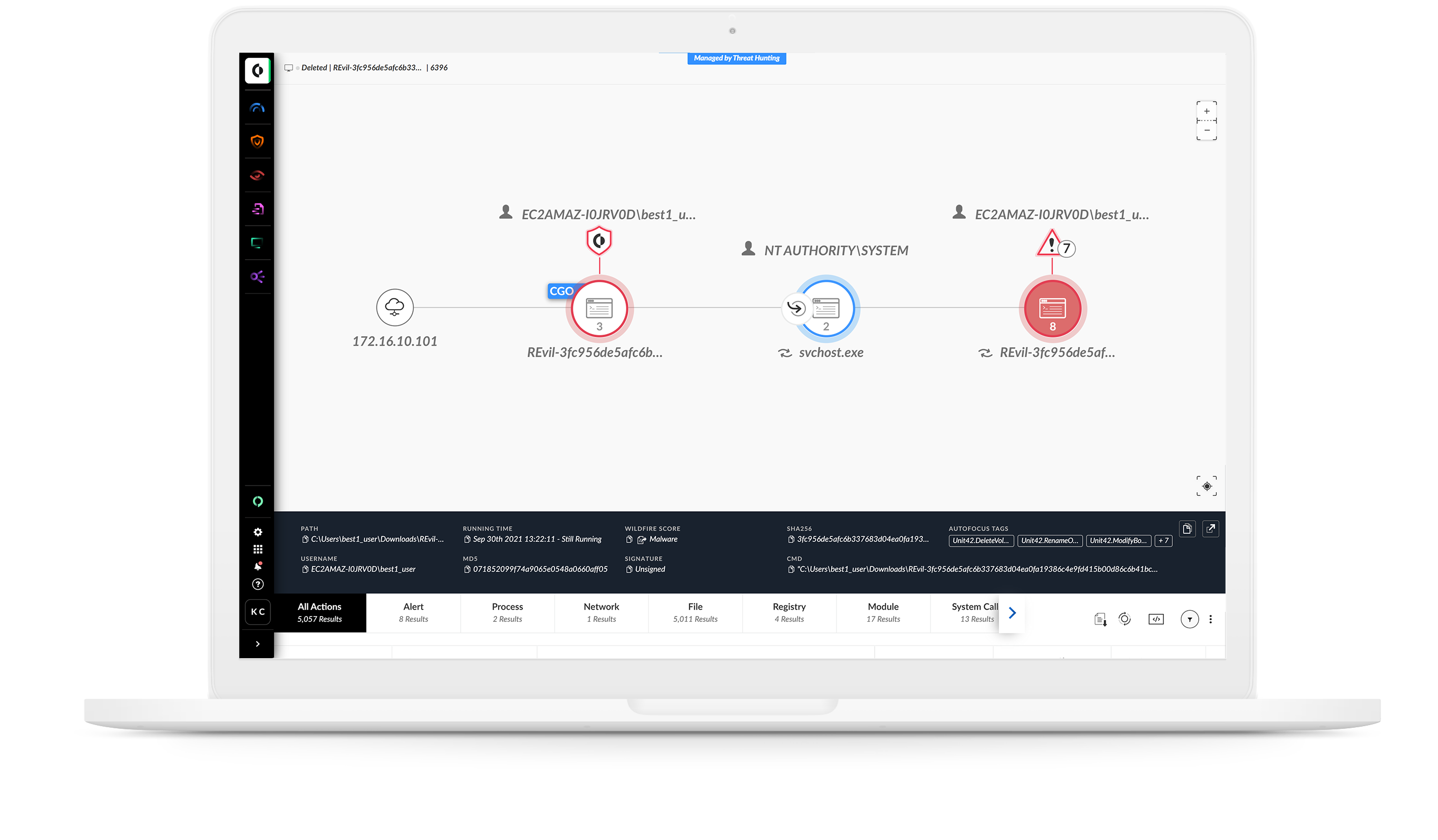
Up-to-date ML models
Tap into a high-performance machine learning framework and an expansive ML training set, powered by WildFire threat intelligence, to halt emerging threats.