Close on the heels of Cortex XDR 2.2 and 2.3, we are proud to announce the availability of Cortex XDR 2.4, which is jam-packed with new features that enhance detection, investigation and ease of management. From vulnerability assessment to integration with Cortex XSOAR Threat Intel Management, this release has something for everyone. We’ll walk you through the highlights in this blog, but be sure to check out our release notes for all the technical details.
Lightning Fast Investigations with Quick Launcher and Pivoting
Every second counts during a cyberattack, and Cortex XDR is designed to make investigations as efficient as possible. To further reduce the number of clicks required to conduct your investigations, we have introduced Quick Launcher and alert pivoting. Now you can easily conduct common investigation tasks or initiate response actions from anywhere in the Cortex XDR management console.
Use the Quick Launcher to:
- Search events for host, IP address, domain and hash.
- Blacklist and whitelist processes by hash.
- Add domains or IP addresses to an external dynamic list (EDL) blocklist.
- Create a new IOC for an IP address, domain or hash.
- Open a Live Terminal session, initiate a malware scan or isolate an endpoint.
You can simply highlight values such as IP addresses or file names in the Cortex XDR management console to pre-populate a query in the Quick Launcher – avoiding the extra steps of copying and pasting values and navigating to the Query Builder.
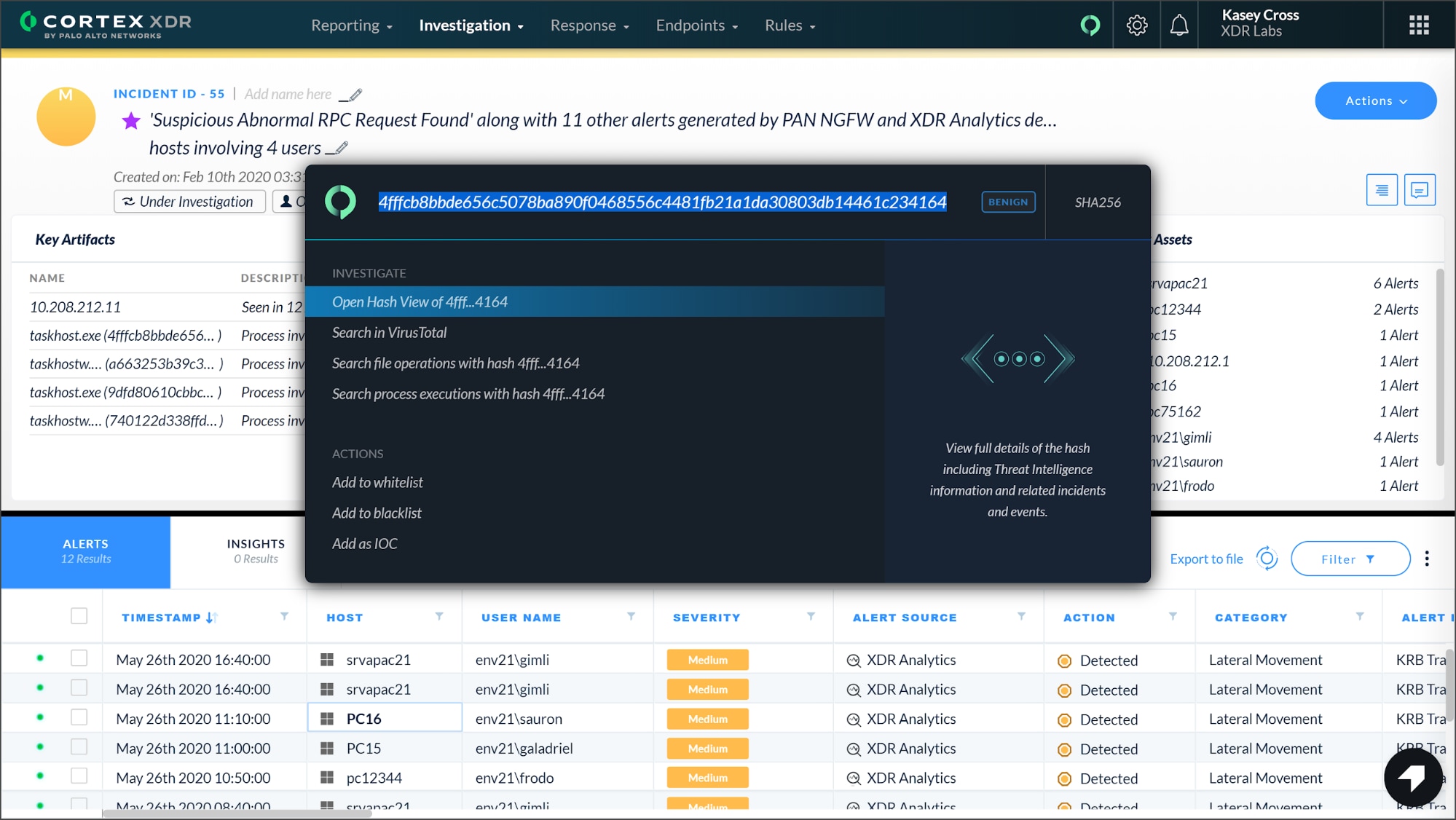
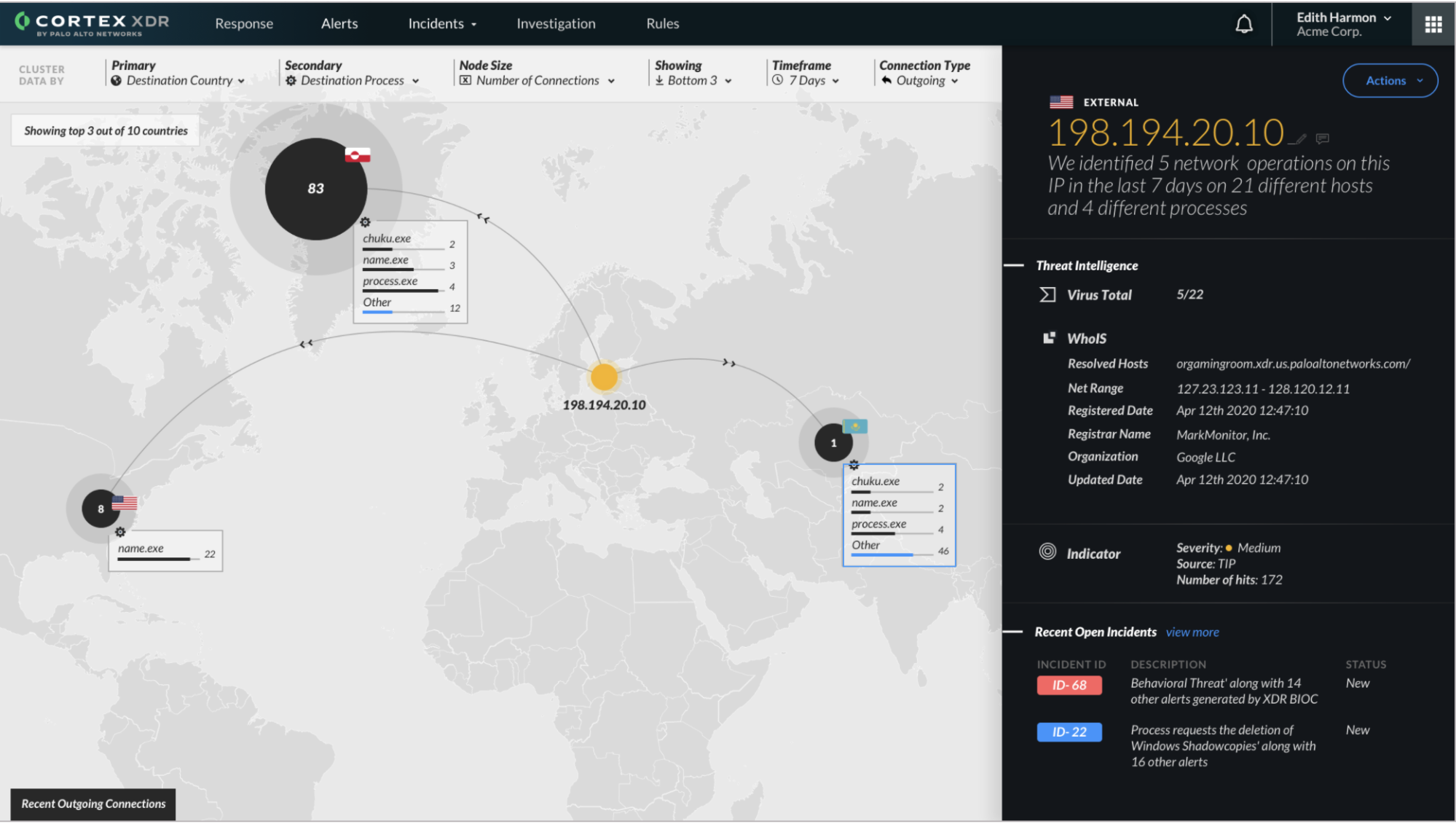
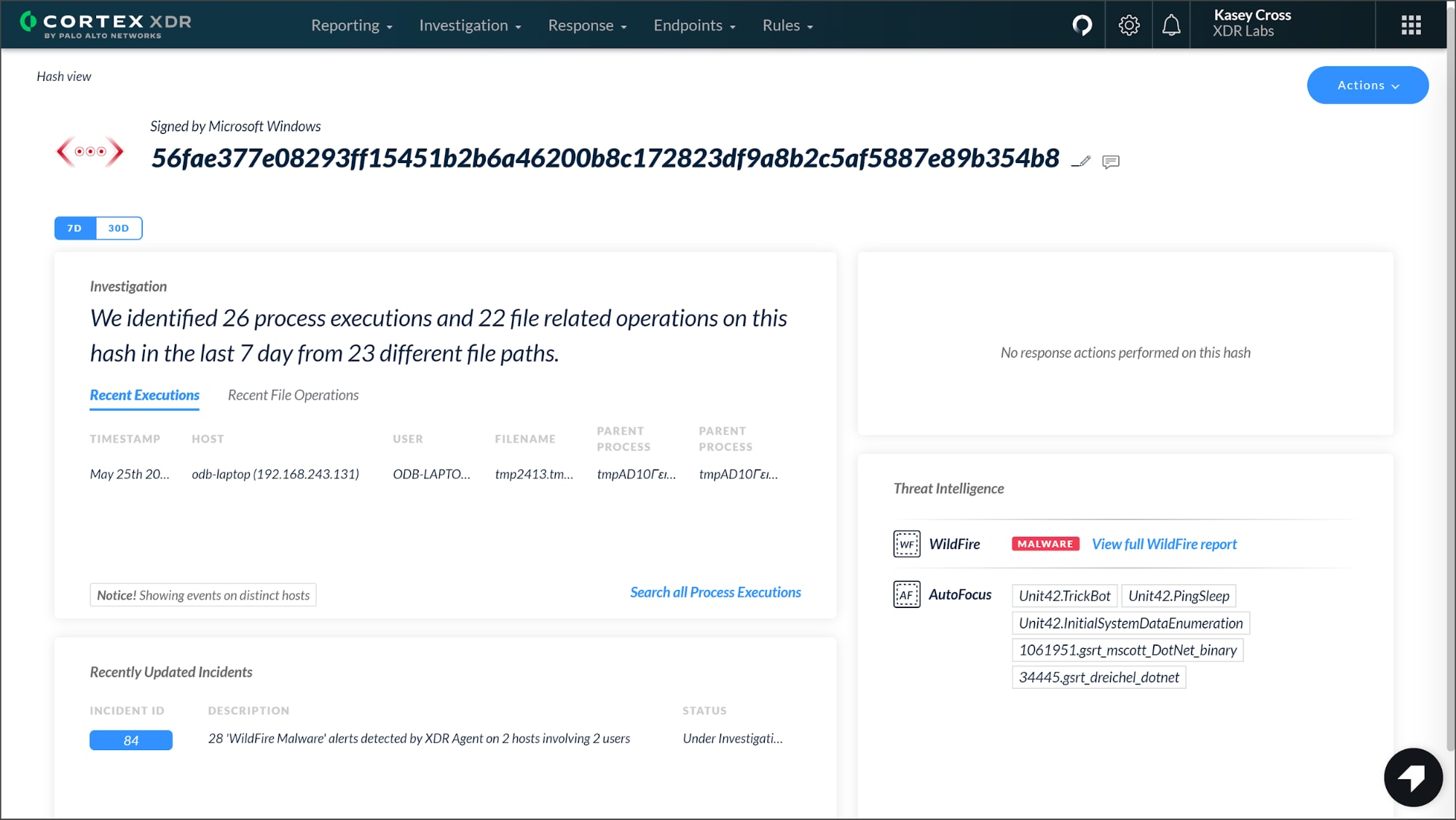
From the Quick Launcher, you can open the IP View or Hash View to display the essential details you need to know about IP addresses and hashes on one screen. From the IP view, you can view threat intelligence, geolocation and network information as well as related incidents involving the IP address. The Hash View reveals recent process executions, threat intelligence data, and associated incidents and response actions. You can also easily navigate to related incidents for further analysis.
To make investigating attacks easier than ever, Cortex XDR 2.4 supports:
-
- Pivoting between alerts, rules, and incidents – You can now pivot from an IOC and BIOC rule to the alerts triggered by the rule with a single click, simplifying investigation workflows. You can also pivot from an alert to a related incident.
- Alert table enhancements – You can view, sort and filter endpoint alerts based on MAC address, domain and endpoint operating system, as well as network alerts based on App-ID category, email subject, URL and much more.
- Remote Procedure Call (RPC) visibility – When analyzing alerts, you can see whether local or remote processes used RPC requests or code injection to initiate events on other processes. These insights can quickly expose malicious activity.
Integration with Cortex XSOAR Threat Intel Management
Spotting indicators of compromise can help you quickly find and root out adversaries. A new API in Cortex XDR 2.4 enables you to outpace adversaries by consuming threat intelligence feeds from third-party sources in JSON and CSV formats. In addition, native integration with Cortex XSOAR Threat Intel Management allows you to have granular control over which indicators to provide to Cortex XDR for IOC-based detection. By gathering threat intelligence data, you can identify threats hiding in your security data. Integration with Cortex XSOAR is expected to be available on June 9.
Vulnerability Assessment
With thousands of new vulnerabilities reported every year, many security teams struggle to find and assess the vulnerabilities in their organizations. Cortex XDR 2.4 alleviates those challenges by identifying and prioritizing your security vulnerabilities. From the Cortex XDR management console, you can view the vulnerabilities detected on your Linux endpoints by CVE or by host.
Additionally, Cortex XDR provides you with a list of all applications installed on your Windows and Linux endpoints and indicates the CVEs only where they exist, providing you with an application inventory of your network.
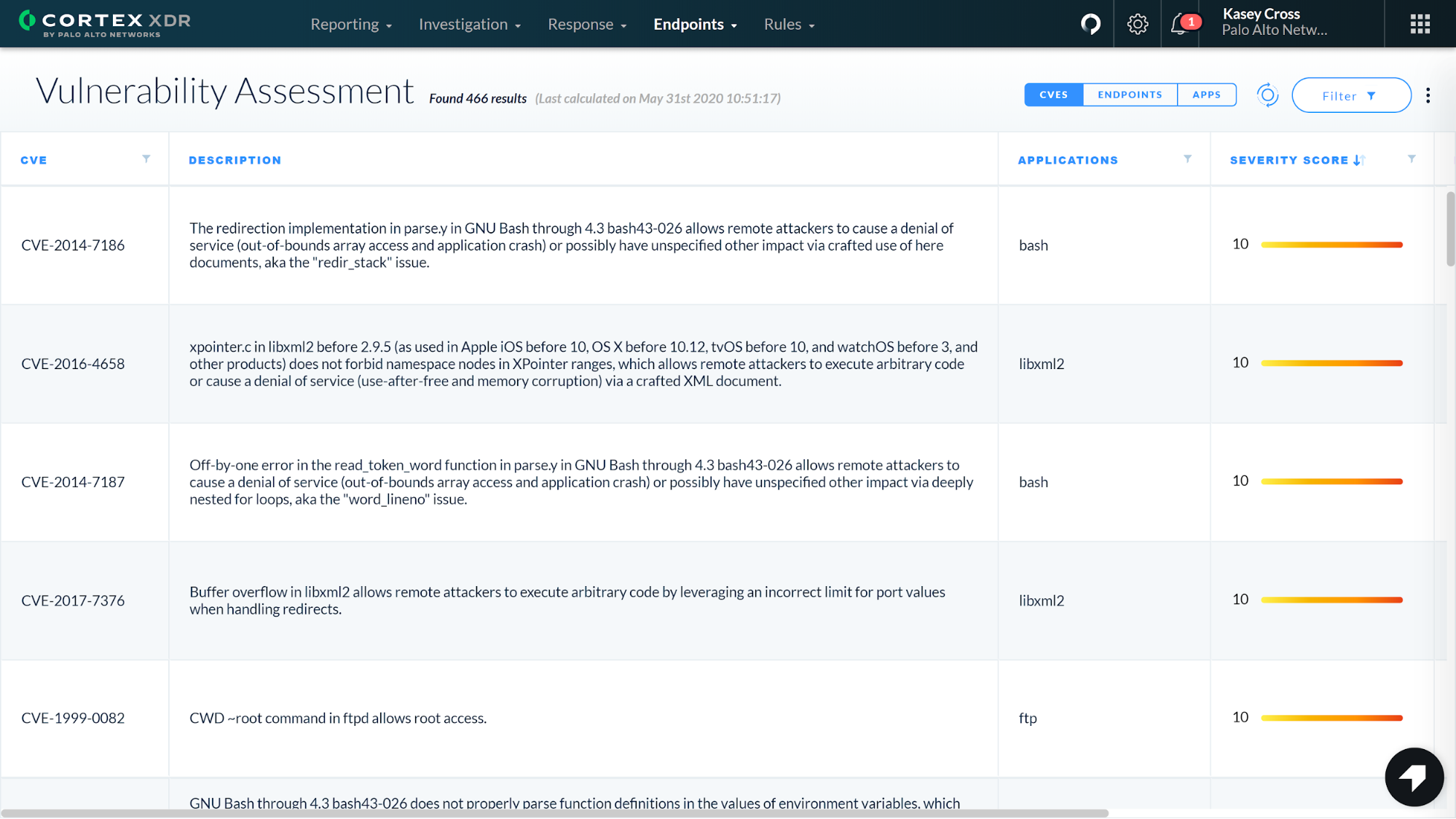
To help you understand vulnerability severity, Cortex XDR retrieves the latest data for each CVE from the NIST National Vulnerability Database, including CVE severity and metrics.
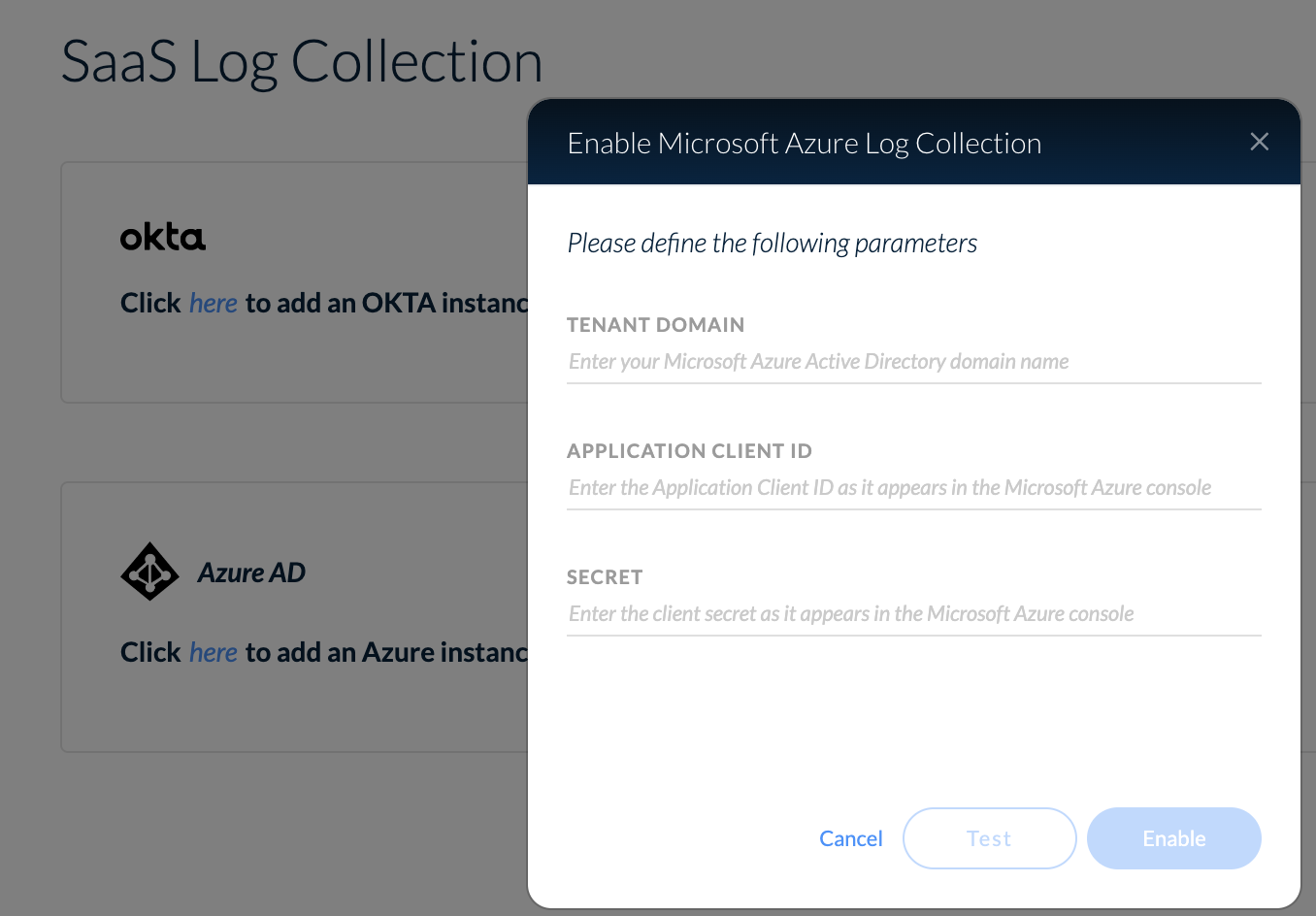
Okta and Azure Active Directory Log Support
Authentication logs allow you to unearth unusual user activity like credential abuse. By searching for suspicious activity, such as a user signing in from an external IP address, you can track down user-based attacks.
In addition to Kerberos and Windows Event Logs, Cortex XDR now collects authentication data from Okta and Microsoft Azure Active Directory. It automatically normalizes these logs from both cloud-based authentication services and provides a platform to query and review authentication sessions. You can hunt for and investigate threats by searching through authentication logs with the Query Builder or text-based queries.
Supercharged Threat Hunting
Our Query Builder is an intuitive search tool, allowing analysts of all skill levels to conduct investigations without needing to learn a new query language. However, advanced threat hunters may wish to perform advanced queries quickly and use more complex query parameters like wildcards. In Cortex XDR 2.4, these power users can execute simple or complex text-based queries to search across all their data in Cortex XDR.
With Native Search, currently available as a beta feature, you have the flexibility to quickly query any information you want, or to copy, edit and paste previous queries. As you type a query, the Native Search feature will help by autocompleting fields based on the known log fields. You can also use regex and wildcards in your queries and can string multiple queries together.
Examples of text-based queries include:
- network connections AND palo alto networks.app id = facebook
- okta.sso AND ip != 10.0.*
- palo alto networks.file create.file name =~ ”.+?”
- cortex xdr agent AND palo alto networks.dst process name CONTAINS chrome
(If you prefer that Unit 42 experts track down threats for you, check out the recently announced Cortex XDR Managed Threat Hunting service.)
But that’s not all…Cortex XDR 2.4 also includes even more enhancements:
- Interactive Script Execution – You can now initiate scripts in Interactive Mode to run multiple scripts on pre-defined endpoints, track the execution progress and view the results in real time.
- APIs – New API fields and values provide you better visibility and control over endpoint scans as well as blacklisted and whitelisted hashes.
- MSSP Management – MSSPs can quickly investigate and hunt for threats in their customers’ environments by executing searches in the Query Builder across multiple Cortex XDR tenants at once.
- Broker Service – You can now securely access the Broker VM using SSH and public key encryption.
For a complete list of new features in Cortex XDR 2.4 see the Cortex XDR release notes.