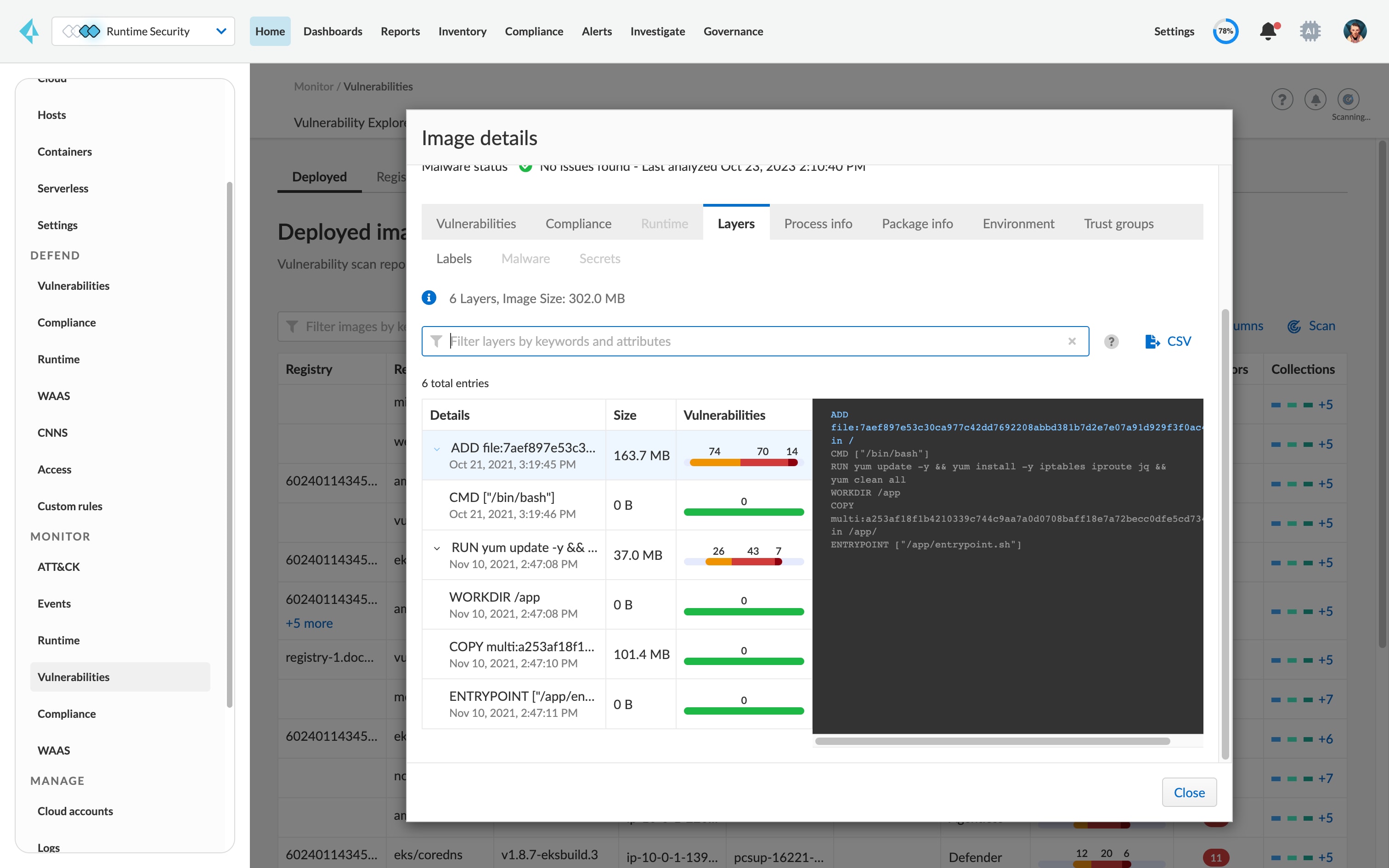
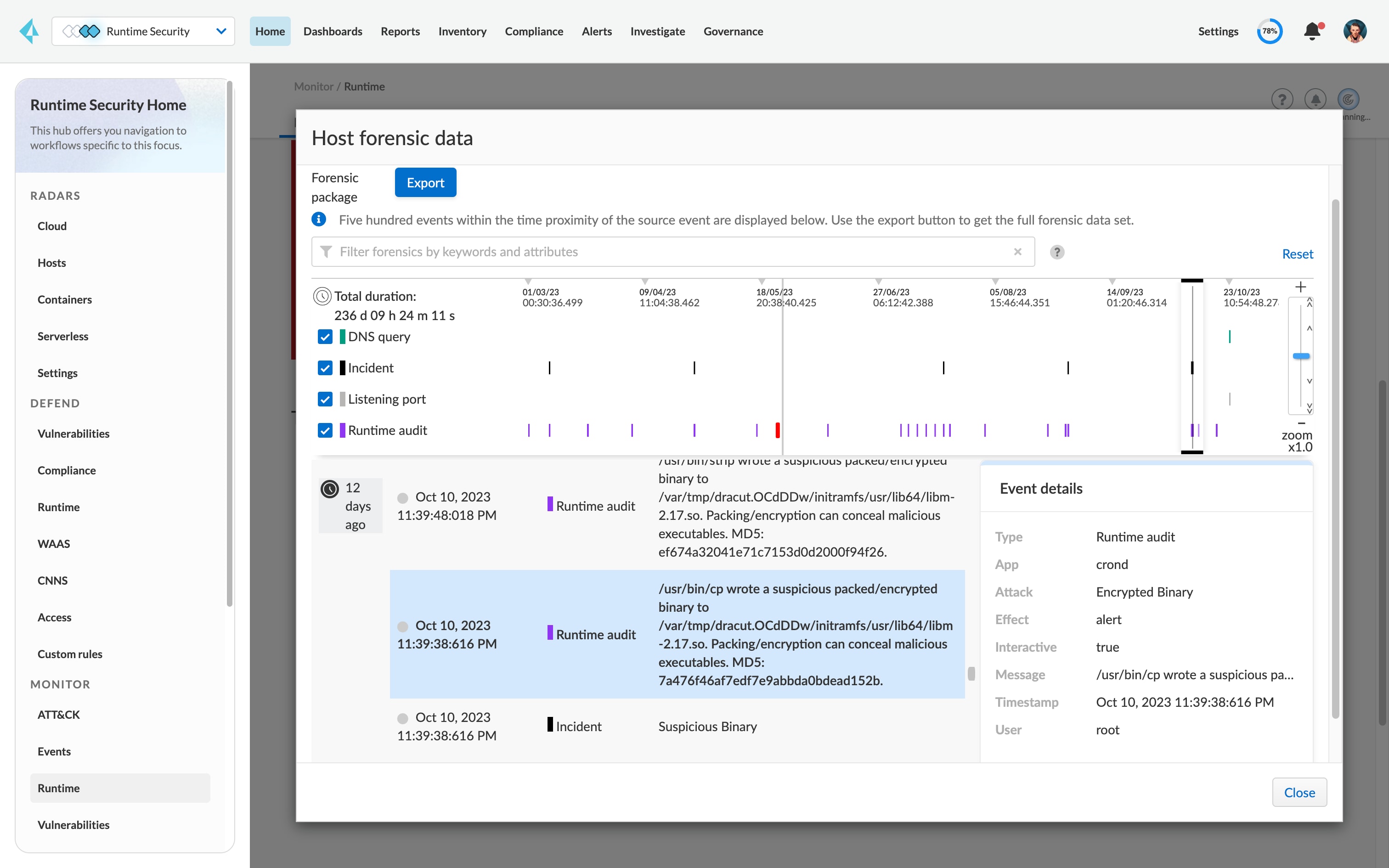
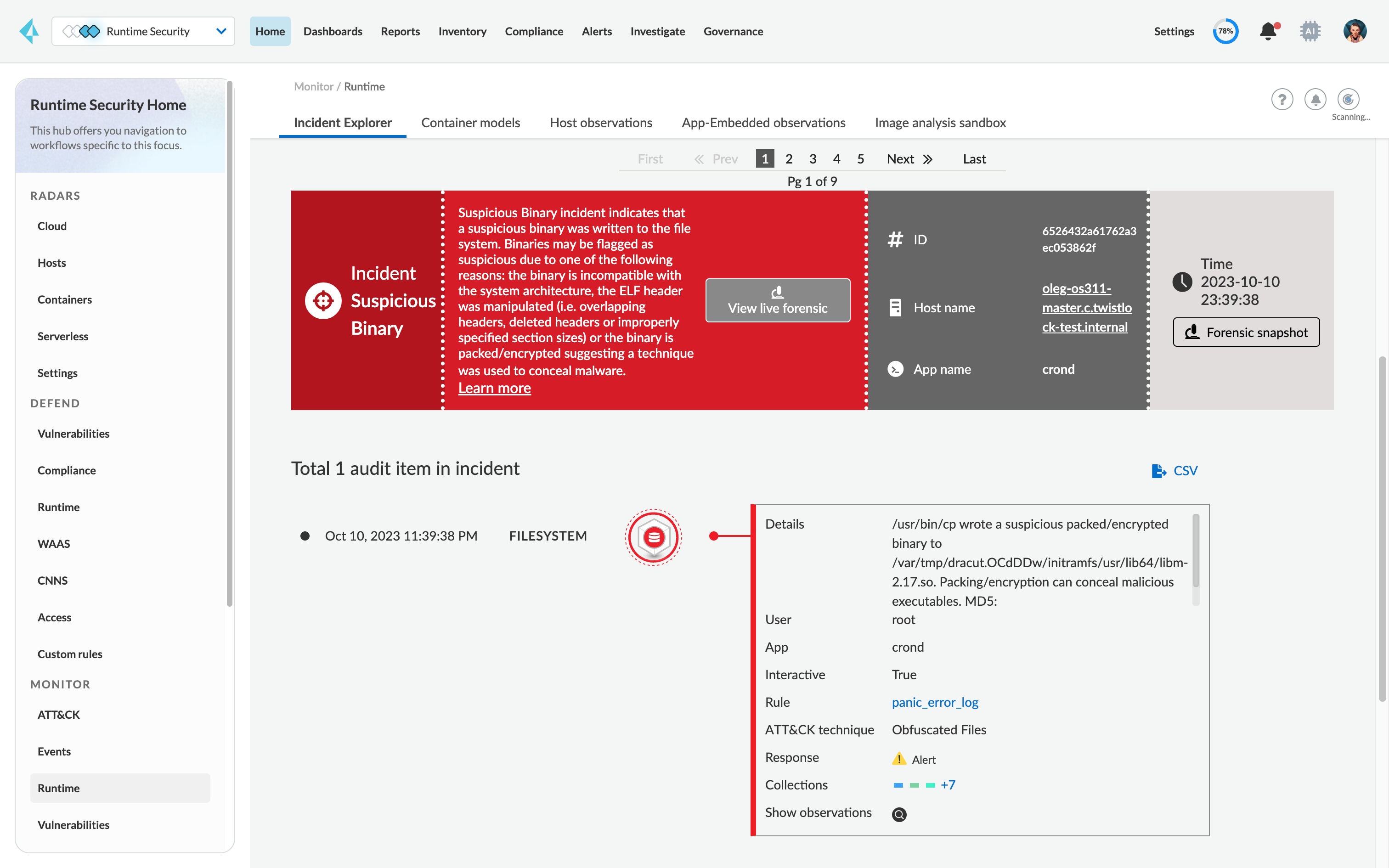
Vulnerability management
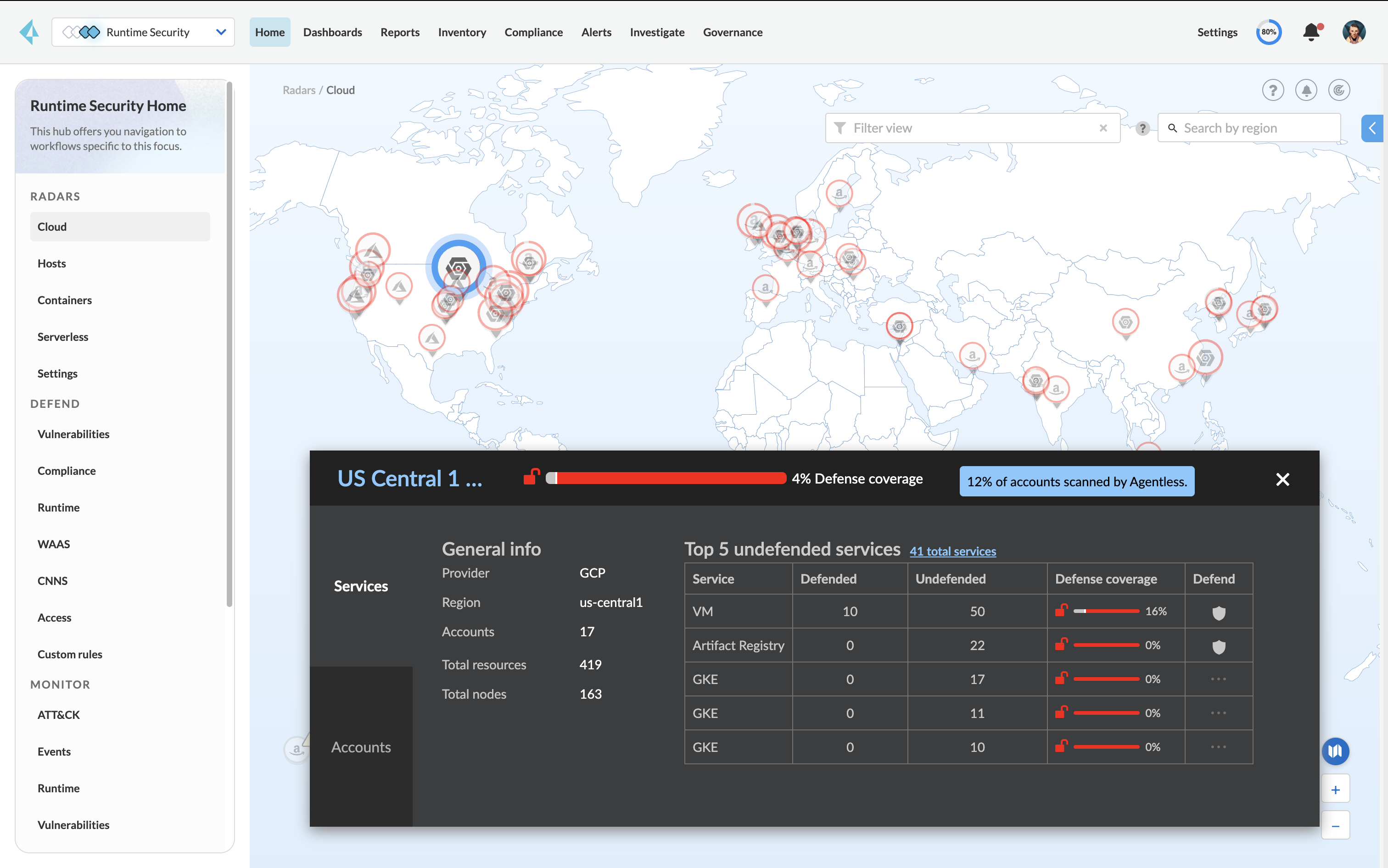
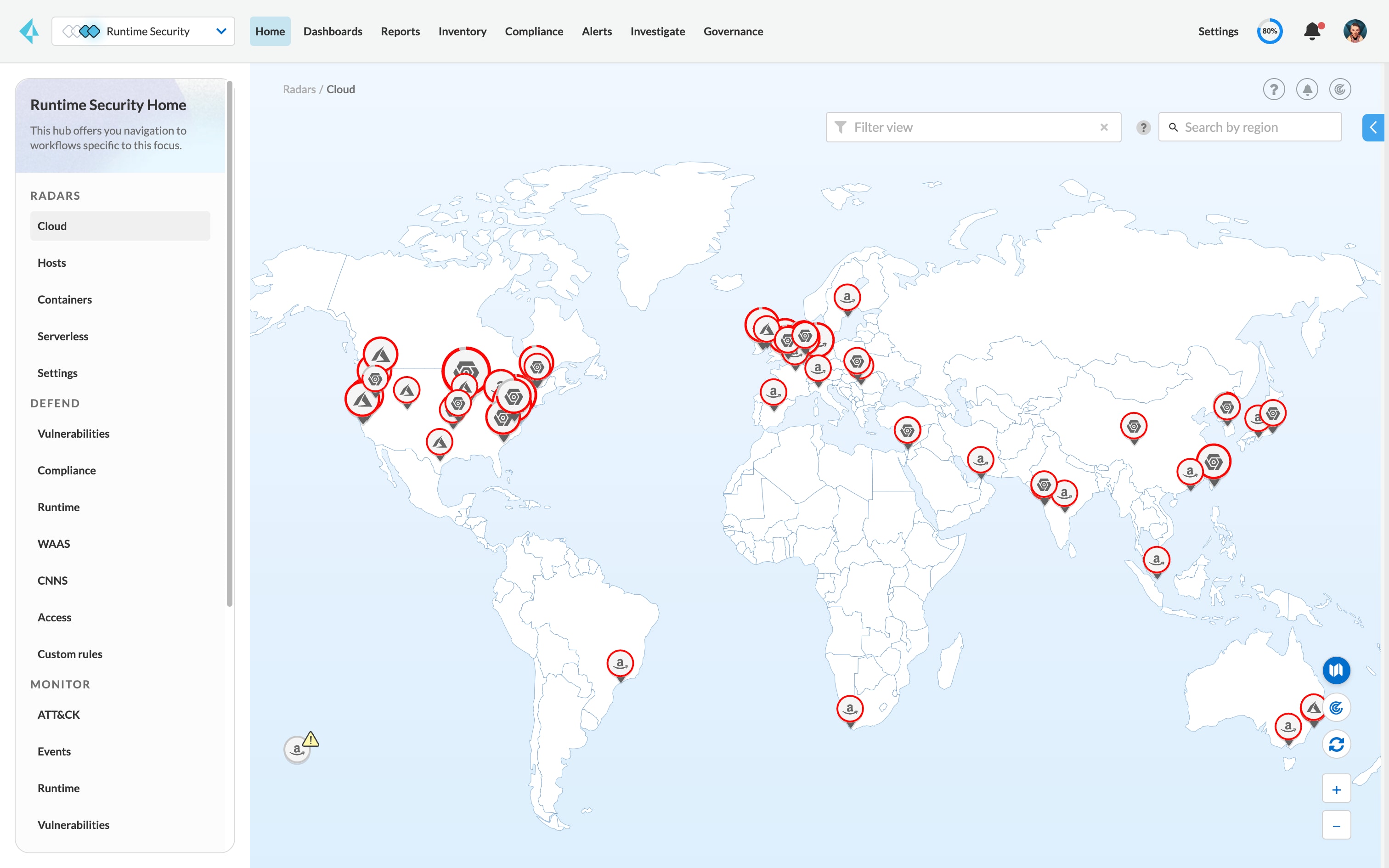
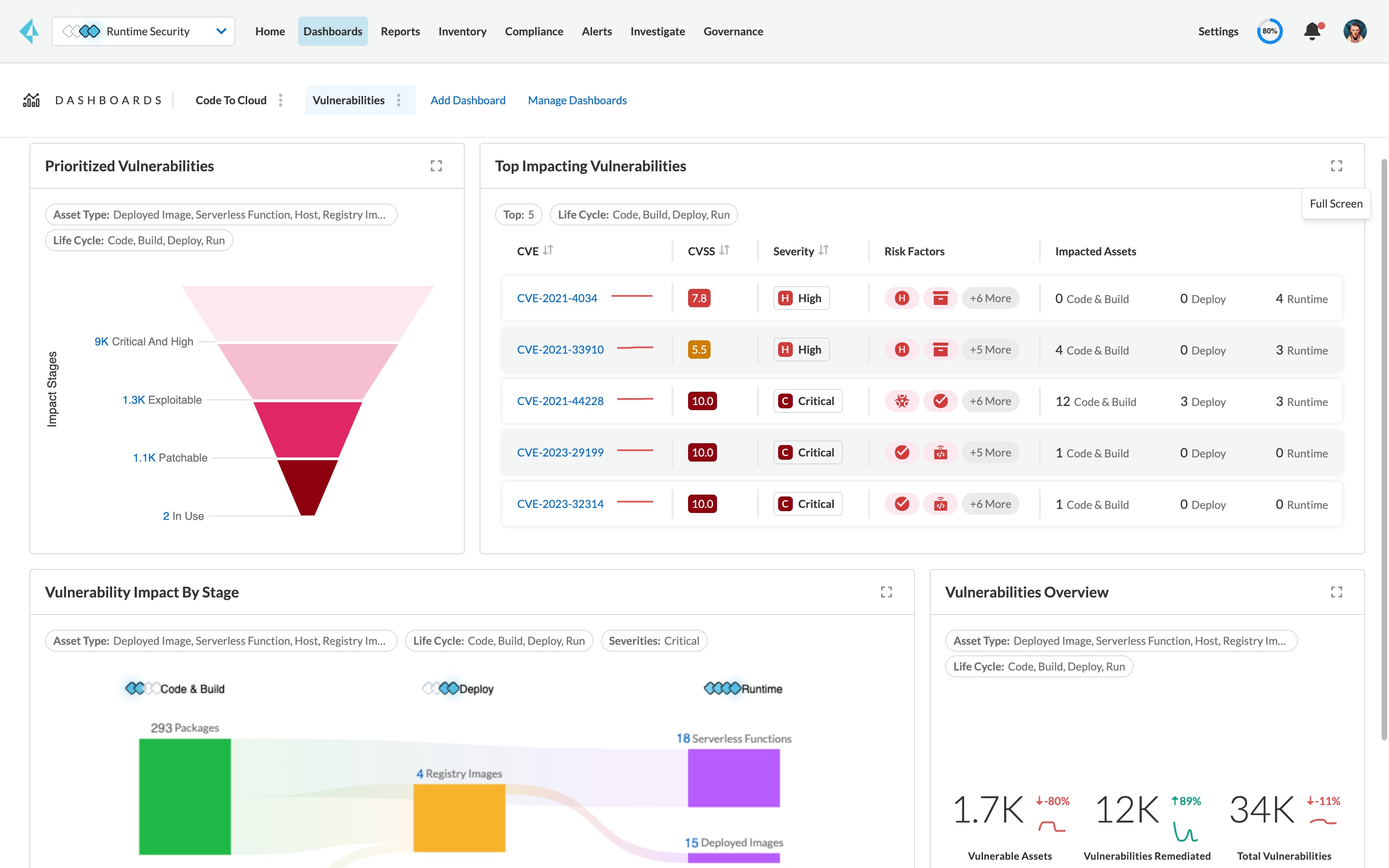
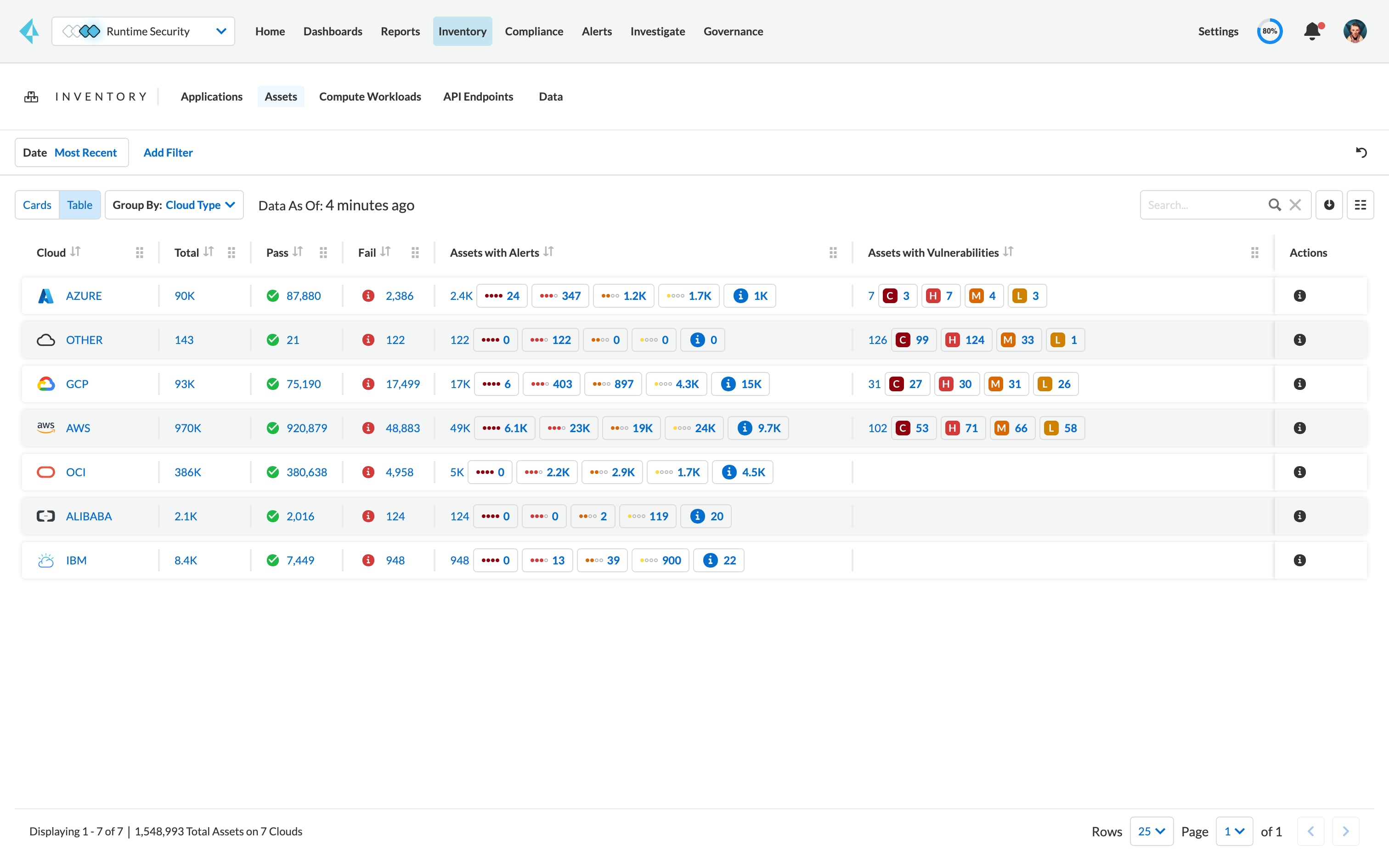
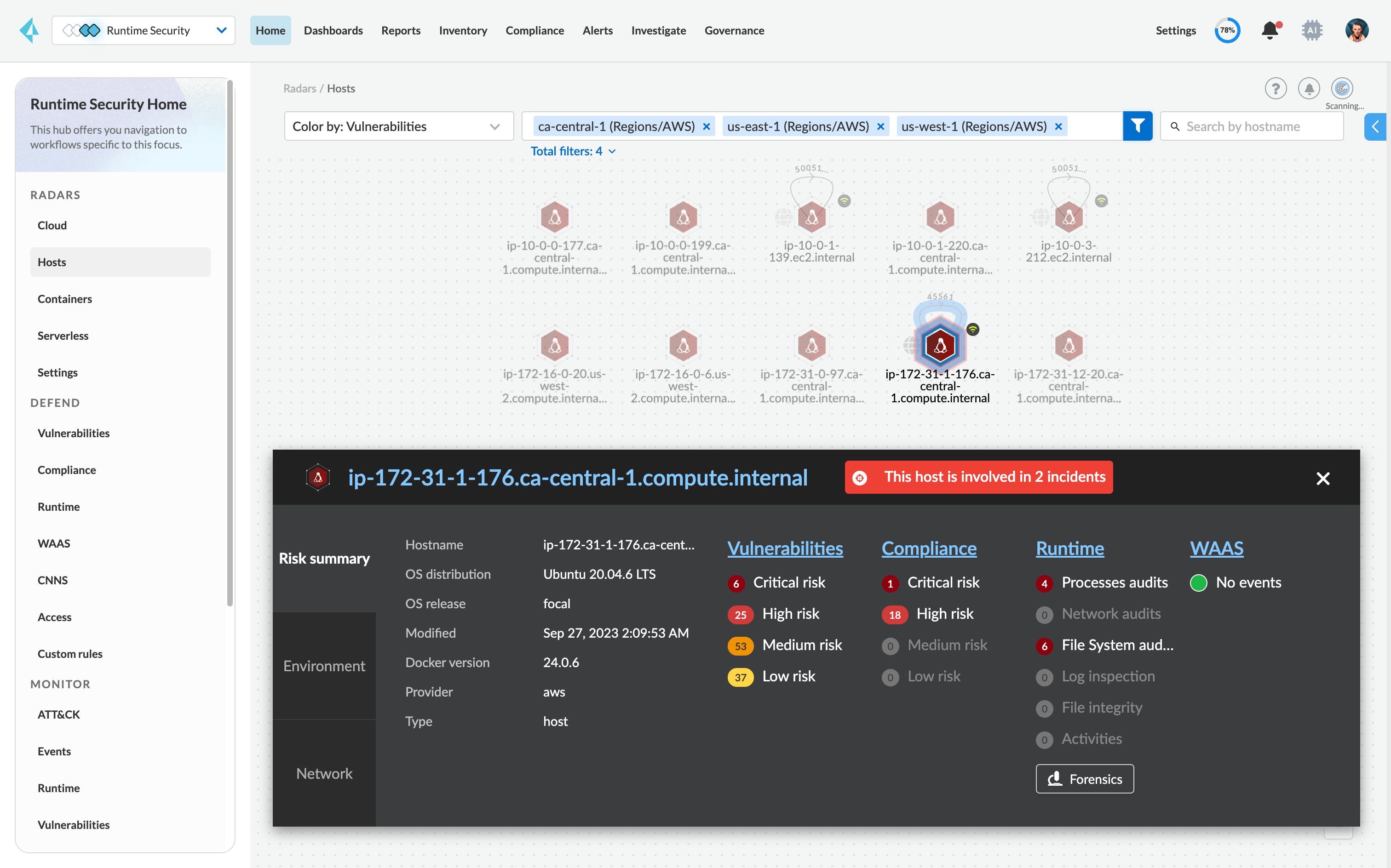
Securing cloud-native applications requires a comprehensive view into vulnerabilities across the application lifecycle. Prisma Cloud delivers a centralized view to help prioritize risks in real time across public cloud, private cloud and on-premises environments for every host, container and serverless function.
Manage risk from a single UI.
Prioritize risk across host OS, container images and serverless functions with intelligent risk scoring.
See vulnerability status with remediation guidance.
View every CVE with details and up-to-date vendor fix information, supporting all cloud-native technologies.
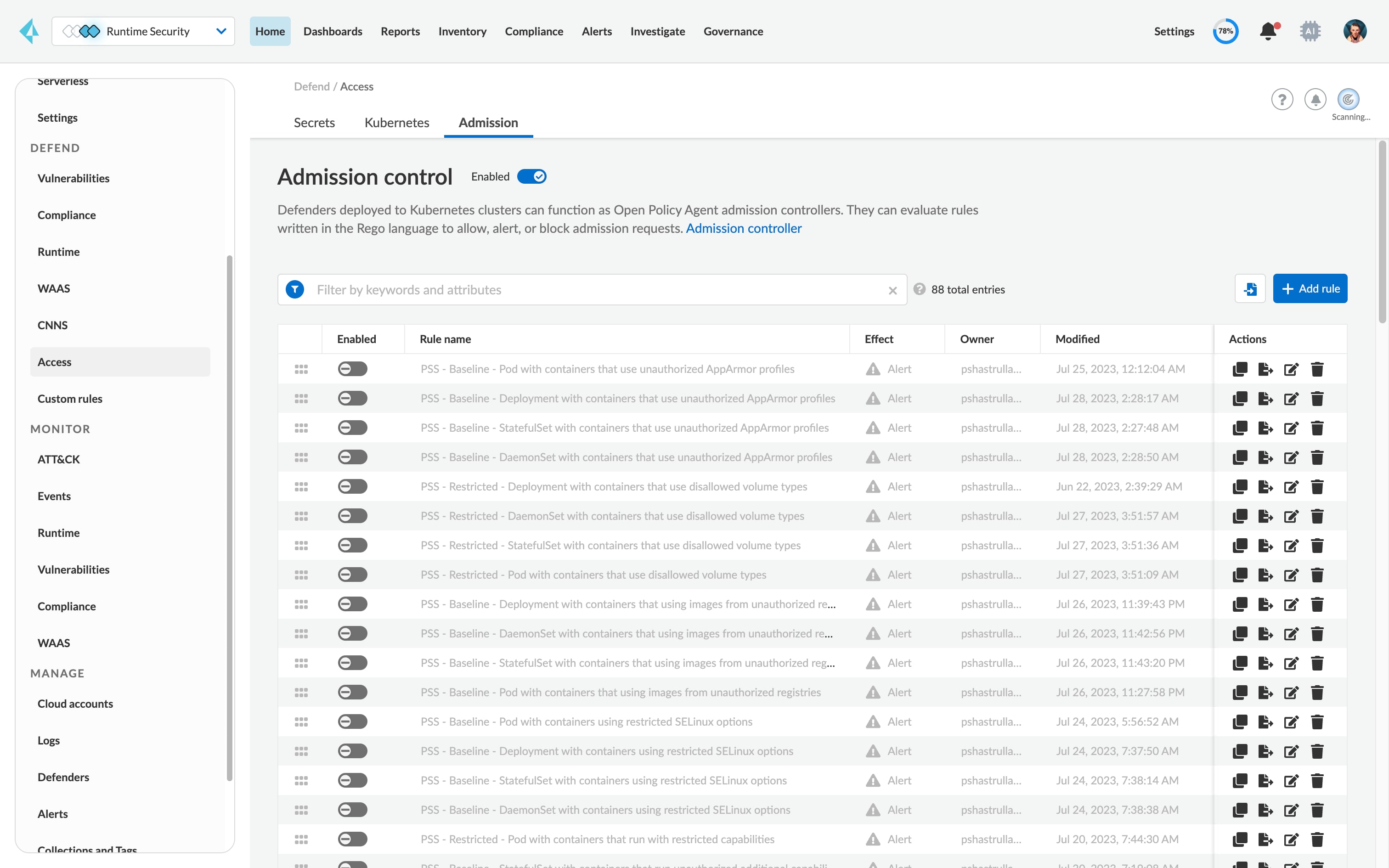
Alert on or prevent vulnerabilities across environments.
Set precise policies to alert on or prevent vulnerable components from running on your environments.
Integrate security into your CI/CD pipeline.
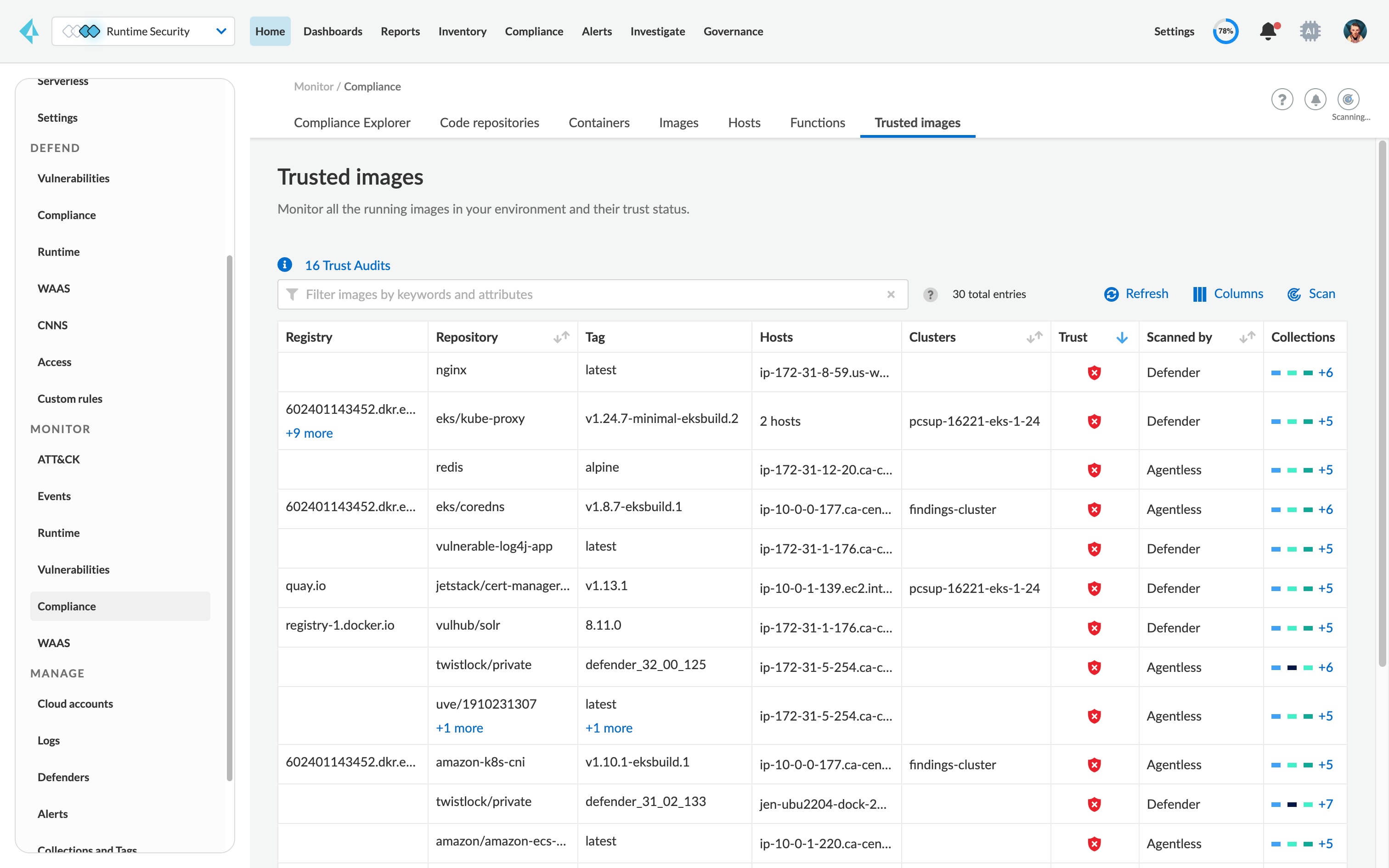
Continuously monitor container registries as well as explicitly define trustworthy images, registries and repositories.
Integrate data with your existing systems.
Integrate vulnerability alerts into common endpoints, including JIRA®, Slack®, PagerDuty®, Splunk®, Cortex® XSOAR™, ServiceNow® and more.