Vulnerability management
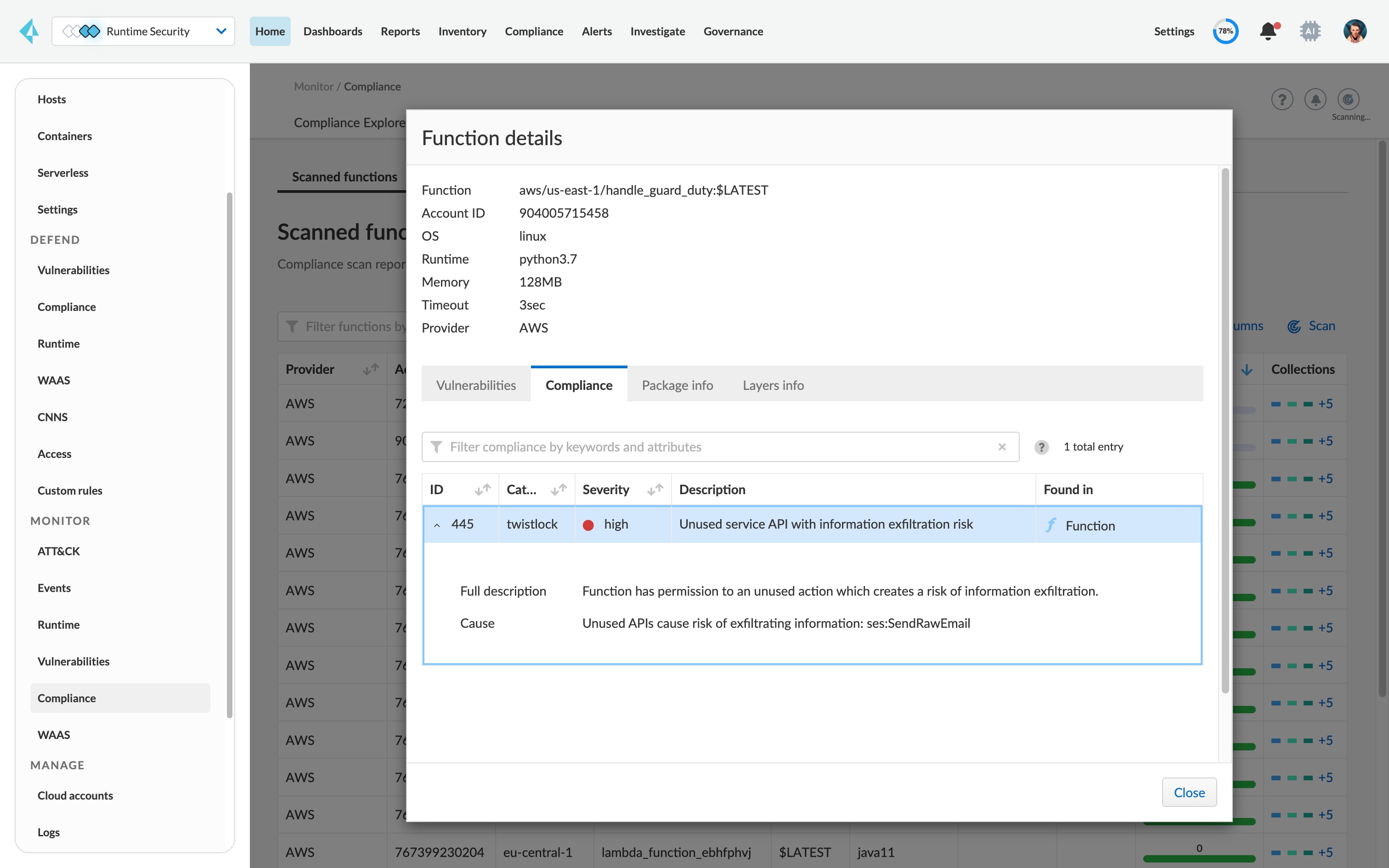
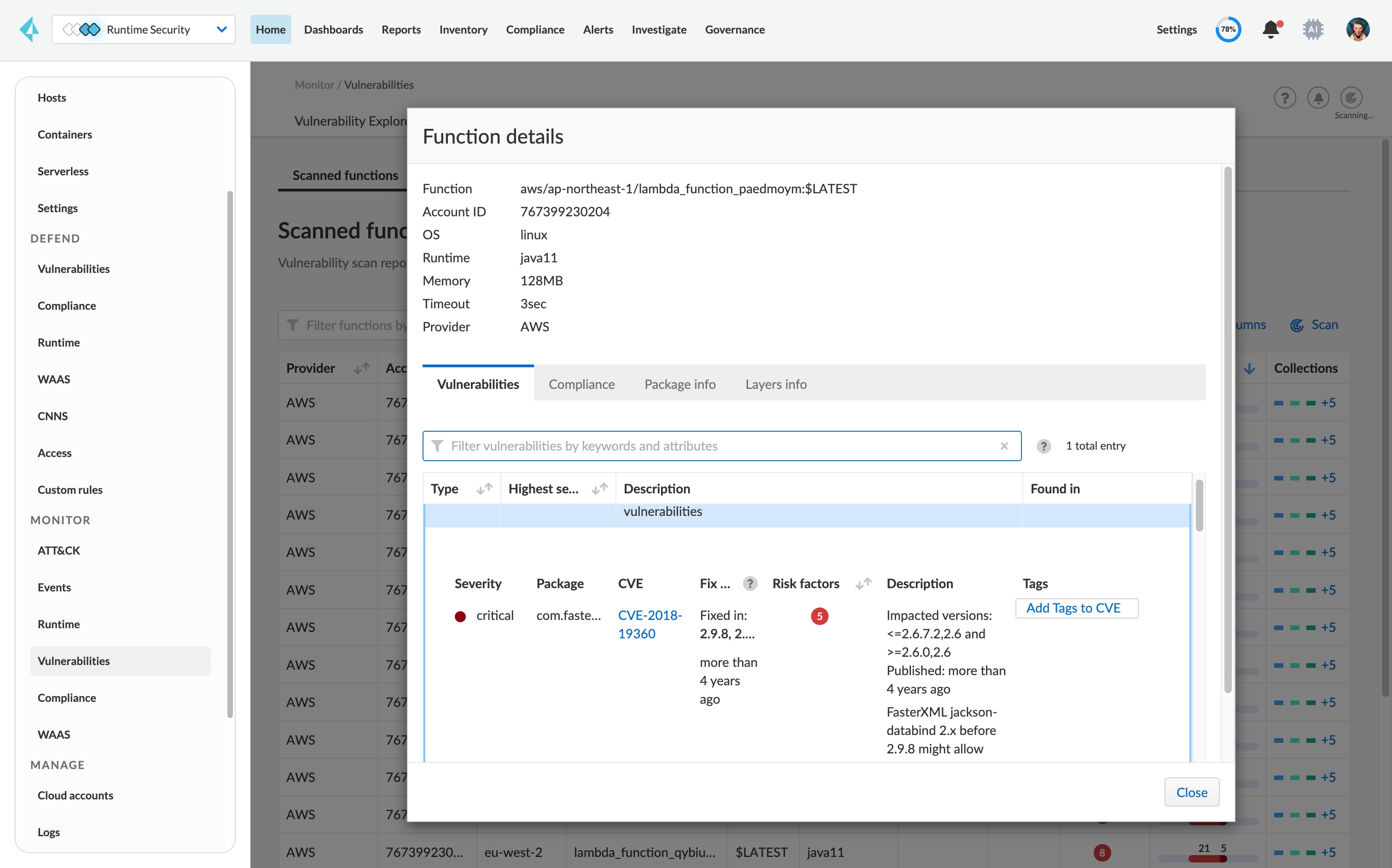
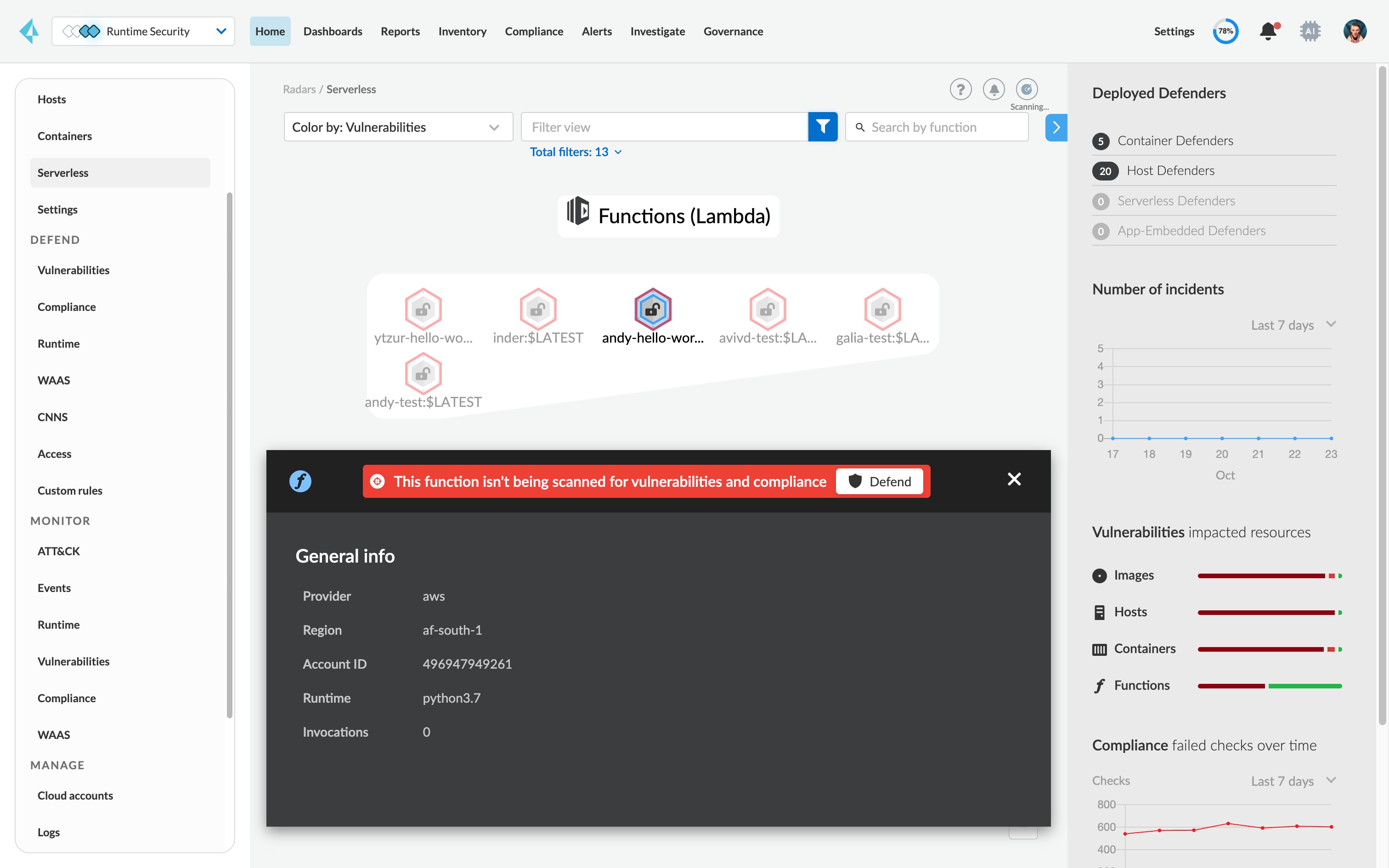
Securing functions begins with understanding and controlling the vulnerabilities in packages being deployed and running. Prisma Cloud scans and continuously monitors functions for vulnerabilities. Start with integrated CI tooling and serverless repositories, and continue through runtime for a full lifecycle view.
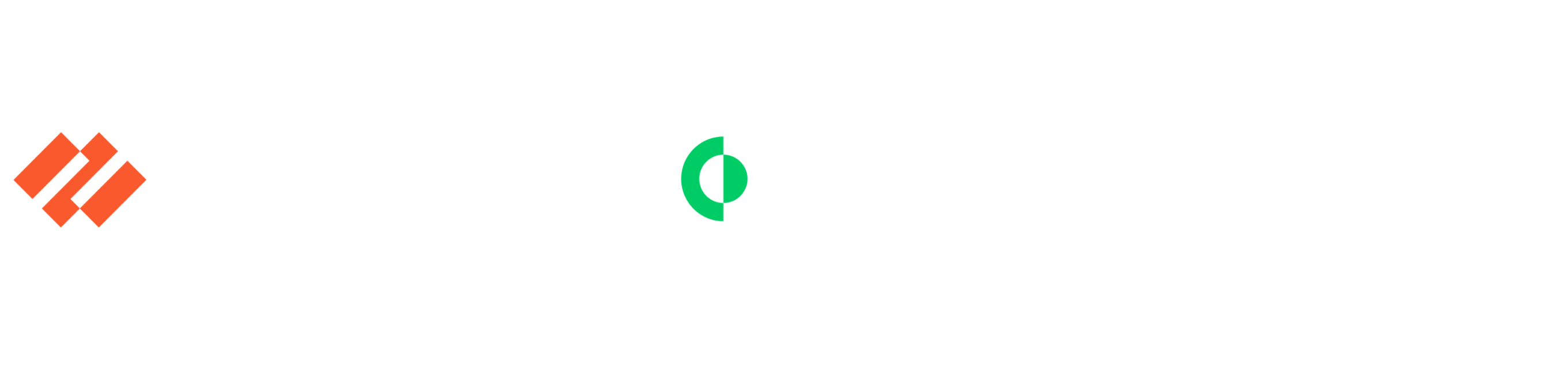
Prioritize top vulnerabilities across functions
Identify the highest priority vulnerabilities based on risk score and exposure across functions as well as Lambda Layers in your repository and runtime.
Leverage remediation guidance to patch quickly
Vulnerabilities identified include package information and fix guidance.
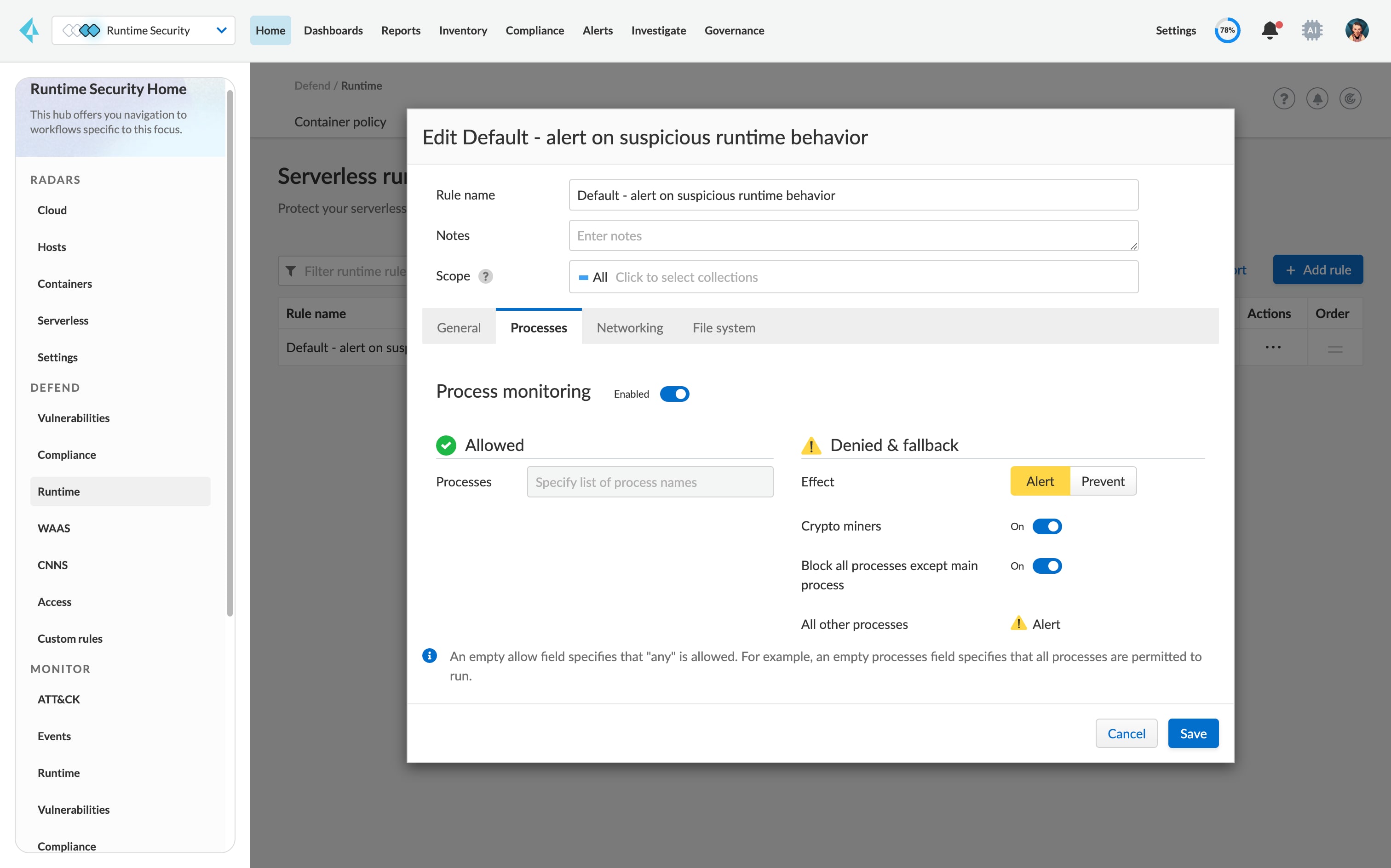
Block functions that fail risk level
Leverage CI integrations and runtime protections to fail builds and prevent deployments of functions with vulnerabilities that don’t meet your risk levels.
Continuously assess the posture of your repositories
Get an up-to-date overview of the vulnerabilities in your functions as Prisma Cloud continuously scans repositories against our vulnerability database.