Why does it seem so hard to consistently deploy secure application infrastructure in the public cloud? Gartner predicts that by 2025, 99% of cloud security breaches will be the customer’s fault. The majority of the problems stem from the insecure configuration of application infrastructure and vulnerabilities in container images.
These insecure configurations can range from setting a wrong access control list on an Amazon S3 bucket or deploying an Amazon Relational Database Service (RDS) instance that is not encrypted, to configuring a Kubernetes app manifest to spin up containers as root. In addition, many enterprises today use some sort of infrastructure as code (IaC) mechanism – Terraform, CloudFormation, Azure Resource Manager (ARM) templates or Kubernetes app manifests – to rapidly deploy resources to multiple cloud environments, which can create insecure configurations at scale if not validated before deployment.
Lastly, more applications are getting containerized and Kubernetes is becoming the de facto standard for container orchestration. The unfortunate result is container images full of vulnerabilities and Kubernetes manifests with overly-permissive container access – both of which can result in high-profile incidents.
Introducing Prisma Cloud DevOps Plugins
In order to prevent these security challenges, we are introducing a library of Prisma Cloud DevOps Plugins to detect insecure configurations in IaC templates and vulnerabilities in container images before resources get deployed in production:
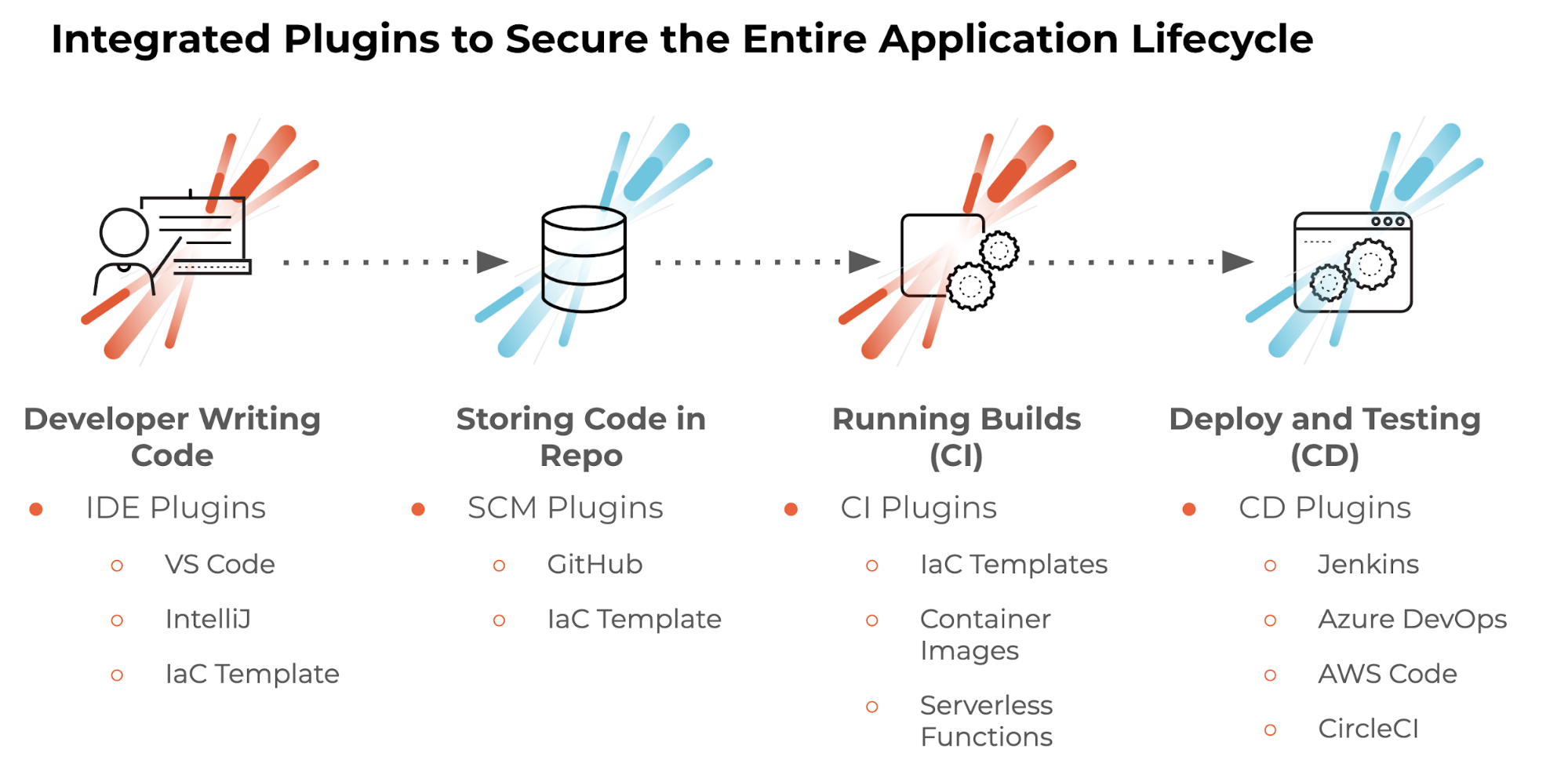
Code Development
When developers write IaC templates like Terraform templates (TFT), CloudFormation templates (CFT) and Kubernetes (K8s) manifests, they can use Prisma Cloud to check for security issues right inside their integrated development environment (IDE) using our native plugins. We are excited to announce plugins for both IntelliJ IDE and VS Code.
Checking Code into Repository
If a developer fails to correct security alerts in IDE and tries to merge insecure IaC templates (TFT, CFT, K8s manifests) into a source repository like GitHub, the native Prisma Cloud GitHub application can stop the pull request (PR) merge completely, and/or create a security issue against a developer who is trying to merge insecure code into your code repository. Prisma Cloud will check for security issues during any Git PR merge and give you the visibility and control needed to take action.
CI/CD Pipeline Security
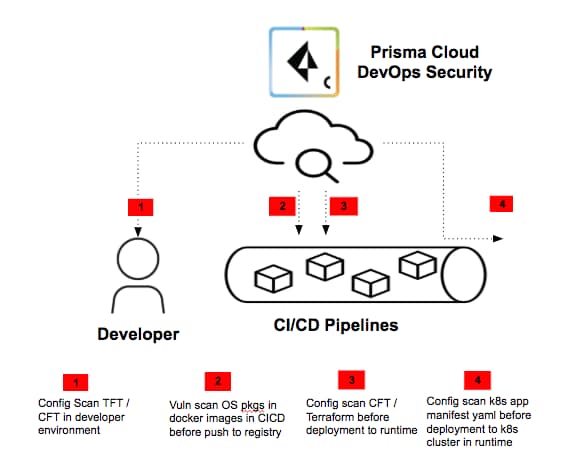
As DevOps pulls components from multiple repositories during the build/deploy time, the native Prisma Cloud CI/CD plugins can check for security issues during the build phase as well as at deployment time.
Our native CI/CD plugins can identify security issues in IaC templates and scan container images and serverless function zips to detect vulnerabilities. Users can even control when to fail a build or pipeline depending on defined failure criteria covering security policies and vulnerabilities severity and count. Today, Prisma Cloud supports native plugins for Jenkins, Azure DevOps, AWS Code and CircleCI, with more coming.
Cloud Agnostic
All Prisma Cloud DevOps Plugins use a default set of policies for IaC scans and support all three major clouds – Amazon Web Services (AWS), Microsoft Azure and Google Cloud Platform (GCP). We use our industry-leading Prisma Cloud threat and vulnerability database for matching vulnerabilities with container images and serverless functions. Each plugin mentioned above is available today on individual DevOps tools marketplaces (e.g. Prisma Cloud GitHub app is available on GitHub marketplace).
Prisma Cloud DevOps Plugins Documentation
We are actively developing additional plugins for more DevOps tools. Take a look at our documentation on these DevOps plugins for additional details on what’s currently available.