Using YARA to Automate Malware Identification and Classification in XSOAR
In the dynamic realm of cybersecurity, maintaining a proactive defense against evolving threats is non-negotiable. One potent weapon that has emerged as a linchpin in the defender's arsenal is YARA, a rule-based language and open-source tool tailored for identifying and classifying malware. In this discourse, we venture into the sphere of automating YARA within the Cortex XSOAR platform, unraveling how this integration can help your security team fortify their cybersecurity posture.
Understanding YARA rules
Rule-Based Mastery
At its core, YARA empowers cybersecurity professionals with the ability to create custom rules or signatures. These rules are crafted based on distinctive patterns, behaviors, or characteristics found within files, processes, or even network traffic.
Versatility in Application
YARA's strength lies in its versatility. It can be applied to a wide array of cybersecurity scenarios, from threat hunting and incident response to malware analysis. The tool provides a structured and efficient means to sift through the vast sea of digital data, honing in on potential threats.
Open Source Collaboration
Embracing an open-source ethos, YARA encourages collaboration within the cybersecurity community. Security researchers, analysts, and organizations converge to contribute to an expanding repository of YARA rules, forging a united front against the ceaseless evolution of the threat landscape.
The Role of YARA Rules in Cyber Defense
Tailored Threat Detection
YARA enables security analysts to create rules tailored to the specific attributes of known threats or vulnerabilities. This allows for precise detection and classification of malware, making it an indispensable asset in the fight against cyber adversaries.
Proactive Threat Hunting
With YARA, cybersecurity professionals can adopt a proactive approach to threat hunting. By continually refining and expanding rule sets, organizations can identify emerging threats before they escalate, reinforcing their proactive cybersecurity posture.
Embracing YARA Automation within XSOAR
Automating Yara Scanning for Incident Files
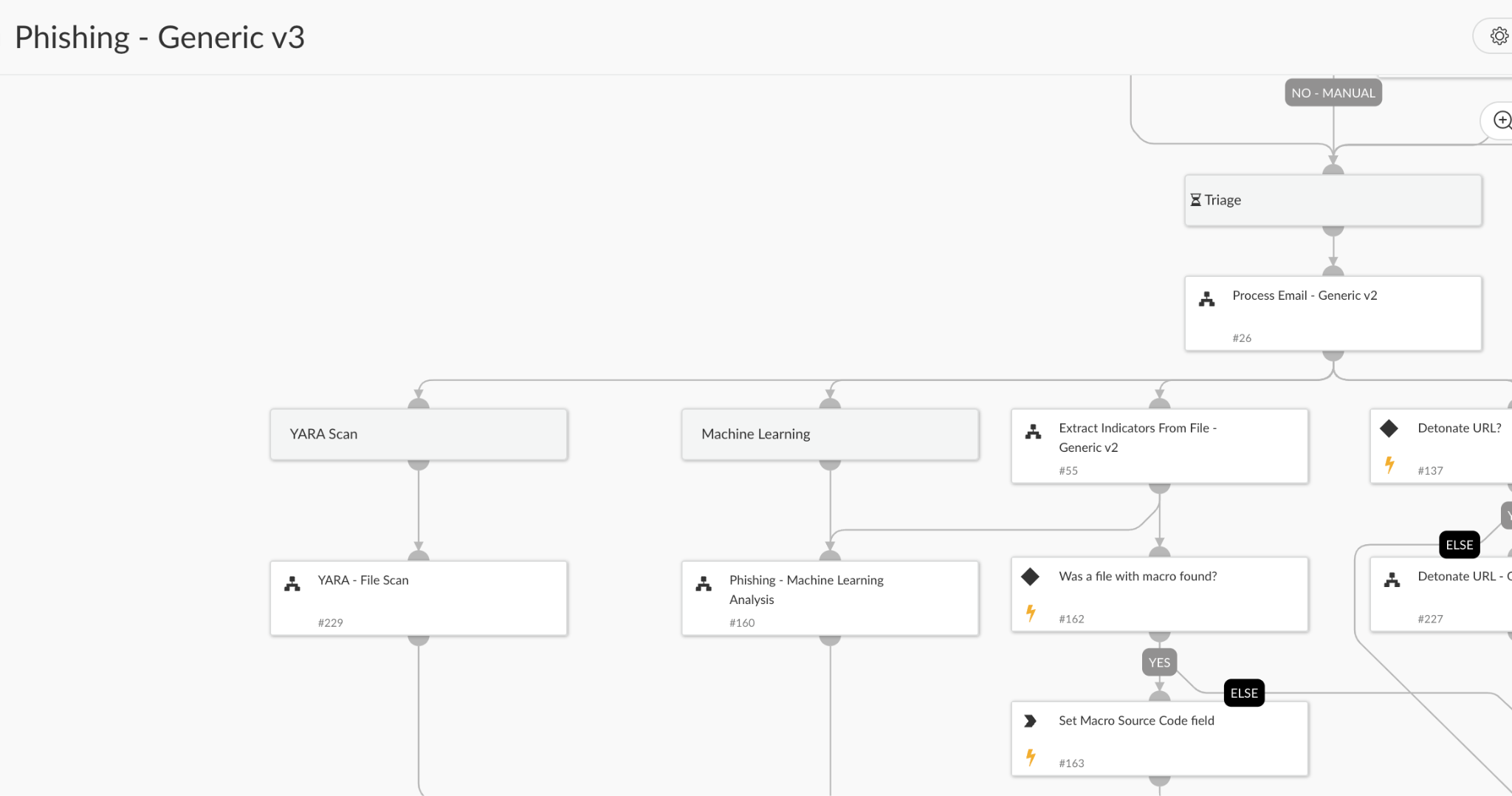
In the XSOAR platform, cybersecurity professionals can leverage the Yara - File Scan playbook to swiftly identify malicious artifacts. This playbook, when integrated into investigation and response playbooks, becomes a crucial asset in incident handling.
Imagine a phishing incident: By running a YARA scan automatically on an EML file, analysts can efficiently unearth popular strings associated with phishing emails. The YARA rule exemplifies a generic phishing email detection logic, showcasing YARA's adaptability to specific use cases.
Let's take the following Yara rule as an example:
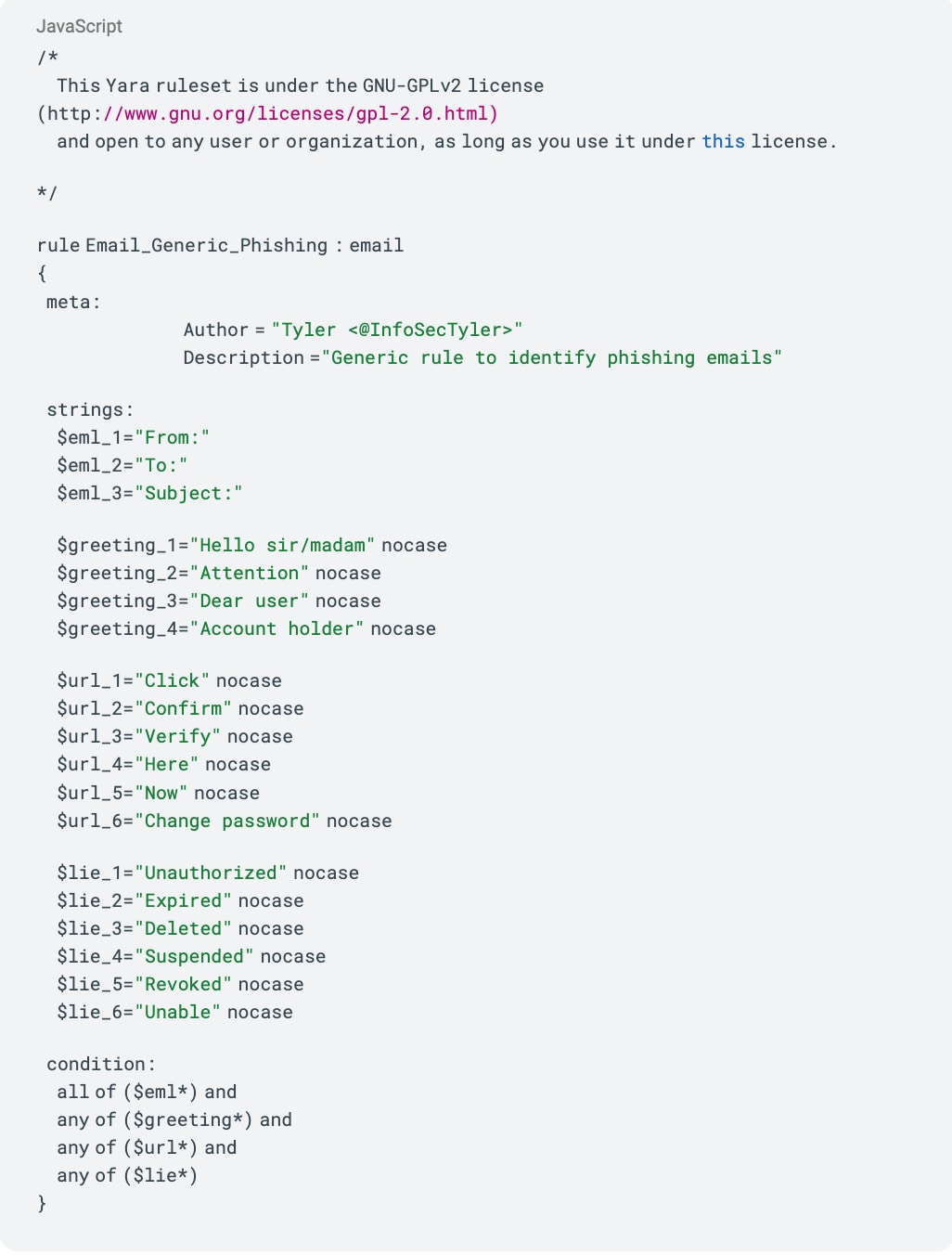
Source: https://github.com/Yara-Rules/rules/blob/master/email/Email_generic_phishing.yar
Installation and Configuration
Before delving into automation, ensure the YARA content pack is installed. Visit the Cortex Marketplace to download the pack.
Adding Yara Scan to the Phishing playbook
Now, we will want to add the Yara - File Scan playbook to our phishing playbook.
Note: If you are using the out-of-the-box phishing playbook, you will need to detach the playbook to add the Yara - File Scan playbook.
Open the playbook task, paste the phishing YARA rule content from the previous section in the ‘Yara’ input and save the playbook.
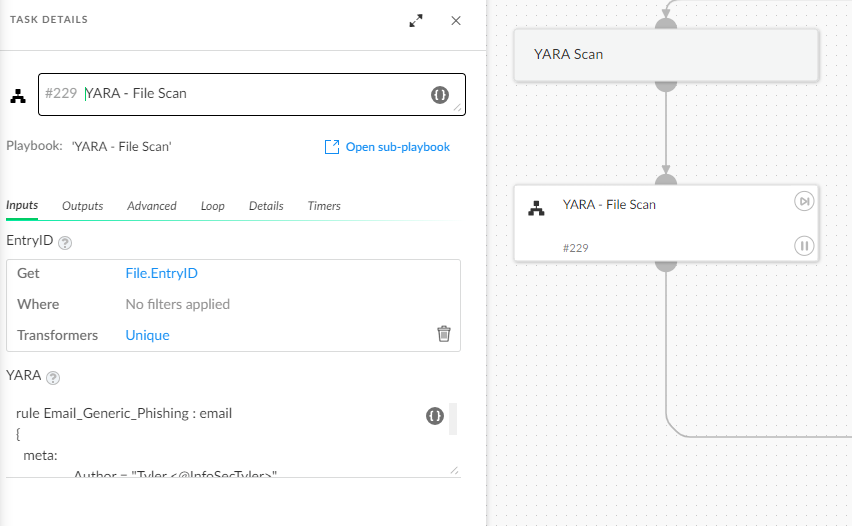
Now every phishing incident playbook triggered will run a YARA scan to help your analysts conduct better and faster incident triage.
Conclusion
In the dynamic landscape of cybersecurity, where adaptability is the linchpin of defense, automating YARA through XSOAR emerges as a stalwart guardian. As organizations strategically prioritize their cybersecurity frameworks, the seamless integration of YARA automation into their defensive arsenal signifies a resilient stance in the face of an ever-evolving digital battlefield.
So, take the first step today by checking out the pack in the Cortex Marketplace. Also explore the Phishing pack capabilities, experiment with the automations embedded in the playbooks, and experience it transforming your SOC into a more dynamic, responsive, and effective unit.
To learn more about how you can automate security operations with Cortex XSOAR, check out our virtual self-guided XSOAR Product Tour
We also host virtual and in-person events, so check here for upcoming ones.