Introduction
Remote Desktop Protocol (RDP) is a widely used technology that allows users to remotely access and control computers and servers over a network connection. It is commonly used by organizations for various purposes, such as remote administration, technical support, and telecommuting.
However, the convenience of RDP also comes with potential risks. RDP has been a common target for cybercriminals who exploit vulnerabilities, weak authentication, or misconfigurations to gain unauthorized access to systems. And according to the Unit 42 Cloud Threat Report, 73% of organizations have RDP exposed to the public internet.
What is RDP brute force?
RDP brute force refers to a type of cyberattack in which an attacker systematically attempts to gain unauthorized access to a network by repeatedly guessing or "brute forcing" the password of an RDP account.
RDP brute force attacks can be carried out by malicious actors with various motivations, including stealing sensitive data, gaining control of a system for further exploitation, or causing disruption to the targeted network or system. These attacks can be particularly effective if the passwords used are weak or easily guessed.
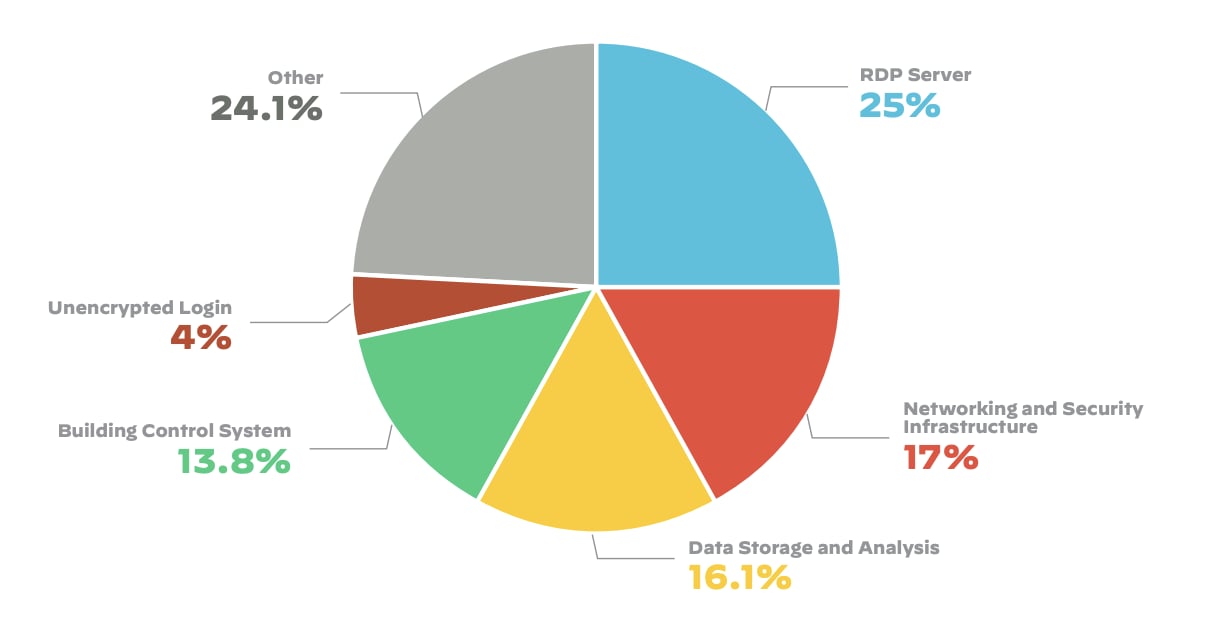
“Nearly one out of every four issues we found on the attack surface was related to an exposed RDP server” - 2022 Attack Surface Threat Report
Why is it important to efficiently detect and respond to RDP brute force alerts?
A successful RDP brute force attack may be the last step before the attacker moves laterally in the network and achieves his final goal, so it is important to quickly and efficiently detect, investigate, and respond to RDP brute force alerts.
Unit 42 research shows that services exposed to the internet are often scanned and targeted opportunistically by attackers.
Investigate and respond to external RDP brute force alerts using XSOAR
The Cortex XDR - Possible External RDP Brute-Force content pack was designed to automate the incident investigation and response process and help SOC teams speed up response.
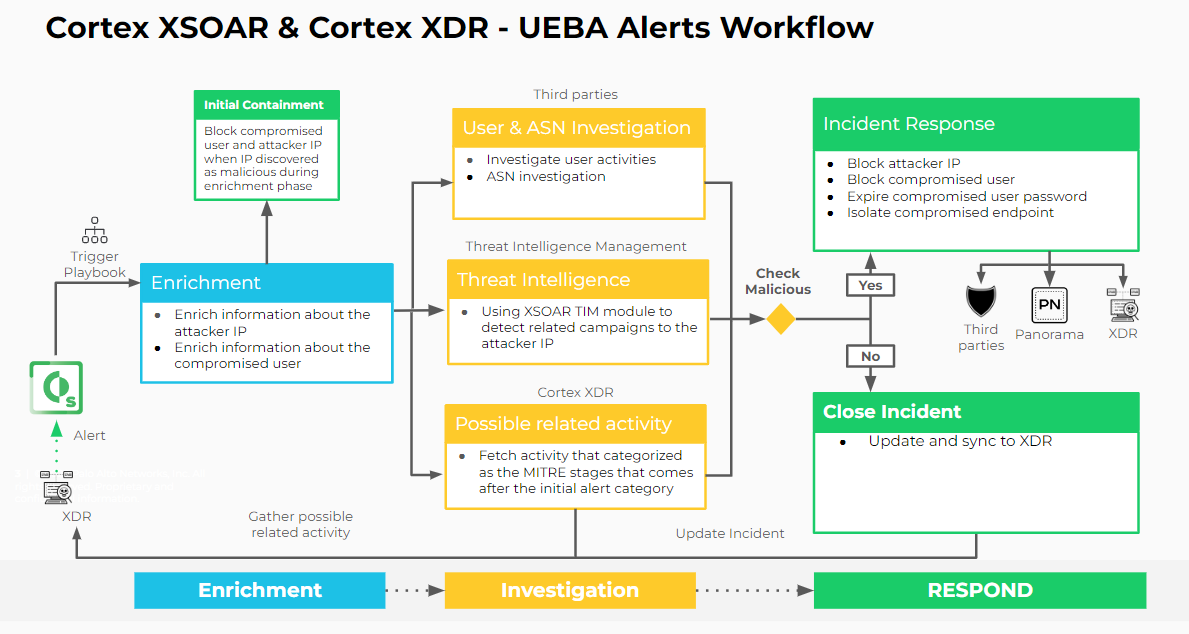
Let’s drill-down on each of the key incident response areas of indicator enrichment, threat hunting, and remediation and how our content pack can be used to automate and speed up the incident response process.
Key Playbook Automations
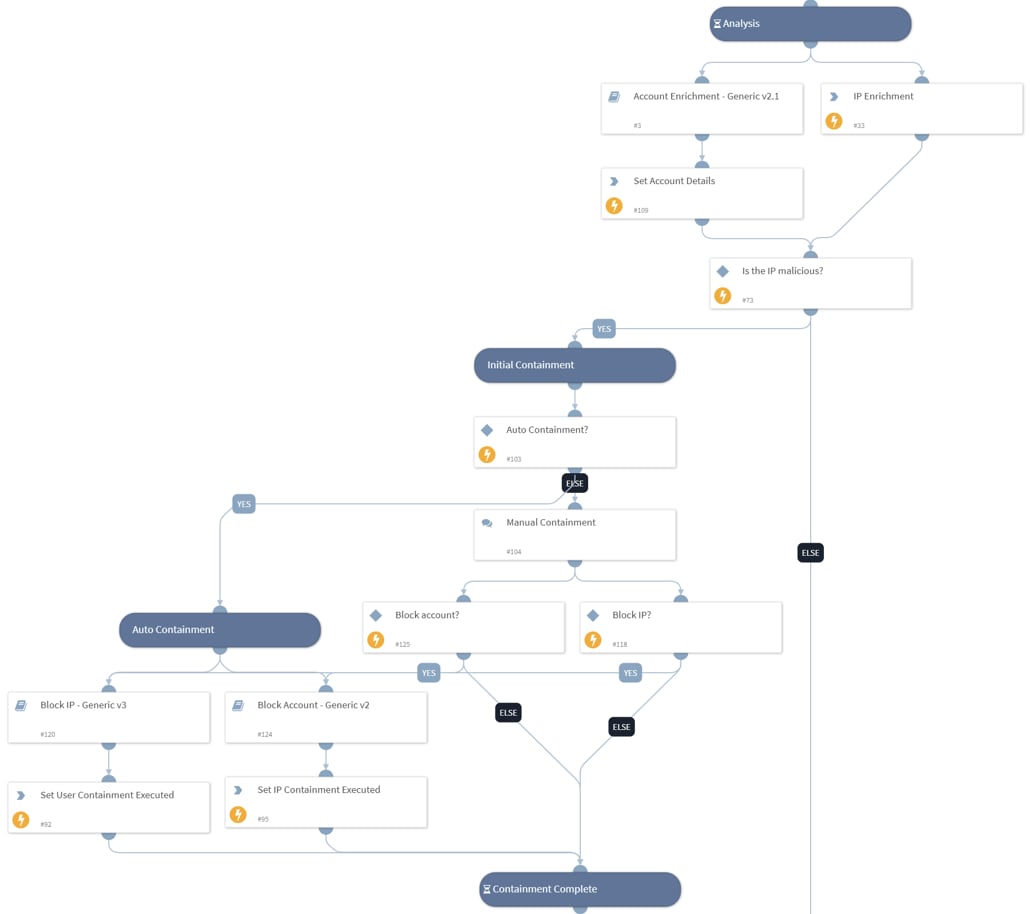
Indicator Enrichment
Enriches information on IP addresses for both compromised users and attackers. Cortex XSOAR will automatically gather the following information:
- IP data and reputation from all available and configured IP enrichment sources.
- User information from internal user management ecosystems.
If the attacker’s IP is detected as known malicious IP, XSOAR will execute an initial automated, or semi-automated, response action that includes blocking the attacker’s IP and disabling the compromised user.
Threat Hunting and Investigation
The next steps include performing an automated deep dive investigation and exploring the following investigation criteria:
- Get threat intelligence insights from XSOAR Threat Intelligence Management (TIM) module using TIM - Indicator Relationships Analysis sub-playbook that will raise a flag if the attacker’s IP address is found to be related to a specific campaign reported by a threat intel feed. The sub-playbook will also provide IOCs that are related to the attacker’s IP or campaign.
- Search for connection anomalies using User Investigation - Generic sub-playbook to raise a flag in case that the RDP connection attempt is made from an unusual country for the user.
- Search for XDR alerts that are related to the compromised user and the compromised endpoint within the same timeline as the RDP Brute Force alert, which could indicate follow-up malicious activity based on the following MITRE ATT&CK tactics:
- Persistence (TA0003)
- Discovery (TA0007)
- Lateral Movement (TA0008)
- Collection (TA0009)
- Command and Control (TA0011)
- Impact (TA0040)
- Hunt for IOCs that are related to the same campaign as the attacker’s IP using Threat Hunting - Generic sub-playbook. A flag will be raised in case that results were found.
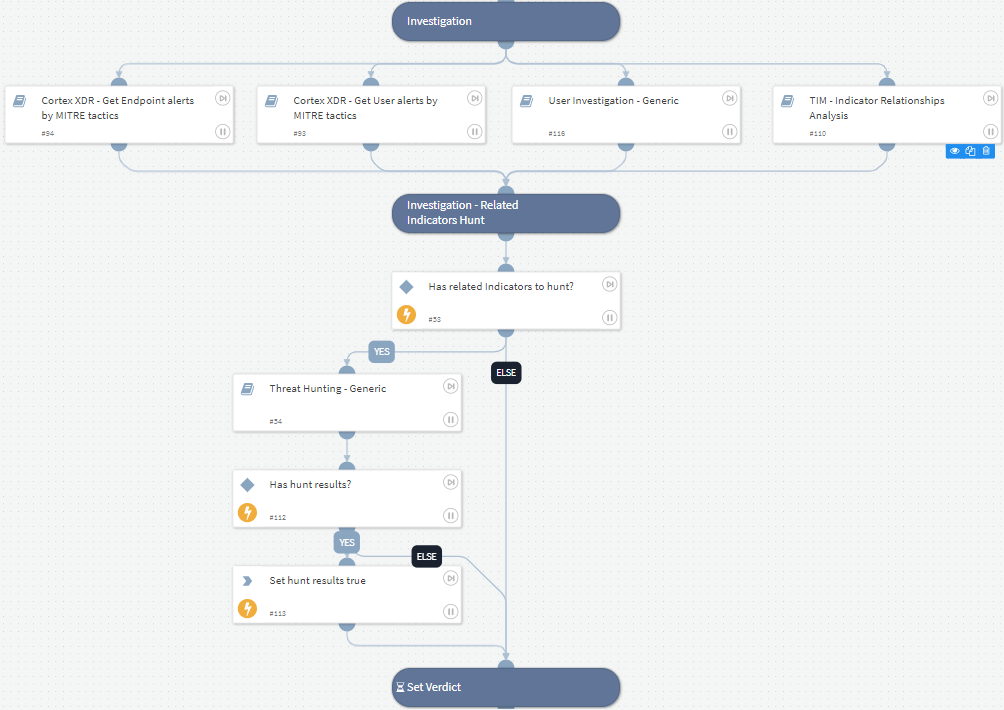
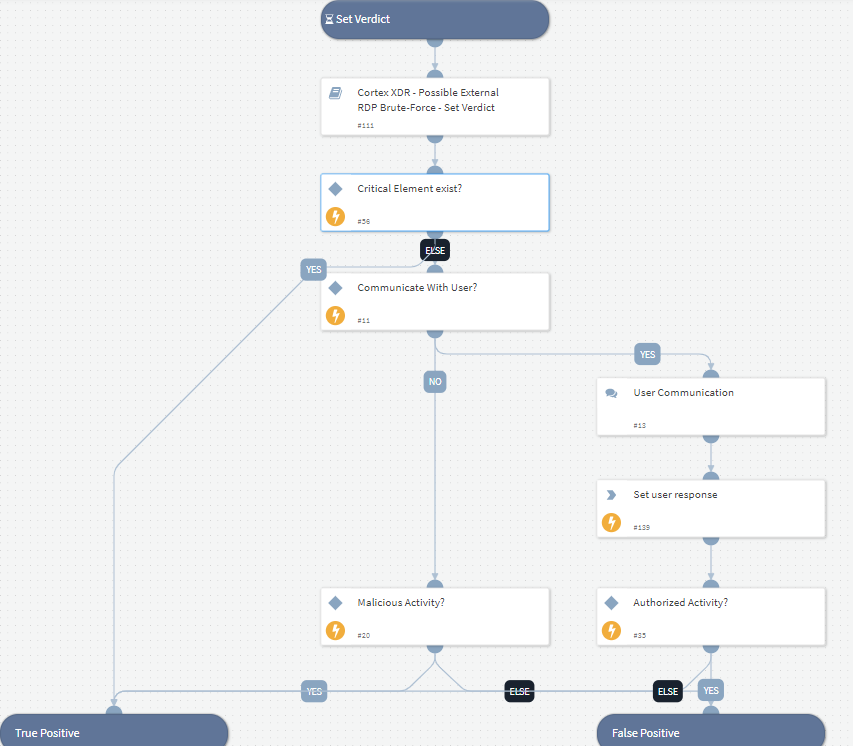
Set Incident Verdict
There are three key factors used in the playbook to determine whether the incident is malicious, with the verdict presented to the analyst in our incident layout window:
- Count of investigation criteria that are suspicious, as compared to threshold set by the user.
- Critical criteria - Analysts can select a specific investigation criteria that, if identified as suspicious, will deem the investigation’s final verdict as malicious.
- User Engagement - Analysts can set the number of suspicious investigation criteria that will trigger user engagement. When this threshold is met, an email will be sent to the user and their manager asking for authorization of RDP activity. If the RDP activity is not authorized by the user, the final verdict is deemed malicious.
Response Actions
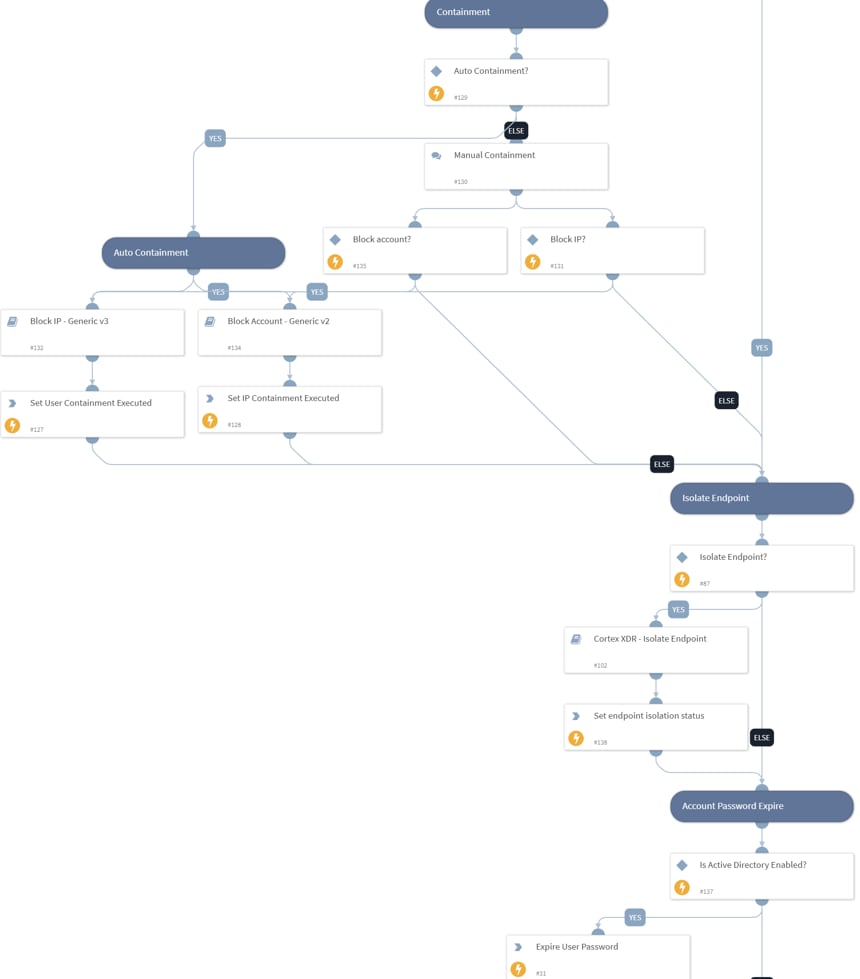
When the final verdict is determined to be malicious, XSOAR will initiate the following automated/semi-automated response procedures:
- Block the attacker’s IP using “Block IP - Generic v3” sub-playbook.
- Disable the compromised account using “Block Account - Generic v2” sub-playbook.
- Expire compromised user password.
- Isolate endpoint using Cortex XDR - can be enabled by the user using playbook inputs.
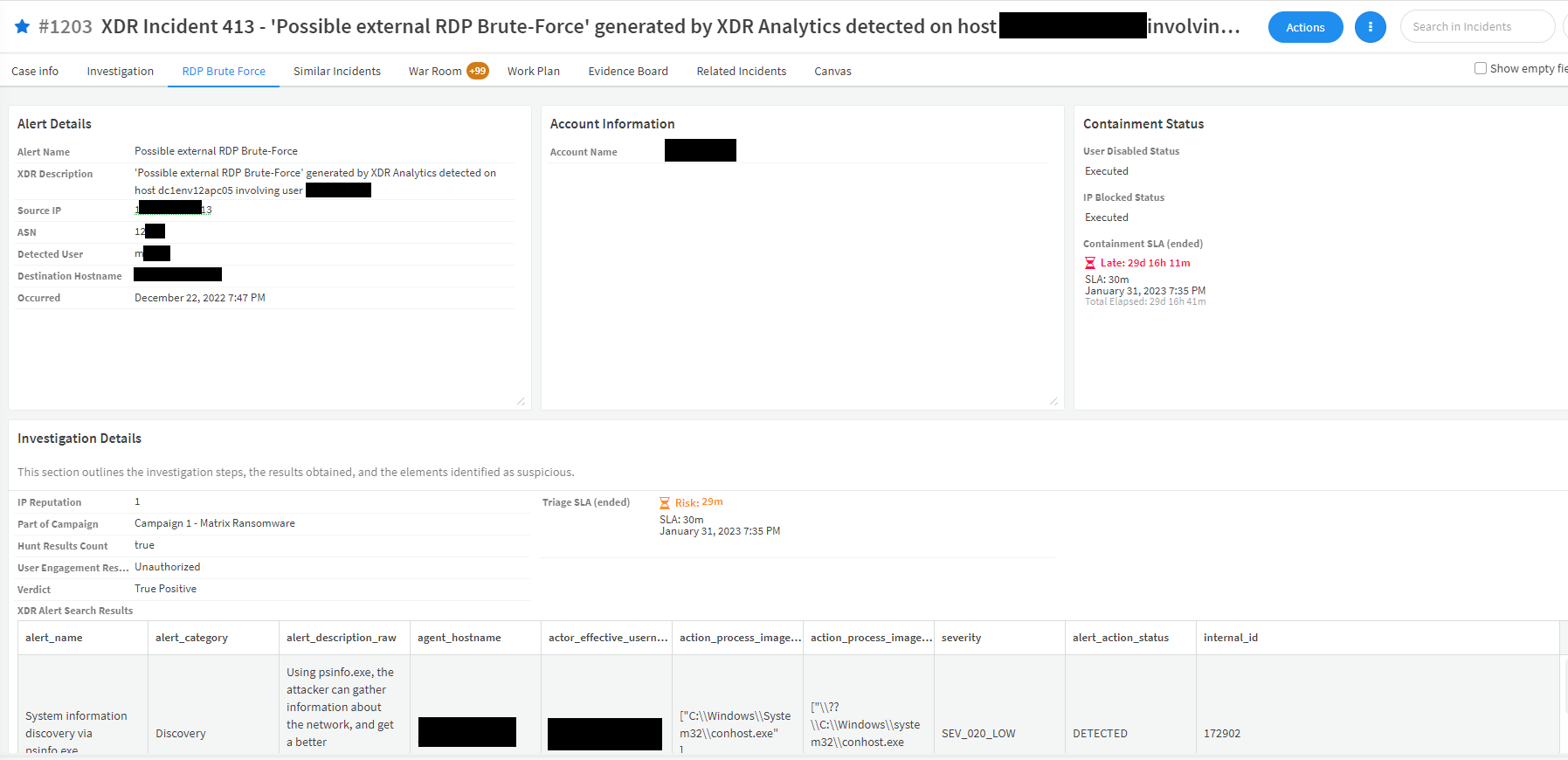
Incident Window for Analyst Review
Once a Cortex XDR incident contains “Possible External RDP Brute-Force” alert is ingested, a new tab will be created under the “Cortex XDR Incident” layout that contains the RDP Brute Force investigation details. The layout tab contains the following:
- Alert details
- Account information
- Containment status
- Investigation details
In conclusion
A well-defined playbook for investigating and responding to RDP brute force alerts is crucial for safeguarding your systems. Stay vigilant, proactive, and prepared, and regularly update your playbook to stay ahead of evolving threats. With a coordinated response and strong security measures in place, you can effectively defend against RDP brute force attacks and protect your organization's critical assets.
For more information on this pack and other automation use cases, visit our Cortex Marketplace.
To learn more about how you can automate security operations with Cortex XSOAR, check out our virtual self-guided XSOAR Product Tour
We also host virtual and in-person events, so check here for upcoming ones.