In today's increasingly complex digital landscape, user and entity behavior analytics (UEBA) has emerged as a crucial tool for organizations looking to enhance their cybersecurity capabilities. UEBA allows organizations to monitor and analyze user and entity activity within their network, and detect suspicious behavior that could indicate a potential cyber attack. One specific type of threat that UEBA can help detect is the first single sign on (SSO) access from a new Autonomous System Number (ASN) or from a new country. With SSO, users sign in once to gain access to multiple applications or services.
Attackers often use this method to gain unauthorized access to an organization's network, which can have significant consequences for the organization's security and reputation.
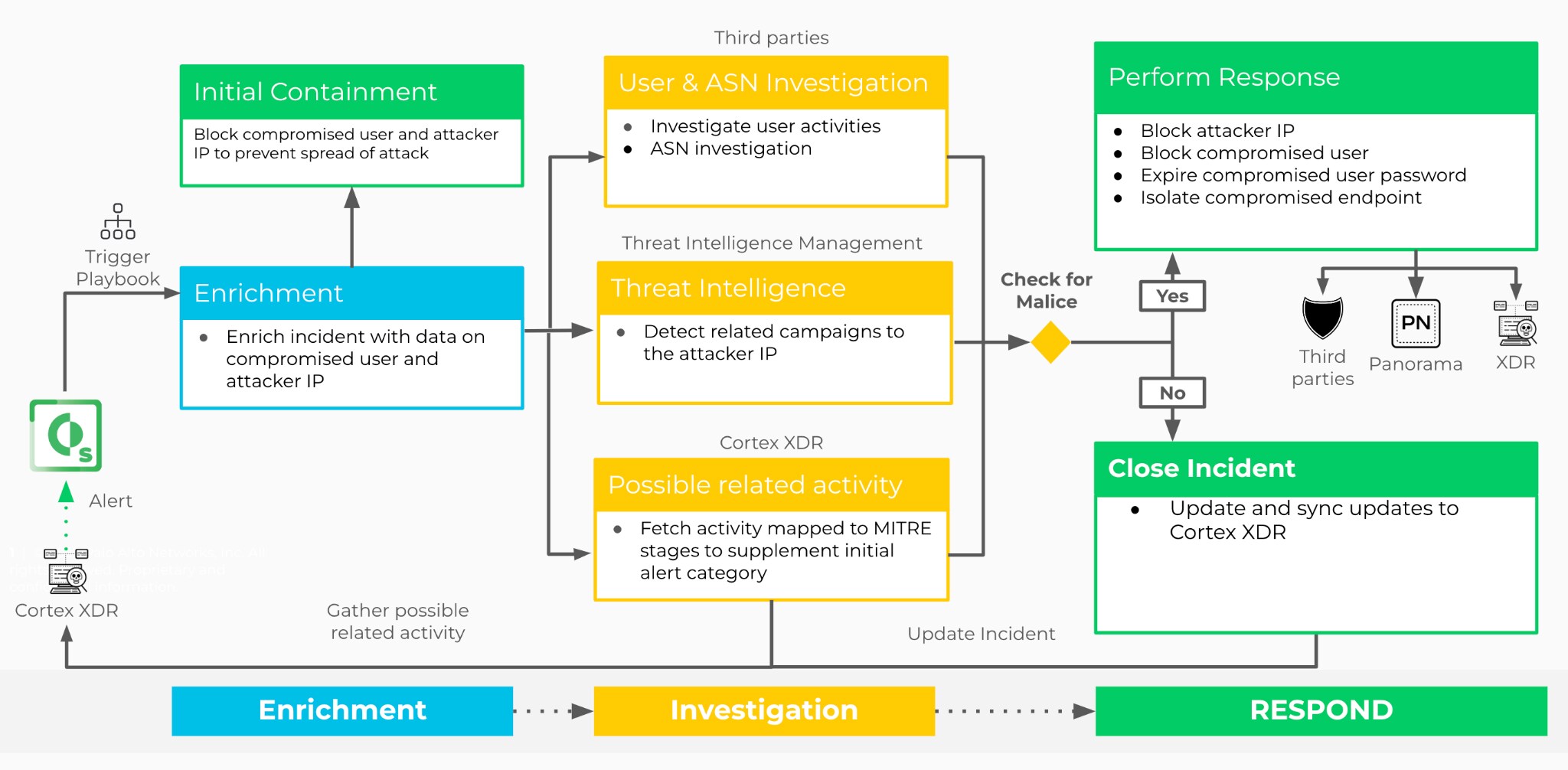
With the Cortex XDR - First SSO Access playbook, enrichment, investigation, and response can be fully automated to handle these alerts:
- First SSO access from ASN in the organization.
- First SSO connection from a country in the organization.
What Does the Playbook Do?
Indicator Enrichment
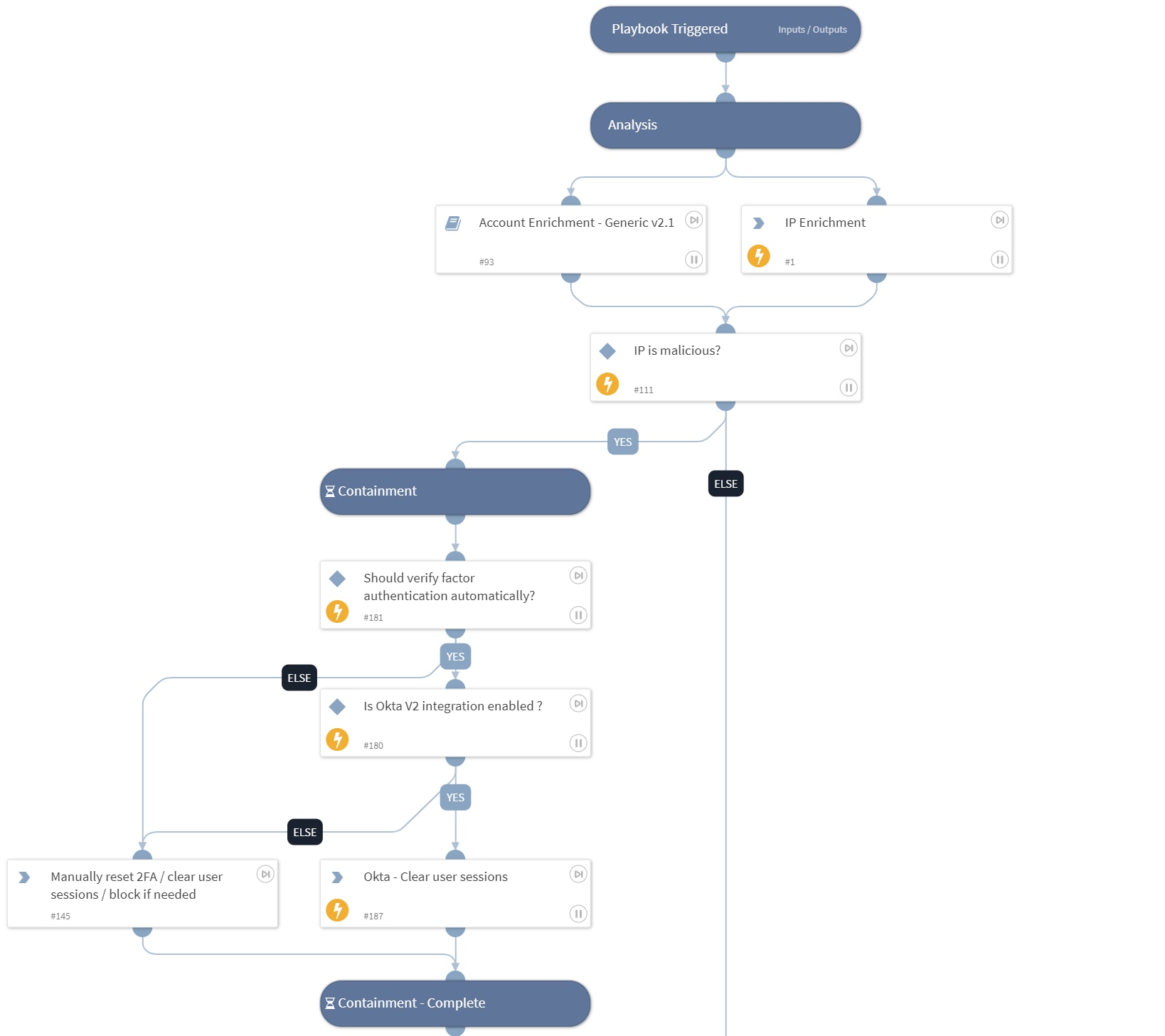
The first stage of the playbook includes critical steps for identifying and addressing potential threats. To achieve this, the playbook performs indicator enrichment to gather information related to the IP address associated with a potential threat. Data and reputation information is gathered from all available and configured IP enrichment sources. Additionally, the playbook enriches the information on the user by gathering data from all available and configured internal user management systems.
Initial Containment
Based on the IP reputation score, XSOAR will execute an initial automated, or semi-automated response by clearing all sessions associated with the compromised user, and require the user to re-authenticate using multi-factor authentication.
Investigation
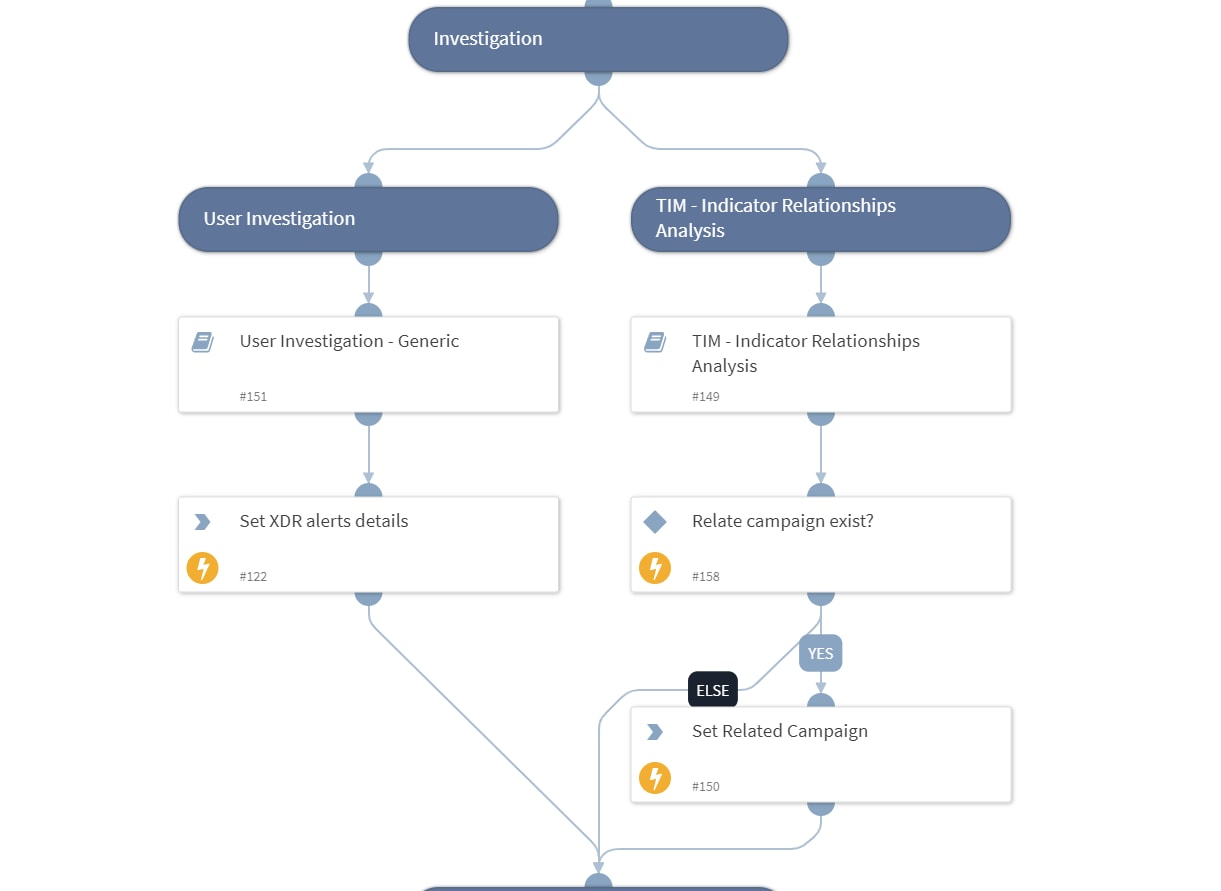
The next stage includes performing an investigation and exploring the following investigation criteria:
- Use the User Investigation - Generic sub-playbook to provide a comprehensive view of the potential threat by searching for:
- Suspicious user activities using SIEM and Okta queries
- Related alerts and user activities based on MITRE ATT&CK tactics via the XDR integration
- Use the TIM - Indicator Relationships Analysis sub-playbook to check insights and identify any indicators of compromise (IOCs) from threat feeds, and to provide notice in case there are related TIM campaigns associated with the user’s IP address.
Verdict Decision
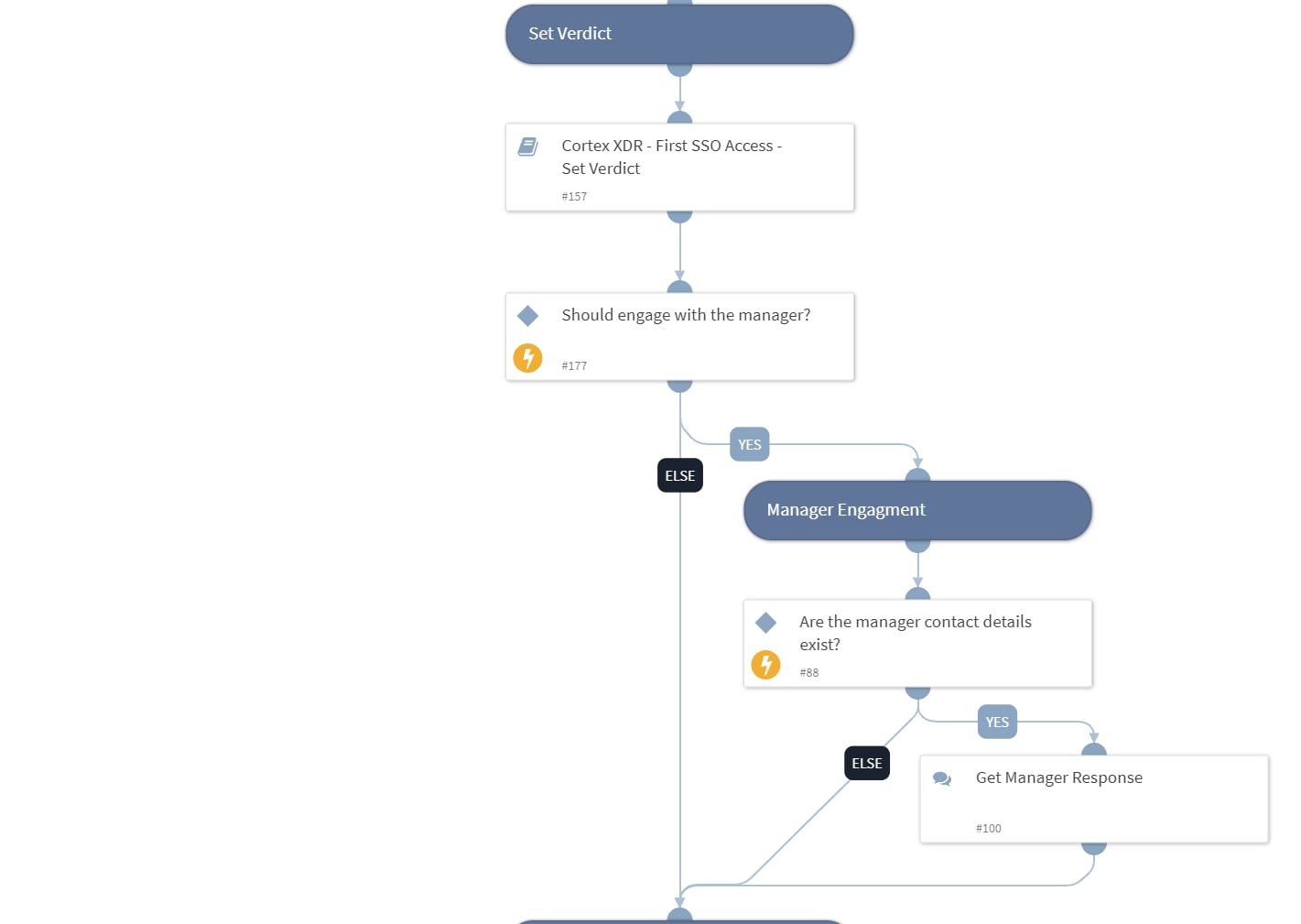
The next stage is to set the alert’s verdict using the Cortex XDR - First SSO Access - Set Verdict sub-playbook to perform various checks based on the enrichment and investigation data.
The verdict is set according to the number of positive results from these checks. The threshold for the number of positive results can be adjusted by changing the threshold value of the playbook’s input.
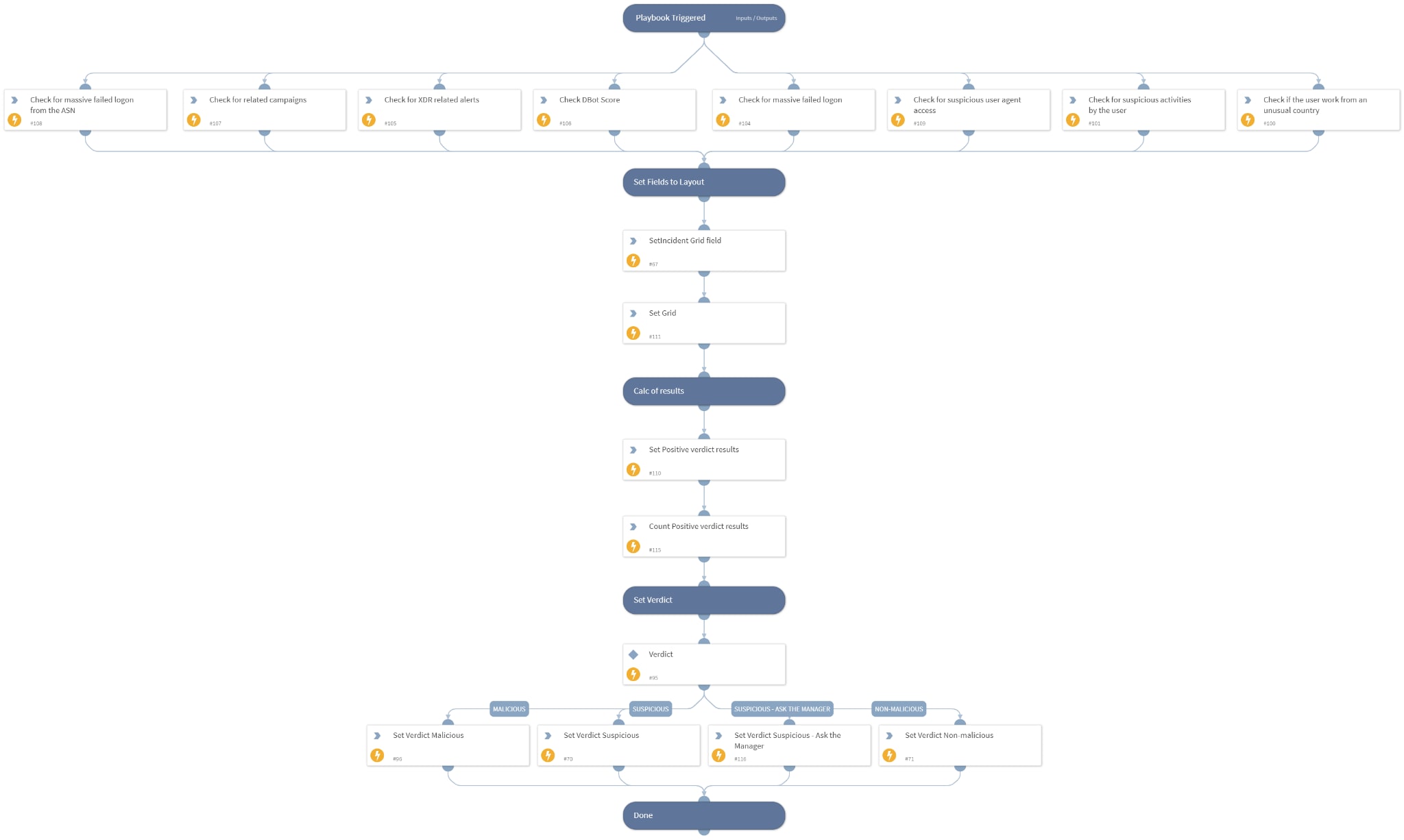
Verdict Resolution
If the verdict is determined to be non-malicious, the incident will be considered a false positive and subsequently closed. If the verdict is determined to be suspicious, it will require manual intervention by an analyst. Additionally, there is an option to automatically request confirmation from the user's manager regarding any suspicious activities, such as verifying if it's reasonable for the user to connect from a specific country. The manager's confirmation can aid the analyst in determining whether the incident is a true or false positive.
If the verdict is determined to be malicious, the next stage will involve performing response actions.
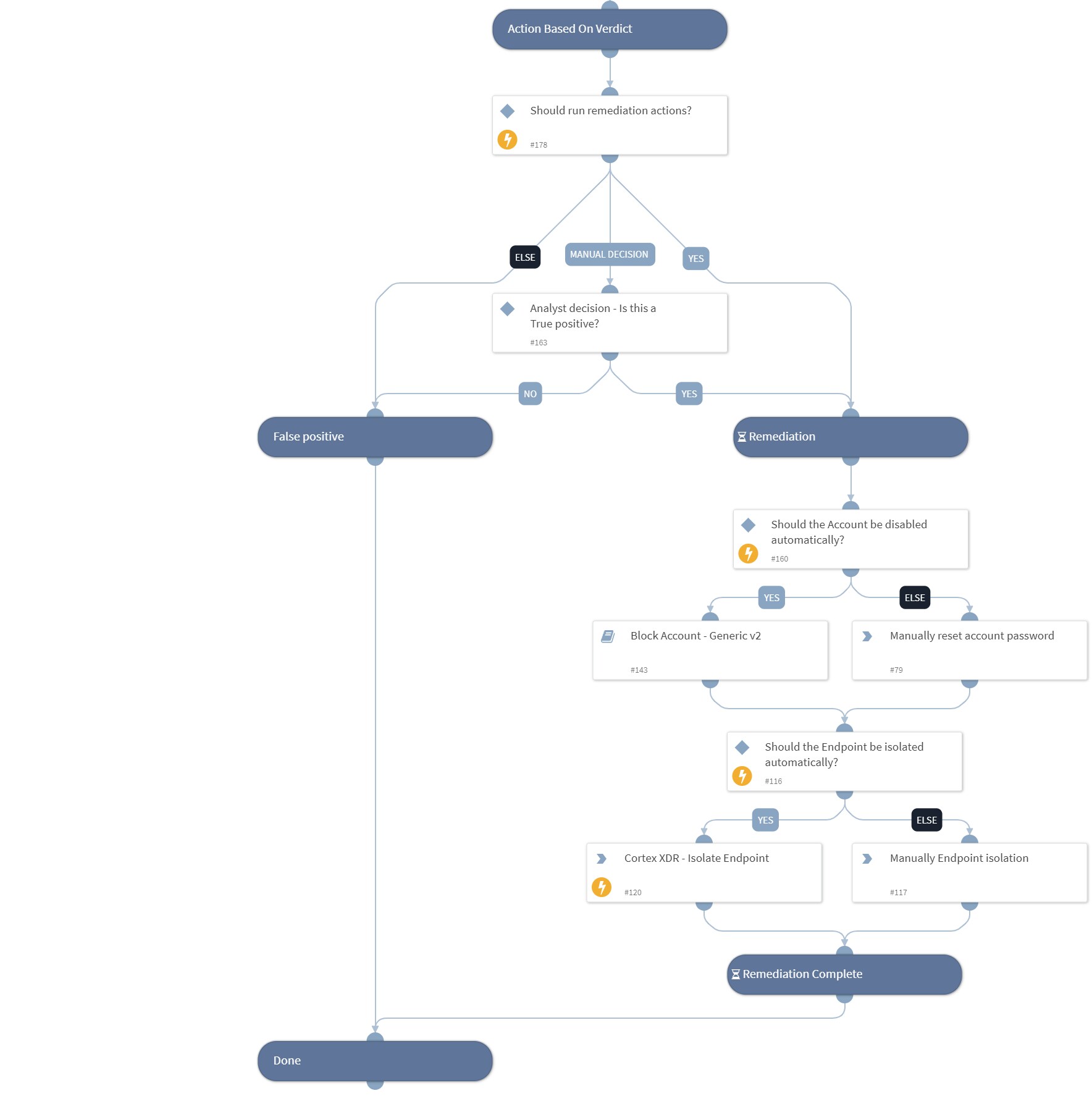
Response Actions
When the final verdict is determined to be malicious, the playbook will initiate the following automated or semi-automated response procedures:
- Block the compromised account using the “Block Account - Generic v2” sub-playbook
- Manually reset the account password.
- Isolate endpoints using Cortex XDR - If there is a Cortex XDR Agent on the endpoint
- Manually isolate the impacted endpoint.
The Layout
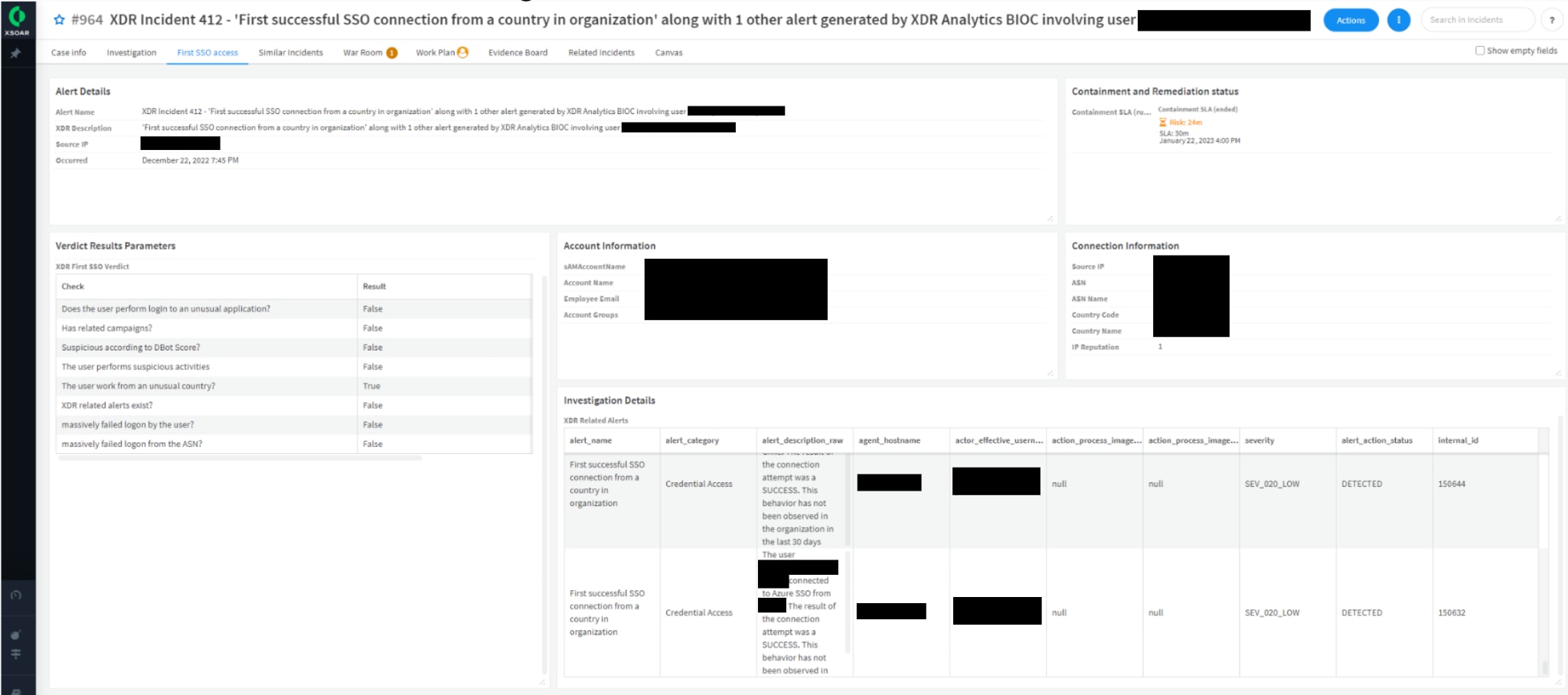
The layout created for this alert provides detailed incident views to aid analysts in furthering their investigation. The layout tab contains the following useful information:
- Alert details
- Containment status
- Account information
- Connection information including country and ASN of login
- Investigation details including XDR related alerts
- Account information
- Containment status
- Verdict results parameters - include the final verdict and the outcomes of all checks conducted to set the verdict
Conclusion
It is essential to monitor and respond to UEBA alerts in your organization. Using the Cortex XDR - First SSO Access playbook decreases the response time and improves the effectiveness of security operations for these use cases. This playbook is part of the Cortex XDR content pack.
Learn More
To learn more about how you can automate security operations with Cortex XSOAR, check out our virtual self-guided XSOAR Product Tour
We also host virtual and in-person events, so check here for upcoming ones.