- Best Rapid7 Competitors & Alternatives
-
What Is Security Operations (SecOps)? Comprehensive Guide
- Security Operations (SecOps) Explained
- The Pillars of Modern SecOps: People, Process, and Technology
- Example Scenario: Incident Response to a Malware Alert
- Proactive Security Operations Examples
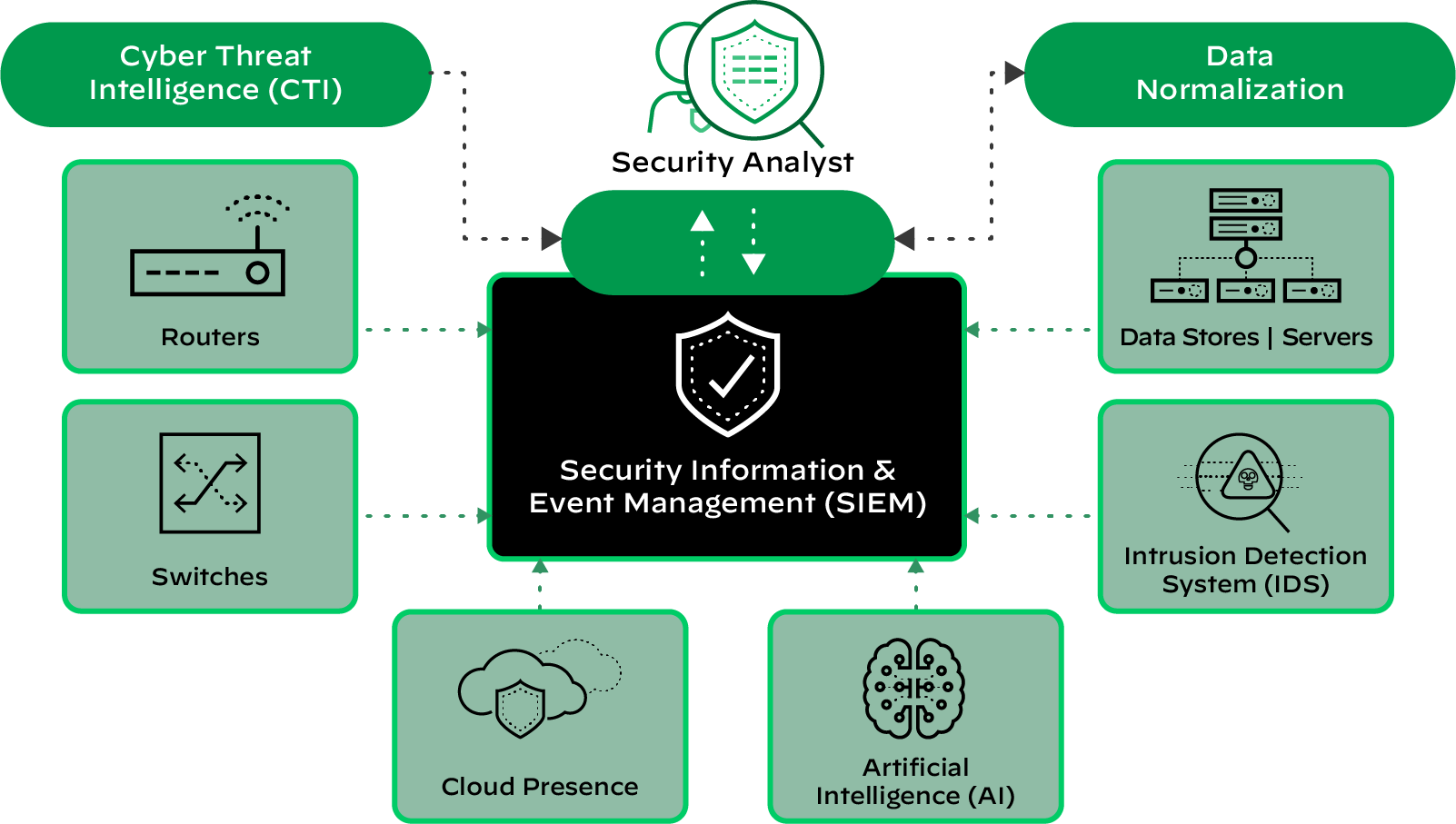
- Technology: Core Tools for the SOC
- Core Components and Functions of the SOC
- SecOps vs. DevOps vs. DevSecOps
- Security Operations FAQs
- Agentic AI Security Solutions: Top 7 Platforms Compared
- Best Sumo Logic Competitors & Alternatives for 2026
- Best SOAR Tools for 2026: Compare 10 Leading Platforms
-
Mastering MTTR: A Strategic Imperative for Leadership
- Beyond "Repair": Other Meanings of MTTR
- Why Is MTTR Important for Cybersecurity?
- Understanding Key Cybersecurity Incident Metrics
- Key Components That Influence MTTR
- How to Measure MTTR Accurately
- MTTR Industry Benchmarks and Defining 'Good' Performance
- Tactics That Effectively Reduce Cybersecurity MTTR
- MTTR in Cloud and Hybrid Environments
- Executive-Level Reporting of MTTR
- Future of Cybersecurity MTTR
- Frequently Asked Questions
- What Is Observability?
- What Is a Security Operations Center (SOC)?
-
How Do I Deploy SecOps Automation?
- Preparing for SecOps Automation
- Start Simple with High-Impact Tasks
- Automation Benefits for Organizations of All Sizes
- Peer Review and Approval
- Secure a Champion for Automation
- Defining Automation Use Cases
- Example Use Cases: Phishing and Malware
- Selecting the Right SOAR Platform
- SOAR Deployment and Use Cases FAQs
- What is SOC as a Service (SOCaaS)?
- How Do I Improve SOC Effectiveness?
-
How AI-Driven SOC Solutions Transform Cybersecurity: Cortex XSIAM
- How Cortex XSIAM 2.0 Revolutionizes Security Operations
- Cortex XSIAM Solutions and Advantages
- Addressing Critical Issues in Current SOC Solutions
- How Cortex XSIAM Transforms the SOC
- Distinctive Features of Cortex XSIAM
- Comprehensive SOC Solutions: Single Platform Delivery Highlights
- Integrated Capabilities: The XSIAM Solutions Delivery
- Ready to Transform Your Cybersecurity Landscape?
Security Operations Center (SOC) Roles and Responsibilities
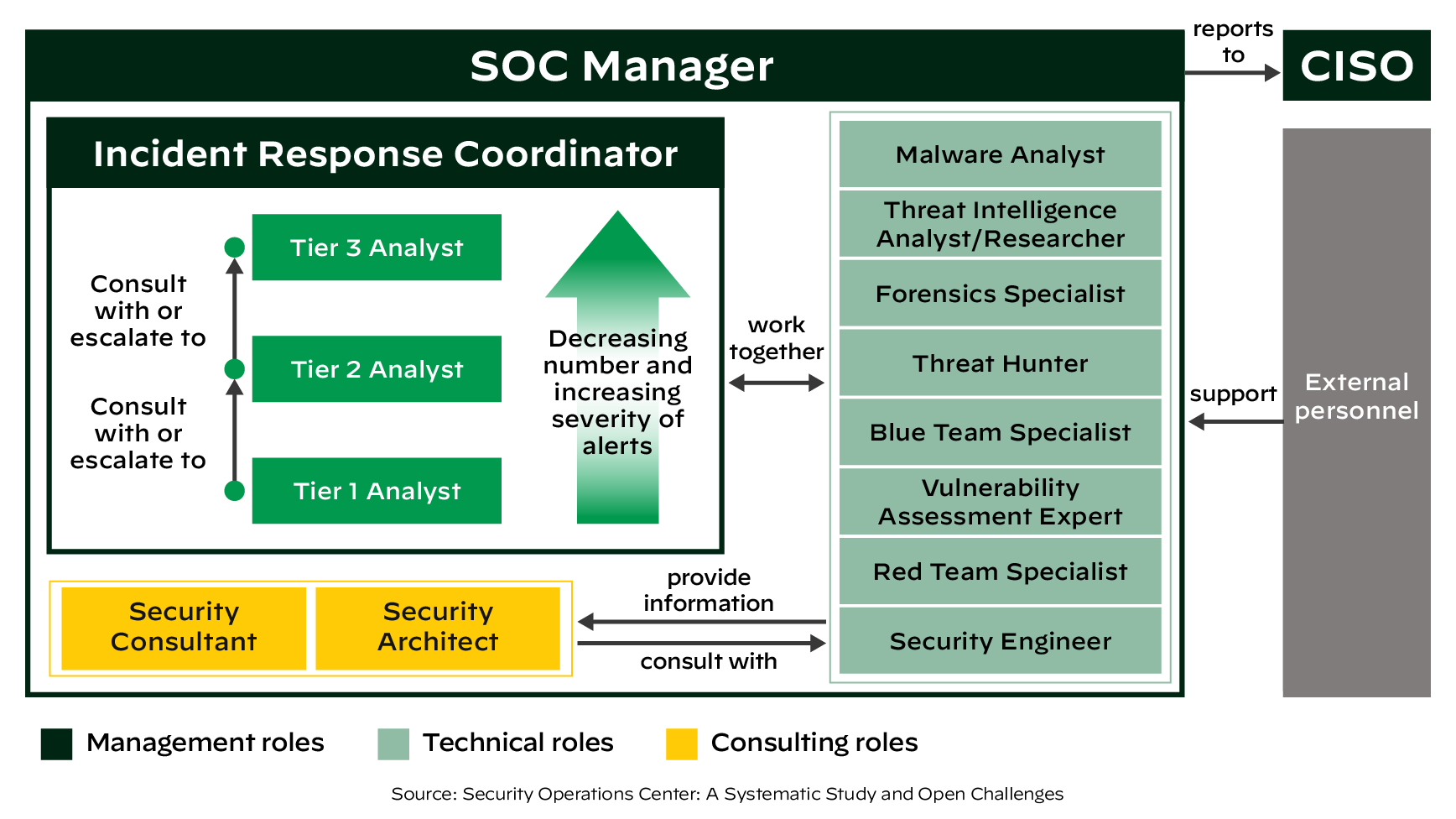
A security operations center, or SOC, is an organizational or business unit operating at the center of security operations to manage and improve an organization’s overall security posture. Its primary function is to detect, analyze and respond to cybersecurity events, including threats and incidents, employing people, processes and technology. Teams are responsible for managing security infrastructure and configuring and deploying various security solutions, tools and products. Just like other organizational units, there are several different roles and responsibilities within a SOC, from tier 1 analysts to specialized roles like threat hunters.
The SOC Team: Roles and Responsibilities
Typical core roles that make up a SOC team consist of different tiers of SOC analysts and dedicated managers. In their research, Manfred Vielberth, Fabian Böhm, Ines Fichtinger and Günther Pernul identify these main roles — each with a specific skill set — in a SOC team.
Tier 1 — Triage Specialist: Tier 1 analysts are mainly responsible for collecting raw data as well as reviewing alarms and alerts. They need to confirm, determine or adjust the criticality of alerts and enrich them with relevant data. For every alert, the triage specialist has to identify whether it’s justified or a false positive, as alert fatigue is a real issue. An additional responsibility at this level is identifying other high-risk events and potential incidents. All these need to be prioritized according to their criticality. If problems occurring cannot be solved at this level, they have to be escalated to tier 2 analysts. Furthermore, triage specialists are often managing and configuring the monitoring tools.
Tier 2 — Incident Responder: At the tier 2 level, analysts review the higher-priority security incidents escalated by triage specialists and do a more in-depth assessment using threat intelligence (indicators of compromise, updated rules, etc.). They need to understand the scope of an attack and be aware of the affected systems. The raw attack telemetry data collected at tier 1 is transformed into actionable threat intelligence at this second tier. Incident responders are responsible for designing and implementing strategies to contain and recover from an incident. If a tier 2 analyst faces major issues with identifying or mitigating an attack, additional tier 2 analysts are consulted, or the incident is escalated to tier 3.
Tier 3 — Threat Hunter: Tier 3 analysts are the most experienced workforce in a SOC. They handle major incidents escalated to them by the incident responders. They also perform or at least supervise vulnerability assessments and penetration tests to identify possible attack vectors. Their most important responsibility is to proactively identify possible threats, security gaps and vulnerabilities that might be unknown. They should also recommend ways to optimize the deployed security monitoring tools as they gain reasonable knowledge about a possible threat to the systems. Additionally, any critical security alerts, threat intelligence, and other security data provided by tier 1 and tier 2 analysts need to be reviewed at this tier.
SOC Manager: SOC managers supervise the security operations team. They provide technical guidance if needed, but most importantly, they are in charge of adequately managing the team. This includes hiring, training and evaluating team members; creating processes; assessing incident reports; and developing and implementing necessary crisis communication plans. They also oversee the financial aspects of a SOC, support security audits, and report to the chief information security officer (CISO) or a respective top-level management position.
In addition to the tiered roles, multiple technical and specialty roles exist, including:
- Malware Analysts or Reverse Engineers offer support in responding to sophisticated threats by reverse engineering malware to help inform incident investigations, provide threat intelligence to the SOC, and improve future detection and response efforts.
- Threat Hunters (which map to tier 2) proactively look (i.e., hunt) for threats inside the organization. While this is also done by tier 3 analysts, a specialized role could be to review logs, proactively hunt for threats or research outside of the organization by analyzing publicly available threat intelligence.
- Forensics Specialists or Analysts investigate and research cyber events or crimes related to information technology (IT) systems, networks and digital evidence.
- Vulnerability Managers continually identify, assess, report on, manage and remediate vulnerabilities across endpoints, workloads and systems.
- Consulting roles: This group's two most important roles are the Security Architect (SA) and the Security Consultant. The SA plans, researches and designs a robust security infrastructure within a company. SAs conduct regular system and vulnerability tests, and implement or supervise the implementation of enhancements. They are also in charge of establishing recovery procedures. Security consultants often research security standards, security best practices and security systems. They can provide an industry overview for an organization and compare current SOC capabilities with competitors. They can help to plan, research and design robust security architectures.
What Is the Role of a Security Operations Center (SOC)?
SOCs were created to facilitate collaboration among security personnel, with a primary focus on security monitoring and alerting, including the collection and analysis of data to identify suspicious activity and improve the organization's security.
A SOC can streamline the security incident handling process as well as help analysts triage and resolve security incidents more efficiently and effectively. In today’s digital world, a SOC can be located in-house, in the cloud (a virtual SOC), staffed internally, outsourced (e.g., to an MSSP or MDR) or a mix of these.
SOCs can provide continuous protection with uninterrupted monitoring and visibility into critical assets across the attack surface. They can provide a fast and effective response, decreasing the time elapsed between when the compromise first occurred and the mean time to detection.
What Are Best Practices for a Winning SOC Team?
With security becoming a board-level topic, organizations are debating whether they need a SOC, what kind of SOC they need, and which components their SOC should include. While there are no specific guidelines to help organizations with their decisions, some best practices exist for scoping out their various options, including ensuring compliance regulations are met.
Whether one is building a physical SOC, a hybrid of cloud and on-premises, or partnering with a third party, some general benchmarks should be considered. Before starting, it’s important to note — to ensure success — that the project has an executive sponsor or “champion” as well as a strong business use case and budget for the long term. There are several ways that security teams can ensure the success of their SOC in any incarnation.
Optimize Security Teams by Focusing on Staff and Personnel
Beyond investing in security solutions and tools, the most important factor in any successful SOC will remain the human element. While machine learning and automation will undoubtedly improve outcomes like response times, accuracy, and remediation overall — especially for low-level, repetitive tasks — attracting, training and retaining security personnel, including engineers, analysts and architects, needs to be baked into any cohesive SOC strategy.
Augmenting Teams with Automation and Machine Learning
Leverage automation and machine learning to their full potential to augment and complement humans in security. Advanced analytics and AI can significantly reduce the time teams spend processing massive amounts of data in the enterprise to come up with critical security insights. By automatically detecting anomalous patterns across multiple data sources and also automatically providing alerts with context, machine learning today can deliver on its promise of speeding investigations and removing blind spots.
Automating Workflows
Security leaders can identify repeatable, low-level tasks that can work with human decision-making to help accelerate incident investigations. With too many manual processes involved in security operations and incident response (IR), including numerous threat feeds to monitor, investing in automation capabilities such as those in a SOAR solution can help orchestrate actions across the product stack for faster and more scalable IR.
Auditing Your Environment to Reduce Risks Associated with Tool Sprawl
Due to acquisitions, mergers and a lack of standardization for similar security products, many organizations are burdened with a disparate swath of tools across their security stack. One of the first steps an organization can take to reduce the security impact of tool sprawl is to audit protected systems and entities. Identify precisely what is being protected and what is being prevented from happening. Is it intellectual property? Customers’ personal information? By identifying as much as possible, whether software or physical assets, an organization can better prioritize protecting high-value and high-risk data. Having this end-to-end visibility can help identify gaps and potential threat vectors.
Want to learn the basics of a Security Operations Center? Read our What is a SOC? article.
SOC Roles and Responsibilities FAQs
Security Analyst: Monitors and analyzes network traffic, detects threats, and responds to incidents.
Incident Responder: Takes action during security incidents to mitigate damage and restore normal operations.
Threat Hunter: Proactively searches for hidden threats within the network.
Security Engineer: Maintains and optimizes security tools and infrastructure.
Developing and implementing security policies and procedures: Defining protocols for incident response, vulnerability management, and security compliance.
Coordinating incident response efforts: Leading and overseeing the response to security incidents.
Ensuring compliance with regulatory requirements: Maintaining adherence to relevant security standards and regulations.
Reporting on SOC activities and performance: Providing regular updates to senior management on the SOC's operations and effectiveness.
Investigating and responding to security incidents: Identifying the root cause, containing the threat, and restoring normal operations.
Conducting vulnerability assessments and recommending mitigation measures: Identifying security weaknesses and recommending solutions to address them.
Keeping up-to-date with the latest threat intelligence: Staying informed about emerging threats and attack techniques.
Documenting incidents and creating reports: Maintaining detailed records of security events and providing comprehensive reports to stakeholders.
Analyzing the impact and scope of incidents: Assessing the extent of damage and identifying affected systems.
Coordinating with other teams to contain and eradicate threats: Collaborating with internal and external resources to ensure effective incident resolution.
Conducting post-incident analysis and reporting: Identifying root causes, lessons learned, and recommendations for improvement.
Developing and maintaining incident response plans: Defining procedures and protocols for handling different types of security incidents.
Proficiency in using threat hunting tools and technologies: Utilizing specialized tools for proactive threat detection and analysis.
Strong analytical and problem-solving skills: Identifying patterns, anomalies, and potential indicators of compromise.
Experience with forensic analysis and malware reverse engineering: Investigating suspicious activities and extracting critical information from compromised systems.
Excellent communication and reporting abilities: Effectively communicating findings and recommendations to technical and non-technical audiences.