Black Hat Asia stands as the premier cybersecurity event in the APAC region, where elite researchers unveil zero-day exploits, trainers demonstrate cutting-edge attack techniques, and thousands of security professionals gather at Marina Bay Sands in Singapore to push the boundaries of what's possible. The conference demands a unique approach to its network security—one that must simultaneously protect critical infrastructure while allowing controlled chaos to unfold in the training environments.
As a longstanding partner, Palo Alto Networks is proud to return and play a critical role in securing Black Hat Asia 2026. Our engagement at the Network Operations Center (NOC) and Security Operations Center (SOC) helps ensure that the conference not only operates without disruption to attendees, but also remains a step ahead of emerging cyberthreats.
Architecture Built for Controlled Chaos
Black Hat's network architecture reflects the unique requirements of hosting security professionals who routinely exploit systems as part of their work. With attendees learning new techniques at all levels, the network cannot simply be left wide open; it requires deep visibility and granular control.
To support this, we provide the NOC with advanced network security services, including next-generation firewall capabilities, and comprehensive network segmentation. Our PA-5430 NGFWs are deployed in high availability to protect Black Hat-owned systems and internal infrastructure. The firewalls operate on a contextual security model: they detect and log malicious activity, but only block traffic based on its source, destination, and intent. If an attack originates from a training class to a benign or expected destination, it is monitored; if an external actor attacks the registration servers, they are immediately blocked.

Zero-Hour Defense Against Live Exploits
The NOC team operates in a perpetual state of zero-hour response, where the normal flow of threats and simulated attacks blend together. As researchers take the stage to disclose brand-new vulnerabilities, our NOC team is immediately monitoring the data, and protecting the infrastructure as attendees begin testing those newly revealed techniques in real-time.
This dynamic environment creates unprecedented challenges. Our response requires immediate, on-the-fly collaboration between Palo Alto Networks engineers, Unit 42 Threat Intelligence teams, and other NOC partners. By triaging detections using Cortex XSIAM in real-time, we ensure malicious activity is tracked without disrupting the educational flow of the conference.
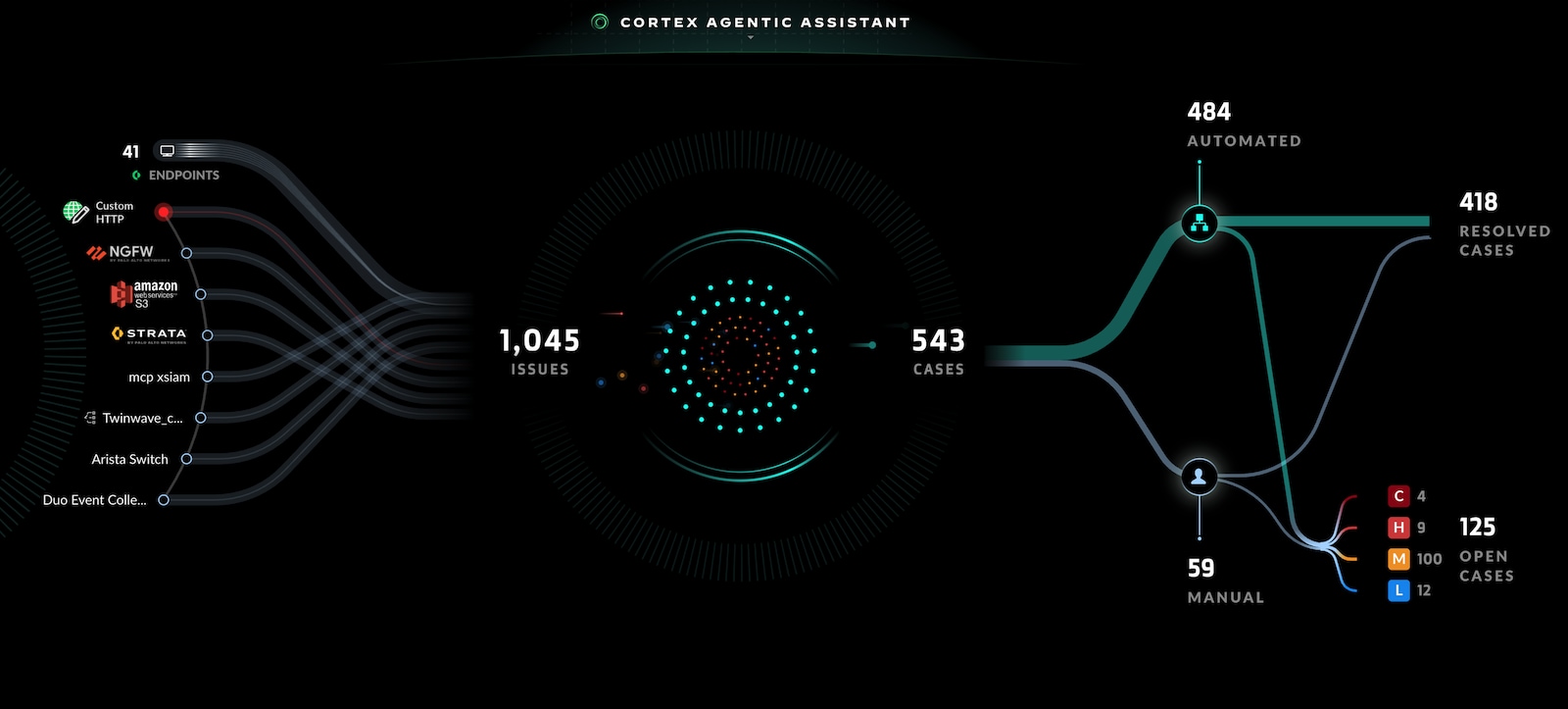
Managing the Issue Fatigue with AI-Driven Automation
The conference generates an immense volume of threat events, with activity patterns spiking during training days as students practice newly learned techniques. Cortex XSIAM fundamentally changes security operations through intelligent automation, allowing the team to manage terabytes of data, generating thousands of issues and hundreds of cases without overwhelming the analysts.
XSIAM consolidates data and logs from all the tools and infrastructure leveraged by Black Hat, including products from the other NOC partners. We rely heavily on automated playbooks to handle the sheer volume of "Black Hat positives"—legitimate attacks that trigger security controls but represent expected behavior within training environments. Playbooks automatically evaluate and close these cases. All of this data and automation in XSIAM empowers an LLM-based chatbot integrated directly into the Black Hat NOC team’s communication tool. This helpful agent collaborates with the threat hunters, allowing direct analyst interaction in the chat, accelerating triage and any required incident response.
Multi-Vendor Integration in a High-Stakes Environment
The Black Hat NOC operates as a real-world example for multivendor security integration. Partner organizations collaborate seamlessly, leaving any industry competition at the door to focus on the unified mission of securing the event.
In Singapore, this collaboration is critical. The Palo Alto Networks team works closely with Arista for network availability and security, Cisco on malware analytics and network monitoring integrations, collaborates with Corelight to analyze deep network traffic detections, and monitors JAMF to help protect the conference's physical assets. The NOC environment serves as the ultimate proving ground to build and test these integrations, which ultimately benefit enterprise customers who deploy multi-vendor security stacks.
See the Team in Action
To see the team in action, the Black Hat NOC will be streamed live via the conference Twitch channel, or you can visit and tour the NOC on-site. The partners also give NOC presentations in the Business Hall and Briefings Pass holders can attend the Black Hat Asia NOC Report on the last day of the conference.
Black Hat NOC Schedule (2026 Dates & Times TBD)
- NOC Visiting Hours
- Live Stream Hours
- NOC Presentations (Business Hall Theater)
- The Black Hat Asia Network Operations Center (NOC) Report*
(Available to Briefings Pass holders only)