The traditional network security model has long relied on a simple yet increasingly outdated concept — the secure perimeter. The secure perimeter approach assumes everything inside a network is inherently trustworthy and focuses security efforts on keeping threats outside a defined boundary. But widespread adoption of cloud computing, coupled with an evolving threat landscape, has exposed the limitations of perimeter-based security.
In response, the Zero Trust model emerged as a more effective security framework. In this blog post, we delve into Zero Trust and the best practices that exemplify it in cloud environments.
Beyond the Perimeter
As organizations moved to the cloud, the need to secure their data and applications led them to implement multiple security solutions, often without fully considering the integration and management aspects. For many, the ad hoc approach accumulated in an overwhelming collection of security tools.
Today, numerous enterprises continue to rely on an array of point tools. In fact, 76% of organizations say the number of tools they use creates blind spots, according to The State of Cloud-Native Security Report 2023. Without comprehensive context, security teams striving to reduce their vulnerability to attacks find themselves increasingly burdened by manual tasks. As organizations attempt to protect their environment from the surge in breaches, they’re aware of the stakes — that the average cost of a data breach is $4.45 million in 2023.
Zero Trust Security Model
In a realm where threats emerge from external and internal sources, Zero Trust has necessarily displaced the traditional concept of network trust. Operating on the premise to never trust, always verify, Zero Trust demands constant scrutiny and validation. Under Zero Trust, every access request, irrespective of its origin, undergoes authentication and authorization. By eliminating the assumption of inherent trust and implementing granular access controls, organizations can enhance their security posture, adapt to evolving challenges, and better protect their valuable assets.
Consider, for example, a scenario involving an employee with legitimate access to sensitive company data who decides to misuse their access for personal gain. In a traditional network security model that assumes trust within the network perimeter, the employee's access might go unchecked once they're inside the network. But Zero Trust practices would mitigate this vulnerability. Practices include:
- Continuous verification: Verify user and device identities continuously before granting access to resources.
- Least privilege access: Grant access permissions based on the principle of least privilege, restricting access to only what’s necessary for the specific task.
- Just-in-time access: Ensure that users, systems and applications receive access to resources only when absolutely needed — the precise duration.
- Comprehensive visibility and monitoring: Implement continuous monitoring and analysis of network traffic, user behavior and security events to detect anomalies and potential threats.
Benefits of Zero Trust in Cloud Environments
Zero Trust plays a vital role in securing cloud environments by addressing unique security challenges inherent in dynamic and distributed architectures. Eliminating trust assumptions and implementing continuous verification, Zero Trust effectively reduces the risk of unauthorized access and lateral movement within cloud networks, protecting sensitive data, applications and infrastructure.
Zero Trust actively enhances visibility through granular insights into user activities, device health and network traffic, enabling organizations to detect and respond to threats swiftly, securing their cloud environments. By offering flexibility and scalability, the Zero Trust model allows organizations to adapt their security measures to evolving needs and workloads, maintaining strong security postures in the face of emerging threats and changing technologies.
Additionally, Zero Trust actively simplifies compliance, aligning with various regulatory frameworks and helping organizations adhere to data protection and access control requirements in the cloud. This alignment not only ensures regulatory compliance but also strengthens organizations' overall security strategies.
Leverage Zero Trust Security Model with Prisma Cloud
Prisma Cloud delivers a cloud-native application protection platform (CNAPP) that seamlessly integrates security functions, eliminating the need for separate tools and interfaces. This unified approach offers visibility across different security domains, ensuring that DevOps, security and cloud infrastructure teams can work together to provide comprehensive security. By embedding security throughout the software development lifecycle, Prisma Cloud helps organizations implement and maintain the Zero Trust model.
Cloud Infrastructure Entitlements Management
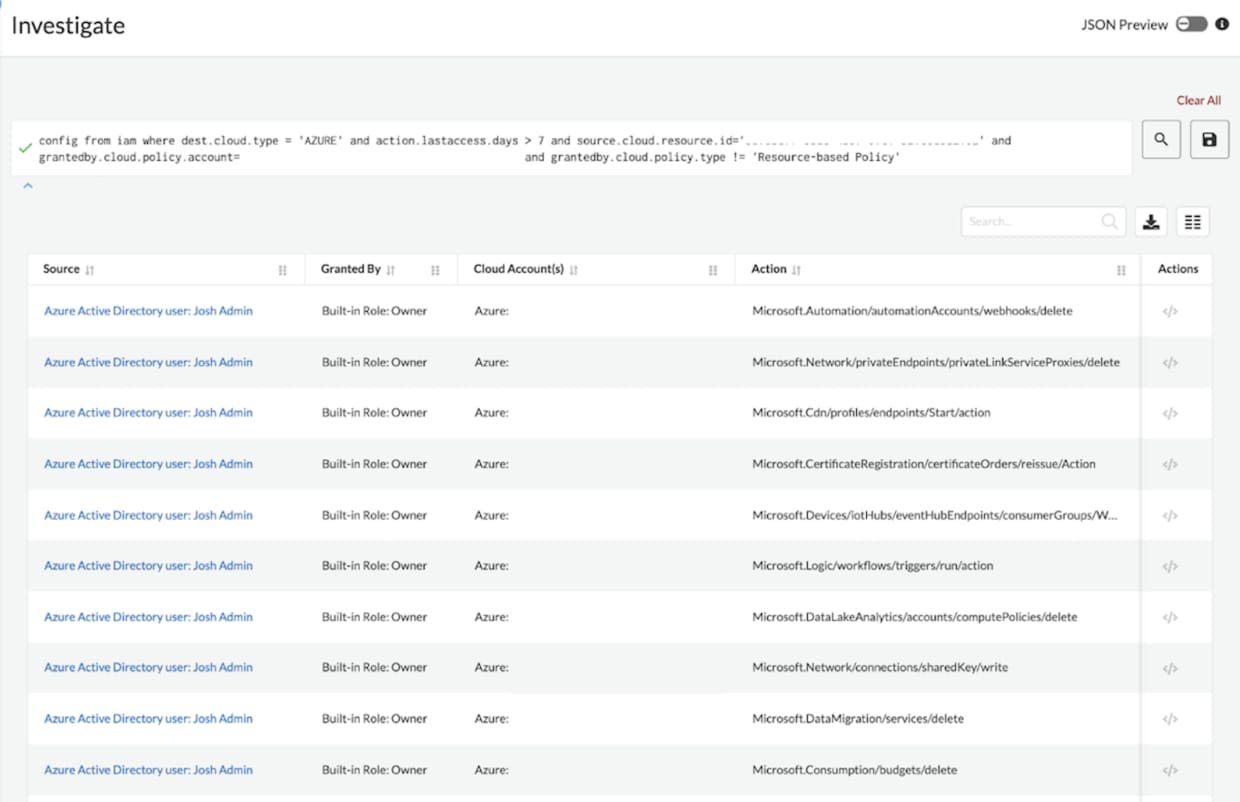
Prisma Cloud's Cloud Infrastructure Entitlement Management (CIEM) directly supports the Zero Trust security model by providing comprehensive visibility and control over user permissions across AWS, Azure and GCP environments. In the Zero Trust framework — where trust is never a given — Prisma Cloud automatically calculates users' effective permissions, identifying overly permissive access and suggesting corrections to achieve the principle of least privilege.
Prisma Cloud takes it a step further, offering specialized policies that detect risky permissions and facilitate the removal of unwanted access to cloud resources. This level of visibility and control empowers organizations to continuously monitor and verify which users can take specific actions on which resources across cloud environments.
Cloud Network Security
In the context of Zero Trust, Prisma Cloud's high-fidelity network visibility enables security teams to reduce risk by identifying potential threats and swiftly mitigating lateral movement within the cloud. Leveraging advanced machine learning, Prisma Cloud monitors normal network behavior in each customer's cloud environment and detects network anomalies and zero-day attacks with remarkable accuracy.
Powered by innovative App-ID technology, the paradigm ushers in a new era of application-level visibility into network traffic. It empowers organizations to make precise decisions regarding which applications are essential for their operations while blocking all other traffic — massively reducing the attack surface. This transcends traditional port blocking through the incorporation of Advanced Threat Prevention and WildFire, enabling VM-Series to scrutinize all authorized application traffic for vulnerability exploits and advanced malware.
Cloud Security Posture Management (CSPM)
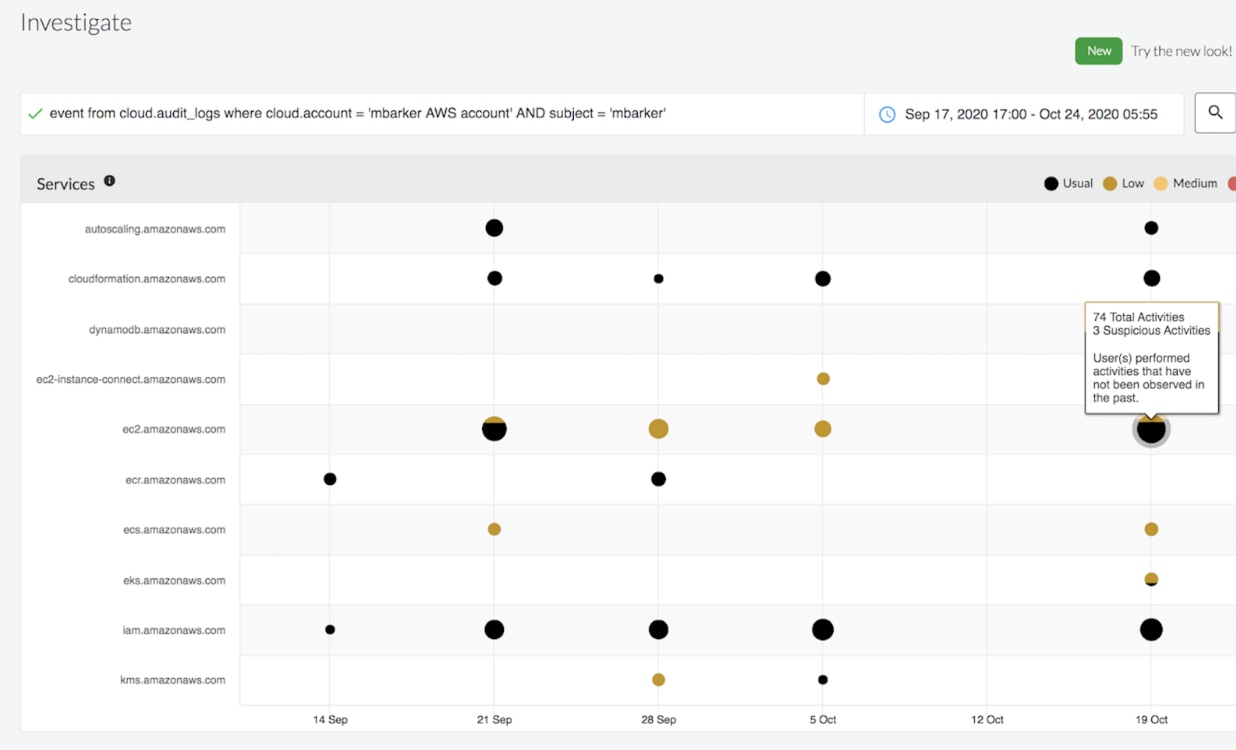
Prisma Cloud offers continuous, automated monitoring and comprehensive visibility across public cloud infrastructure, extending to the identification of new and existing assets, anomalous behaviors and potential threats. The CSPM platform's unique ability to normalize and analyze disparate data sources ensures unmatched risk clarity, aligning with Zero Trust's demand for precise insights.
Prisma Cloud's use of anomaly-based policies, driven by machine learning, complements traditional rule-based policies, providing a comprehensive approach to threat detection, a fundamental aspect of Zero Trust. Additionally, Prisma Cloud Data Security addresses the challenges of data discovery and protection in dynamic public cloud environments, offering a fully integrated cloud-native solution that enhances security and trust verification.
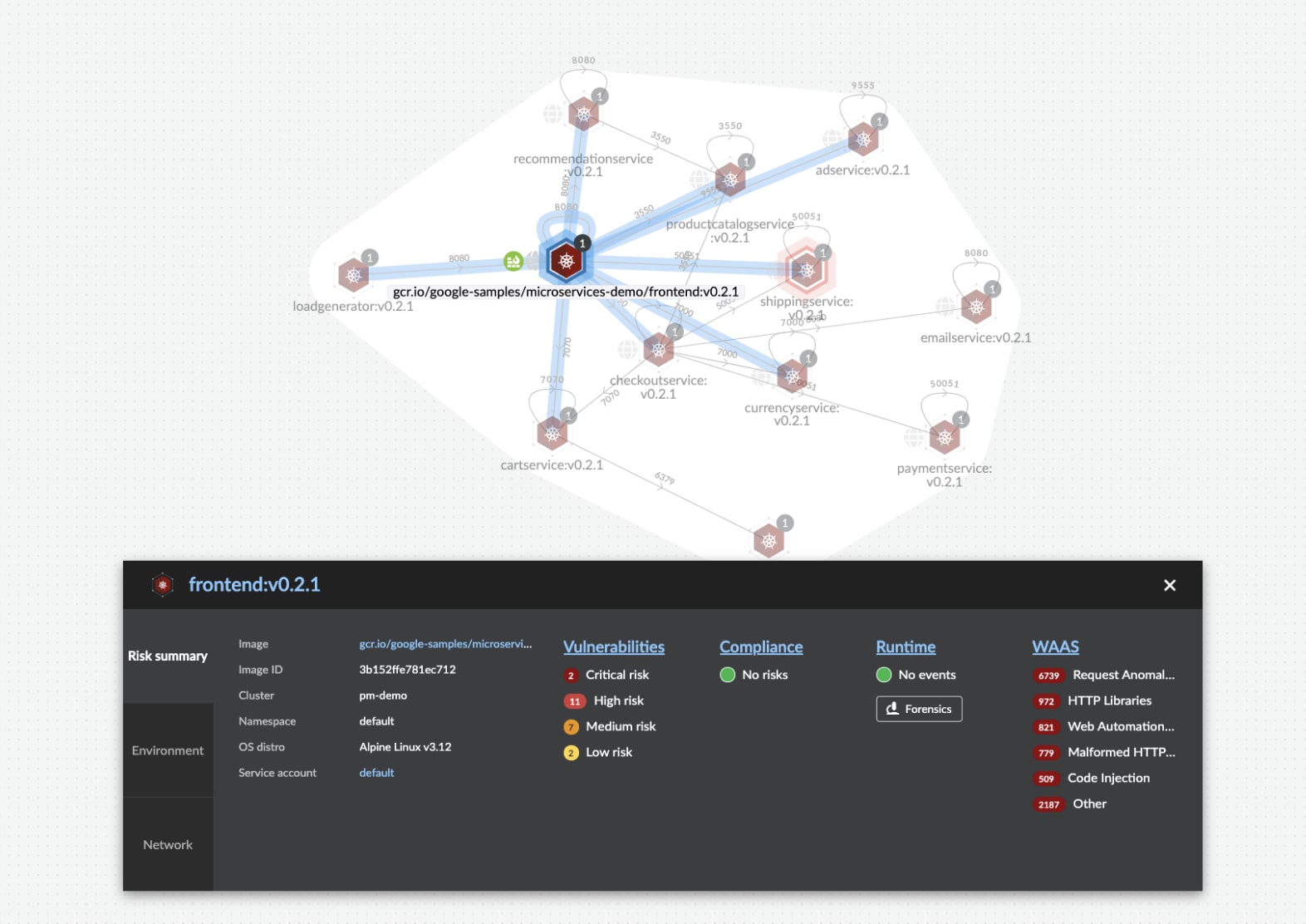
Runtime Cloud Workload Protection Platform
Prisma Cloud, as a comprehensive cloud workload protection (CWP) solution, plays a pivotal role in advancing the principles of the Zero Trust security model within cloud environments. Its versatile security capabilities safeguard a spectrum of cloud assets, from virtual machines (VMs) to containers, Kubernetes applications, serverless functions and even containerized offerings like AWS Fargate tasks.
The platform’s support for infrastructure as code (IaC) templates, container images, open-source packages and delivery pipelines underscores its commitment to comprehensive code security.
Continuous Monitoring, Incident Detection and Automation
Continuous monitoring is the guardian of Zero Trust, providing organizations with up-to-the-minute insights into their network activities and user behaviors. It acts as the eyes and ears of the security posture, enabling rapid detection of anomalies, insider threats and external attacks. Automation also plays a critical role in implementing and maintaining a Zero Trust by allowing organizations to respond to security incidents faster.
Imagine an unexpected security event unfolds for an e-commerce company. A user who typically engages with the payment processing system within standard business hours attempts access late at night a foreign location. Prisma Cloud's anomaly policy Unusual User Activity immediately flags the activity. As part of its automated response, it isolates the affected servers to contain the potential threat and notifies the security team of the incident.
The company's security experts initiate an investigation into the root cause. Their analysis reveals that the user's login credentials had been compromised. Monitoring and anomaly detection enables the security team to avert a breach.
Learn More
By adopting Zero Trust principles, organizations can enhance their security posture, protect critical assets, and minimize the impact of security breaches. When combined with cloud-native security capabilities and best practices, Zero Trust provides a solid security foundation for the dynamic and distributed nature of cloud computing.
If you haven’t tried Prisma Cloud and would like to test drive best-in-class code-to-cloud security, we invite you to experience a free 30-day trial.
References
“2022 State of Cloud Native Security Report.” n.d. Palo Alto Networks. /state-of-cloud-native-security.“
IBM Registration Form.” n.d. IBM. https://www.ibm.com/account/reg/us-en/signup?formid=urx-52258.