Threat Intelligence is the power that battles the minds that make malware, ransomware and other cyber threats. Knowledge of threats and threat data is not enough as the key to win this battle is not just analyzing the data but acting on it quickly. Taking action to operationalize it is a critical component for security teams to mitigate relevant risks and disrupt targeted malicious attack campaigns
Security operations centers (SOCs) and Threat Analysts are struggling with ever-increasing and growing cyber threats. Massive volumes of data created every second lead to new vulnerabilities and attack vectors. How do SOCs and incident response teams keep up with the threats happening across the landscape? To be effective, SOCs must have access to the right data with the right context at the right time to fulfill their mission of identifying and responding to threats.
Why is it Important to Operationalize Your Threat Data?
Threat intelligence without context is just threat data. In order for threat intelligence to be of use, the original context of the threat intel has to be applied appropriately and mapped to internal incidents and policies.
The flood of indicators—Security teams rarely get the most value out of their threat intel investments, given the millions of indicators that come in daily. Not all threat intelligence is relevant, forcing analysts to manually tune and score them before they can be distributed to enforcement points.
Too many tools and services—As part of their cyber threat intelligence (CTI) programs, many organizations consume open source CTI, purchase feeds, view product portals, share information with industry ISACs, and purchase custom reports or services for monitoring impending threats. Somehow, the security teams have to organize, analyze, and gain knowledge from this mire of information.
Time Consuming Manual Processes—Security teams today still rely on human intelligence to collect, correlate, contextualize, and enrich CTI—before they can use it for their benefit. With so much time spent on managing technology through manual processes, organizations struggle to turn CTI into insight that can be used to fine-tune security controls, generate remediation rules, or communicate risk to business stakeholders. This cannot scale and has nothing to do with understanding and responding to threats in a timely manner.
In order to operationalize cyber threat intelligence, it needs to be actionable. Threat Intelligence Platforms can help fill the gap. Threat Intelligence Platform (TIP) is a technology solution that collects, aggregates, and organizes threat intel data from multiple sources and formats. A TIP provides security teams with information on known malware and other threats, powering efficient and accurate threat identification, investigation, and response
Why Can a Threat Intelligence Management Platform Help?
To truly achieve operationalized threat intelligence, an investment must be made in an underlying threat intelligence management platform that will enable an organization to truly harness the power of threat intelligence and translate that threat intelligence into action.
Cortex® XSOAR Threat Intelligence Management introduces a completely new approach to embedding and taking action on threat intelligence across every aspect of the incident lifecycle. It enables you to attain unmatched visibility into the global threat landscape with automated connections between external threat intelligence and internal incidents.
Playbook Driven Automation
The ready-to-use playbooks can identify and automate responses to frequent threats, including phishing, malware, and so on. XSOAR TIM features more than 150 Threat Intelligence based diverse range of playbooks based on industry best practices and standards.
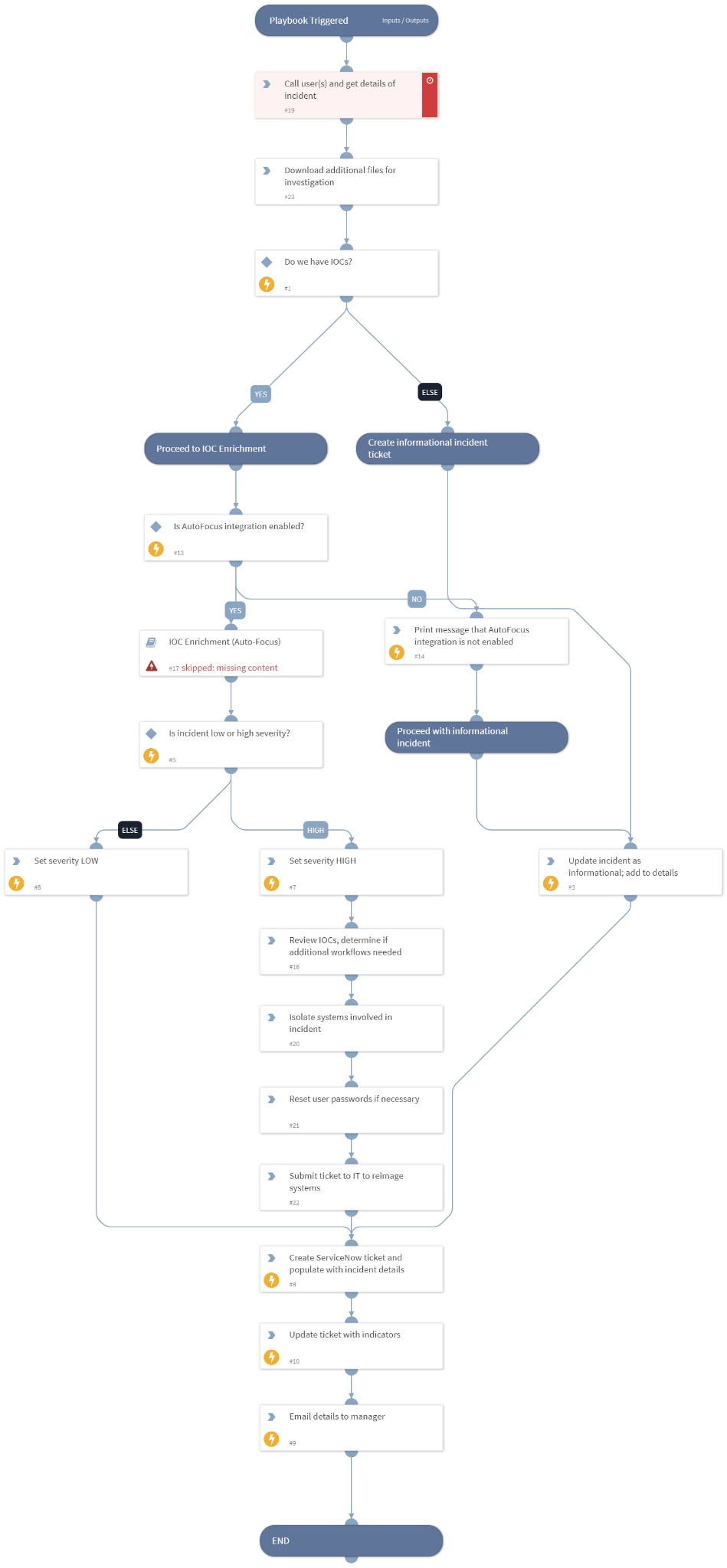
XSOAR TIM playbook in action
You can also build customized or advanced playbooks, which gives security teams the flexibility to respond when they see fit. For organizations unsure about automation, playbooks can be customized to undertake automatic enrichment actions while also fulfilling role-based security demands requiring authorization for containment. These capabilities support fully- and semi-automated actions providing security teams the ability to identify the level of automation required at every phase of the response process, with the final decision made by a human analyst if needed. For example, a playbook for malware analysis covers every stage of the response process from detection and investigation to containment and remediation.
Take automated action to shut down threats with purpose-built playbooks based on proven SOAR capabilities.
Learn how Cortex XSOAR Threat Intelligence Management and threat intel provider, Intel 471 empowers your team to fight cybercrime with confidence.
Join our next live webinar and Q&A, “Operationalize Threat Intelligence with User Driven Automation” featuring Intel471 starting at 9 a.m. PDT on Wednesday, Oct 13.. Register today!
In this webinar, you’ll learn:
- What ransomware is and the associated attack chains
- How Cortex XSOAR Threat Intelligence Management is the glue between threat intelligence tools, like Intel 471.
- How threat analysts and security teams can significantly speed investigation, prevention and response by operationalizing threat intelligence
- How to empower your cybersecurity team to fight cybercrime with confidence
Be a part of this must-see live webinar. Unable to make it? Sign up to receive a link with the recording.