- What Is Access Management?
- What Is Access Control?
-
What Is an Application Gateway? Layer 7 Balancing Explained
- App Gateway Explained: Beyond Basic Load Balancing
- The Anatomy of a Request: Listener to Backend Pool
- Key Benefits and Strategic Advantages
- Application Gateway vs. Traditional Tools
- Why Gateways Support Zero Trust
- Implementation Challenges and Solutions
- Advanced Proactive Defense
- Application Gateway FAQs
-
What Is User Behavior Analytics (UBA)?
- User Behavior Analytics Explained
- How UBA Works: The Data-to-Insight Flow
- Core UBA Data Sources
- UBA vs. UEBA: Understanding the Entity Difference
- Critical Use Cases for Modern Security Ops
- Top 3 Benefits of UBA Deployment
- UBA-Enabled Adaptive Authentication
- Zero Trust and Behavior Analytics Alignment
- User Behavior Analytics FAQs
-
What Is Adaptive MFA? How Risk-Based Authentication Works
- How is Adaptive MFA Different from Traditional MFA?
- Why Is Adaptive MFA Important?
- How Does Adaptive MFA Work?
- Adaptive MFA Use Cases & Real-World Examples
- What are Common Risk Signals Used by Adaptive MFA?
- How is Adaptive MFA Related to Zero Trust?
- What are Some Examples of Adaptive MFA in Action?
- Adaptive MFA Transition Checklist
- Implementation Notes for SOC Leaders
- What Is Active Directory (AD)?
-
Authentication and Authorization Explained
- Authentication and Authorization Explained
- Differentiating Authentication from Authorization
- Authorization Models: RBAC, ABAC, and Policy Enforcement
- Lateral Movement and Attacker Workflow
- Cloud Security Implications for Authorization
- Zero Trust Alignment with Access Control
- Authentication and Authorization FAQs
- What Is CIAM (Customer Identity and Access Management)?
- What Is Single Sign-On (SSO)?
- What Is Passwordless Authentication?
- What is BeyondCorp?
- What is the Evolution of Multifactor Authentication
- What Is Cloud Infrastructure Entitlement Management (CIEM)?
- What is Multifactor Authentication (MFA) Implementation?
- What Is Identity and Access Management (IAM)?
What Is the Principle of Least Privilege?
The principle of least privilege (PoLP) is an information security concept which maintains that a user or entity should only have access to the specific data, resources and applications needed to complete a required task. Organizations that follow the principle of least privilege can improve their security posture by significantly reducing their attack surface and risk of malware spread.
The principle of least privilege is also a fundamental pillar of zero trust network access (ZTNA) 2.0. Within a ZTNA 2.0 framework, the principle of least privilege provides the ability to accurately identify applications and specific application functions across any and all ports and protocols, including dynamic ports, regardless of the IP address or fully qualified domain name (FQDN) an application uses. The principle of least privilege within ZTNA 2.0 eliminates the need for administrators to think about network constructs and enables fine-grained access control to implement comprehensive least-privileged access.
How does the principle of least privilege (PoLP) work?
The principle of least privilege works by limiting the accessible data, resources, applications and application functions to only that which a user or entity requires to execute their specific task or workflow. Without incorporating the principle of least privilege, organizations create over-privileged users or entities that increase the potential for breaches and misuse of critical systems and data.
Within ZTNA 2.0, the principle of least privilege means the information technology system can dynamically identify users, devices, applications and application functions a user or entity accesses, regardless of the IP address, protocol or port an application uses. This includes modern communication and collaboration applications that use dynamic ports.
The principle of least privilege as executed within ZTNA 2.0 eliminates the need for administrators to think about the network architecture or low-level network constructs such as FQDN, ports or protocols, enabling fine-grained access control for comprehensive least-privileged access.
Video Description: Kumar Ramachandran, senior vice president of Prisma SASE, explains the principle of least privilege within ZTNA 2.0.
Why Is the Principle of Least Privilege Important?
The principle of least privilege is an important information security construct for organizations operating in today’s hybrid workplace to help protect them from cyberattacks and the financial, data and reputational losses that follow when ransomware, malware and other malicious threats impact their operations.
The principle of least privilege strikes a balance between usability and security to safeguard critical data and systems by minimizing the attack surface, limiting cyberattacks, enhancing operational performance and reducing the impact of human error.
What Are the Benefits of the Principle of Least Privilege?
The principle of least privilege:
- Minimizes the attack surface, diminishing avenues a malicious actor can use to access sensitive data or carry out an attack by protecting superuser and administrator privileges.
- Reduces malware propagation by not allowing users to install unauthorized applications. The principle of least privilege also stops lateral network movement that can launch an attack against other connected devices by limiting malware to the entry point.
- Improves operational performance with reductions in system downtime that might otherwise occur as a result of a breach, malware spread or incompatibility issues between applications.
- Safeguards against human error that can happen through mistake, malice or negligence.
The benefits of PoLP for modern applications
The principle of least privilege is all about providing the minimum amount of privilege possible for users to get their work done. Unfortunately, legacy security solutions require organizations to allow access to a broad range of IP addresses, port ranges and protocols in order to use SaaS and other modern apps that use dynamic IPs and ports. This approach violates the principle of least privilege, creating a huge security gap that can be exploited by an attacker or malware.
ZTNA 2.0 enables comprehensive usage of the principle of least privilege with Prisma Access and its patented App-ID functionality to provide dynamic identification of all users, devices and applications as well as application functions across any and all protocols and ports. For administrators, this enables very fine-grained access control to finally implement true least-privileged access.
Video Description: Kumar Ramachandran, senior vice president of Prisma SASE, explains how ZTNA 2.0 protects data in all applications, no matter where they’re located.
The Benefits of PoLP for Client-Server Applications
Comprehensive principle of least privilege technologies – like those available in Prisma Access – enable bidirectional access control between a client and server to define application access policies and easily enable least-privileged access for applications that use server-initiated connections. This includes mission-critical applications such as update and patch management solutions, device management applications and help desk applications.
The Benefits of PoLP for Private Applications
Many private applications lack the built-in, fine-grained access control capabilities that exist in most modern SaaS apps. Something as simple as allowing users to access an application to view – but not upload or download – data is simply not possible because the application is identified purely based on IP address and port number.
With the PoLP capabilities available through ZTNA 2.0 and Prisma Access, organizations get granular control at the sub-app level, enabling them to identify applications at the App-ID level.
How to Implement PoLP in your organization
Implementing the principle of least privilege within your organization should not be difficult, overwhelming or come with compromises. It boils down to alignment – mapping needs to the key concerns or challenges without requiring a massive architectural shift or business disruption.
Where to Start a PoLP Implementation
VPN technology replacement is a good starting point for implementing the principle of least privilege within your organization. Replace legacy remote access outdated VPN technologies with a more modern ZTNA 2.0 solution to overcome performance bottlenecks and simplify management.
VPN replacement initiatives are driven by a number of factors:
- Applications moving to a true hybrid model, taking advantage of on-premises, cloud and multicloud environments. Legacy VPN technology that trombones or backhauls traffic to an on-premises “concentrator” doesn’t scale or deliver the best possible user experience in this new model.
- Changes in enterprise app access requirements. Traditionally, employees used managed devices to complete work-related tasks. However, more and more unmanaged devices have made their way onto corporate networks and can access corporate applications.
- Organizations looking for consistent and universal protection and a security model for all apps, not just web or legacy applications.
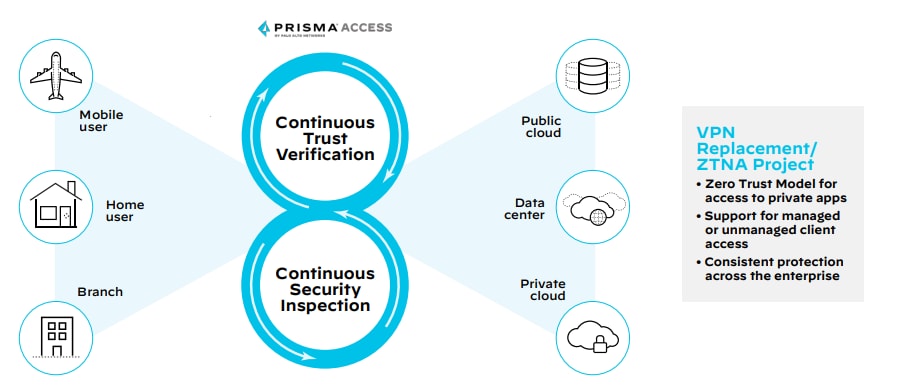
While there are a number of solutions that can address some of those needs, only ZTNA 2.0 with Prisma Access helps transform networking and security to support both managed and unmanaged devices while delivering consistent security protection across the entire organization.
Get PoLP with ZTNA 2.0 on Prisma Access
Prisma Access provides cloud-delivered ZTNA 2.0 with the best user experience in a simple unified product. See how Prisma Access dramatically reduces the attack surface and securely connects all users and all apps with fine-grained access controls with patented App-ID technology to precisely control access at the app and sub-app levels, including download or upload.
Watch the video
Download the paper from ESG Global
Visit the webpage
Principle of Least Privilege Access FAQs
- Balancing security with user productivity, as overly restrictive access can hinder workflow.
- Ensuring consistent enforcement across all systems and applications.
- Addressing resistance to change from users accustomed to broader access.
- Managing complexity, especially in large organizations with diverse IT environments.