This post is also available in: 日本語 (Japanese)
On March 17, our webinar “Leverage Your Firewall to Expose Attackers Hiding in Your Network” webinar will share tips on using Cortex XDR to discover network threats. Register today!
Artificial intelligence (AI) for security isn’t autonomous – yet. The art of utilizing machine learning (ML) is therefore in perfecting how it augments human intuition and curiosity, and in automating this unity to the maximum extent. The following is a true story from a pilot Cortex XDR Managed Threat Hunting customer, and it showcases the security outcomes that can be achieved today when you pair powerful AI with elite threat hunting expertise.
Cortex XDR is built on over a hundred ML models, with an elite group of security experts augmenting the models’ predictions with human intuition. These analysts are called Unit 42: the global threat intelligence team at Palo Alto Networks that is renowned for their work to hunt, catch and tag threats.
With Community Access to Cortex XDR Managed Threat Hunting, customers now have Unit 42 as part of their teams, giving them access to a world-class SOC along with the world-class AI-driven XDR platform.
On a sunny Saturday morning, an anomalous signal came to the Cortex Managed Threat Hunting team’s attention. A QBot remote access trojan, known for facilitating ransomware infections of entire networks, was attempting to execute on a server at a Massachusetts-based software company. Although the malware was a never-before-seen mutation of the Qbot virus, our Behavioral Threat Protection (BTP) engine caught it.
| For those of you new to the world of mutating viruses: there are free open-source frameworks that attackers use to automate the mutation of viruses on a large scale, compiling new, undetectable versions of the same malicious code to bypass antivirus software that still relies on signatures. The only way to keep up with the growing number of new mutations is via ML models that learn to pick up the similarities between mutations by analyzing the executables and their behavior as they run. Cortex XDR’s BTP engine learns all these mutations based on customer occurrences and Unit 42 research, continuously improving our global model and sharing this threat intel across all our customers in real time. |
Fortunately, the Cortex XDR endpoint agent killed the malware as soon as the executable attempted to run. Even though the mutation had never been seen before, BTP picked it up and correctly determined that it was malicious.
Then, a second alert came from Cortex XDR signaling that a second host was attempting to run the same file with a different name, but Symantec Endpoint Protection caught it by the hash and removed it prior to execution.
Problem Solved – Right?
At this stage, these were the only two detected occurrences of the virus, and they’d both been eliminated. Call it a day? Not really – there were still questions to answer. Where did the viruses come from? Will they come back again? This is the point when the Unit 42 analysts start working on a root cause analysis, peeling off the layers of this mystery.
| About Qbot (QakBot): Qakbot is a fully featured remote access trojan which has plugins for basically everything. In particular, Qakbot is known for its worming capabilities which has been known to facilitate ransomware infections of entire corporate networks. QakBot is over a decade old, and this specific sample was first seen in the WildFire cloud on March 10, 2015. QakBot is generally associated with criminal adversaries, and the primary function is information stealing, although it can easily be used to load additional malware onto the infected host. Lateral movement is performed by the malware attempting to spread itself to open shares on the network, including administrative shares of C$ and Admin$. In case of shares protected by weak passwords, it will attempt brute-forcing via a dictionary attack. QakBot may also attempt to access the Credential Store where Windows stores cached passwords for network logins. The Password Manager of Internet Explorer may also be accessed to steal additional cached credentials. |
Knowing that Qbot moves like a worm through shared folders, analysts concluded that it must have come from somewhere on the network. And the fact that we hadn’t seen it on other computers meant that it lived on an unmanaged device that kept infecting the network. No company has 100% endpoint agent coverage: We needed to look at the network for clues.
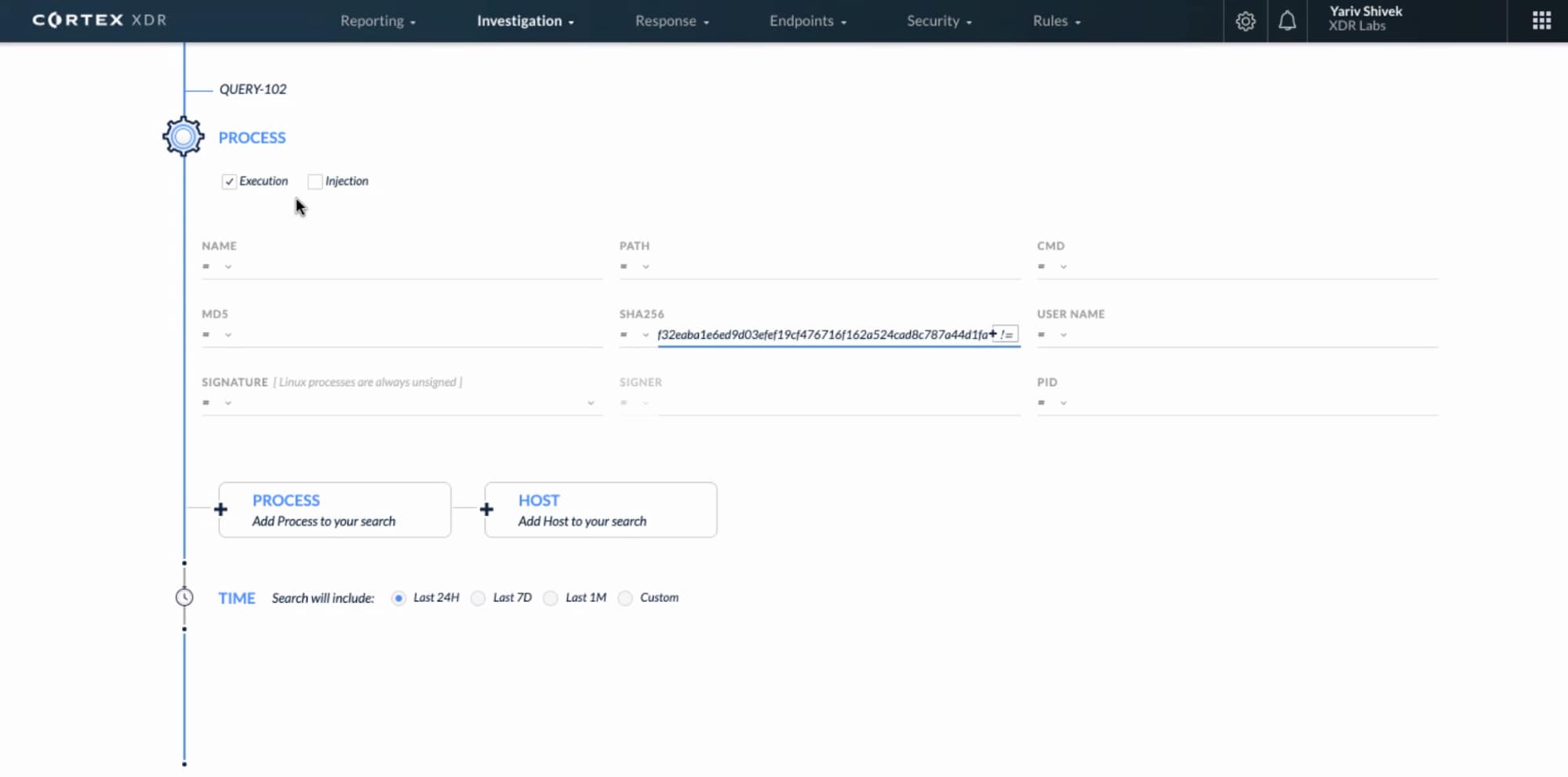
Our MTH analysts ran backend queries searching in Cortex Data Lake to look at network traffic and server message block (SMB) file transfers over network shares. We found one host that the two infected servers got the virus from – as we guessed, the host was unmanaged. Looking at the network traffic between the hosts involved, we saw the Qbot executables traveling from the unmanaged server to the ones where they’d been caught.
We investigated further in the network logs and found that the unmanaged host seemed to have been infected for over a month, as indicated by continuous beaconing activity to the internet.
| Beaconing is when a piece of malware sends and receives short, intermittent, repeating beacons to and from the internet, which may indicate command and control (C2) activity. Beaconing usually involves the use of domain generation algorithms (DGA) to randomize domain names regularly – sometimes daily – to circumvent domain name blacklisting. We built ML models in Cortex XDR that recognize DGA behavior, as described in detail in a previous blog. |
We’re Not Done Yet.
At this point, we had one unmanaged host that was infected and was likely attempting to infect other computers on the network. Peeling the onion further, the team found two additional unmanaged systems that showed similar suspicious DGA beaconing activity. No endpoint data was available for those hosts, either. One of them had been beaconing for the past few weeks, while the other one only started a few days prior.
Our MTH group kept hunting for other indicators of compromise that are characteristic of QBot. What else was infected, what damage had been done? They looked for correlations and signs across disk activities and network traffic using Cortex XDR and Autofocus queries against the customer’s WildFire instance, Unit 42’s private threat intel databases, and unique, low-fidelity sources.
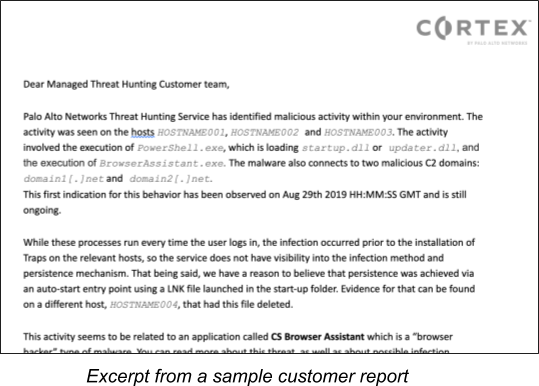
The Customer Report
When the MTH team reached their conclusion, they quickly compiled a report to notify the customer about the threat. When customers receive this report, they kick off their incident response procedure and remediate the situation in-house. Since MTH findings are extremely accurate, some of our pilot customers respond to it automatically.
Proactive Courtesy
While this customer story was about Unit 42 analysts responding to a suspicious signal, there’s also an important proactive angle to Cortex XDR Managed Threat Hunting. Unit 42 continues to run proactive research on telemetry captured in and across our MTH customers’ environments. It happens periodically that MTH customers receive proactive alerts when a new, high-impact malware is found, or a large attack shows up in the news:
“Dear customer, you may have heard about this and that new malware in the news – we ran a proactive scan in your environment and can confirm that you’re okay.”
Our customers love this collective and proactive intelligence. They know that Unit 42 is at the cutting edge of malware discovery. It gives them peace of mind.
Learn more about Cortex XDR Managed Threat Hunting service. Community Access is available now; general availability is expected in April.
Read more stories in the Busted by Cortex XDR series.